Add eSignature Presentation Now
Make the most out of your eSignature workflows with airSlate SignNow
Extensive suite of eSignature tools
Robust integration and API capabilities
Advanced security and compliance
Various collaboration tools
Enjoyable and stress-free signing experience
Extensive support
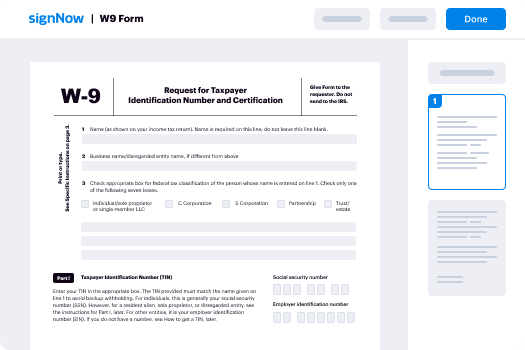
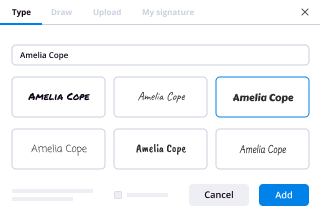
How To Add Sign in eSignPay
Keep your eSignature workflows on track
Our user reviews speak for themselves






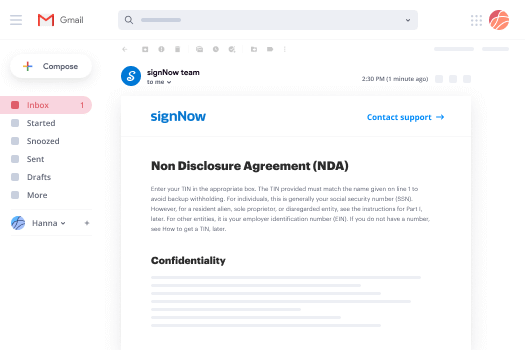
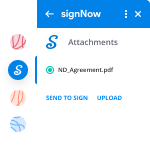
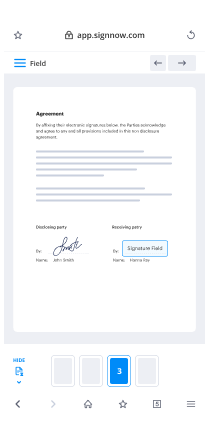
Add eSignature Presentation Now. Check out the most consumer-helpful experience with airSlate SignNow. Manage your complete record digesting and discussing method digitally. Move from hand held, papers-dependent and erroneous workflows to automated, computerized and perfect. You can actually make, supply and sign any paperwork on any system anywhere. Make sure that your essential company situations don't slide over the top.
Learn how to Add eSignature Presentation Now. Adhere to the simple information to start:
- Make your airSlate SignNow profile in click throughs or sign in with your Facebook or Google account.
- Enjoy the 30-day time free trial or pick a pricing plan that's excellent for you.
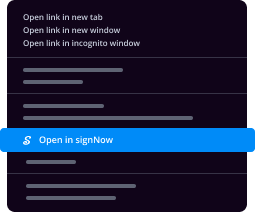
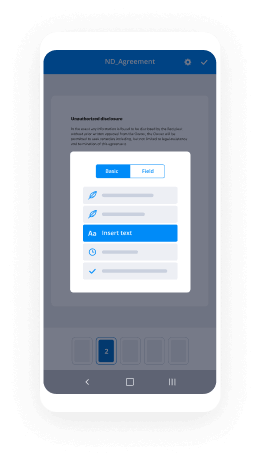
- Discover any legal template, construct online fillable types and talk about them safely.
- Use advanced functions to Add eSignature Presentation Now.
- Signal, modify signing order and acquire in-man or woman signatures 10 times more quickly.
- Set intelligent reminders and get notices at every move.
Relocating your jobs into airSlate SignNow is simple. What practices is a simple approach to Add eSignature Presentation Now, as well as ideas to maintain your co-workers and associates for far better collaboration. Encourage the employees using the very best tools to stay on top of company processes. Boost efficiency and level your small business speedier.
How it works
Rate your experience
-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
Intuitive UI and API. Sign and send documents from your apps in minutes.
A smarter way to work: —how to industry sign banking integrate
FAQs
-
What are your most profoundly helpful definitions of Art that explain its meaning best to you in one sentence or less?
Art is simply the expression of an idea intended to be experienced. A lot of times people confuse the issue by stating that art has to demonstrate talent, or it has to be beautiful. Those are judgements. Art can be beautiful and it can demonstrate talent, but it can also be ugly and it can be as simple as arranging a couple of found objects. Art can be, in its purest sense, simply the act of creating for no other reason than for the intention of being art. Its audience may be vast or it may only be the artist who created it. Art can be very complicated, it can be utilitarian, it can be vague, it can be timeless and it can be fleeting. It can be all of these things and none of them. Art is defined by the act of its creation, not necessarily by anyone else.
-
What is the best real estate technology?
