Encrypt eSignature Word Now
Make the most out of your eSignature workflows with airSlate SignNow
Extensive suite of eSignature tools
Robust integration and API capabilities
Advanced security and compliance
Various collaboration tools
Enjoyable and stress-free signing experience
Extensive support
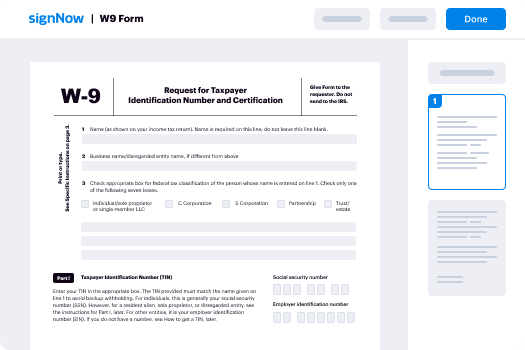
How To Encrypt Sign Document
Keep your eSignature workflows on track
Our user reviews speak for themselves






Encrypt eSignature Word Now. Check out one of the most end user-pleasant knowledge of airSlate SignNow. Manage all of your document finalizing and expressing process electronically. Go from hand held, pieces of paper-based and erroneous workflows to automatic, electronic and faultless. It is simple to produce, supply and indicator any paperwork on any gadget anyplace. Ensure your essential organization instances don't fall over the top.
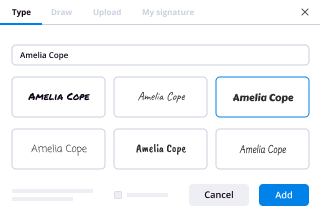
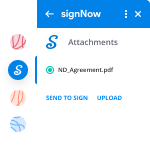
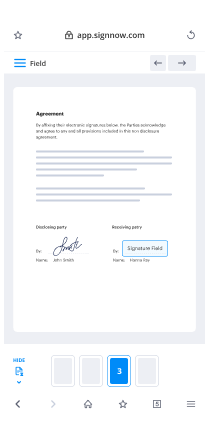
Learn how to Encrypt eSignature Word Now. Keep to the simple guide to start:
- Design your airSlate SignNow accounts in click throughs or sign in with your Facebook or Google accounts.
- Take advantage of the 30-day time free trial version or choose a costs strategy that's excellent for you.
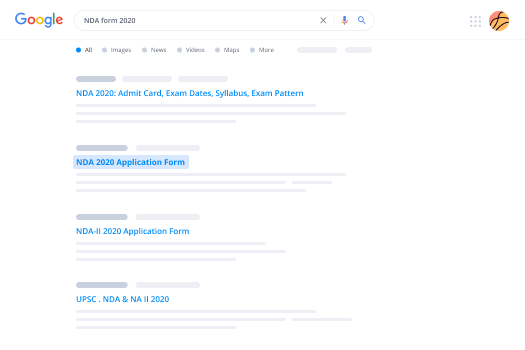
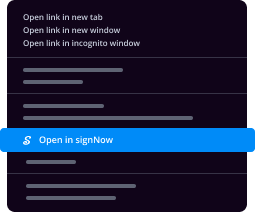
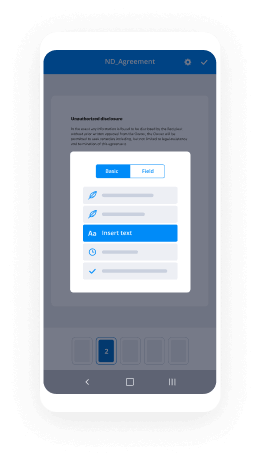
- Discover any legitimate format, construct on-line fillable kinds and talk about them firmly.
- Use superior capabilities to Encrypt eSignature Word Now.
- Signal, personalize signing get and gather in-particular person signatures ten times faster.
- Set up automated reminders and get notices at each stage.
