Add eSignature Presentation Secure
Make the most out of your eSignature workflows with airSlate SignNow
Extensive suite of eSignature tools
Robust integration and API capabilities
Advanced security and compliance
Various collaboration tools
Enjoyable and stress-free signing experience
Extensive support
How To Encrypt Sign Presentation
Keep your eSignature workflows on track
Our user reviews speak for themselves






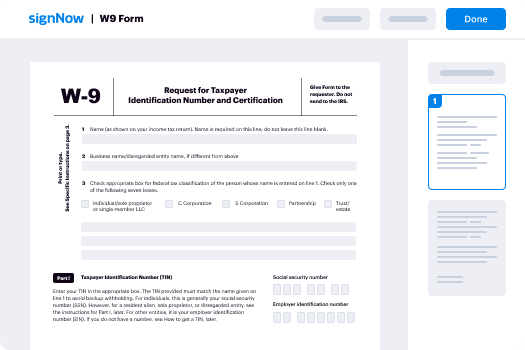
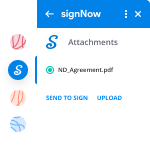
Add eSignature Presentation Secure. Investigate one of the most customer-friendly experience with airSlate SignNow. Control all of your document digesting and discussing process electronically. Move from portable, pieces of paper-structured and erroneous workflows to programmed, digital and faultless. It is simple to produce, produce and indicator any paperwork on any product just about anywhere. Ensure your crucial enterprise instances don't move overboard.
Discover how to Add eSignature Presentation Secure. Adhere to the basic guide to get started:
- Create your airSlate SignNow account in click throughs or log in together with your Facebook or Google profile.
- Take pleasure in the 30-day time free trial version or pick a prices prepare that's great for you.
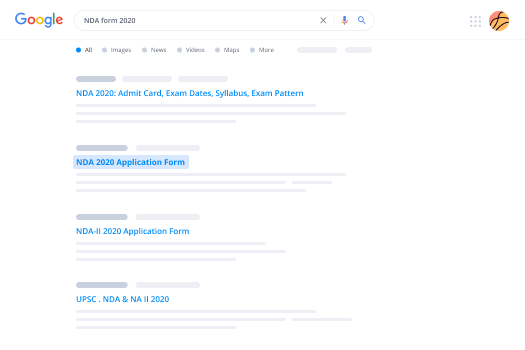
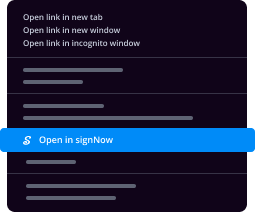
- Find any legal web template, create on the web fillable varieties and discuss them firmly.
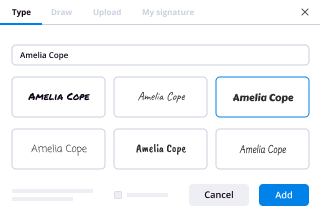
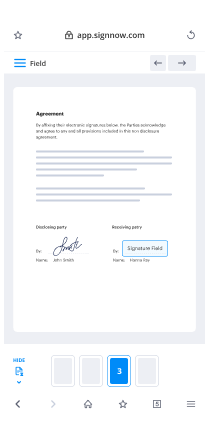
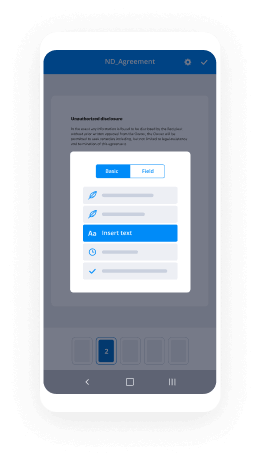
- Use innovative features to Add eSignature Presentation Secure.
- Sign, modify signing purchase and accumulate in-individual signatures ten times more quickly.
- Set up automatic reminders and obtain notices at each and every move.
Shifting your tasks into airSlate SignNow is simple. What comes after is a simple procedure to Add eSignature Presentation Secure, as well as recommendations to keep your peers and partners for much better collaboration. Empower your staff together with the greatest instruments to remain on the top of company procedures. Increase productivity and size your business quicker.
