Add eSignature Presentation Computer
Make the most out of your eSignature workflows with airSlate SignNow
Extensive suite of eSignature tools
Robust integration and API capabilities
Advanced security and compliance
Various collaboration tools
Enjoyable and stress-free signing experience
Extensive support
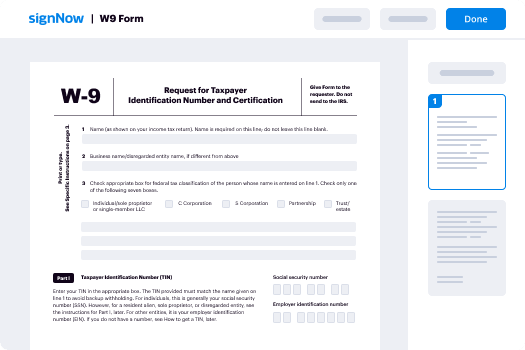
How To Add Sign in eSignPay
Keep your eSignature workflows on track
Our user reviews speak for themselves






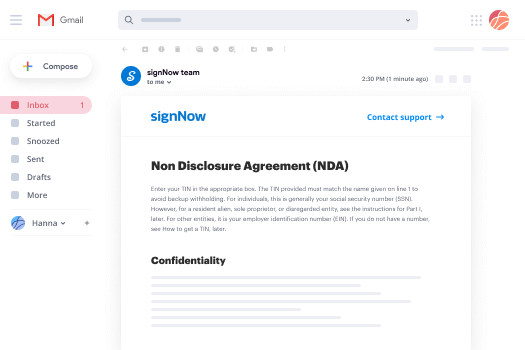
Add eSignature Presentation Computer. Discover one of the most customer-warm and friendly knowledge of airSlate SignNow. Deal with your complete file processing and discussing system digitally. Go from hand-held, document-dependent and erroneous workflows to programmed, computerized and faultless. It is simple to generate, produce and indication any documents on any product anywhere. Ensure that your crucial organization cases don't fall overboard.
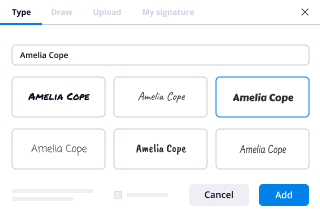
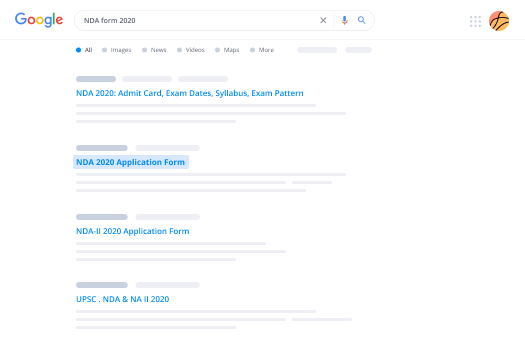
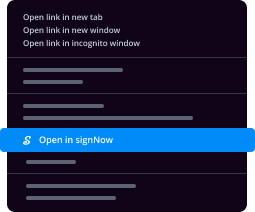
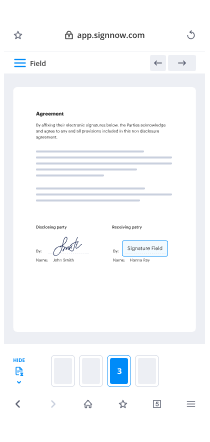
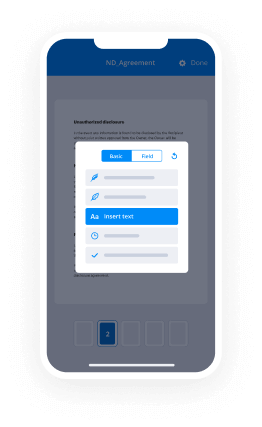
See how to Add eSignature Presentation Computer. Follow the straightforward information to begin:
- Design your airSlate SignNow account in mouse clicks or log on with the Facebook or Google accounts.