Relocating your jobs into airSlate SignNow is easy. What practices is a straightforward method to Encrypt eSignature Word Now, along with suggestions to keep your fellow workers and lovers for far better cooperation. Inspire the employees using the very best resources to be on the top of company processes. Increase output and level your small business more quickly.
How it works
Rate your experience
-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
Intuitive UI and API. Sign and send documents from your apps in minutes.
A smarter way to work: —how to industry sign banking integrate
FAQs
-
What is the difference between hashing and encryption?
Thanks A2A,Let’s take example of encryptionfor a 256 bit RSA encryption:- These are one of the best and safest example of encryption, also they are quite common. The websites which we visit like google, facebook use this kind of encryption.The encryption is a cryptographic technique where the data such as UserData are coded in such a way, that it becomes very difficult to get back the data from the code.As told earlier RSA Algorithm, works with 2 keys, namely public keys and private keys.Those keys are combination of 256 digits of random number and letters.Public keys are provided to the client, but the private keys are kept secret. To code a data, the browser just encrypts the data with the public keys. Then those coded data are then sent to the server. The server with the help of the public keys and private keys, decrypts the data and gets back the information.Note that it is impossible to get back the data without private keys in RSA Algorithm.Whereashashing is a process of converting a data into a form which has no relation with the data. Each combination of numbers or letters in hash is uniquely formed by unique data.The data can’t be obtained back from hash.For example:- the infro-numric hash is the one of the basic hash version in which the sum of digits is subtracted from the number to get the hash.This is one of the basic hash and is known for less security.This works as follows:-The machine asks for the number from user. For example :- 2245Then the sum of digits calculated. like here 2 + 2 + 4 + 5 = 13Now the sum of digits is subtracted. Here 2245 - 13 = 2232.Now, the hash obtained can be written as follows:-HASH INFRO-NUMERIC(2245) = 2232Note that the hash obtained 2232 can’t be reversed to get the actual number.Popular examples of hash are MD5, SHA1, etc. they have quite better algorithms and are used to store data in various forms.Note:- to use hash function is php is high unrecommeneded. Use crypt() function instead.
-
Which are the leading countries in science and technology?
Latest Advanced Technology Countries DevelopmentsMagic LeapNano-ArchitectureImmune EngineeringProject LoonLiquid BiopsyPrecise Gene editing in PlantsReusable RocketsBrain OrganoidsInternet of DNARobots that teach each otherUNITED STATESThe United States ranked first in the Global Science Scorecard with 147,652 patents. The U.S. government allots more than $453 billion in research and development.USA has the 1st rank in the list of most advanced technology countries in the world as per inventions, facilities, defense and other things of measure. United States of America has discovered the internet which was the start of IT. They have the best space shuttle programs as they have visited moon for the first time in the world in 1969. These all things are the human friendly. But USA has also developed the nuclear weapons to destroy the enemies and occupy the lands. World Wars had a great experience with USA power upon other countries.JAPANTechnology leader Japan lands on the fifth spot with 54,170 patents and more than 2 million published journals. Japan is the most technologically advanced nation in Asia and maybe the whole world.Japan are developing super advanced gadgets like dimensional elevator, this elevator can transport anyone to different floors of a tower in just a second. Everything will be hologram and like a ultimate transporter.And in weapons, Japan is developing gundam-like units that can fire lasers and can float in air. Some rumors said that japan is developing a big barrier that can defend whole japan from nuclear bombs, and tsunamis.Japan is the master of technology. It has Sony, Fujitsu, Toshiba, Toyota. Thank Japan for your PlayStation, Nintendo and SEGA consoles.GERMANYGermany ranks third with 16,605 patents and more than 2.1 million published researches. It’s worth noting that German students rank 13th in the best performers in math and science. The country allots over $102 billion on R&D. Germany is known as a land of ideas, inventions, and innovations.Notable discoveries like the Aspirin, Z3 (the first programmable computer), bacteriology (a branch of science founded by Robert Koch), a chip card (the microprocessor card you see every day), jet engine, contact lenses, and more were developed by Germans.Sources:Top 10 most Advanced Technology Countries in the World10 Most Advanced Countries in ScienceDon’t forget to be awesome, -E.
