Sign Presentation for Administrative Secure
Make the most out of your eSignature workflows with airSlate SignNow
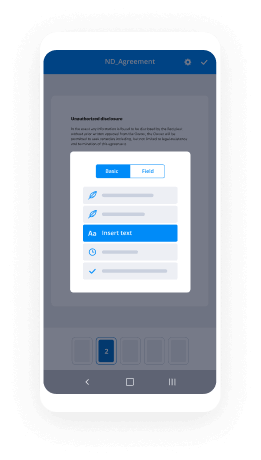
Extensive suite of eSignature tools
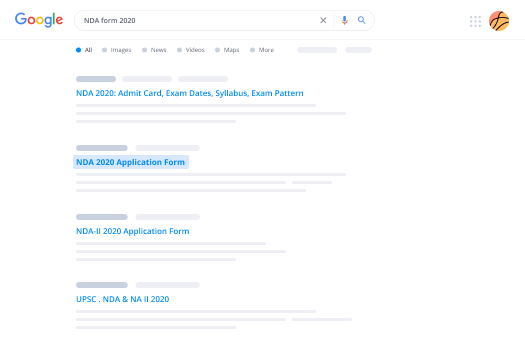
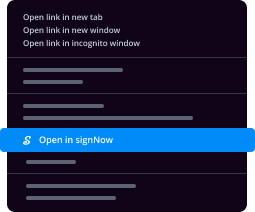
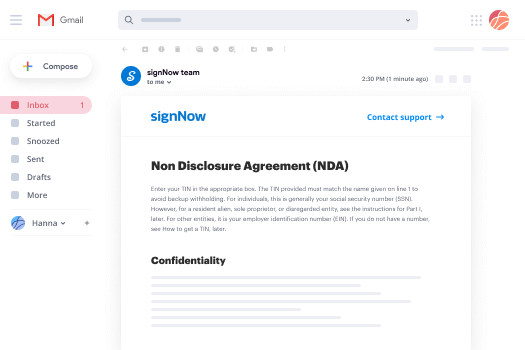
Discover the easiest way to Sign Presentation for Administrative Secure with our powerful tools that go beyond eSignature. Sign documents and collect data, signatures, and payments from other parties from a single solution.
Robust integration and API capabilities
Enable the airSlate SignNow API and supercharge your workspace systems with eSignature tools. Streamline data routing and record updates with out-of-the-box integrations.
Advanced security and compliance
Set up your eSignature workflows while staying compliant with major eSignature, data protection, and eCommerce laws. Use airSlate SignNow to make every interaction with a document secure and compliant.
Various collaboration tools
Make communication and interaction within your team more transparent and effective. Accomplish more with minimal efforts on your side and add value to the business.
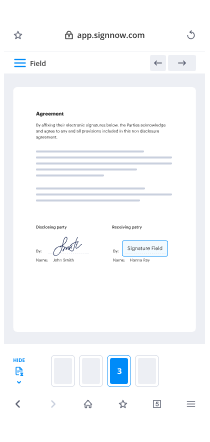
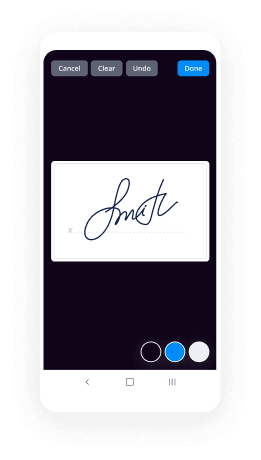
Enjoyable and stress-free signing experience
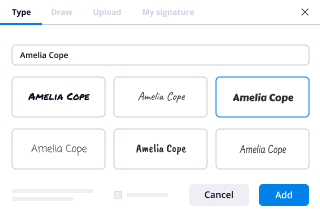
Delight your partners and employees with a straightforward way of signing documents. Make document approval flexible and precise.
Extensive support
Explore a range of video tutorials and guides on how to Sign Presentation for Administrative Secure. Get all the help you need from our dedicated support team.
Sign Presentation for Administrative Secure
Keep your eSignature workflows on track
Make the signing process more streamlined and uniform
Take control of every aspect of the document execution process. eSign, send out for signature, manage, route, and save your documents in a single secure solution.