- Enjoy the 30-day time free trial or choose a prices prepare that's ideal for you.
- Locate any legitimate format, build on the web fillable types and reveal them tightly.
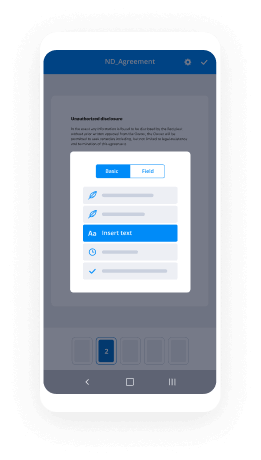
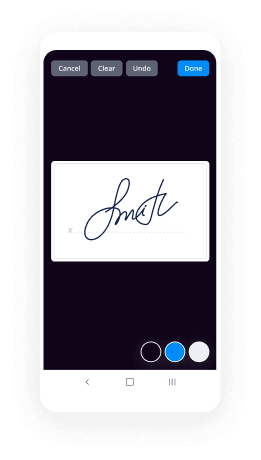
- Use superior functions to Add eSignature Presentation Computer.
- Indicator, modify putting your signature on buy and gather in-man or woman signatures 10 times quicker.
- Established automatic reminders and acquire notices at every move.
Shifting your activities into airSlate SignNow is straightforward. What comes after is a simple procedure to Add eSignature Presentation Computer, as well as recommendations to maintain your colleagues and partners for greater alliance. Encourage your staff using the greatest tools to remain on top of organization operations. Improve productiveness and level your small business faster.
How it works
Rate your experience
-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
Intuitive UI and API. Sign and send documents from your apps in minutes.
A smarter way to work: —how to industry sign banking integrate
FAQs
-
What is the best real estate technology?
A survey conducted by Coldwell Banker and CNET found that eighty-one percent of prospective home buyers were drawn to homes equipped with the latest in-home technology. Among those, thirty-five percent of people who preferred what is known as smart homes over traditional residences believed that such features solidified the property as “move-in ready.”Technology is also changing the field of home selling. Here are five ways that apps and other online features are making the life of a real estate agent easier.1. Broadcasting with Periscope and TwitterWhat better way to send out a massive blast than on Twitter? The social media site lets you keep it short but sweet as you tell followers that the home of their dreams has an upcoming open house session. You can also post pictures on Twitter that give potential buyers a better perspective of what they will see during their in-person tour of the property. Take the virtual showing a step further by using Periscope to share live footage of yourself walking through the house online. In past times, a substantial amount of money was necessary to promote property by way of commercials. Twitter and Periscope bring the perk to you for free so long as you have a smartphone or tablet when going live and taking pictures.2. Tracking with Glympse and WazeRunning twenty minutes behind used to be a deal breaker pre-Digital era. Not only did you inconvenience the client but you also provided a guess that was often inaccurate and led to more time wasted at the property. Traffic apps in the twenty-first century have made such estimating unnecessary.Waze is one app that provides navigation tips based on real-time traffic information. You can better coordinate appointments so that clients are not left waiting for several minutes and provide clearer updates when you are running late. Glympse also tracks traffic in real-time but takes things a step further by offering a link by which clients can track your whereabouts. Text or email the URL to prospective buyers and let them follow along as you make your way to the location.3. Meet Online with Reflector 2 and Join.meReal estate agents should consider investing in Reflector 2 instead of bringing their USB stick along to nail that next listing presentation. The app serves as a sort of projector by allowing you to cast all activity on your smartphone and tablet on a larger screen. The Reflector 2 works with nearly any device and does not require additional purchase outside of the app itself.Free Screen Sharing, Online Meetings & Web Conferencing is another app that has made buying a selling a home more convenient. Agents can hold brief meetings with clients without requiring them to come into the office. Sharing your computer screen is the best way to convey pertinent information to new homeowners. The recording and playback feature is particularly useful when you need to recall a client’s home preferences. They will be impressed with your attention to detail in finding a house with a built-in barbecue pit. You will know that such meticulousness is because of Free Screen Sharing, Online Meetings & Web Conferencing.4. Add Transparency and Rapidity with an Automated Mortgage Loan ProcessThe traditional method of the home loan process involved hours spent trying to secure financing. Leaving one paycheck stub or bank statement at home often meant holding off on the process until the client was able to furnish proof of such documentation. There was no transparency in the process, which meant that customers were entirely reliant on the expertise of the real estate agent.Technological advances have revolutionized the mortgage loan process. Automated processing now establishes criteria by which applicants are judged that makes applying simpler. Some financial institutions can pre-approve hopefuls in ten minutes. Individuals who go through the entire process may see their