A survey conducted by Coldwell Banker and CNET found that eighty-one percent of prospective home buyers were drawn to homes equipped with the latest in-home technology. Among those, thirty-five percent of people who preferred what is known as smart homes over traditional residences believed that such features solidified the property as “move-in ready.”Technology is also changing the field of home selling. Here are five ways that apps and other online features are making the life of a real estate agent easier.1. Broadcasting with Periscope and TwitterWhat better way to send out a massive blast than on Twitter? The social media site lets you keep it short but sweet as you tell followers that the home of their dreams has an upcoming open house session. You can also post pictures on Twitter that give potential buyers a better perspective of what they will see during their in-person tour of the property. Take the virtual showing a step further by using Periscope to share live footage of yourself walking through the house online. In past times, a substantial amount of money was necessary to promote property by way of commercials. Twitter and Periscope bring the perk to you for free so long as you have a smartphone or tablet when going live and taking pictures.2. Tracking with Glympse and WazeRunning twenty minutes behind used to be a deal breaker pre-Digital era. Not only did you inconvenience the client but you also provided a guess that was often inaccurate and led to more time wasted at the property. Traffic apps in the twenty-first century have made such estimating unnecessary.Waze is one app that provides navigation tips based on real-time traffic information. You can better coordinate appointments so that clients are not left waiting for several minutes and provide clearer updates when you are running late. Glympse also tracks traffic in real-time but takes things a step further by offering a link by which clients can track your whereabouts. Text or email the URL to prospective buyers and let them follow along as you make your way to the location.3. Meet Online with Reflector 2 and Join.meReal estate agents should consider investing in Reflector 2 instead of bringing their USB stick along to nail that next listing presentation. The app serves as a sort of projector by allowing you to cast all activity on your smartphone and tablet on a larger screen. The Reflector 2 works with nearly any device and does not require additional purchase outside of the app itself.Free Screen Sharing, Online Meetings & Web Conferencing is another app that has made buying a selling a home more convenient. Agents can hold brief meetings with clients without requiring them to come into the office. Sharing your computer screen is the best way to convey pertinent information to new homeowners. The recording and playback feature is particularly useful when you need to recall a client’s home preferences. They will be impressed with your attention to detail in finding a house with a built-in barbecue pit. You will know that such meticulousness is because of Free Screen Sharing, Online Meetings & Web Conferencing.4. Add Transparency and Rapidity with an Automated Mortgage Loan ProcessThe traditional method of the home loan process involved hours spent trying to secure financing. Leaving one paycheck stub or bank statement at home often meant holding off on the process until the client was able to furnish proof of such documentation. There was no transparency in the process, which meant that customers were entirely reliant on the expertise of the real estate agent.Technological advances have revolutionized the mortgage loan process. Automated processing now establishes criteria by which applicants are judged that makes applying simpler. Some financial institutions can pre-approve hopefuls in ten minutes. Individuals who go through the entire process may see their loans finalized in ten days instead of the average four-week period. Digital tools provide real-time updates so that even those who are not approved can move on to the next bank quickly instead of waiting for a rejection letter to arrive by way of snail mail.5. Agree from Home with E-signaturesIn past times, the thrill of closing quickly became inconvenient for buyers upon hearing that all approved owners would need to stop by the real estate agent’s office to sign final documents. Some individuals were forced to take a sick day from work just to make their mark on the paper. Such heartache is why the masses are thrilled to learn that e-signatures have the same weight as traditional marks on legal documents. A real estate agent can email paperwork that his clients can sign at their leisure and return electronically. It is even possible to solidify documents on a smartphone in some instances, which makes the home loan process that much more convenient.
-
What digital tool, as a real estate agent, do you most use?
As an agent, we have access to the MLS, which the public only has limited access to. In my area the public can see exactly what Zillow can which is active listings. Our board does not disclose the sales price of closed prices, which makes services like Zillow pretty much worthless in my area. (Zillow may be useful in some areas, perhaps many, just not where I work).That said, my favorite and most useful tool, which is also available to the public, is the GIS (Government Information Service). Type in to Google: (Your county)(Your state) GIS [ie: Marion County Indiana GIS ] . While it isn’t available in every county of the country, you will find it in most major areas. It will give you access to the tax assessor records and often times the sales history of the property. The tax records will give you the details of site size, improvements, assessed values and depending on the county may or may not give you the annual taxes.Since real estate agents in some areas count the basement area when they list the size of the property, the GIS will allow me to figure out what is really there if I’m new to the area. For what I am looking for, there is a signNow difference between a stated 3,600 square foot house by the agent and 1,800 square foot above ground over a 1,800 square foot basement. - Lenders only count the above ground square footage as living area when making a loan.Hope this helps.
-
How do I get my boss to communicate with me about when they will be working remotely and not coming into the office?
They might think that the fact that they are working remotely is on a ‘need to know’ basis and you don’t ‘need to know’. They may also like the fact that they are the boss and can come and go from the office as they please. Why do you need to know?Ask yourself these questions:Is their absence from the office impacting your work and not allowing you to get certain things done?Are there important documents that need their physical signature?Are there things that need approval and require their physical presence?Are there meetings with customers that had to be cancelled because the customers e...
-
How are cracked versions of software created and why are developers not able to prevent it?
Cracked versions of software are created with the use of debuggers. (A debugger is a special type of software that lets programmers deconstruct their software into its constituent parts for the purpose of finding bugs, and thus de-bugging. Additionally debuggers can be used for reverse-engineering, or to see what is inside the software, to learn its logic. The latter method is used mostly by malware researchers to study what malware (or computer viruses) do on-the-inside. But it can be also used by an attacker to "crack" (or bypass) legal software registration, or at times, to alter normal behavior of software, for instance by injecting a malicious code into it.)For the sake of this example, I will assume that the software that is being "cracked" was compiled into a native code, and is not a .NET or a JavaScript based application. (Otherwise it will be somewhat trivial to view its source code.) The compiled native code is a bit more tricky "beast" to study. (Native means that the code executes directly by the CPU, GPU, or other hardware.)So let's assume that the goal of an attacker is to bypass the registration logic in the software so that he or she doesn't have to pay for it. (Later for lolz, he or she may also post such "crack" on some shady online forum or on a torrent site so that others can "use" it too and give him or her their appreciation.)For simplicity let's assume that the original logic that was checking for the software registration was written in C++ and was something similar to the following code snippet:In this code sample "RegistrationName" and "RegistrationCode" are special strings of text that a legitimate software user will receive after paying for the license. (The name is usually that person's actual name or their email address, and the code is some string of unique/special characters that is tied to the name.)In the logic above, the function named "isRegistrationCodeGood()" will check if "RegistrationName" and "RegistrationCode" are accepted using some proprietary method. If they are, it will return true. Otherwise false. That outcode will dictate which branch (or scope) the execution will follow.So the logic above will either show that registration failed and quit:Or, if the registration code and name matched, it will save the registration details in persistent storage (such as the File System or System Registry) using the function named "rememberRegistrationParameters()" and then display the message thanking the user for registering:A "cracker" will obviously want to achieve the second result for any registration code that he or she enters. But they have a problem. They do not have the C++ source code, part of which I showed above. (I hope not!)So the only recourse for an attacker is to disassemble the binary code (that always ships with software in the form of .exe and .dll files on Windows, and mostly as Unix executables inside the .app packages on a Mac.) An attacker will then use a debugger to study the binary code and try to locate the registration logic that I singled out above.Next you can see the flowchart for a snippet of code that I showed in C++, presented via a low-level debugger. Or, as the code will be read in the binary form after compilation:(For readability I added comments on the right with the names of functions and variables. They will not be present in the code that an attacker could see.)