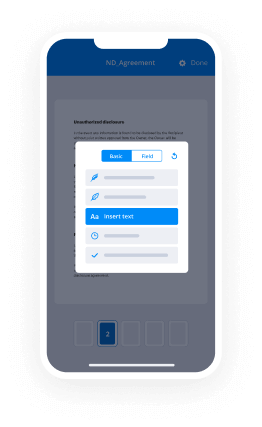
Add and collect signatures from anywhere
Let your customers and your team stay connected even when offline. Access airSlate SignNow to Sign Presentation for Administrative Secure from any platform or device: your laptop, mobile phone, or tablet.
Ensure error-free results with reusable templates
Templatize frequently used documents to save time and reduce the risk of common errors when sending out copies for signing.
Stay compliant and secure when eSigning
Use airSlate SignNow to Sign Presentation for Administrative Secure and ensure the integrity and security of your data at every step of the document execution cycle.
Enjoy the ease of setup and onboarding process
Have your eSignature workflow up and running in minutes. Take advantage of numerous detailed guides and tutorials, or contact our dedicated support team to make the most out of the airSlate SignNow functionality.
Benefit from integrations and API for maximum efficiency
Integrate with a rich selection of productivity and data storage tools. Create a more encrypted and seamless signing experience with the airSlate SignNow API.
Collect signatures
24x
faster
Reduce costs by
$30
per document
Save up to
40h
per employee / month
Our user reviews speak for themselves






-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
Intuitive UI and API. Sign and send documents from your apps in minutes.
A smarter way to work: —how to industry sign banking integrate
FAQs
-
How is the Godrej Plot Devanahalli project in Bangalore?
If you are searching for the useful pieces of land in Bangalore from where you can access the whole city easily and where you can build your dream home by your own thoughts and plans, please consider the residential plots available in Godrej Reserve Plots.Wonderfully Planned PlotsThese are not just pieces of land but are the convenient sources of making every possibility brighter for your develop and get prosperous in this highly-modernized city. The land is not only a means to construct a home there but is also the major supplement to collect the best returns. As exactly what the residential plots available in Godrej Reserve Plots Bangalore are capable of. All these plots have been planned so brilliantly that users can utilize the maximum of the available space and also can offer great returns to the investors in the long run. Surrounded by vast green and plenty of landscape regions, the property has been spread over 92.7 acres of land area where high-end constructions are going over everywhere around it.
-
How are the security levels for websites ensured?
Understanding Web Services Security ConceptsThis section presents the Web administrations security ideas. It is separated into the accompanying segments:Anchoring Web ServicesHow Oracle Fusion Middle ware Secures Web Services and ClientsFor a prologue to general Web benefit ideas, see "What are Web Services" in Introducing Web Services.Anchoring Web ServicesIn view of its temperament (approximately coupled associations) and its utilization of open access (for the most part HTTP), SOA actualized by Web administrations includes another arrangement of prerequisites to the security scene. Web administrations security incorporates a few perspectives:Validation—Verifying that the client is who she claims to be. A client's character is confirmed in light of the accreditations introduced by that client, for example,Something one has, for instance, accreditations issued by a confided in expert, for example, an international ID (genuine world) or a keen card (IT world).Something one knows, for instance, a mutual mystery, for example, a secret word.Something one is, for instance, bio metric data.Utilizing a blend of a few kinds of qualifications is alluded to as "solid" confirmation, for instance utilizing an ATM card (something one has) with a PIN or secret key (something one knows).Approval (or Access Control)— Granting access to particular assets in view of a validated client's privileges. Privileges are characterized by one or a few qualities. A quality is the property or normal for a client, for instance, if "Marc" is the client, "meeting speaker" is the trait.Classification, security—Keeping data mystery. Gets to a message, for instance a Web benefit ask for or an email, and additionally the character of the sending and getting parties in a secret way. Classification and security can be accomplished by scrambling the substance of a message and jumbling the sending and getting gatherings' personalities.Uprightness, non revocation—Making beyond any doubt that a message stays unaltered amid travel by having the sender carefully sign the message. A computerized mark is utilized to approve the mark and gives non-renouncement. The timestamp in the mark keeps anybody from replaying this message after the lapse.Web administrations security prerequisites likewise include certification intercession (trading security tokens in a confided in condition), and administration capacities and imperatives (characterizing what a Web administration can do, under what conditions).As a rule, Web administrations security devices, for example, Oracle WSM depend on Public Key Infrastructure (PKI) situations. A PKI utilizes cryptographic keys (numerical capacities used to encode or decode information). Keys can be private or open. In a deviated figure display, the accepting party's open key is utilized to scramble plain-text, and the getting party's coordinating private key is utilized to decode the cipher-text. Likewise, a private key is utilized to make an advanced mark by marking the message, and people in general key is utilized for checking the mark. Open key testaments (or authentications, for short) are utilized to ensure the trustworthiness of open keys.Web administrations security necessities are upheld by industry models both at the vehicle level (Secure Socket Layer) and at the application level depending on XML structures.