loans finalized in ten days instead of the average four-week period. Digital tools provide real-time updates so that even those who are not approved can move on to the next bank quickly instead of waiting for a rejection letter to arrive by way of snail mail.5. Agree from Home with E-signaturesIn past times, the thrill of closing quickly became inconvenient for buyers upon hearing that all approved owners would need to stop by the real estate agent’s office to sign final documents. Some individuals were forced to take a sick day from work just to make their mark on the paper. Such heartache is why the masses are thrilled to learn that e-signatures have the same weight as traditional marks on legal documents. A real estate agent can email paperwork that his clients can sign at their leisure and return electronically. It is even possible to solidify documents on a smartphone in some instances, which makes the home loan process that much more convenient.
-
What digital tool, as a real estate agent, do you most use?
As an agent, we have access to the MLS, which the public only has limited access to. In my area the public can see exactly what Zillow can which is active listings. Our board does not disclose the sales price of closed prices, which makes services like Zillow pretty much worthless in my area. (Zillow may be useful in some areas, perhaps many, just not where I work).That said, my favorite and most useful tool, which is also available to the public, is the GIS (Government Information Service). Type in to Google: (Your county)(Your state) GIS [ie: Marion County Indiana GIS ] . While it isn’t available in every county of the country, you will find it in most major areas. It will give you access to the tax assessor records and often times the sales history of the property. The tax records will give you the details of site size, improvements, assessed values and depending on the county may or may not give you the annual taxes.Since real estate agents in some areas count the basement area when they list the size of the property, the GIS will allow me to figure out what is really there if I’m new to the area. For what I am looking for, there is a signNow difference between a stated 3,600 square foot house by the agent and 1,800 square foot above ground over a 1,800 square foot basement. - Lenders only count the above ground square footage as living area when making a loan.Hope this helps.
-
What is the best invoicing app for small businesses?
SeisoRidh-Billing Acoounting Softwarefor demo click hereKey Features:Multiple Business/Shops:Set up multiple businesses in the application.No restriction on numbers of businesses.Inventory & accounting information is kept separately for each business.Add Location / Storefronts / Ware House:Create multiple locations for your business/shopManage all of them at the same time.Stocks, Purchases, Sell can be tracked differently for locations.Customize invoice layout, invoice scheme for each locationUser & Role Management:Powerful user and role management systemPredefined roles – Admin & CashierCreate different Roles with permission as per your need.Create unlimited users with different roles.Contacts (Customer & Suppliers):Mark contact as customer or supplier or both(customer & Supplier)View details of transactions with a contact.View total of Credit/Debit balance amountDefine pay term and get payment alerts week before the due date.Products:Manage Single & Variable products.Classify products according to Brands, Category, Sub-Category.Add products having different unitsAdd SKU number or auto-generate SKU number with prefixes.Get stock alerts on low stocks.Save time by auto calculating selling price, the system is smart to auto calculate selling price based on purchase price and profit margin.No need to type variations every time, create variation template and use it everytime you need to create variable products.Purchases:Easily add purchases.Add purchase for different locations.Manage Paid/Due purchases.Get Notified of Due purchases week before the pay date.Add discounts & TaxesSell:Simplified interface for selling productsDefault Walk-In-Customer automatically added to a businessAdd new customer from POS screen.Ajax based selling screen – save reloading time.Mark an invoice for draft or final.Different options for payments.Customize invoice layout and invoice scheme.Manage Expenses:Easily add business expensesCategorise expensesAnalyse expenses based on category and business locations with expenses report.Reports:Purchase & Sale reportTax ReportContact ReportsStock ReportsExpense ReportView Trending Products, drill down by Brands, Category, Sub-category, Units and date rangesOther useful feature:Set currency, timezone, financial year, the profit margin for a business.Translation ready.Predefined barcode sticker settings.Create your barcode sticker settingManage Brands, Tax Rate & Tax groups, Units, Category & Sub-CategoryEasy 3 steps installation.Detailed documentation
-
What is a good iPhone invoicing app for a startup marketing company?
