E-mail Electronic signature PDF Simple
Make the most out of your eSignature workflows with airSlate SignNow
Extensive suite of eSignature tools
Robust integration and API capabilities
Advanced security and compliance
Various collaboration tools
Enjoyable and stress-free signing experience
Extensive support
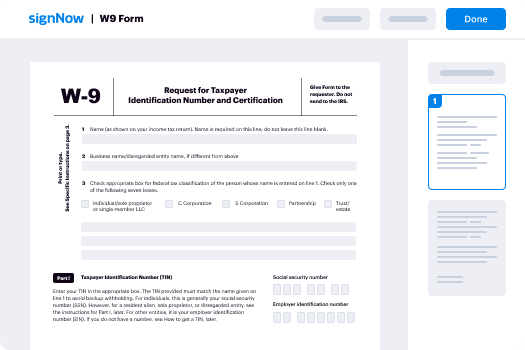
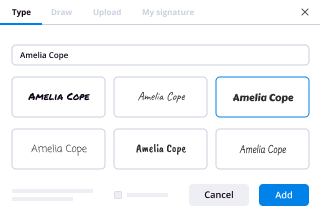
How To Add Sign in eSignPay
Keep your eSignature workflows on track
Our user reviews speak for themselves






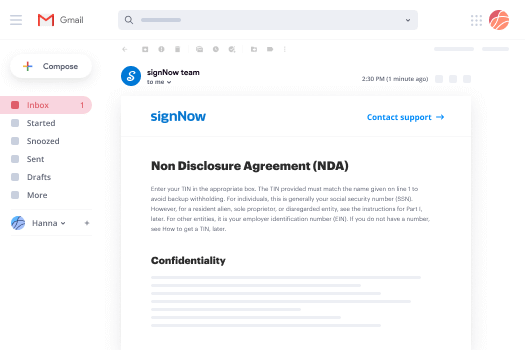
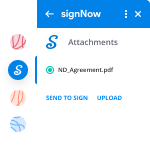
E-mail Electronic signature PDF Simple. Discover by far the most end user-warm and friendly experience with airSlate SignNow. Manage your entire document processing and discussing system electronically. Change from hand held, document-centered and erroneous workflows to programmed, computerized and faultless. It is possible to create, produce and indicator any paperwork on any device just about anywhere. Make sure that your important company instances don't slip overboard.
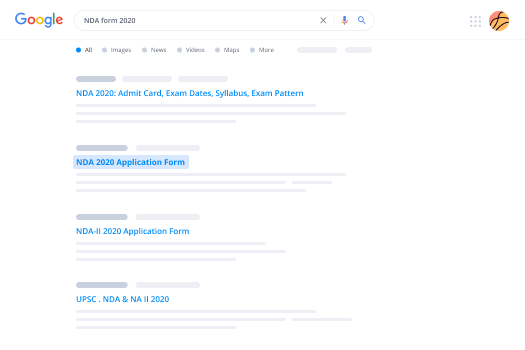
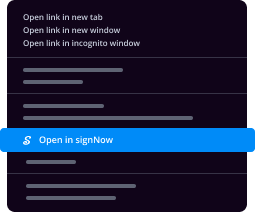
Find out how to E-mail Electronic signature PDF Simple. Keep to the easy guideline to start:
- Build your airSlate SignNow bank account in clicks or sign in with the Facebook or Google accounts.
- Take advantage of the 30-working day free trial or select a costs program that's excellent for you.
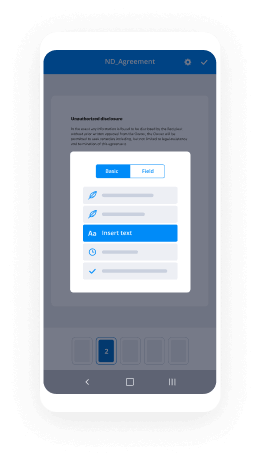
- Get any legal web template, build on-line fillable forms and talk about them safely.
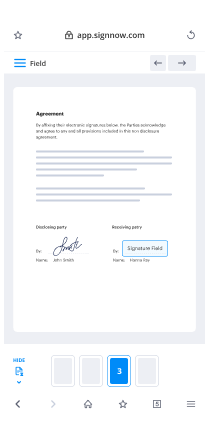
- Use innovative capabilities to E-mail Electronic signature PDF Simple.
- Indicator, individualize putting your signature on purchase and acquire in-particular person signatures ten times faster.
- Establish auto alerts and get notices at each and every step.
Moving your duties into airSlate SignNow is simple. What practices is an easy process to E-mail Electronic signature PDF Simple, in addition to ideas to help keep your co-workers and companions for far better alliance. Encourage the employees together with the very best tools to remain on top of company operations. Boost productivity and scale your business speedier.