(To understand what is shown above an attacker will have to have good knowledge of the Assembly language instructions for the native code.)I also need to point out that having a disassembly snippet like the one above is the final result for an attacker. The main difficulty for him or her is to locate it among millions and millions of other similar lines of code. And that is their main challenge. Not many people can do it and that is why software "cracking" is a special skill.So having found the code snippet above in the software binary file a "cracker" has two choices:1) Modify (or patch) the binary.2) Reverse-engineer the "isRegistrationCodeGood()" function and copy its logic to create what is known as a "KeyGen" or "Key Generator."Let's review both:The first choice is quite straightforward. Since an attacker got this far, he or she knows the Intel x64 Instruction Set quite well. So they simply change the conditional jump from "jnz short loc_7FF645671430" at the address 00007FF645671418 (circled in red in the screenshots) to unconditional jump, or "jmp short loc_7FF645671430". This will effectively remove any failed registration code entries and anything that the user types in will be accepted as a valid registration.Also note that this modification can be achieved by changing just one byte in the binary code from 0x75 to 0xEB:But this approach comes with a "price" of modifying the original binary file. For that an attacker needs to write his own "patcher" (or a small executable that will apply the modification that I described above.) The downside of this approach for an attacker is that patching an original executable file will break its digital signature, which may alert the end-user or the vendor. Additionally the "patcher" executable made by an attacker can be easily flagged and blocked by the end-user's antivirus software, or lead criminal investigators to the identity of the attacker.The second choice is a little bit more tricky. An attacker will have to study "isRegistrationCodeGood()" function and copy it into his own small program that will effectively duplicate the logic implemented in the original software and let him generate the registration code from any name, thus giving any unscrupulous user of that software an ability to register it without making a payment.Vendors of many major software products understand the potential impact of the second method and try to prevent it by requiring what is known as "authentication." This is basically a second step after registration, where the software submits registration name to the company's web server that returns a response back to the software of whether the code was legitimate or not. This is done by Microsoft when you purchase Windows (they call it "Activate Windows") and also by signNow, and many other companies. This second step may be done behind-the-scenes on the background while the software is running, and will usually lead to cancellation of prior registration if it was obtained illegally.So now you know how software is "cracked".Let me answer why it is not possible to prevent it. It all boils down to the fact that any software code needs to be read either by CPU (in case of a binary native code) or by an interpreter or a JIT compiler (in case of JavaScript or .NET code.) This means that if there's a way to read/interpret something, no matter how complex or convoluted it is, an attacker with enough knowledge and persistence will be able to read it as well, and thus break it.There is an argument though that cloud-based software is more secure, which is true, since its (binary) code remains on the server and end-users do not have direct access to it. And even though cloud-based software is definitely the future, it has some major drawbacks that will never allow it to fully replace your conventional software. To name just a few:Not everyone has an internet connection, or is willing to upload their data online. Additionally someone’s internet connection can be very expensive or too slow to make the software run very laggy.Then there’s a question of distributed computing. For instance, Blizzard Entertainment would never make “World of Warcraft” to fully run on their servers due to immense computational resources needed to render every single scene for every player they have. Thus it is in their best interest to let each individual user’s computer to do the rendering instead.As a software developer myself, I obviously don't like when people steal software licenses. But I have to accept it and live with it. The good news is that there are not that many people who are willing to go extra mile and search for a cracked version of software. The main problem for those who do, is that by downloading a patched executable, or an attacker's KeyGen or a Patcher, they are effectively "trusting" him or her not to put anything "nasty" into it that was not "advertised on the package" (stuff like trojans, malware, or keyloggers.) So the question for those people becomes -- is it worth the cost of the software license to potentially infect your system with a nasty virus?On the other side of the equation, some developers react very negatively to any attempts to steal their software licenses. (I was there too.) They try to implement all kinds of countermeasures -- anything from tricking reverse-engineers, to adding booby traps in the code that may do something nasty if the code detects that it is being debugged, to obfuscating or scrambling the code, to enforcing all kinds of convoluted DRM schemes, to blocking users from certain countries. I personally try to stay away from all of those measures. And here's why:A) Any kind of anti-reverse-engineering tactics could be bypassed by an attacker with enough persistence. So why bother and waste my time when I can invest that time into adding something useful to my software that will make it more productive for legitimate users?B) Some code packers could create false positives with antivirus software, which is obviously not good for marketing of that software. It also creates unnecessary complexity for the developer to debug the software.C) Adding booby traps in the code can also “misfire” on your legitimate users, which will really infuriate them and can even lead to lawsuits.D) Any DRM scheme will probably catch some 100 illegal users and greatly inconvenience 10,000 legitimate ones. So why do it to your good customers?E) Our statistics show that about 75% of all illegal licenses come from China, Russia, Brazil, to name the worst offenders. (I also understand that the reason may be much lower incomes that people have in those countries.) The main issue for us though was the fact that if we enforce our DRM or add some strong registration authentication, many people that wanted to bypass our registration would simply use a stolen credit card number. And we had no control over it. Our system will use it to send them a legitimate license only to have the payment bounce in weeks time. As a result we would lose the money that were paid for the license, plus the credit card company will impose an additional chargeback fee to our account, which may range from $0.25 to $20 per bad purchase on top of the license cost.F) As was pointed out in the comments, some companies may actually benefit from allowing pirated copies of their software. Microsoft for instance gets a lot of free publicity from people using their Windows OS, the same goes for signNow with their Photoshop. That is a good point that I agree with.So my philosophy is now this -- if someone wants to go extra mile and steal our software, go for it! They went this far to do it anyway, so they probably have a good reason. On the positive side there are so many other customers that appreciate the work that goes into creating software that greatly outnumber those that don’t.PS. Thank you for all your feedback! It makes me feel good that the knowledge I shared is useful to others.
-
Why are Chinese products cheaper?