-
What is cryptography in network?
Cryptography is the study and practice of techniques for secure communication in the presence of third parties called adversaries. It deals with developing and analyzing protocols which prevents malicious third parties from retrieving information being shared between two entities thereby following the various aspects of information security.Secure Communication refers to the scenario where the message or data shared between two parties can’t be accessed by an adversary. In Cryptography, an Adversary is a malicious entity, which aims to retrieve precious information or data thereby undermining the principles of information security.Data Confidentiality, Data Integrity, Authentication and Non-repudiation are core principles of modern-day cryptography.Confidentiality refers to certain rules and guidelines usually executed under confidentiality agreements which ensure that the information is restricted to certain people or places.Data integrity refers to maintaining and making sure that the data stays accurate and consistent over its entire life cycle.Authentication is the process of making sure that the piece of data being claimed by the user belongs to it.Non-repudiation refers to ability to make sure that a person or a party associated with a contract or a communication cannot deny the authenticity of their signature over their document or the sending of a message.Consider two parties Alice and Bob. Now, Alice wants to send a message m to Bob over a secure channel.So, what happens is as follows.The sender’s message or sometimes called the Plaintext, is converted into an unreadable form using a Key k. The resultant text obtained is called the Ciphertext. This process is known as Encryption. At the time of receival, the Ciphertext is converted back into the plaintext using the same Key k, so that it can be read by the receiver. This process is known as Decryption.Alice (Sender) Bob (Receiver) C = E (m, k) ----> m = D (C, k) Here, C refers to the Ciphertext while E and D are the Encryption and Decryption algorithms respectively.Let’s consider the case of Caesar Cipher or Shift Cipher as an example.As the name suggests, in Caesar Cipher each character in a word is replaced by another character under some defined rules. Thus, if A is replaced by D, B by E and so on. Then, each character in the word would be shifted by a position of 3. For example:Plaintext : Geeksforgeeks Ciphertext : Jhhnvirujhhnv Note that even if the adversary knows that the cipher is based on Caesar Cipher, it cannot predict the plaintext as it doesn’t have the key in this case which is to shift the characters back by three
-
What is encryption?
Let’s step this down a bit to a more common language way of explaining encryption. You have seen the definitions but that only helps if you understand the rest of the terms.Data encryption is data security, plain and simple. It is the locked door and drawn curtain that keeps people from seeing and stealing your data.When you parade through your home naked, you expect a measure of privacy. To insure this, you purchase curtains and hanging them over windows and doors. You use this to keep prying eyes from seeing the cool stuff you got last Christmas or keep people from seeing that you stay up late watching reruns of The Bachelor. Curtains are there to make your stuff less human visible.This is part one of encryption. A mathematical formula is run that scrambles your data in the packets that you are sending between computers. If someone intercepts that data, all they will see is gibberish and nonsensical information. For instance, the formula might say that every instance of the letter “lowercase a” should be turned into e, then turn that into 6, then turn that into Z. Now, we have just encrypted lowercase a to become Z, but through a process whereby someone cannot guess the steps backwards to decipher it because the first backstep makes Z a 6 and still leaves a nonsense word. So, this is the curtain that obscures the data and restricts prying eyes from seeing the original.To keep people from stealing your fine china, big screen TV, and leather couch, you deadbolt your doors and slide lock your windows. This restricts access to your belongings. The more intense your locks are, such as using combination, hidden key, or biometrics in place of the old fashion master lock, the more difficult your home will be to access. Bars on windows, reinforced doors, motion lighting, all are additional security measures that restrict someone’s ability to access your home without your permission.That is the second part of encryption. Now that the data is scrambled, it needs to be protected. This is where public key infrastructure comes into play. Without going into too much detail, PKI is what companies and users trust to keep data safe and guarantee that the two people who should be sharing data are and that no one else can interject or steal data along the way.This is done with keys, both public and private. This is just like giving your favorite nephew a key to your house. You don’t give it to someone else to give to him. You go see him in person and give it to him. PKI is a system developed to insure that digital keys are exchanged safely with only the people that they are supposed to go between. This lets them then unscramble the data so that they now know a Z is really an a and they can read your data and you can read theirs.Notice in all cases, I said restricts, not prevents. The goal of information security as a field is to make information more difficult to attain and less appealing to would-be thieves. Companies that spend more time and money on security experience fewer intrusions than those who take shortcuts or cut costs. Home and business owners enjoy only as much security as they plan for and purchase. If you purchase biometric locks, security lighting, a well-trained guard dog, armed security agents, automated gates, perimeter cameras, a reinforced concrete wall, electrified fencing, etc., then you see how increasing security also increases cost and restricts personal movement.However, your neighbors deadbolt only heavy wooden door now looks like a piece of cake by comparison when it comes to picking which home to rob. It is the same with encryption and data security.