How it works
Rate your experience
-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
Intuitive UI and API. Sign and send documents from your apps in minutes.
A smarter way to work: —how to industry sign banking integrate
FAQs
-
How can I sign a document online for free?
If you have been in the corporate world for a while, it is sure that you must have come across the term Electronic signature or eSignature. Basically it refers to signing a document online in the digital form. These signatures hold equal legal acceptance and importance like that of a handwritten signature. What is the need to sign documents online? Coz it’s just a matter of few clicks Think of times when you were asked to sign and return PDF or a document. What was the process? Well the traditional method was to download the form, go to your printer, print it then sign on it using a pen which then is scanned and mailed back. If the entire process is carried out digitally then why not sign it online as well? Well you’ll be glad to know that document signature software [ https://www.esignly.com ] have made the entire process simple and easier than you think. In just few clicks you can sign any number of documents and send it the same time. Much easier than the paper process. Now the question is how to Sign A Document Online For Free? As more and more people have chosen electronic signature technique in order to save hours of their valuable time, several electronic document signature software are available in the market. Let’s look at some top trending document signature software of 2019: * eSignly * signNow * SignNow * signNow * signNow E-Signature * signNow * signNow * signNow * eSignLive * signNow * signNow * signNow and many more…. The above mentioned lists are some booming digital signature software preferences that holds maximum share in the industry. Many corporate or legal entities are utilizing these platforms in carrying out electronic signatures. Any of these document signature api [ https://www.esignly.com/esignly-api.htm ] provide e-signature solutions as a free offering. They often carry out free trials for its customers but this should be noted that it is limited for one time. If you require extensive solutions with added benefits and facilities then certain amount of investment will be required to buy subscriptions. You can select any of these options mentioned above to sign up for a free trial and you are good to carry out signing your crucial business documents for free using digital signatures.
-
How do I open an account with Zerodha? What are all the things I need?
If you want to trade, i.e. buy and sell securities, in the Indian stock market, you’ll need to open a demat account. Let’s learn more about a demat account:Demat Account – DefinitionWhy A Demat Account?Demat Account – Features & BenefitsOpening A Demat Account(1)Demat Account – DefinitionAs mentioned earlier, a demat account is just like a bank account where you hold your securities instead of money. Buying and selling of these securities happen through a demat account.(2)Why A Demat Account?By using a demat account, you need not worry about mutilated share certificates, postal delays, and counterfeit shares. A demat account is a safe and convenient means of holding securities.(3)Demat Account – Features & BenefitsAs opposed to dealing in physical certificates and facing delays with your transactions, holding and trading securities via a demat account has the following advantages:You won’t have to worry about the safety of your shares, bonds, debentures, etc. They are secure in a demat accountTransaction costs are lower than when dealing with their physical counterpartsWith a demat account, it is easy and simple to invest in securities onlineYou can sell as many shares you want, even one is fine, whenever you wantPhysical certificates come with risks such as theft, fake certificates, forgery, bad delivery, transfer delays, etc. A demat account eliminates all these threatsElectronic settlements are super easy and convenient with a demat accountTransferring securities is faster, thanks to reduced paperworkBest demat account providers in india with NSE active clientsZerodha (7,89,526)Sharekhan (5,63,526)Axis securities (4,14,450)Angel broking (4,10,384).Kotak securities (4,04,365)(4)Opening A Demat AccountWhen it comes to demat accounts, there are two terms that you need to understand – depositories and depository participants (DPs). There are two depositories that are SEBI-registered :-National Securities Depository Limited (NSDL)Central Depository Services Limited (CDSL).These depositories hold your electronic securities and allow you to make transactions.The depository participants are the middle-men (or agents) that work between you, as an investor, and the depository.You’ll need to open an account with the DP (which is actually the demat account) in order to avail the facilities offered by the depositories.Choose a depository participant (A depository participant can be a financial organisation like:BanksBrokersFinancial institutionsCustodiansYou can open Demat Account online within few minutes. You just need to have scanned copies of:(i) Aadhaar Card No(ii) PAN Card No(iii) 1 cancelled Cheque (It should contain your name, IFSC Code, MICR No). Else you can you use latest Bank Account Statement.