How it works
Rate your experience
-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
Intuitive UI and API. Sign and send documents from your apps in minutes.
A smarter way to work: —how to industry sign banking integrate
FAQs
-
What is the best real estate technology?
A survey conducted by Coldwell Banker and CNET found that eighty-one percent of prospective home buyers were drawn to homes equipped with the latest in-home technology. Among those, thirty-five percent of people who preferred what is known as smart homes over traditional residences believed that such features solidified the property as “move-in ready.”Technology is also changing the field of home selling. Here are five ways that apps and other online features are making the life of a real estate agent easier.1. Broadcasting with Periscope and TwitterWhat better way to send out a massive blast than on Twitter? The social media site lets you keep it short but sweet as you tell followers that the home of their dreams has an upcoming open house session. You can also post pictures on Twitter that give potential buyers a better perspective of what they will see during their in-person tour of the property. Take the virtual showing a step further by using Periscope to share live footage of yourself walking through the house online. In past times, a substantial amount of money was necessary to promote property by way of commercials. Twitter and Periscope bring the perk to you for free so long as you have a smartphone or tablet when going live and taking pictures.2. Tracking with Glympse and WazeRunning twenty minutes behind used to be a deal breaker pre-Digital era. Not only did you inconvenience the client but you also provided a guess that was often inaccurate and led to more time wasted at the property. Traffic apps in the twenty-first century have made such estimating unnecessary.Waze is one app that provides navigation tips based on real-time traffic information. You can better coordinate appointments so that clients are not left waiting for several minutes and provide clearer updates when you are running late. Glympse also tracks traffic in real-time but takes things a step further by offering a link by which clients can track your whereabouts. Text or email the URL to prospective buyers and let them follow along as you make your way to the location.3. Meet Online with Reflector 2 and Join.meReal estate agents should consider investing in Reflector 2 instead of bringing their USB stick along to nail that next listing presentation. The app serves as a sort of projector by allowing you to cast all activity on your smartphone and tablet on a larger screen. The Reflector 2 works with nearly any device and does not require additional purchase outside of the app itself.Free Screen Sharing, Online Meetings & Web Conferencing is another app that has made buying a selling a home more convenient. Agents can hold brief meetings with clients without requiring them to come into the office. Sharing your computer screen is the best way to convey pertinent information to new homeowners. The recording and playback feature is particularly useful when you need to recall a client’s home preferences. They will be impressed with your attention to detail in finding a house with a built-in barbecue pit. You will know that such meticulousness is because of Free Screen Sharing, Online Meetings & Web Conferencing.4. Add Transparency and Rapidity with an Automated Mortgage Loan ProcessThe traditional method of the home loan process involved hours spent trying to secure financing. Leaving one paycheck stub or bank statement at home often meant holding off on the process until the client was able to furnish proof of such documentation. There was no transparency in the process, which meant that customers were entirely reliant on the expertise of the real estate agent.Technological advances have revolutionized the mortgage loan process. Automated processing now establishes criteria by which applicants are judged that makes applying simpler. Some financial institutions can pre-approve hopefuls in ten minutes. Individuals who go through the entire process may see their loans finalized in ten days instead of the average four-week period. Digital tools provide real-time updates so that even those who are not approved can move on to the next bank quickly instead of waiting for a rejection letter to arrive by way of snail mail.5. Agree from Home with E-signaturesIn past times, the thrill of closing quickly became inconvenient for buyers upon hearing that all approved owners would need to stop by the real estate agent’s office to sign final documents. Some individuals were forced to take a sick day from work just to make their mark on the paper. Such heartache is why the masses are thrilled to learn that e-signatures have the same weight as traditional marks on legal documents. A real estate agent can email paperwork that his clients can sign at their leisure and return electronically. It is even possible to solidify documents on a smartphone in some instances, which makes the home loan process that much more convenient.
-
What digital tool, as a real estate agent, do you most use?