Disclaimer: I am the founder of Invoice by Alto.Alto brings desktop-class invoicing and time tracking functionality to mobile devices. The app enables small businesses and freelancers to track billable hours, send estimates and invoices and get paid. Users can choose from five invoice template options to suit their brand images. The Alto Timer companion app makes it possible for users to track billable time on the fly and then bill for it instantly by email. Alto can work for individuals or teams. The app features integration with Stripe, Square and Paypal to make Alto a payment processing app that can collect funds from clients. Integration with Dropbox, Github, and Photos enables the user to reference files, documents, images, code commits and other items needed to support an invoice. AddressBook integration simplifies setup and streamlines the invoicing process. A built-in set of animated visual charts give the user visibility into business statistics.http://www.alto.co
-
What is a good free software for keeping track of invoices and expense for a small business?
Hi,Invoicing and expense tracking is one of the biggest aspects of managing a business and its finances. And yet, small business owners make some grave mistakes when it comes to invoicing and they suffer the actions of their consequences.One such mistake is not investing in a robust cloud-based invoicing software which costs less with a pay-as-you-go model.This cloud-based accounting and invoicing software have invoicing features like:Ability to send invoices anywhere you are using any device,Ability to customize invoices and make them look beautiful to wow the customers.Ability to add multiple payment avenues(net banking, debit card, credit card, payment gateways, etc) within the invoices that saves time.Ability to track unpaid invoices and send automated reminders once the due-date is met and the invoices remain unpaid.Ability to send invoices on a recurring basis.Some of the best invoicing, expense management and overall accounting software today are not free but they offer high bang for buck with their features and support. They are listed below:GiddhQuickbooksZoho invoicesProfitbookBearbookSage
-
What is the best invoicing software that has a mobile app?
Since last 10 years Spectrum POS is one of the best invoicing software that has a mobile app MOBEX for any retail business. A most innovative invoicing software and complete solution to run your business in a better way at your location. According to latest trends & technology, now latest version of Spectrum POS has changed the features in a better performing way and have added new features for more performance. It offers Invoicing, Inventory, CRM, Payments and E-commerce for your business. This invoicing software mobile app works on any hardware including your mobile phone, tablet or lapto...
-
How are cracked versions of software created and why are developers not able to prevent it?