In the words of Tim Cook: "The popular conception is that companies come to China because of low labor costs. I'm not sure what part of China they go to, but the truth is China stopped being the low labor cost country years ago. That is not the reason to come to China from a supply point of view, the reason is because of the skill."Let us look at the concept of labor or the involvement of labor in an every-day product. Let us compare 2 products: a plastic fork vs a plush toy. Although both products fall on opposite spectrums of the consumer life cycle (one disposable whilst the other one is reusable), both are sure to be made in China.A plastic fork is made from food-grade Polystyrene (PS) plastic pellets or beads through a process known as plastic inject molding. In here the pellets are heated in a molding machine to a viscous state and are injected into a mold. The mold produces multiple sets of forks within a matter of seconds and from there on it’s as simple as detaching the forks from a sacrificial (?) holder or tool (this is also made of PS and in most cases is recycled). From here the product is moved into packaging and then sent out of the factory for export. A fully automated machine can be set to run continuously 24 hours a day with very little monitoring by a worker, thus being a low labor product.Now, let us look at that plush toy. The stuffed animal is comprised of textile material for the cover, stuffing, two eyes and a nose. The material must be cut into pieces, sewn together and stuffed. The nose, eyes and mouth are sewn onto the material together and stuffed, requiring skilled labor(-). The cutting of the pieces may be done by hand or by machine, but the pieces are sewn together by a worker using a high-speed sewing machine. Next comes the insertion of stuffing – this is rather complex for a machine to do, as such the insertion is done by hand and the insertion point is also manually closed. It is evident that this requires much labor, therefore, this type of a product is considered a high labor product with labor contributing 70% of the total cost [1]. In the end, much like a fork, the product is moved and packaged for export.Because labor is only one part of the total cost of a product, and in many cases it's as low as 20% of the total cost, – this must indicate that there may be other factors at play in making Chinese products, such as the fork. If labor were the only factor, then most of the “plush toy/labor intensive” industries would have shifted to other countries – but only some industries already have e.g. Bangladesh, Vietnam and Mongolia to name just a few. To that extent, manufacturing of plastic forks could possibly return to the USA; but that’s not happening.Industrial production does not take place in isolation, but rather relies on networks of suppliers, component manufacturers, distributors, government agencies and customers who are all involved in the process of production through competition and cooperation. The ecosystem of doing business in China has evolved quite a lot in the last thirty years. Here are the additional factors, including labor, that affect the overall cost of manufacturing and thus make Chinese exports cheaper:A. Commendable supply chain: Supply chain activities transform natural resources, raw materials, and components into a finished product that is delivered to the end customer. No country, at present, has a supply chain more sophisticated yet flexible than China. China’s biggest advantage is their domestic availability of most of the raw materials required to manufacture a given product [2]. Not only are private entities involved in the process of outputting raw material for manufacturing. Rather, many Chinese State Owned Enterprises (SoEs) actively control and output raw materials for small factories to transform into ready-made goods. If the government is involved in such activities, it is safe to assume that this is an active industry that requires not only oversight and monitoring, but active involvement. Access to affordable raw materials helps bring down manufacturing costs to a considerable extent. As a result, having suppliers who are local to the manufacturer has gained importance as a way to cut costs[6].B. Rebate upon Export: The export tax rebate policy was initiated in 1985 by China as a way to boost the competitiveness of its exports by abolishing double taxation on exported goods[7]. China is one of over 150 countries that utilize a Value Added Tax (VAT) system. It is a tax only on the "value added" to a product, material, or service at every state of its manufacture or distribution. The VAT rate is generally 17%, or 13% for some goods. Chinese companies receive a VAT refund from the government for materials of products produced for export. Basically, factories that export do not pay any VAT on goods or raw materials used made for export – further subsidizing raw material costs. American imports to China are charged a VAT, but the U. S. doesn't have a VAT to charge Chinese imports. Moreover, Chinese manufacturers work with far lower profit margins than those in the U.S.C. Efficient Infrastructure and Logistical Access: In its fast-paced effort towards industrialization, China has built many ports (big and small), roads and railroad access. Such a system is not secluded to the big cities (Tier 1 or Tier 2 cities), it connects all of them, including Tier 4 cities or small towns used as industrial manufacturing zones. Having an efficient logistical system allows for cheaper travel costs –the cost of units (kilometers or miles) per currency (dollar or RMB) decreases. Also, an efficient infrastructure reduces overall downtime. Such is the case of India, as pointed out by Vaibhav Mandhana [3]: “Given the poor roads, a shipment from India's north can take a week or more to signNow India's south. Sometimes it is quicker and cheaper to actually get a shipment from Shenzhen than Kolkata. Time is money and all those delays add to your cost. If I could get something in two days, I could sell it immediately rather than wait two months to sell it [add up the interest costs]”"The road freight from LA to Nevada will cost you a lot more than the sea freight from China to LA."[5]D. Subsidized Utilities and Availability: Within China’s industrial areas many fixed and variable production costs are heavily subsidized. For example: electricity and water are subsidized up to 30% compared to normal household or commercial zones. Moreover, the local government gives support with land access at competitive rates, creating jobs in the area. This further helps to diminish the cost of the end product – after all you have access to cheaper land, water and light (What manufacturing does not require these? - Hell, even mining bitcoin does!). In non-industrialized or not fully industrialized countries (Indonesia, Vietnam, India), access to water and electricity remains a critical issue, until today. “In Coimbatore and other industrial places, you get power for like eight hours a day. That means the machinery lies idle for sixteen hours and that wasted capacity adds to the cost.”Do we see a trend of several factors, other than labor, which affect the overall cost of the product? Hold on, there are more!E. Bureaucracy: Barriers for entry in China, in this context, are extremely low. Although you need to fill out a huge number of papers (Customs Declaration Form, Land Annexation, Tax Filing, Compliance Related Documentation, Drawback/Rebate Forms, Annual Returns and etc.), the process is not complex. Relevant departments and accountability are there; you do not need to grease palms to get what you need; streamlined government policies are in place. Again, non-industrialized countries do not have many of these processes in place – they are in the early stages, whereas China has been through all this. I am not saying China is pure and not corrupt, there might be corruption in some cases, but the overall industrial process is so deeply rooted, that people just follow established guidelines. Greasing palms and running around places to get a stamp or a signature causes further delays (time is money) and increases overall costs. This is considered more as “Political Will” than bureaucracy; meaning the government’s will to allow you to do business is prominent thus reducing barriers for you to do business or manufacture or engage in services.F. Technology and Automation/ Skilled Labor: It would be unreasonable to discard China’s interconnectivity between technological advancement and manufacturing capacity. They work hand-in-hand. Availability of the latest technology to manufacture products of a high quality on a large scale. And let's be honest, scalability can be a very important factor in deciding price of a product. Apart from technology, China has a large population, thus having a bigger access to a wide talent pool. Availability to a greater talent pool decreases the overall demand as there is an oversupply – again, denting the costs of the product. If you recall, Tim Cook's main reason for manufacturing in China is: the depth of highly skilled labor in the manufacturing space. To rephrase what Cook said: "No other country in the world besides China has the combination of an electronic component