As an agent, we have access to the MLS, which the public only has limited access to. In my area the public can see exactly what Zillow can which is active listings. Our board does not disclose the sales price of closed prices, which makes services like Zillow pretty much worthless in my area. (Zillow may be useful in some areas, perhaps many, just not where I work).That said, my favorite and most useful tool, which is also available to the public, is the GIS (Government Information Service). Type in to Google: (Your county)(Your state) GIS [ie: Marion County Indiana GIS ] . While it isn’t available in every county of the country, you will find it in most major areas. It will give you access to the tax assessor records and often times the sales history of the property. The tax records will give you the details of site size, improvements, assessed values and depending on the county may or may not give you the annual taxes.Since real estate agents in some areas count the basement area when they list the size of the property, the GIS will allow me to figure out what is really there if I’m new to the area. For what I am looking for, there is a signNow difference between a stated 3,600 square foot house by the agent and 1,800 square foot above ground over a 1,800 square foot basement. - Lenders only count the above ground square footage as living area when making a loan.Hope this helps.
-
What is the difference between a digital signature and an electronic signature in your professional opinion?
Both terms - “electronic signature” and “digital signature” - are often used interchangeably, they aren’t exactly the same. Electronic signatures could be considered virtual representations of a pen-and-paper (“wet”) signatures. Digital signatures, also called cryptographic signatures, are a type of electronic signature that’s coded and encrypted in order to prevent the impersonation of a signee, tampering, and improve security overall.The main difference is that a digital signature is mainly used to secure documents and is authorized by certification authorities while an electronic signature (e-signature, e-sign) is usually associated with a contract where the signer has got the intention to do so: Difference Between Digital Signature and Electronic SignatureE-signature helps an individual to show his agreement to the conditions and terms of an electronic service. It can also be used to confirm the identity of the message's creator. Many countries give the same legal importance and significance to e-signatures as to traditional ways of executing documents. Here are the features of some most popular tools in this area: Best E-Signature Software Reviews & Comparisons | 2019 List of Expert's ChoicesWith electronic signature tools you avoid signing digital documents by hand - which is tedious cause otherwise you need to print, sign and scan all that stuff - that’s why such tools are on the rise. If you work with such signatures often, maybe you need some simple free tool which is specialized exactly for your business tasks. It really depends on the purpose for which you need this to sign an already typed document - it is often better to use a specialized tool, like Draw Your Signature Online and Sign PDF - CreateMySignature.com (instead of a regular image editor) to streamline your business documents workflow.
-
What's a safe website for fast cash loans?
Times can be tough, but that doesn’t mean you should settle for just any short-term loan you can find. Payday loans and installment loans aren’t legal in every state, and even if they are legal, lenders usually have to abide by strict regulations. Any lender that isn’t willing to comply with state law won’t be legit.Finding a legit lender doesn’t have to be difficult. All you need is a good sense of your state laws and a baseline for finding a good deal.What is a legit short-term loan?A legit payday loan is one that is offered to you legally. The lender needs to abide by the regulations set by your state, even if you are temporarily visiting somewhere else. Short-term loans can be applied for online and in-store but fall under the same regulations.Generally, short-term lenders have more relaxed criteria than banks and other lenders. You’ll be able to apply for a short-term loan if you have bad credit, are on a lower income or receive government benefits. However, the relaxed eligibility criteria does mean rates and fees are higher than other loans.Lenders still have to stick to state-mandated APR and can only lend up to the state’s maximum amount.Lenders must make a reasonable judgment on an applicant’s ability to repay the loan. The lender should assess factors such as income, housing expenses and existing debt in determining if the applicant can reasonably repay the loan.If a lender doesn’t ask you for any of that information or doesn’t attempt to evaluate if you can afford the loan, the lender probably isn’t legit. Since there are plenty of lenders that check, you should move on and find one that combines good terms with a strong lending ethic.
-
How are cracked versions of software created and why are developers not able to prevent it?