Cracked versions of software are created with the use of debuggers. (A debugger is a special type of software that lets programmers deconstruct their software into its constituent parts for the purpose of finding bugs, and thus de-bugging. Additionally debuggers can be used for reverse-engineering, or to see what is inside the software, to learn its logic. The latter method is used mostly by malware researchers to study what malware (or computer viruses) do on-the-inside. But it can be also used by an attacker to "crack" (or bypass) legal software registration, or at times, to alter normal behavior of software, for instance by injecting a malicious code into it.)For the sake of this example, I will assume that the software that is being "cracked" was compiled into a native code, and is not a .NET or a JavaScript based application. (Otherwise it will be somewhat trivial to view its source code.) The compiled native code is a bit more tricky "beast" to study. (Native means that the code executes directly by the CPU, GPU, or other hardware.)So let's assume that the goal of an attacker is to bypass the registration logic in the software so that he or she doesn't have to pay for it. (Later for lolz, he or she may also post such "crack" on some shady online forum or on a torrent site so that others can "use" it too and give him or her their appreciation.)For simplicity let's assume that the original logic that was checking for the software registration was written in C++ and was something similar to the following code snippet:In this code sample "RegistrationName" and "RegistrationCode" are special strings of text that a legitimate software user will receive after paying for the license. (The name is usually that person's actual name or their email address, and the code is some string of unique/special characters that is tied to the name.)In the logic above, the function named "isRegistrationCodeGood()" will check if "RegistrationName" and "RegistrationCode" are accepted using some proprietary method. If they are, it will return true. Otherwise false. That outcode will dictate which branch (or scope) the execution will follow.So the logic above will either show that registration failed and quit:Or, if the registration code and name matched, it will save the registration details in persistent storage (such as the File System or System Registry) using the function named "rememberRegistrationParameters()" and then display the message thanking the user for registering:A "cracker" will obviously want to achieve the second result for any registration code that he or she enters. But they have a problem. They do not have the C++ source code, part of which I showed above. (I hope not!)So the only recourse for an attacker is to disassemble the binary code (that always ships with software in the form of .exe and .dll files on Windows, and mostly as Unix executables inside the .app packages on a Mac.) An attacker will then use a debugger to study the binary code and try to locate the registration logic that I singled out above.Next you can see the flowchart for a snippet of code that I showed in C++, presented via a low-level debugger. Or, as the code will be read in the binary form after compilation:(For readability I added comments on the right with the names of functions and variables. They will not be present in the code that an attacker could see.)(To understand what is shown above an attacker will have to have good knowledge of the Assembly language instructions for the native code.)I also need to point out that having a disassembly snippet like the one above is the final result for an attacker. The main difficulty for him or her is to locate it among millions and millions of other similar lines of code. And that is their main challenge. Not many people can do it and that is why software "cracking" is a special skill.So having found the code snippet above in the software binary file a "cracker" has two choices:1) Modify (or patch) the binary.2) Reverse-engineer the "isRegistrationCodeGood()" function and copy its logic to create what is known as a "KeyGen" or "Key Generator."Let's review both:The first choice is quite straightforward. Since an attacker got this far, he or she knows the Intel x64 Instruction Set quite well. So they simply change the conditional jump from "jnz short loc_7FF645671430" at the address 00007FF645671418 (circled in red in the screenshots) to unconditional jump, or "jmp short loc_7FF645671430". This will effectively remove any failed registration code entries and anything that the user types in will be accepted as a valid registration.Also note that this modification can be achieved by changing just one byte in the binary code from 0x75 to 0xEB:But this approach comes with a "price" of modifying the original binary file. For that an attacker needs to write his own "patcher" (or a small executable that will apply the modification that I described above.) The downside of this approach for an attacker is that patching an original executable file will break its digital signature, which may alert the end-user or the vendor. Additionally the "patcher" executable made by an attacker can be easily flagged and blocked by the end-user's antivirus software, or lead criminal investigators to the identity of the attacker.The second choice is a little bit more tricky. An attacker will have to study "isRegistrationCodeGood()" function and copy it into his own small program that will effectively duplicate the logic implemented in the original software and let him generate the registration code from any name, thus giving any unscrupulous user of that software an ability to register it without making a payment.Vendors of many major software