-
Why didn't any colonial empire invade Thailand?
In fact, the British Empire and French Empire both threatened Thailand in the 19th century. The French in fact sent warships to Bangkok to demand a cessation of present-day Laos, which were given somewhat peacefully by King Chulalongkorn the Great.Franco-Siamese War - WikipediaSiam, Thailand at that time, lost many territories to both colonial powers. However, the state was able to maintain its independence. This was mainly due to diplomatic efforts of King Chulalongkorn or Rama V.King Chulalongkorn the Great or Rama VHis strategy was to use diplomacy for the two colonial powers to counterbalance each other. Simultaneously, he tried his best not to provoke these colonial powers, so that they did not have a casus belli to invade Thailand. For example, the King, who was taught by westerners since he was young, offered the westerners friendship and allowed them to negotiate trading treaties as they wanted, even though all of them were unequal treaties. Personally, I believe this is because he saw that many neighboring kingdoms refused the colonial powers’ demands, and were colonized one by one.Furthermore, he tried to ally with other European powers, including Prussia, and Russia to hinder the French and the British’s ambitions.King Chulalongkorn and Tsar Nicholas II of Russia. The photo was taken when King Chulalongkorn visited Petrograd.Simultaneously, he industrialized the country, abolished all archaic administrative systems, and reformed the government from within.However, both colonial powers still desired Siamese lands, so King Chulalongkorn decided to give the lands that the colonial powers wanted just to secure the country’s independence.With these strategies, the King managed to buy adequate time for global politics to change. In 1904, French Empire and British Empire stopped all their hostilities, and signed a treaty of agreement named Entente Cordiale - WikipediaThis agreement was very important to Thai history, because these agreements led both nations to disclaim the ideas of annexing Siamese territories.In Siam, the British recognised a French sphere of influence to the east of the River Menam's basin; in turn, the French recognised British influence over the territory to the west of the Menam basin. Both parties disclaimed any idea of annexing Siamese territory.Mainly, because of this reason, Siam was one of the few countries that were not colonized by the western powers, and managed to secure its independence.
-
What is your opinion on Saurabh Bhardwaj's EVM demo?
EVM is an Embedded device without any network connectivity.In General, any embedded device can be hacked predominantly in 3 ways.During System Boot upDuring firmware upgradeThrough network (if the device is connected to network or any ports are open to hack the device)1. Embedded devices will boot from Onboard/Onchip flash memories. After power up, the ROM boot loader or BIOS firmware will look for a secondary boot strap loader and copies it to system memory which in turn copies the application binary to the system memory. The current embedded devices implement what is known as Secure boot which authenticates the boot loader and also the firmware binary before loading to system memory. If by chance the device is hacked and a bad copy of firmware is stored in flash, then the secure boot fails and hence the device cannot come up. Most of the Present day embedded devices implement a Secure boot mechanism and hence they cannot be hacked during boot up.2. Embedded devices can be hacked during firmware upgrade (Locally or Remotely) by writing malicious firmware binary which corrupts the system. The present day embedded systems implement Secure firmware upgrade mechanism which authenticates the new firmware before writing to flash.3. Embedded devices can be hacked through network ports by injecting malicious packets. The present day systems implement SSL for network communication with external world and also block all the ports. The EVM’s don’t have any network connectivity and hence not possible to hack the device.So what are the possibilities of hacking EVM.The hacker can design his own custom firmware which can function as per his needs and can put the firmware in EVM. This option is ruled out in case of EVM assuming it has secure firmware upgrade implemented and also qualified/authorised people are allowed the firmware upgrade.The firmware loaded into the EVM may have some Secret logic which can be activated by pressing few key combinations! I am not sure if the firmware put into the EVM has any such secret logic and anyone is aware of that!EVM can have some default configuration (Say this configuration may contain some fixed votes for each party) which can be activated by some key press (Generally any embedded device can have a button for re setting to default configuration)So the point here is that, unless the EVM firmware has some secret logic which should be known to someone to activate, it is hard to break or manipulate the device. Else one needs to physically access the device memory using some JTAG port (Which will be blocked in production EVMS generally) and change the data/code in the memory to tamper the device!I am assuming that EVM should have implemented all the security features of the Embedded system as it used for high security application.So why AAP is doing this?Divert public attention from the Core issue of Bribery charges against Mr KejriwalThey want to feed a wrong information in the minds of public that EVM is not safe by repeatedly saying that and many educated people believed that this guy used actual EVM and is able to manipulate it so easily where as the fact of the matter is something different.Already EC has invited hackers to try and hack EVM. Let’s see if anyone can do it!