Cracked versions of software are created with the use of debuggers. (A debugger is a special type of software that lets programmers deconstruct their software into its constituent parts for the purpose of finding bugs, and thus de-bugging. Additionally debuggers can be used for reverse-engineering, or to see what is inside the software, to learn its logic. The latter method is used mostly by malware researchers to study what malware (or computer viruses) do on-the-inside. But it can be also used by an attacker to "crack" (or bypass) legal software registration, or at times, to alter normal behavior of software, for instance by injecting a malicious code into it.)For the sake of this example, I will assume that the software that is being "cracked" was compiled into a native code, and is not a .NET or a JavaScript based application. (Otherwise it will be somewhat trivial to view its source code.) The compiled native code is a bit more tricky "beast" to study. (Native means that the code executes directly by the CPU, GPU, or other hardware.)So let's assume that the goal of an attacker is to bypass the registration logic in the software so that he or she doesn't have to pay for it. (Later for lolz, he or she may also post such "crack" on some shady online forum or on a torrent site so that others can "use" it too and give him or her their appreciation.)For simplicity let's assume that the original logic that was checking for the software registration was written in C++ and was something similar to the following code snippet:In this code sample "RegistrationName" and "RegistrationCode" are special strings of text that a legitimate software user will receive after paying for the license. (The name is usually that person's actual name or their email address, and the code is some string of unique/special characters that is tied to the name.)In the logic above, the function named "isRegistrationCodeGood()" will check if "RegistrationName" and "RegistrationCode" are accepted using some proprietary method. If they are, it will return true. Otherwise false. That outcode will dictate which branch (or scope) the execution will follow.So the logic above will either show that registration failed and quit:Or, if the registration code and name matched, it will save the registration details in persistent storage (such as the File System or System Registry) using the function named "rememberRegistrationParameters()" and then display the message thanking the user for registering:A "cracker" will obviously want to achieve the second result for any registration code that he or she enters. But they have a problem. They do not have the C++ source code, part of which I showed above. (I hope not!)So the only recourse for an attacker is to disassemble the binary code (that always ships with software in the form of .exe and .dll files on Windows, and mostly as Unix executables inside the .app packages on a Mac.) An attacker will then use a debugger to study the binary code and try to locate the registration logic that I singled out above.Next you can see the flowchart for a snippet of code that I showed in C++, presented via a low-level debugger. Or, as the code will be read in the binary form after compilation:(For readability I added comments on the right with the names of functions and variables. They will not be present in the code that an attacker could see.)(To understand what is shown above an attacker will have to have good knowledge of the Assembly language instructions for the native code.)I also need to point out that having a disassembly snippet like the one above is the final result for an attacker. The main difficulty for him or her is to locate it among millions and millions of other similar lines of code. And that is their main challenge. Not many people can do it and that is why software "cracking" is a special skill.So having found the code snippet above in the software binary file a "cracker" has two choices:1) Modify (or patch) the binary.2) Reverse-engineer the "isRegistrationCodeGood()" function and copy its logic to create what is known as a "KeyGen" or "Key Generator."Let's review both:The first choice is quite straightforward. Since an attacker got this far, he or she knows the Intel x64 Instruction Set quite well. So they simply change the conditional jump from "jnz short loc_7FF645671430" at the address 00007FF645671418 (circled in red in the screenshots) to unconditional jump, or "jmp short loc_7FF645671430". This will effectively remove any failed registration code entries and anything that the user types in will be accepted as a valid registration.Also note that this modification can be achieved by changing just one byte in the binary code from 0x75 to 0xEB:But this approach comes with a "price" of modifying the original binary file. For that an attacker needs to write his own "patcher" (or a small executable that will apply the modification that I described above.) The downside of this approach for an attacker is that patching an original executable file will break its digital signature, which may alert the end-user or the vendor. Additionally the "patcher" executable made by an attacker can be easily flagged and blocked by the end-user's antivirus software, or lead criminal investigators to the identity of the attacker.The second choice is a little bit more tricky. An attacker will have to study "isRegistrationCodeGood()" function and copy it into his own small program that will effectively duplicate the logic implemented in the original software and let him generate the registration code from any name, thus giving any unscrupulous user of that software an ability to register it without making a