(iv) Your Signature on a piece of paperNow lets get started & open the Zerodha Account:1. Click here to go to the account opening page. Open an online trading and demat account with Zerodha and enjoy the lowest brokerage .2. After doing so, you need to fill up your details like Name, Mobile number (NOTE: Your Aadhaar should be linked to this mobile no if you want to open the account online. For offline, you can give any mobile no) and email id & then click on CONTINUE TO SIGNUP.3. Click on CONTINUE TO SIGNUP. Then, you will receive a mail on the e-mail id entered by you to reset your password.You will need to click on “Click here” to set your password. Choose a strong password with a combination of alphabets, numbers & symbols.4. Now after, That You need to Fill up your PAN details and Date of Birth, You need to check mark the box, for confirming PAN details.5. Then in Step 1, you will be asked to opt your Trading choices, If you are new to stock market you can simply choose Equity and Currency option (300 ₹ ) as I have done so. But, if you want to trade commodities as well then select that option too.6. Then, you will asked to pay the amount for opening a Trading account with Zerodha. Pay the amount from your preferred payment method (Card/ Netbanking/ Wallet).7. After payment, you will receive you will see Congratulations message displayed on screen. Below that you need to fill up more details as shown in below picture.First you will have to fill up Bank Details (Branch’s IFSC, Bank Account No)Then below that you will have to fill up Background Info (Mother’s first name, mother’s last name, marital status, occupation etc). After filling, you should tick all the 3 boxes below & click on CONTINUE.8. A new page will open where you will see the option of “Instant Account Opening with Aadhaar”. If you do not have a digilocker account, you need to create it first by clicking on the link mentioned there (shown in image below).A new page like this(image below) will open. There you will have to register by entering your mobile no & verifying OTP.Then you need to set your username & password.After that you need to link your Aadhaar by quoting Aadhaar no verifying with OTP (OTP will come in no registered with Aadhaar).Thats it your DigiLocker account will be created. Now you need to return to the previous tab where you were opening Zerodha Account.Tick both the boxes & then click on LINK YOUR DIGILOCKER WITH ZERODHA.9. A pop up will appear where you need to sign in to your DigiLocker account by entering username & password. (Do not forget to tick the box “I allow DigiLocker to share my documents with Zerodha….”)Select your Aadhaar Card from there.After that you need to again click on LINK YOUR DIGILOCKER WITH ZERODHA.10. A new screen will come displaying “Let’s finish the application”.Below that you have to again fill up some details like Marital status, Father’s first name, Father’s last name etc. You will again need to fill up Bank Account & Background Info although you had already filled up the same in previous pages.Tick the 3 boxes & click on CONTINUE.11. Next is IPV Verification over webcam/phone.You should write down your OTP shown on screen on a piece of paper or receive it on your smartphone by clicking on the link on the page(Step 1)Then hold the piece of paper/ mobile phone with the code infront of your mobile phone/ webcam. (As shown in image below).Click on Start IPV. Then click on Take Video. Then click on SAVE IPV.12. Now you will have the option to either Digitally sign the application with Aadhaar (mobile OTP) or else print & courier it. I will suggest you to select Aadhaar Option.13. Now you need to upload the scanned copy of the documents: Bank Account Proof, Signature, PAN (Note: Format of PAN scan should be jpg/jpeg ie it should be an image format. Rest all can be pdf format). Income Proof is optional & only required if you want to trade Futures & Options.14. Now is the time to eSign. If you had opened only Equity account, you will have to only eSign Equity. Click on eSign Equity.A popup will display. You can proceed with Google+ or through email where you will have to verify OTP sent to your registered mail.Then a popup will appear. You have to tick on the box (I agree to do eKYC…) & click proceed to eSign.You will be then redirected to NSDL website where you will have to enter your Aadhaar No & then verify OTP. (Do not forget to tick the box: I hereby…).Then you have to click Sign Now.The again the same NSDL website will re-appear. You will again have to enter Aadhaar No & verify OTP.15. You are almost done. Now you will have to download the Demat POA form, fill it up & send it to the address mentioned there.NOTE: Transaction charges at Zerodha(for purchasing/selling stocks) after account opening are as follows-Thanks for your patience for going through my lengthy post.So go ahead and open your account at Zerodha
-
What types of websites are most likely to contain viruses or malware?