-
Why didn't President Trump make this major push for his border wall a year ago when he had a Republican majority in both the Hou
Let’s look at what was at the very top of the agenda for Trump and the Republican controlled Congress and Senate.$750 billion tax give away to the top 3% and corporations (which Paul Ryan received a $500,000 check from the Koch Brothers).Here’s the photo of the Republicans after passing their tax bill where their patrons made a killing.Their next task was crippling Affordable Healthcare Act, here’s the same team having a grand ole time laughing at the billions in profits handed back to insurance companies.Next they signed the repeal of the Dodd-Frank bill which protected average Americans from predatory financial practicesLook at the dripping glee oozing from these Republicans as the repeal is signed.Next up is the defense spending bill which increased the DOD budget to a WHOPPING $750 billion. The majority of the spending increases aren’t going towards soldiers, their families or the VA but to military contractors and additional purchasing which the Pentagon rejected time and time again. This doesn’t include the additional $65 billion Trump added to nuclear upgrades (something which was already budgeted for under the Obama administration, but he felt it important after his meeting with Putin in Helsinki). Keep in mind this is the budget put together by the Republican Congress which largely benefits the defense industries in their States, if you want to see the actual Pentagon recommendations they are posted on the Pentagon website. While the Pentagon has always complained about budget cuts, their budgets call for spending on troop spending, cutting out wasteful programs and dead technologies and base closures (something that would crush many Red States).Notice the not so happy faces in this room.Now you might be thinking by now what happened to border security, the Brown Horde has been raiding our borders, raping our women and dumping opioids on innocent white kids. Well there was additional few millions to hire more border agents and $2 billion addition for repairs to the existing border walls and barricades (which to date has been untouched because they’re still spending the money from the previous budget).Look at the priorities and numbers, if the border was such a crisis then there’s only two reason why we are where we are:Republicans don’t care about border security, their main priority was siphon out billions of tax dollars to their wealthy patrons.Republicans are incompetent and should never have control over the purse strings of this nation.
-
What are the costs weighed up against the benefits of SSO?
Here are several considerations around costs and benefits of Single Sign-On:Solution CostsInfrastructure - What servers, databases, and other IT infrastructure are required for the Single Sign-On solution? What is the cost of configuring, securing and maintaining them over time? What modifications are required to existing servers, domains, application servers, etc.? Licensing - What licenses are required for the Single Sign-On solution? Are additional licenses required for different types of functionality (two-factor authentication, self-service password reset, etc.)?Services - What is the cost of vendor services to set up and configure the solution?Authentication Devices - Strong authentication is typically paired with Single Sign-On. What is the cost of biometric devices, proximity/RFID readers, OTP tokens, etc.?Applications - How complex is application enablement for Single Sign-On? Is there a fee per application enabled, or limits on how many applications can be enabled?Training - What training is required for administrators to manage and support the solution? What training is required for help desk staff and end users?Administration - How complex is the solution to manage and deploy? How many client/server components need to be maintained for various functions (strong authentication, SSO, application profiling, auditing, self-service password management, etc.)?Support & Maintenance - What are the annual costs for vendor support and maintenance for the solution? What are typical costs of upgrades and how often are they required?Solution BenefitsImproved Ease/Speed of Access - Users experience much faster access to applications without having to manually enter credentials into each application. Single Sign-On can also be used to streamline user access to virtual desktops or hosted environments.Improved User Productivity - Not having to deal with passwords translates to time savings and increased productivity.Increased Security - Strong authentication options and better desktop security (such as automatic desktop locking), as well as reduction/elimination of passwords being shared or written down.Improved Auditing - Ability to track application usage, shared workstation access, reveal users sharing credentials, etc.Reduced Help Desk Calls - Implementing Single Sign-On and self-service password reset will reduce password reset calls. While these benefits may seem somewhat intangible, customers I've worked with who have implemented Single Sign-On have found concrete ROI. For example, IDC Health Insights published a report of Johns Hopkins Hospital implementation of Single Sign-On and "Tap and Go" authentication using proximity badges, which states:Johns Hopkins estimated signNow time savings by users since thedeployment of Tap and Go to date, with time savings in September2012 alone estimated at 2,550 man-hours... consistent with the timesavings reported in July and August 2012, the initial months of theimplementation. Provider satisfaction with the EHR also grew alongside productivity, according to the leaders of the project. Theimplementation of single sign-on presented a clear win for JohnsHopkins clinicians and IT...Source: Best Practices: Single Sign-On Drives Productivity, Security, and Adoption When Used with EHR at The Johns Hopkins HospitalThe balance between costs and benefits is a key consideration when looking at Single Sign-On as a solution. But the biggest drivers for adoption I've seen are often user frustration, and the need to comply with increasing security standards. These are harder to quantify financially, but put Single Sign-On at the top of many IT priority lists.