payment.Vendors of many major software products understand the potential impact of the second method and try to prevent it by requiring what is known as "authentication." This is basically a second step after registration, where the software submits registration name to the company's web server that returns a response back to the software of whether the code was legitimate or not. This is done by Microsoft when you purchase Windows (they call it "Activate Windows") and also by signNow, and many other companies. This second step may be done behind-the-scenes on the background while the software is running, and will usually lead to cancellation of prior registration if it was obtained illegally.So now you know how software is "cracked".Let me answer why it is not possible to prevent it. It all boils down to the fact that any software code needs to be read either by CPU (in case of a binary native code) or by an interpreter or a JIT compiler (in case of JavaScript or .NET code.) This means that if there's a way to read/interpret something, no matter how complex or convoluted it is, an attacker with enough knowledge and persistence will be able to read it as well, and thus break it.There is an argument though that cloud-based software is more secure, which is true, since its (binary) code remains on the server and end-users do not have direct access to it. And even though cloud-based software is definitely the future, it has some major drawbacks that will never allow it to fully replace your conventional software. To name just a few:Not everyone has an internet connection, or is willing to upload their data online. Additionally someone’s internet connection can be very expensive or too slow to make the software run very laggy.Then there’s a question of distributed computing. For instance, Blizzard Entertainment would never make “World of Warcraft” to fully run on their servers due to immense computational resources needed to render every single scene for every player they have. Thus it is in their best interest to let each individual user’s computer to do the rendering instead.As a software developer myself, I obviously don't like when people steal software licenses. But I have to accept it and live with it. The good news is that there are not that many people who are willing to go extra mile and search for a cracked version of software. The main problem for those who do, is that by downloading a patched executable, or an attacker's KeyGen or a Patcher, they are effectively "trusting" him or her not to put anything "nasty" into it that was not "advertised on the package" (stuff like trojans, malware, or keyloggers.) So the question for those people becomes -- is it worth the cost of the software license to potentially infect your system with a nasty virus?On the other side of the equation, some developers react very negatively to any attempts to steal their software licenses. (I was there too.) They try to implement all kinds of countermeasures -- anything from tricking reverse-engineers, to adding booby traps in the code that may do something nasty if the code detects that it is being debugged, to obfuscating or scrambling the code, to enforcing all kinds of convoluted DRM schemes, to blocking users from certain countries. I personally try to stay away from all of those measures. And here's why:A) Any kind of anti-reverse-engineering tactics could be bypassed by an attacker with enough persistence. So why bother and waste my time when I can invest that time into adding something useful to my software that will make it more productive for legitimate users?B) Some code packers could create false positives with antivirus software, which is obviously not good for marketing of that software. It also creates unnecessary complexity for the developer to debug the software.C) Adding booby traps in the code can also “misfire” on your legitimate users, which will really infuriate them and can even lead to lawsuits.D) Any DRM scheme will probably catch some 100 illegal users and greatly inconvenience 10,000 legitimate ones. So why do it to your good customers?E) Our statistics show that about 75% of all illegal licenses come from China, Russia, Brazil, to name the worst offenders. (I also understand that the reason may be much lower incomes that people have in those countries.) The main issue for us though was the fact that if we enforce our DRM or add some strong registration authentication, many people that wanted to bypass our registration would simply use a stolen credit card number. And we had no control over it. Our system will use it to send them a legitimate license only to have the payment bounce in weeks time. As a result we would lose the money that were paid for the license, plus the credit card company will impose an additional chargeback fee to our account, which may range from $0.25 to $20 per bad purchase on top of the license cost.F) As was pointed out in the comments, some companies may actually benefit from allowing pirated copies of their software. Microsoft for instance gets a lot of free publicity from people using their Windows OS, the same goes for signNow with their Photoshop. That is a good point that I agree with.So my philosophy is now this -- if someone wants to go extra mile and steal our software, go for it! They went this far to do it anyway, so they probably have a good reason. On the positive side there are so many other customers that appreciate the work that goes into creating software that greatly outnumber those that don’t.PS. Thank you for all your feedback! It makes me feel good that the knowledge I shared is useful to others.
-
What is a payday loan, and why are they so bad?