products understand the potential impact of the second method and try to prevent it by requiring what is known as "authentication." This is basically a second step after registration, where the software submits registration name to the company's web server that returns a response back to the software of whether the code was legitimate or not. This is done by Microsoft when you purchase Windows (they call it "Activate Windows") and also by signNow, and many other companies. This second step may be done behind-the-scenes on the background while the software is running, and will usually lead to cancellation of prior registration if it was obtained illegally.So now you know how software is "cracked".Let me answer why it is not possible to prevent it. It all boils down to the fact that any software code needs to be read either by CPU (in case of a binary native code) or by an interpreter or a JIT compiler (in case of JavaScript or .NET code.) This means that if there's a way to read/interpret something, no matter how complex or convoluted it is, an attacker with enough knowledge and persistence will be able to read it as well, and thus break it.There is an argument though that cloud-based software is more secure, which is true, since its (binary) code remains on the server and end-users do not have direct access to it. And even though cloud-based software is definitely the future, it has some major drawbacks that will never allow it to fully replace your conventional software. To name just a few:Not everyone has an internet connection, or is willing to upload their data online. Additionally someone’s internet connection can be very expensive or too slow to make the software run very laggy.Then there’s a question of distributed computing. For instance, Blizzard Entertainment would never make “World of Warcraft” to fully run on their servers due to immense computational resources needed to render every single scene for every player they have. Thus it is in their best interest to let each individual user’s computer to do the rendering instead.As a software developer myself, I obviously don't like when people steal software licenses. But I have to accept it and live with it. The good news is that there are not that many people who are willing to go extra mile and search for a cracked version of software. The main problem for those who do, is that by downloading a patched executable, or an attacker's KeyGen or a Patcher, they are effectively "trusting" him or her not to put anything "nasty" into it that was not "advertised on the package" (stuff like trojans, malware, or keyloggers.) So the question for those people becomes -- is it worth the cost of the software license to potentially infect your system with a nasty virus?On the other side of the equation, some developers react very negatively to any attempts to steal their software licenses. (I was there too.) They try to implement all kinds of countermeasures -- anything from tricking reverse-engineers, to adding booby traps in the code that may do something nasty if the code detects that it is being debugged, to obfuscating or scrambling the code, to enforcing all kinds of convoluted DRM schemes, to blocking users from certain countries. I personally try to stay away from all of those measures. And here's why:A) Any kind of anti-reverse-engineering tactics could be bypassed by an attacker with enough persistence. So why bother and waste my time when I can invest that time into adding something useful to my software that will make it more productive for legitimate users?B) Some code packers could create false positives with antivirus software, which is obviously not good for marketing of that software. It also creates unnecessary complexity for the developer to debug the software.C) Adding booby traps in the code can also “misfire” on your legitimate users, which will really infuriate them and can even lead to lawsuits.D) Any DRM scheme will probably catch some 100 illegal users and greatly inconvenience 10,000 legitimate ones. So why do it to your good customers?E) Our statistics show that about 75% of all illegal licenses come from China, Russia, Brazil, to name the worst offenders. (I also understand that the reason may be much lower incomes that people have in those countries.) The main issue for us though was the fact that if we enforce our DRM or add some strong registration authentication, many people that wanted to bypass our registration would simply use a stolen credit card number. And we had no control over it. Our system will use it to send them a legitimate license only to have the payment bounce in weeks time. As a result we would lose the money that were paid for the license, plus the credit card company will impose an additional chargeback fee to our account, which may range from $0.25 to $20 per bad purchase on top of the license cost.F) As was pointed out in the comments, some companies may actually benefit from allowing pirated copies of their software. Microsoft for instance gets a lot of free publicity from people using their Windows OS, the same goes for signNow with their Photoshop. That is a good point that I agree with.So my philosophy is now this -- if someone wants to go extra mile and steal our software, go for it! They went this far to do it anyway, so they probably have a good reason. On the positive side there are so many other customers that appreciate the work that goes into creating software that greatly outnumber those that don’t.PS. Thank you for all your feedback! It makes me feel good that the knowledge I shared is useful to others.
-
As a computer science student, what can I learn right now in just 10 minutes that could be useful for the rest of my life?