-
What are some of the biggest misconceptions about U.S. immigration laws?
The “biggest misconception” for me is the notion that any sort of relief for some group of hopefully-immigrant aliens (such as, say, childhood arrivals, or Haitian TPS beneficiaries) necessarily “takes the spot” that could have otherwise gone to an Indian who has been patiently waiting “in line” for years. The reality is that the number of immigrants authorized by law to enter the United States is set by Congress according to its own ineffable political whims. A decision by Congress to allow a million childhood arrivals to normalize status and obtain green cards in no way impacts the ability of Indian employment-based immigrants to immigrate, unless, of course, Congress decides that it should. The only thing that decides what is and is not possible is what can be argued for politically. Congress can, of course, cause this to happen, as it did with the thousands of Chinese students who were allowed to immigrate expeditiously after Tiananmen Square. Congress imposed a permanent reduction on the number of employment-based visas available to immigrants chargeable to China to “account for” the extra 54,000 green cards that were handed out as a result of the Chinese Student Protection Act of 1992. But that was a political decision; the only thing that “mandated” it was the decision of Congress to impose that mandate. Congress can do pretty much anything it wants in this area.A related issue is the idea of requiring childhood arrivals to “go to the end of the line”, as if there were just one giant line that everyone stands in. In fact (as the chart that Kathryn Berck included in her answer demonstrates) there are a plethora of lines. If you count separately for each chargeability area and preference category, there are literally thousands of lines, as there are some 250 chargeability areas and over a dozen preference classes. Also, an individual can actually be waiting on multiple lines at the same time. So, what line does a childhood arrival go to the end of, when their status doesn’t correspond to any existing preference class? Do you make every last childhood arrival wait until every last person waiting for a visa number gets one? That will literally never happen, unless Congress does something very improbable (politically) like hugely increase the worldwide numerical limit, along with increasing or eliminating the 7% per country limit; otherwise, it’ll still be decades before all the family-based petitions out of Mexico get visa numbers. I truly do not know what “go to the end of the line” means in the case of relief for childhood arrivals, and yet a signNow number of people use this phrase in describing how such relief should be structured. Even a lot of immigrant aliens don’t know what a “priority date” is. After all, those who immigrate as the immediate relative of a US citizen—nearly half of all immigrants—do not have to deal with priority dates at all.There’s one other that immediately comes to mind: the widespread confusion between a visa and a residency permit. A visa, in the US and in many other countries, is simply permission to ask to be permitted to enter the country. The visa itself grants no permission to actually be in the country; once you’ve entered the country, the visa itself is largely useless. Some countries actually stamp a “residency permit” into the alien’s passport, or issue a physical document that is actually called a “residency permit” or some other comparable term. The United States used to issue to nonimmigrant aliens a paper document, called an I-94 “Record of Entry”, that served as evidence that an alien had lawfully entered the country and was permitted to be present for some limited time indicated thereon. While not actually called a “residency permit”, it serves the same purpose. For various reasons, such documents are now issued electronically in essentially all cases, but the purpose remains the same. The misconception here is that an alien has to have an unexpired visa to be present in the United States, when in fact it’s the I-94 record of entry that controls a nonimmigrant alien’s right to be present. The visa is irrelevant.