This is a loan intended to be short term “payday” came about as it was intended to be a loan to carry you over till you got your next paycheck.As others have noted they are very high interest rate loans. Having such a loan for a short period of time (1–2 weeks) is expensive but not unmanageable. If you take such a loan off and take a long time to pay it off, then it will cost you a fortune in interest payments.The main issue is that when you get the loans they have 1–2 year terms on them, thus the payments may seem like they are not too bad monthly, but in reality you are paying a lot of interest and little on the principle so over that time you may pay double or triple the loan you took out (assuming you don’t just pay it off right away.The secondary issue is that these loans tend to be geared towards and given to lower income people with bad credit. Someone with good credit, even with low income, likely can have a credit card that could cover some unexpected expense, which is still high interest rate but no where near as bad as a payday loan… people with bad credit however will turn to payday loans, and there is a reason they have bad credit and this is normally related to their lack of ability to manage money. Take someone who is not good at managing money, give them a high interest loan and a long time to pay it off and it is very bad for the consumer.The final issue is that people also don’t use these loans for what they should be used for. This likely falls back to the poor money management part of things. People will take one of these loans out so they can buy a video game system or a new big TV, not to cover a necessity till the next paycheck. Basically this starts a spiral of debt on the heads of people who in general cannot afford it.
-
What do I need to start my own crowdfunding platform, where do I start from?
The establishment of a crowdfunding website is not terribly difficult. However the establishment of a successful crowdfunding site is a whole other proposition entirely. The market is crowded with thousands of sites already in existence and hundreds more coming online weekly. While by no means do I wish to discourage you, a realistic perspective on the undertaking could help you save both time and money in pursuing a potentially fruitless endeavour.To undertake a project like this, you will need to establish a point of difference in the market. You need a clearly defined vision and plan for your platform. What will make someone choose your site over others? What unique purpose or functionality will the platform offer? Replicating sites like Kickstarter and Indiegogo without a unique twist will see you remain a small fish in a big pond.If you are confident that you have something unique to offer, then your next step will be to secure your domain. Depending on your skill set, you can either construct the site yourself or outsource it to a specialist. You will need to ensure you meet the regulatory and compliance standards of the country hosting the site. You will likely have to register the site as company and comply with legal and financial reporting regulations associated with the enterprise. I would also suggest securing your intellectual property such as your brand name and concept.From here, you will need to heavily market your services to potential customers. Crowdfunders will need some assurance that you have a captive audience and backers will need to see some attractive campaigns and a platform that offers them something better, something different or at least something more competitive than the thousands of other platforms out there already. Herein lies the challenge.How do you attract crowdfunders with no audience? How do you attract an audience with no campaigns? It can (and obviously has been) done, hence the numerous crowdfunding platforms available across the globe today.The most challenging aspect of this endeavour is the marketing. Sites such as Kickstarter achieved prominence as groundbreakers in the crowdfunding space. The were able to gain substantial organic signNow due to the excitement it garnered as an innovative offering. Indiegogo were able to leverage the popularity of Kickstarter by offering a cheaper and more flexible alternative during a time of few competitors. There are now thousands of these sites and more popping up every day.The platforms that are able to stand out from the crowd offer something different. The bones of the concept may be the same or similar, but the offering is unique. Take Go Fund Me for instance. The popularity this platform gained was from stepping away from products and services and into fundraising. If you want to succeed in this crowded market, I suggest you take a leaf out of the Go Fund Me book and find an angle that has yet to be exploited or a need that has yet to be addressed. Remember, starting a website and starting a business are one in the same. Before you proceed, ensure you have a thorough business plan in place. These can be downloaded online for free and are handy development tools. They force you to consider all aspects of the proposed business and can save you much heartache and pain by solidifying your vision before you spend any of your hard earned money or valuable time.I hope this helps.
-
Do you need a loan to stop your troubles? Easy loan?