supply chain and large pools of skilled labor needed to make iPhones on the scale which Apple needs."G. Labor: It is comparatively cheaper to many so-called “developed countries”. You can have someone do the same labor task for a comparatively lower price than say Europe or the USA for that matter. This further brings down costs. As noted before, it is not the cheapest – but it is not the most expensive either. What is important to remember here is that labor in China, is skilled – although most laborers are not trained, but have learned by doing. When you outsource to China, you’re working with time-tested factories that have been producing quality products in similar industries as yours for years on end, and in massive supply.Where a labor task might cost you $8-9 USD/hour in developed countries, it will cost you $450-500 USD for an entire month in China (8 hours a day, 28 days a month). If you do the math, that’s about $2.19 USD/hour. Countries like Indonesia a semi-skilled laborer will do it for half, $1.05 USD/hour – but the manufacturing process will be influenced by factors all the factors mentioned.H. Local Government: Local government officials are appointed, not elected. Part of their job is to help the industries and they are measured by results. Furthermore, locals compete with each other. That means Suzhou is competing with Chengdu to attract industries, and so on. Hence officials are always using their local advantages to help, attract, and grow industries, such as providing low cast land, building industrial parks, and making sure that the support infrastructure (roads, electricity, water, etc.) even local housing and schools are there. Since these officials are not elected locally, their actions are much more efficient rather than dealing a motion to go through town hall meetings or waiting for a ballot to pass for months. The downside of such efficiency could be that some environmental studies were not complete or many local concerns are not addressed fully (All credit for how to local governments operate within China go to Mr. James Yeh ).Here are few controversial factors, claimed by several sources:I. Currency: There is the ever-present theory of currency manipulation among economists, where China undervalues their currency by an estimated 30%-40%, which simply makes every product that China ships out 30-40% cheaper than those of a potential American competitor. The Yuan is manipulated and pegged undervalued to the US dollar [2]. So the price quoted in US dollars( more exports are quoted in dollars), will be cheaper than normal; (This manipulation has affected the domestic price of the product and labor wages as it has been kept much lower than it should have been. The Chinese yuan has, however, been steadily increasing in value against the dollar over the past few years.J. Compliance: The Chinese government does not bind itself with Intellectual Property issues. They allow the industry to investigate the products developed successfully elsewhere in the world. They then produce them in large quantities. Personally, there is nothing wrong in this benchmarking. Most industries do benchmark; especially in the automotive world. This saved the industry from expensive investments in R&D [4]. Although China has its own environmental protection agency, the environmental protection laws are generally lax and not enforced fully, especially at the local level. In previous years, Chinese factories cut down on waste management costs -further bringing down overall product costs. Things have been different lately, thanks to the strong efforts from the national government. Laws on IP and environmental protection are being enforced, especially after the Hangzhou G20 summit. There is still some belief that more needs to be done.If cheap labor was in itself the key driving factor, a large percentage of the labor-intensive factories would have already shifted to cheaper labor countries and lower labor-intensive jobs would have returned to the countries such as the USA - because China is not the synonym for cheap labor anymore. But that's not what we are experiencing; only certain jobs within the manufacturing field are moving to South East Asia. A huge chunk is there and is still able to reap the benefits of various factors. It will take more than a cutthroat desire for emerging economies to set up a business ecosystem that can compete with China's.Wow now over 1,000 Thanks for your upvotes! If you would be kind enough to give a like for this same article on my LinkedIn profile: https://www.linkedin.com/pulse/w...Footnotes:1. https://www.industryweek.com/env...2. https://qr.ae/TUtz1K3. https://qr.ae/TUtzTO4. https://labs.ebanx.com/en/market...5. Walter Hay's answer to How expensive is it to import to Nevada from China?6. 5 Reasons Why You Should Manufacture In China With ITI[7] China Will Continue To Dominate World Production
-
What other chords can I put in between the I-IV-V chords to make it sound better?
There are many. This is the theory behind some of them:A major scale has modes, right? Ok, each one of this modes represents a region. Major modes represent major regions; minor modes represent minor regions. For the moment we are not going to talk about the diminished mode, so for the moment the locrian is not going to represent a region close to tonic. So, for C major, we have the following regions:I Tonic - C majorii dorian - D minoriii mediant - E minorIV subdominant - F majorV Dominantvi submediantviib5 Ups! This region is not that close. I’ll tell you why later.Yes, I know, you should be thinking: “why mediant and not frigian?” Well, this are not modes, these are names of regions. We say dorian to differentiate it from the region of the supertonic (II major).So, the major regions are closely related to tonic. And these major regions have minor relative regions.ii is the relative minor of IViii is the relative minor of Vvi is the relative minor of I(vii is the relative minor of II, but we don’t have a D major chord that appears naturally, so this region should be not that close).So I was saying that the ii, the iii, the IV, the V and the vi are closely related to tonic. Well, we can import the alterations of this regions, we can use the key signature of them to build artificial chords. This artificial chords don’t belong to the tonality, that’s why they are artificial. But they are very close to the tonality. We can use them to ornament a progression.So, which are those alterations? Let’s see…From F major and D minor, we import Bb. But the ascending vension of the melodic scale of D minor has also B natural and C#. B natural is already in C, but C# is not. We can import it too.From G major (and E minor, it’s relative minor) we import F#. But the melodic scale of E minor presents C# and D# in the ascending version. We can import them too.So in C major we can import:Remember this formula: +4, -1, where “+” is the number of sharps to add and “-” is the numbers of flats. Let’s call it the hidden key signature. You will never write it on the score, it’s just a way to explain close relations to tonic. 4 sharps and one flat are close to a major tonality. This formula is relative to the real key signature. If we were in G major, four sharps and one flat would be:… And in Eb, we would have:So what’s the point with all this stuff? Four sharps and one flat are alterations that belong to regions that are close to tonic, and you can use them to build artificial chords: artificial dominants (they are also called secondary dominants), artificial semidiminished chords and even an artificial diminished chord.So, when you have a progression, you can ornament it by adding artificial chords in between. Artificial dominants are fifth degrees. So if we are in C major and you want to signNow the IV, you can put the V of the IV, which is C7. You can also use the vii° of the IV (Eb5, or Eb5 7).So in your progression, you can add:I - (I7) - IV - (II7) - VYou could also use half diminished chords, and it would be fine. Half diminished and diminished chords are seventh degrees of the target chord. The seventh degree must be a leading tone (half step below your target chord).There are many other chords that can be used, that come from not so close regions. I’m not going to explain them here, because it will take a long explanation. But augmented sixth chords can be used to replace the subdominant or to ornament the resolution to V.You could also add the I 6/4 in between the IV and the V. This is a diatonic ornament, no accidentals needed, and it was very common in the classical period.And of course you could also add suspensions, sevenths, anticipations, melodic ornaments, etc. If you know about voice leading, even a simple chord progression can sound really cool.All of this works fine for very conventional purposes but it also works for jazz. In jazz music you could use many other things, but in many cases they would be also related to this explanation.Edit: Now, the most important thing to understand is that harmony is not about formulas, but about technique. Many diatonic and non-diatonic chords can be used. Good or bad results depend on your purpose and the musical contexts.I hope this answer helps. Good luck.
-
What are the variants of the Boeing 747?