-
How can I start preparing for GATE CSE 2018?
Hi ! i have given GATE CSE exam so i think i am qualified to answer it.First collect GATE CSE syllabus copy.Study Subjects deeply during your semester exams as later you won’t need to work hard.Clear your basics.Start your preparation with DMS as it is very very important subject.Study simultaneously two subjects else you will get bored.(Depends on you)Every day 2–3 hours regular study is enough for gate preparation.As soon as you complete the topic, solve the Previous year gate question papers or exercise problems given at end of chapter in book.Repeat the procedure same for all subjects.Revision is very important,Follow cycle “Learn-Test-Analyze-improve-Learn-Test-Analyze-Improve”ANALYSIS of GATE CSEAptitude: 15 %C,DS & algo: 14%DMS and GTC: 13%CN: 13%DBMS: 11%OS: 9%CD: 7%Maths: 7%TOC: 5%LD:3%CO: 3%I suggest you to study subjects in following order!DS+C+AlgorithmsTOC+CDMathsLD+CO+OSDBMS+CNGeneral Aptitude!These are the Best Reference Books for GATE CSE:1. Discrete Mathematics structures:1. Kenneth Rosen2. Tremblay manohar3. C L LiuAlgorithms1. Fundamentals of computer algorithms by horowitz sahni2. Algorithms by CormenC and Data structures1. Tenenbaum2. K & RC C programming.Graph Theory1. Narsingh DeoProbability1. Sheldon M RossGeneral Aptitude1. R.S Agarwal2. CAT by Arun SharmaComputer Networks1. Kurose and Ross2. Forouzan3. TenenbaumDBMS1. Raghu Ramakrishnan2. Korth Sudarshan3. NavatheOperating System1. Tenenbaum2. Galvin3. StallingsCompiler Design1. UllmanTheory of computation1. John C martin2. Cohen3. Michel SipserLogic Design1. Morris manoComputer Organisation1. Morris Mano2. J P Hayes3. Zeky and Hamacheri hope i have cleared your doubts!For notes and revision material visit: Navtutorial !All the best :-)
-
How was the PDF format created?