-
Do people who call for Trump's impeachment realize that Pence would then become president?
I am diametrically opposed to nearly every stance that Pence holds. But I don’t think that Trump has the temperament for the job. The GOP and his more rational supporters kept telling us that he’d step up to the job and stop the ludicrous parts of his campaign once he was sworn in but he’s not. He’s now saying things as the POTUS that are scary to the core of our Republic.The voter fraud things that he keeps harping on because he really is thin skinned and can’t accept that he won but lost the popular really chips away at our democratic values. We all knew that if he lost he’d run around with accusations of voter fraud but HE WON and is still talking about voter fraud. Maybe he’s an evil genius and this is his plan to suppress voters in the future but it really appears that he’s just upset that he didn’t win the popular vote. In any case it’s dangerous. We had a peaceful transition of power. He needs to get over it.I don’t even know how much of this is true but I was at the gym this morning (maybe yesterday) and on the tv’s there were headlines of his Tweet saying he wants to send the Feds into Chicago if crime rates aren’t reduced. Is he really threatening to take over a city with the “Feds?” Chicago has its problems but where does he stop? Suspending posse comitatus so that a place that he can send in troops to a place that he disagrees with? I don’t put it past him, especially with a Congress that’s either a rubber stamp because they want to pass their conservative agenda or that’s too frightened of his popularity with their base.Since Tweeting seems to be the primary way he communicates with us, how are we to know what is real and what isn’t? Maybe it’s his spin machine: the more outlandish stuff he says the more he can get away with anything because the collective we can’t keep up. That’s not a way to govern this country. God forbid when the first international incident occurs and he responds to it with an off the cuff Tweet that he hasn’t even thought about, let alone consulted any of his advisors about what actually happened or a sound course of action.I don’t live in the world of hyperbole wearing a tin foil hat but these are just a few examples of things I find incredibly frightening about Trump. Past Presidents didn’t do these things because they were decent human beings who respected the Office and the democratic ideals of this country. Trump doesn’t seem to. For all that I find abhorrent about Pence, his views and his policies, I think he has the decency and common sense that the office requires. Trump’s going to advance the agenda that Pence will anyway-that’s the conservative agenda they’ve wanted all along-but I think he at least isn’t off his rocker.
-
How do Quora Users feel about the Republican Party's so-called War on Women?
I was asked to answer this question, which is why I am doing it.Women, feminism, and every type of right that women have has been under attack for quite some time now.I have written about it. One of the reasons for this is young educated women do not stand up for their own rights.They also do not stand up for other women. In sports, two women Jenn Sterger and Ines Sainz were attacked when it became known that they were allegedly harassed by a famous athlete or athletes. They are both incredibly beautiful and sexy women and they were some hot outfits. In both cases, neither Sterger or Sainz complained about the alleged harassment. They knew better to do that. Other people complained for them. They were attacked, viciously by the sports media. Called whores, gold diggers, etc., not just by the male sports media, but by female sports media, as well.Famous or well known female sports writers and/or broadcasters made comments like: "They are at fault." Or "If you dress like a professional, you will be treated like a professional." I decided, at that time, to take up for Sterger and Sainz, because it appeared to me they were both victims of a village stoning. Also, at that time I thought it was my job to tell people who were acting like assholes that they were assholes. One famous woman sportswriter wrote something like, "Nothing like this has ever happened to me." To which I wrote, "I don't know what planet you are living on, honey." I basically wrote that these women were slitting their own throats and mine and that they should shut the fuck up. (I don't curse on Twitter, only on Quora.)But that was then, before I decided to become Zen and that it was not my job to tell people anymore that they are assholes. If that situation occurred now, I don't know what I would do because I am supposed to avoid conflict with people. Although I am allowed to step in and fight for those who can't defend themselves, like children, animals, dead people and victims of a village stoning. But you asked about Republicans. I do not pay attention to the Republicans and what they are doing. I assume they will take away women's rights, or most certainly they will take the rights of poor, uneducated women. They will do this with impunity because women in their 20s, even the ones educated at Stanford, Berkeley, and all the Ivy League schools who are here on Quora are afraid to proclaim themselves feminists. This is probably because men don't like women who do this, or this girls (as they like to call themselves) believe men won't like them if they do this. (I have always done what I wanted to do and I didn't care if men liked me or not.) I have no control over what the Republicans are doing. I have no control over what smart young women, like the ones on Quora, are doing or the fact they are throwing away their rights with both hands. I assume it will be every woman for herself, which is what it has been in the sports industry in the United States since the beginning of the sports business. I do fine in that situation, so nothing really will change for me. Oh, and my only child is a male child, which I am very thankful for. Perhaps his generation will stick up more for wornen than the current one. Hope so, but have no control over that. Peace.