Have you ever felt that something(like taking backup of files, deleting old files etc.) should automatically happen when you connect your pen-drive to your system?Let us take an example, Suppose your teacher wants you to copy your assignments into his pendrive in front of him. The pen drive contains your final examination paper. You want your ubuntu system to automatically copy all the data from that pen drive to your hard disk automatically in the background (without even opening a copy dialogue). Here is how to do it on ubuntu:1] First let us write a simple shell script which we want to execute whenever a pen drive is connected to our system. Let us write a simple script which copies all data from the connected device to your home directory.First open a new fileemacs $HOME/script.shand add following lines to that file.#!/bin/bash sudo mkdir -p /tmp/test sudo mkdir -p $HOME/device_data sudo mount /dev/sdb1 /tmp/test sudo cp -r /tmp/test/* $HOME/device_data/ sudo umount /tmp/test Save and close the file.This script essentially creates a new directory named "device_data" inside your home folder and copies all the data from the pen drive into device_data directory.(Note: You can write ANYHTING into this script, so use it wisely :P)Now let us make this script executable.sudo chmod +x $HOME/script.sh As this script needs sudo permissions, we need to make it sudo runnable. To do this add the name of the script into sudoers file.Open sudoers file.sudo visudo -f /etc/sudoers Now after the 25th line (%sudo…) add this line
ALL=(ALL) NOPASSWD: /home/ /script.sh So now this script will run with sudo rights but will not ask for password! :)2]Now we need to tell our system to follow OUR rules (i.e execute our script) whenever a pendrive is connected. For this we need to create our own "udev rules" file. This file should be created in '/etc/udev/rules.d' directory.cd /etc/udev/rules.d Open a new file (with sudo rights):sudo emacs 91-myrules.rules Make sure the file name starts with "91". This gives your rules priority over other rules.Now add these lines into that fileACTION=="add", ATTRS{idVendor}=="****", ATTRS{idProduct}=="****", RUN+="/paht/to/your/script.sh" Make sure you enter proper path into RUN variable.Done!!Now plug any pendrive into your system and test this!Note: 1] When you connect your external drive this script will be run and your system won’t be able to use it unless this script execution is complete! So have some patience! :p 2] This answer is written for educational purposes only! Do not misuse it.Thanks Mehak Sharma for promoting the answer! -
Can I get a personal loan to purchase a computer?
Technically, I'm sure you can.But do you really want to have a computer without actually owning it, and end up paying nearly twice as much for the computer?Let say you get a loan for $60 a month.plus interest.plus a 33% interest charge when you don't pay a bill one month..It turns out to be more like $84 a month for a computer.Over a year long period, so you'll he paying $1,008 for a computer you could have bought in almost half the time for only $640.Only difference is, you saved your $90 a month instead of taking out a loan to do so.If you like living as an indentured servant to others, check with your bank that you primarily use.
Trusted esignature solution— what our customers are saying
Get legally-binding signatures now!
Related searches to Add eSignature Presentation Computer
Frequently asked questions
How do i add an electronic signature to a word document?
How to esign a filable pdf file?
How to eSign liberty mutual policy?
Get more for Add eSignature Presentation Computer
- How To Electronic signature Iowa Real Estate PPT
- How Do I Electronic signature Iowa Real Estate Document
- How To Electronic signature Iowa Real Estate PPT
- How Do I Electronic signature Iowa Real Estate PPT
- Help Me With Electronic signature Iowa Real Estate PPT
- Help Me With Electronic signature Iowa Real Estate Document
- How Can I Electronic signature Iowa Real Estate PPT
- Can I Electronic signature Iowa Real Estate PPT
Find out other Add eSignature Presentation Computer
- Formulario esan
- Caravan booking form template
- Introductory statement form moh
- Etisalat elife bill view form
- Saudi arabia visa application form sample
- Modulo ap23 da scaricare form
- Ncdva 12 form
- Greg secker books form
- Protective asset protection reviews form
- Oklahoma dv plates form
- Release of lien bond form
- Ohms law worksheet form
- Ameristar shuttle form
- Medication administration form pdf
- Pairs cricket score sheet form
- Dbl 5430 form
- Vernon native housing application form
- Nx 12 tutorial pdf download form
- Disposition form
- Biographical data sheet form