Google and Wikipedia are your friends…I’m your friend too, so let me describe the different variants of the Boeing 747 for you on Quora:747–100First flight: February 9, 1969Number built: 168We start with the first generation 747. The prototype aircraft was named City of Everett, and it took off from the Boeing Field in Washington for its maiden flight.The inaugural commercial 747 flight took place on January 22, 1970. The plane serving the flight was Clipper Victor, the 11th Jumbo Jet built.On August 2, 1970, this plane was involved in the first ever hijacking of a 747. Pan Am Flight 299 was hijacked en-route to San Juan with 379 people aboard.The hijacker had a gun and explosives, and he demanded the captain to fly the plane to Cuba. The captain complied with his order.Having been notified of the hijacking, Cuban Prime Minister Fidel Castro visited Jose Marti Airport to witness the landing of a 747—a plane he had never seen before.Castro was intrigued by the unprecedented size of the Jumbo Jet. When the captain disembarked the plane with the terrorist, Castro bombarded the captain with questions about the jet’s capabilities, seemingly forgetting that he had just endured the sheer terror of a hijack.Unfortunately, Clipper Victor would later be involved in the worst aviation accident ever. On March 27, 1977, while operating as Pan Am Flight 1736, the plane was struck by KLM Flight 4805 on a runway, resulting in 583 fatalities.The second Boeing 747 ever built was turned into a noodle restaurant after retiring from service. However, the restaurant failed and the plane was scrapped.747–100SRFirst flight: August 31, 1973Number built: 7When Japanese airlines requested a high-capacity, domestic version of the 747, Boeing launched the 747–100 Short-Range. This variant has lower fuel capacity, and higher payload allowance. This is the first airliner to be configured to carry more than 500 passengers. Japan Airlines’ 747–100SR can carry up to 550 passengers.As the –100SR was designed to perform twice as many flight cycles as the –100, Boeing had to strengthen its airframe and landing gear.A –100SR was involved in the deadliest single-aircraft aviation accident, when Japan Airlines Flight 123 crashed in 1985, killing 520 people.▲ The aircraft involved in the tragedy.747–100BFirst flight: June 20, 1979Number built: 9This variant borrowed the stronger fuselage and landing gear design from the 747–100SR. Compared to the 747–100, it has a greater fuel capacity and longer range. Boeing also offered new engine options.In 1996, an Ilyushin Il-76TD struck a Boeing 747–100B flying at about 14,000 feet, resulting in the most fatal mid-air collision in history.747–100B SRFirst flight: November 3, 1978Number built: 20The difference between this model and the regular 747–100SR is an increased maximum take-off weight.747–100B SR SUDFirst flight: February 26, 1986Number built: 2This model has the same features as the 747–100B SR, but with a Stretched Upper Deck that is around 7 meters longer, providing a 10% increase in capacity and allowing for more seats. This new upper deck also came with a pair of full-size emergency exit doors for faster evacuation.▲ This image depicts an actual 747–100, not a –300.747–100SFThe 747–100 Special Freighter is a 747–100 converted to carry cargo. A main-deck side cargo door and cargo loading mechanisms were added. The main deck was strengthened to accommodate the increased weight of the payload.If you look closely at the image below, you’ll be able to see three exit doors that are sealed off, and the side cargo door behind the wing.747SPFirst flight: July 4, 1975Number built: 45The 747 Special Performance is truly unique and quirky. It is derived from the 747–100, and it’s about 14.7 meters shorter than a regular 747. It also has one less pair of exit doors on the main deck.It has a stubby fuselage, a huge vertical stabiliser, four turbofan engines and two passenger decks. It just looks ludicrous, and wonderful.The following was stated in Boeing’s 1984 edition of “747 Airplane Characteristics — Airport Planning”:[The 747SP] can fly higher, faster and farther than any other wide-body aircraft, and as a result serves well on long-distance air routes that do not require the size of the standard 747.The 747SP apparently had a top speed of approximately Mach 0.92 (630 mph/ 1013 kmh).One plane was involved in a near-disaster. In February 1985, China Airlines Flight 6 plummeted 30,000 feet in under 2 and a half minutes, before the pilots were able to regain control and level their jet out at 9,600 feet. The flight landed safely.▲ Damage sustained by the plane’s empennageThe plane was repaired, but its wings were permanently bent upwards by 5 cm.747–200BFirst flight: October 11, 1970Number built: 225The “second-generation” 747 entered service in February 1971, just a year after the original model. It has more powerful engines, higher maximum take-off weight and longer range.The 747-200B denotes the “basic” passenger version.▲ The KLM 747–200B that collided with Clipper Victor on the runway747–200FFirst flight: Early 1972Number built: 73This is the first freighter version of the 747 to be manufactured by Boeing.Boeing stated that this plane has “virtually” the same cargo space as the 747–100SF.747–200CFirst flight: Early 1973Number built: 13Equipped with a nose cargo door, the 747–200 Convertible is capable of being quickly converted from a passenger aircraft to a cargo aircraft, and vice versa. It can also carry a mix of cargo and passengers.▲ There are passenger windows on the nose cargo door.An El Al Boeing 747–200C carried a record-breaking 1,087 passengers on a single flight during Operation Solomon in 1991 (figure excludes babies board on the flight).747–200MFirst flight: Late 1974Number built: 78Also known as the –200B Combi, this plane is functionally similar to the –200C. It was built with a passenger cabin in the front half of the plane, and a cargo compartment in the back half.This model does not have a nose cargo door. Instead, a left-side main-deck cargo door was implemented near the rear of the aircraft. Unlike the –200C, this model cannot be converted into an all-cargo configuration.747 (SUD)While Boeing built the 747–100B SR SUD from scratch, they offered the Stretched Upper Deck as a retrofit to the 747–100B, 747–100SR, 747–200B and 747–200M variants.These images show the SUD modification process:All 747s that were upgraded with the extended upper deck were designated as “SUD” models. For example, the “747–200B SUD”.▲ Top: An original KLM 747–200B | Bottom: The same plane with the SUD upgrade747–300First flight: October 5, 1982Number built: 56The 747–300 is the third-generation passenger 747, and it came with the stretched upper deck as standard. To reiterate, the upper deck was stretched to be about 7 meters longer than older, non-retrofitted 747s, and it came with a pair of full-size exit doors.Boeing gave customers the option for updated engines, or the same engines from the 747–200 models.While older 747 variants had spiral staircases connecting the two passenger decks, the 747–300 featured a new staircase design which occupied less space in the cabin, providing room for more seats.