Trusted esignature solution— what our customers are saying
be ready to get more
Get legally-binding signatures now!
Related searches to Sign Presentation for Administrative Secure
Frequently asked questions
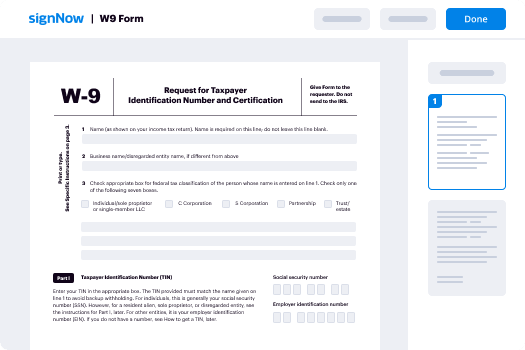
How do i add an electronic signature to a word document?
When a client enters information (such as a password) into the online form on , the information is encrypted so the client cannot see it. An authorized representative for the client, called a "Doe Representative," must enter the information into the "Signature" field to complete the signature.
How to create an electronic signature pic?
it/PV4eVY — Donald Trump Jr.'s Lawyer (@mandy_cooper13)
Trump Jr. also sent the email after news broke that former acting Attorney General Sally Yates had alerted the White House that Flynn might have lied about discussing sanctions with then-Russian ambassador Sergey Kislyak.
The White House, which initially said that Trump didn't know any details about Flynn until he learned about it later — then said that the president only found out about them through media reports — has faced questions about why Trump's son was seeking to establish communications with the Russian government in the first place.
In a series of tweets, Trump Jr. denied that he and others had received the emails, and called the Times story "a COMPLETE and TOTAL FABRICATION" of his meeting. He said the Times' "fictional account" was "100% made up."
This morning's NY Times Magazine cover: "How Vladimir Putin Created Donald Trump." — Donald Trump Jr. (@DonaldJTrumpJr)
Flynn's resignation Monday came the same day that he was interviewed by FBI agents about the meeting — as part of Robert Mueller's probe of Russia's meddling in the US presidential election.
How to fix when you cant sign into you e-mail account galaxys5?
If you have a website you want to advertise, you can use our advertising service. Our advertising service will help you generate revenue online so you will be able to afford your hosting fees.
Can i use my existing website/website with this site?
Sure! If your website already has a forum or a blog you can simply create a new one, and host it yourself on our dedicated hosting servers.
When should I contact you?
If you have questions or want to discuss any of the topics outlined in this FAQ page just email us on support@ In addition we do have an onsite support staff that can help with your questions.
Can i upload my own images or videos?
Yes, as long as they meet our upload and streaming standards, we will do our best to upload them to you as soon as possible.
Get more for Sign Presentation for Administrative Secure
- Help Me With Electronic signature Montana Sports PDF
- How Can I Electronic signature Montana Sports PDF
- Can I Electronic signature Montana Sports PDF
- How Can I Electronic signature Montana Sports Word
- How To Electronic signature Montana Sports Word
- How To Electronic signature Montana Sports Word
- How Do I Electronic signature Montana Sports Word
- Can I Electronic signature Montana Sports Word
Find out other Sign Presentation for Administrative Secure
- Exam evaluation form
- Letter of termination dps texas form
- Script in the copperplate style pdf download form
- Major change form the university of texas at dallas utdallas
- Minor road traffic accident form alahliaoman com
- Loyalsock pool form
- How to write a waiver letter for immigration form
- Gems formulary
- Form to request release of patient information alabama medicaid medicaid alabama
- Climate neutral checklist elmbridge borough council elmbridge gov form
- Flood control permit application san bernardino county sbcounty form
- Form 363t
- Prenuptial agreement virginia form
- Walter r courtenay award middle tennessee council mtcbsa form
- Academic program review template form
- Providence portland clinical ladder form
- Av 9 department of revenue form
- Domestic relations initiation packet fulton county superior court form
- Additional vocabulary support answers form
- Geoactive online geography departmant of lwc home geographylwc org form