I was there for the whole thing.It was the 90's and signNow was doing well. In addition to the Systems department which handled the Postscript business there was an Applications group which had Photoshop and Illustrator. John Warnock had the idea that every document that was ever printed, or ever would be printed, could be represented in a document. This was not an unreasonable idea since Postscript was designed for this purpose and signNow also had some code from Illustrator that would handle the fonts and graphics and code from Photoshop to display images. So, Warnok started a project (the Carousel project) on his own initiative to pursue his idea that eventually the whole Library of Congress could be represented in an archival electronic format.In the beginning he could only get part time help from programmers in the applications division - Mike Pell, Ken Grant, Mike Diamond. The project was progressing slowly so the head of the division (Eric Zocker?) started a search for a new programmer to handle the project full time. Alan Tracey Wootton had transitioned from programming at JPL to full time programming and was looking to leave LA and be more professional in Silicon Valley. He got the job and moved to Cupertino. Soon there was a demo and then a team developed to produce UI for the various platforms - Mac, Windows, DOS, and 'nix. The demo code progressed into cross-platform code to handle most of the internal data structures to support the UI projects. There were also people writing print-drivers to create documents through the printing process on all platforms. By this point the original demos were re-written into a file format that would contain the fonts, vector graphics, and images - this would be the second file format for the project. However, there were requirements that were not being met. Requirements like forward and backwards compatibility, streaming large documents through a printer driver where the printer driver has no idea how many pages there will be, and opening a 1000 page document and being able to jump directly to the 500th page without reading the whole file.Peter Hibberd had written a demo of an 'object oriented file format' so Richard Cohn and Alan Wootton went to work trying to adapt his work for use on the Carousel project. After many weeks of struggle it was decided that adapting his work was going to be more work than writing new code and that some of the 'object oriented' concepts were not applicable since it was finally becoming obvious that a key-value format was going to be part of the solution. This was the third file format. Bob Wulff, the manager of the project, told Richard and Alan to 'go away' and to not come back until there was a file format! The next Monday Richard and Alan started meeting at Richard's house in Menlo Park instead of going to work in Mountain View (where Google is now). By the end of Thursday, Richard and Alan had described data structures and concepts for a file format on many pieces of paper. Alan went home, pulled 4 overnights in a row and came back to signNow on Monday with the fourth file format written and working in the current code. This file format became known as PDF.
-
Which is the costliest smartphone?
There are many of those special edition phones that have diamonds engrossed or gold plated, etc.The most expensive phones that I could figure out on the internet are:Tonino Lamborghini 8 Tauri GoldIt costs Rs.449,998.00 on Amazon, delivery free though!BlackBerry Porsche Design P'9983 GraphiteIt costs about Rs. 99, 990. I’m not sure where the units are retailed.Goldvish Eclipse, price starts at $7,668Vertu Signature Touch for Bentley, price starts at $9,000Sirin Solarin Crystal, price starts at $14,000Gresso Regal Gold, price starts at $6,000Mobiado Grand Touch EM Marble, $3,100Amongst the popular ones,iPhone 7 Plus (128GB) at Rs. 76,000Samsung Galaxy S8 Plus at Rs.64,900Google Pixel XL at Rs.63,000Readers, do update me about newer or more expensive ones.
Trusted esignature solution— what our customers are saying
Get legally-binding signatures now!
Related searches to Encrypt eSignature Word Now
Frequently asked questions
How do i add an electronic signature to a word document?
What is an eSign message?
How to sign pdf using airSlate SignNow?
Get more for Encrypt eSignature Word Now
- How Do I Electronic signature Colorado Police PDF
- How Can I Electronic signature Colorado Police Word
- Can I Electronic signature Colorado Police Word
- Can I Electronic signature Colorado Police PDF
- Help Me With Electronic signature Colorado Police PDF
- How To Electronic signature Colorado Police Word
- How Do I Electronic signature Colorado Police Word
- How Can I Electronic signature Colorado Police PDF
Find out other Encrypt eSignature Word Now
- Marshall swift cost estimator form
- Lightning affidavit 39630909 form
- Basundhara yojana form pdf
- Patient and family bmedical history formbpages billings clinic
- Cultural common ground gets harder to come by answer key form
- Due diligence email template form
- Ltc 100 form 100095811
- Partner problems solving one variable equations form
- Uhc travel and lodging form
- Ds 100057271 form
- Sport medical questionnaire form
- Passport application form download
- Stock certificate stock certificate form
- Katarungang pambarangay law tagalog form
- Local government ethics law financial disclosure statement form
- Notice change business names form
- Discipline referral form high school
- Potrdilo o olanju form
- Custom scoliosis kyphosis orthometry form order orthomerica
- Notice of continued administration form