▲ Left: Spiral staircase on a 747–200B | Right: Staircase on the 747–300747–300MFirst flight: Late 1982Number built: 21As with the 747–200M, the updated –300M can carry passengers and freight on the main deck. It is also referred to as the 747–300 Combi.747–300SRFirst flight: Late 1987Number built: 4This plane was once again introduced for Japanese airlines. It has a capacity of 584 passengers.747–300SFBoeing didn’t produce a freighter version of the 747–300, but they initiated a modification program in May 2000 to turn the passenger variants into cargo planes.747–400First flight: April 29, 1988Number built: 442The fourth-generation 747 introduced numerous structural and technological advancements, providing greater efficiency. It has more range, more fuel tanks, longer wings, and new wingtips that increase fuel efficiency by 4%.More importantly, this model came equipped with a glass cockpit consisting of multifunctional digital screens, which supersede many analog instruments. More computerised flight control systems were implemented, eliminating the need for a flight engineer and largely reducing the amount of knobs, dials and switches.Additionally, the model came with new powerplants choices and a refreshed passenger cabin. With 442 planes constructed, the 747–400 is the most popular 747 model.Unsurprisingly, the 1000th 747 produced is a 747–400.▲ This plane was delivered to Singapore Airlines in October 1993.747–400FFirst flight: Late 1993Number built: 126The freighter version of the 747–400.Since an extended upper deck is redundant and adds weight to the aircraft, every 747–400F retained the same upper deck dimensions as the 747–200F.747–400MFirst flight: Mid 1989Number built: 61Otherwise known as the 747–400 Combi, this aircraft can haul passengers and cargo on the main deck. Compared to older Combi aircraft, this model came with enhanced fire protection systems.The 747th 747 was a –400M. It was delivered to Lufthansa in September 1989.747–400DFirst flight: Early 1991Number built: 19For their high-capacity, short-range 747–400, Boeing decided to drop the “SR” label in favour of a new name, the 747–400 Domestic.Yet again, this variant was produced for the Japanese market. Because it’s tailored for short-haul flights, no winglets were installed on newly-manufactured 747–400D. Boeing later offered the winglets as a retrofit.This airplane has a maximum capacity of 660 passengers in a single-class configuration.747–400ERFirst flight: July 2002Number built: 6The 747–400 Extended Range was launched with an option of one or two additional fuel tanks in the forward cargo bay. Structural modifications allowed for a higher maximum takeoff weight.▲ Qantas is the sole operator of the –400ERThe Boeing Signature Interior, which debuted on the Boeing 777, was installed on every 747–400ER.The 747–400ER is expected to be retired by 2020.747-400ERFFirst flight: September 2002Number built: 40This model can fly 525 kilometres farther than the standard 747–400F. Like the -400ER, this plane has a more robust structure, enabling higher maximum takeoff weight allowance.747-400BCFFirst flight: October 5, 2005Every 747–400 Boeing Converted Freighter was once a passenger 747–400. Boeing appoints contractors like HAECO and SIAEC to perform the conversion work.Like the –400F, it has a side main-deck door situated behind the wings.747–8IFirst flight: March 20, 2011Number built: 47 as of September 2018Initially named the 747 Advanced, the 747–8 Intercontinental was launched in 2005.This model was developed with technologies and design derived from the 787. For the first time, Boeing lengthened the 747’s airframe. As a result, the 747–8I is the longest 747, and the longest commercial aircraft to date.It is powered by GEnX engines, the same ones found on the 787.The 747–8I features a redesigned wing and raked wingtips inspired by the 787. To reduce weight and improve efficiency, parts of the wings are constructed using carbon-fibre composites.It comes with updated flight deck systems and avionics, along with the Boeing Sky Interior. Its passenger windows are 16% larger than those on the 747–400, but unlike the 787, the windows don’t dim electrically.747–8FFirst flight: February 8, 2010Number built: 82 as of September 2018This freighter aircraft shares many attributes with the 747–8I, including its record fuselage length. However, the dimensions of the upper deck remain identical to original 747.The two 747–8 models are 5.6 meters longer than older 747 models, and 20.3 meters longer than the 747SP. They were stretched in different areas to suit their purposes:DreamlifterFirst flight: September 9, 2006Number converted: 4The 747–400 Large Cargo Freighter, better known as the Dreamlifter, is an oversized cargo transporter. This colossal aircraft has three times the cargo capacity of a –400F. It was exclusively designed and used by Boeing to carry parts of the 787 Dreamliner from suppliers around the world to the assembly plant.Like the –400BCF, this airplane model was converted from passenger 747–400s.▲ This 747–400 is one of the 4 aircraft to be modified into Dreamlifters.The first Dreamlifter rolled out of the hangar in August 2006, and it wasn’t particularly sightly. Then-president of Boeing Commercial Airplanes, Scott Carson, was reportedly heard apologising to the designer of the 747, Joe Sutter, by saying:[Sorry] for what we did to your plane.VC-25AFirst flight: May 16, 1987Number built: 2Commonly mistaken as the “Air Force One”, the VC-25A is a heavily modified version of the 747–200B. It’s only known as Air Force One when the POTUS is on board.In recent years, it has made many cameo appearances in tabloid newspapers.VC-25BFirst flight: July 8, 2016 (as a 747–8I)Number to be converted: 2The VC-25B will supplant the ageing VC-25A. It should be operational by 2024.To keep costs low, the US Air Force purchased two 747–8I airplanes that were originally built for a Russian airline which went bankrupt.▲ The two undelivered 747s destined to be VC-25Bs, stored in the Mojave desert747 SupertankerFirst flight: February 19, 2004Number converted: 3This is a Boeing 747 variant that was transformed into an aerial firefighting air tanker. It can carry up to 74,000 litres of fire retardant or water, and holds the record for the largest firefighting aircraft.Three Supertankers were built from a 747–100, –200C and –400BCF. However, only two entered service. This image below shows the 747–100 Supertanker:Presently, only the 747–400BCF Supertanker is in service.▲ This passenger plane was first converted into a freighter, then an air tanker.SOFIAFirst flight: April 26, 2007The Stratospheric Observatory for Infrared Astronomy is a heavily retrofitted 747SP. It has a telescope installed near the rear of the airframe, and flies at up to 45,000 feet during its missions.This 747SP was formerly owned by Pan Am, and subsequently United.