Try this site where you can find the best solutions for all your personal financial needs://creditandfinancesol.info/index.html?src=compare//RELATEDCar Insurance parked hit and run question?I have USAA as my auto insurance. Here’s the back story. I was parallel parked alongside a street here in Atlanta and a car (more than likely) was trying to get out of his/her space and hit the left driver side bumper pretty hard (ruining the paint and loosening up the bumper pretty good…and cracking the tail light). This person did not leave a note. I have my 500 deductible. I also have uninsured motorists coverage. Right now USAA is saying that I will have to pay the $500 ded. Why couldn’t they put it under the uninsured motorists coverage I have instead so I wouldn’t have to pay a dime? Is it within reason to call them and ask for this issue to be adjusted? If so, what points can I make to insure I get the deductible taken care of under the uninsured motorists coverage? Thank you for your help!”How much would insurance be on a Nissan 350z?Hi guys!! Ok so I’m soon to get a 2003–2006 Nissan 350z Touring or Enthusiast. Maybe around 9000$ to 15000. I’m almost 18 and what would insurance be like for me??? Allstate, State Farm, ect. I just need a basic monthly quote! Thanks!!”Flying insurance????????????do u need insurance if you are flying in a private jet charter (like a private jet)What are the best websites to get car insurance quotes from different companies in New York City?What are the best websites to get car insurance quotes from different companies in New York City?Geico Car Insurance?I have a 2013 Mitsubishi Lancer GT. My mother took the loan out and I was wondering can I get my own insurance (19 years old) and insurance the mitsubishi even though the loan is in her name?Co-op Health Insurance?Can anybody out there tell me how does Co-op Health insurance work. im researching for a paper in my finance class and cant find info elsewhereWhat is car insurance for a first time driver?Okay i am 18 and have never had my license before and am going to be getting it at the end of this month…soon we are going to start getting insurace quotes for my car, we have been talking about what would be the best way to go about getting the cheapest insurance…so would it be best to put the car in my name but then just be added to my parents insurance and have me as the primary driver OR would it make a difference if we put the car in one of my parents name and then had me listed as the secondary driver for the car ? OR maybe you know a better way to go about this please give me all the advice you know about this! thanks”Will taking a defensive driving class lower my insurance and take points off my driving record?Ive been in two car accidents one in Nov.2007 and the other Feb. 2008 and i was wondering if taking a defensive driving course would take points off my driving record and lower my insurance.Car insurance INCREASE every 6 months with no accidents/tickets? wtf!?Last year I had Unitrin Direct….they were charging me $85 a month…this is with NO tickets or accidents for the last 5 years of my driving record….this is also with the BASIC insurance that you need in Florida…10/10/20…NO collision…and a $1000 deductible….. So at the end of my 6 months…it was time for a renewal…they tried to bump me up to $140 a month for no reason…still no accidents/tickets…nothing had changed…i had expected my rate to DECREASE….they tell me it’s a STATEWIDE INCREASE ……so i called around… Ended up switching to Allstate who has been charging me $90 a month (better than $140 right?)…..6 months go by, everything’s cool…..now my policy renewal is coming up and they’re trying to tell me i need to pay $160 a month for their basic insurance. Are you kidding me? And according to them it’s another STATEWIDE INSURANCE INCREASE …… They also told me that it could be due to not having CONSECUTIVE insurance for the last few years, as in…I switched from State Farm to Unitrin to Allstate……they told me call the state insurance commissioner…which I did…. Got connected to some guy in Gainesville who tells me that the INSURANCE companies are the ones who decide the rates and increases…not them. Pretty much BS….Allstate’s blaming the state, state’s blaming them…feels like a huge runaround to me. Guess my questions are…. Should I stick with Allstate and pay $160 a month for this absolute BASIC insurance (keep in mind..no collision, $1000 deductible)…my car’s not even worth a YEAR of their insurance. …. Or shop around? But if I switch back to Unitrin or get Geico or whatever….will I risk having ANOTHER increase after 6 months? And is it true that one of the reasons for these statewide increases is not having consecutive insurance with the same company for so many years? Thanks all.”I’m on a fixed income with 3 cats. Does any cat owner know of a good affordable cat insurance plan?*I purr..fer to hear from people that already have a good affordable cat insurance plan.
-
Can I borrow some money?
if you need money, there are ways you can get it safely and quicklyThere are times in life where you need money for a late bill or an emergency expense, but you might not know where to start on an often time-consuming and frustrating process. Our article below outlines the ways you can borrow money fast so you don’t have to spend time worrying about filling the gap between paychecks.Few month ago I need some urgent money, My friend Henry suggest me to take money from this website its reliable and you can get urgent money just after fill a form.So I did it.And get Money within 3 hours .This is the website URLOnline short term loans have less strict requirements than a traditional loan.One way to minimize interest rates how much a short term loan will cost is to only borrow the amount of money you need to cover your expenses and to choose the shortest repayment period you can afford.Here is the process3 Easy Steps1. Complete the Short Loan Request Form2. Our Network of Lenders Reviews Your Request – You Can Get a Loan Offer3. If Approved, Review and Accept Your Loan – All Conveniently OnlineRemember, our service is free and you’re not obligated to accept any loan offer.Eligibility:You do not need to have a perfect credit score to be eligible for a bad credit loan. Customers with poor credit may still qualify for a loan; however, our lenders do not typically provide loans over $1,000 to bad-credit individuals. Please note that meeting these requirements does not mean you will be connected to a lender.Requirements:Be at least 18 years old.Provide proof of citizenship, such as a Social Security number, or legal residency.Have a regular income, either from full-time employment, self-employment, or disability or Social Security benefits.Have a checking account in your name.Provide work and home telephone numbers.Provide a valid email address.Loan Process:Our loan request process is designed to connect you with the lender from our network who can assist with your financial needs. If successfully connected, our lender network will verify your information quickly and review your loan request.Depending upon the information you provide, a lender might respond with a loan offer. You should take your time in reviewing all details of any loan you’re considering. You will not be obligated to accept the offer if it is not the right offer for you!When you decide to accept your loan, just agree to the lender’s terms via e-signature. (Remember, you are under no obligation to accept any loan offered.)Once you add your electronic signature to the lender’s contract, they will distribute the loan funds to your checking account via direct deposit. All funds should be available as soon as the next business day, however, the exact availability timeframe will depend on your lender’s deposit process.Best and trusted online loanRepayment:The lender will present you with the repayment schedule and you will be able to repay your installment loan off over time rather than all at once.That’s all there is to it! Our lenders require no collateral, and you will not be denied a loan solely based on a poor credit history. Your steady income and checking account is the only security required.Note: Bad Credit Loans is not a lender; rather, They specialize in connecting borrowers with Their network of bad credit lenders and financial service providers. Bad Credit Loans cannot dictate your loan terms, conditions or interest rates/fees.
Trusted esignature solution— what our customers are saying
Get legally-binding signatures now!
Related searches to Add eSignature Presentation Secure
Frequently asked questions
How do i add an electronic signature to a word document?
How to esign a filable pdf file?
What is my esign password for sscw?
Get more for Add eSignature Presentation Secure
- How Can I Electronic signature Iowa Real Estate PPT
- How Do I Electronic signature Iowa Real Estate PPT
- Can I Electronic signature Iowa Real Estate Document
- Help Me With Electronic signature Iowa Real Estate PPT
- How Can I Electronic signature Iowa Real Estate PPT
- Can I Electronic signature Iowa Real Estate PPT
- Can I Electronic signature Iowa Real Estate PPT
- How To Electronic signature Iowa Real Estate Word
Find out other Add eSignature Presentation Secure
- Trimet public records request form
- Class 5 form fill up
- John lies del mar picks today form
- Confirmation of vacating premises eviction notice form
- Formulario inscripcion cursos cortos doc
- Third party authorization form roundpoint mortgage servicing
- Ensav4 module 01 fundamentals of network form
- Medical history supplemental form us naval sea cadets
- Respite care invoice idaho federation of families idahofederation form
- Leter motivuese form
- Advanced algebra linear regression calculator worksheet 2 5 form
- Mdc online form
- Guiding questions for reading the ramayana answers form
- Georgia visa application form pdf
- Irrevocable trust agreement legal forms legalforms
- Mv2548 permanent disabled parking indentification permit dot state wi form
- Child pick up authorization letter form
- Leader and times form
- Orea form
- Hoya hiring form