▲ SOFIA, before make-up▲ SOFIA, after make-upBoeing YAL-1First flight: July 18, 2002This plane was once a 747–400F, before becoming the YAL-1 Airborne Laser. It has an infrared chemical laser mounted on its nose, which was intended to destroy tactical ballistic missiles.▲ This plane gives Rudolph a run for its moneyThe plane successfully destroyed two test missiles. However, it was expensive and not operationally feasible. Hence, it was scrapped in 2014.Boeing E-4First flight: June 13, 1973Number built: 4The E-4 is an airborne strategic command and control post. It is derived from the 747–200B. When in operation, the E-4 is identified as a “National Airborne Operations Center”.This plane is capable of aerial refuelling, and was designed to remain airborne for a week during an emergency.▲ This 747 variant has a hump on top of its hump, which houses an antenna.There are two versions of the model, the E-4A and E-4B. The US Air Force initially had three E-4A planes. In 1979, Boeing delivered a new E-4, with upgraded equipment, which was designated as the E-4B. Thereafter, the E-4A jets were refurbished to become E-4B models.Shuttle Carrier AircraftFirst flight with a space shuttle: February 18, 1977Number converted: 2The Shuttle Carrier Aircraft was designed to transport space shuttles from landing sites back to the launch complex. In 1974, an American Airlines 747–100 was acquired by NASA and turned into the SCA.During the maiden flight with an orbiter, Enterprise, the SCA signNowed a speed of 462 km/h (287 mph), and an altitude of 16,000 feet.In 1988, a 747–100SR was obtained from Japan Airlines and converted into a second SCA.▲ The SCA piggybacking Space Shuttle Enterprise▲ Space Shuttle Endeavour riding on the SCAAfter the conclusion of the space shuttle program, the Shuttle Carrier Aircraft carried the shuttles from the Kennedy Space Centre to various museums.Thereafter, the SCA were sourced for spare parts that could be reused on SOFIA. Both planes are now preserved at museums.▲ The 747–100 SCA on display at Space Center HoustonJumbohostelFirst night: January 15, 2009This 747–200B was transformed into a hostel.After some additional work, the engine nacelles were turned into small rooms.Let’s move on to some 747 variants that were conceptualised but never built.747 trijetPeriod of study: Late 1960s — Early 1970sBoeing engineers crafted a concept for a 747 trijet to compete with the DC-10 and L-1011, but they realised it was too costly to develop. Boeing engineers figured that making a three-engine version of the 747 would require a redesign of the wings and the vertical stabiliser, along with other hassles that made the concept uneconomical.So, Boeing scrapped the 747 trijet.747–500X/ –600X/ –700XAnnounced: September 2, 1996Boeing proposed three versions of the 747 with longer fuselages as potential competitors to the hypothetical A3XX plane, which would later become the A380.The concept models were to feature an improved wing design taken from the Boeing 777, more landing gear wheels and a new interior design.▲ 747–400 (Top) compared to the 500X and 600XThe 747–600X and –700X were planned to receive longer and wider fuselages, while retaining the existing wing dimensions and landing gear structures. Furthermore, Boeing stated that the –700X would potentially have a capacity of 650 passengers in a typical three-class configuration.The –500X and –600X were offered for sale at the 1996 Farnborough Airshow, but they didn’t receive any orders. Thereafter, Boeing axed these three models.Oh and one last variant…747–8 PSPImagined: October 18, 2018The Boeing 747–8 Photoshopped Special Performance is the chubbiest 747 ever.Thanks for viewing.// //If you’re interested to know how the worst aviation accident in history happened, and learn about other mid-air disasters, check out Isaac Low's answer to Have planes crashed into each other?Image sources1st — General Aviation News2nd — Aviation Safety Network3rd — The Pan Am Historical Foundation4th — Vecamspot5th — SOBIFY6th — Wikimedia Commons7th — National Geographic8th — Wikimedia Commons9th — Dennis HKG/Flickr10th — Wikimedia Commons11th — Wikimedia Commons12th — Wikimedia Commons13th — Airliners[.]net14th — Cargo Facts15th — NACOE16th — Airline Reporter17th — Top: Airport-Data[.]com | Bottom: Bureau of Aircraft Accidents Archives18th — Airlines Inform19th — Left: Sam Chui | Right: Airliners[.]net20th — Airplane-Pictures[.]net21st — Wikimedia Commons22nd — Rohan Patel/Flickr23rd — Wikimedia Commons24th — Air Charter25th — (Thumbnail of YouTube video by akino33 Aviation Video Channel)26th — Wikimedia Commons27th — Airliners[.]net28th — Airplane-Pictures[.]net29th — Wikimedia Commons30th — Wikimedia Commons31st — Wired32nd — Modern Airliners33rd — Wikimedia Commons34th — australianaviation[.]com[.]au35th — JetPhotos36th — indicator[.]gr37th — unilad[.]co[.]uk38th — Defense One39th — Planespotters[.]net40th — The Gazette41st — Wikimedia Commons42nd — Wikimedia Commons43rd — SOFIA Science Centre44th — Wikimedia Commons45th — Wikimedia Commons46th — Wikimedia Commons47th — NASA48th — Wikimedia Commons49th — Amusing Planet50th — Hostelworld[.]com51st — robertcatanescu[.]wordpress[.]com52nd — Simple Flying53rd — Boeing Images54th — Wikimedia Commons (photo edited by me)Note: Due to Quora’s policy, I cannot add the image URL sources in my answer. To view the image links, click here.
Trusted esignature solution— what our customers are saying
Get legally-binding signatures now!
Related searches to Add eSignature Presentation Now
Frequently asked questions
How do i add an electronic signature to a word document?
How to esign a filable pdf file?
How to eSign buildium?
Get more for Add eSignature Presentation Now
- Can I Electronic signature Iowa Real Estate Word
- How To Electronic signature Iowa Real Estate Document
- Can I Electronic signature Iowa Real Estate PPT
- How Do I Electronic signature Iowa Real Estate Document
- How To Electronic signature Iowa Real Estate PPT
- How Do I Electronic signature Iowa Real Estate PPT
- Help Me With Electronic signature Iowa Real Estate Document
- Help Me With Electronic signature Iowa Real Estate PPT
Find out other Add eSignature Presentation Now
- North carolina residential rental lease application form
- Nc trust form
- Deed trust form 481373943
- North carolina legal last will and testament form for a single person with minor children
- Nc codicil form
- North dakota notice intent form
- Nd notice form
- Nd judgment form
- North dakota trust form
- Nebraska buyers notice of intent to vacate and surrender property to seller under contract for deed form
- Ne discovery form
- Nebraska assignment of deed of trust by corporate mortgage holder form
- Notice terminate tenancy form
- Personal information form pdf 481373958
- New hampshire sellers disclosure of financing terms for residential property in connection with contract or agreement for deed form
- Nh corporation form
- Nh divorce file form
- Nh lease form
- New hampshire assignment of mortgage by corporate mortgage holder form
- New hampshire notice of intent not to renew at end of specified term from landlord to tenant for residential property form