What types of websites are most likely to contain viruses or malware? Websites that sell ads from real-time ad broker networks. By far, by far, the most common way for viruses and malware to be spread from Web sites is through poisoned ads.What is the most dangerous website?So be careful when you visit these sites, since your computer may not come out in good health, after your visit.#1 Ucoz. com. Description: Site hosting. Global rank in malware hosting: 14.#2 sapo .pt.#3 Amazonaws .com.#4 Blogspot .de.#5 4shared .com.#6 sendspace .com.#7 comcast .net.Can certain websites cause viruses?Yes, it's entirely possible to get infected by simply visiting a website. Most commonly via what we call "Exploit Kits". Right now, EK are used to deliver a lot of dangerous malware (such as banking trojans and Cryptoware) to computers worldwide. So using a standard Antivirus and Antimalware won't cut it.Can you get a phone virus from a website?How phones get viruses. The most common way for a smartphone to get a virus is by downloading a third-party app. However, this isn't the only way. You can also get them by downloading Office documents, PDFs, by opening infected links in emails, or by visiting a malicious website.Threat 1 >> Malicious Flash files that can infect your PCThe Place: Websites that use FlashsignNow's Flash graphics software has become a big malware target in recent years, forcing the company to push out frequent security patches. But another danger you might not know about is associated with Flash cookies. Flash cookies are small bits of data that their creators can use to save Flash-related settings, among other things. But like regular cookies, Flash cookies can track the sites you visit, too. Worse still, when you delete your browser's cookies, Flash cookies get left behind.If You Have to Go There: To help protect against Flash-based attacks, make sure you keep your Flash browser plug-ins up-to-date. And you can configure the Flash plug-in to ask you before it downloads any Flash cookies.Threat 2 >> Shortened links that lead you to potentially harmful placesThe Place: TwitterScammers love Twitter since it relies so much on URL shorteners, services that take long Internet addresses and replace them with something briefer.And it's very simple to hide malware or scams behind shortened URLs. A shortened link that supposedly points to the latest Internet trend-du-jour may be a Trojan horse in disguise.If You Have to Go There: Simply don't click links. Of course, that takes some of the fun out of Twitter. The other option is to use a Twitter client app. TweetDeck and Tweetie for Mac have preview features that let you see the full URL before you go to the site in question.Some link-shortening services, such as Bit.ly, attempt to filter out malicious links, but it seems to be a manual process, not an automatic one. TinyURL has a preview service you can turn on.Threat 3 >> E-mail scams or attachments that get you to install malware or give up personal infoThe Place: Your e-mail inboxAlthough phishing and infected e-mail attachments are nothing new, the lures that cybercrooks use are constantly evolving, and in some cases they're becoming more difficult to distinguish from legitimate messages. My junk mailbox has a phishing e-mail that looks like a legitimate order confirmation from Amazon. The only hint that something's amiss is the sender's e-mail address.If You Have to Go There: Don't trust anything in your inbox. Instead of clicking on links in a retailer's e-mail, go directly to the retailer's site.Threat 4 >> Malware hiding in video, music, or software downloadsThe Place: Torrent sitesTorrent sites (such as BitTorrent) are often used for sharing pirated music, videos, or software, and are a trove of malware. No one vets the download files--they may be malware in disguise.Ben Edelman, privacy researcher and assistant professor at Harvard Business School, thinks torrent sites are the most dangerous places to visit, since they don't have a business model or reputation to defend (by comparison, many porn sites rely on being deemed trustworthy). "The [torrent] customers, they really don't want to pay," he says.If You Have to Go There: It's probably best to avoid torrent sites entirely, given their untrustworthy content, but if you must visit, use a secondary PC to protect your main system. Use antivirus software, and keep it updated. Scan downloaded files and wait a couple of days before opening them. Brand-new malware can be tricky to catch, but the delay in opening may allow your antivirus software to get the necessary signatures.Threat 5 >> Malware in photos or videos of scantily clad womenThe Place: ‘Legitimate' porn sitesPorn sites have a reputation of being less secure than mainstream sites, but that assumption doesn't tell the whole story. "There is no doubt that visiting Websites of ill-repute is deadly dangerous. If you make a habit of it, it's a given that you'll be attacked at some point," says Roger Thompson, chief research officer with security firm AVG. "Unfortunately, staying away from those sites won't keep you safe by itself, because innocent sites get hacked all the time, and are used as lures to draw victims to the attack servers."And as mentioned earlier, many porn sites operate as actual, legitimate businesses that want to attract and retain customers. That said, it may be hard to tell the "legit" porn sites from malware-hosting sites that use porn as a lure.If You Have to Go There: Be suspicious of video downloads, or sites that require you to install video codecs to view videos (see the next threat, below). Using tools like AVG's LinkScanner and McAfee's SiteAdvisor (or SiteAdvisor for Firefox) can help you weed out the malicious sites.And, again, consider visiting such sites on a secondary machine. You don't want your browser history on the family PC.Threat 6 >> Trojan horses disguised as video codecs, infecting your PC with malwareThe Place: Video download sites, peer-to-peer networksIf you watch or download video online, you've likely been told to download a video codec--a small piece of software that provides support for a type of video file--at least once. Usually, these bits of software are perfectly legitimate (for example, the popular DivX codec), but some less-than-reputable download services or video sites may direct you to download a piece of malware disguised as a codec. Security software company Trend Micro provides a good example of what these attacks look like.If You Have to Go There: Your safest option is to stick with well-known video sites such as YouTube and Vimeo. And for catching up on the latest episodes of your favorite TV shows, sites and services like Hulu, http://TV.com, ABC Home Page - ABC.com, and iTunes are safer than peer-to-peer networks.Threat 7 >> Geolocation--your smartphone and perhaps other parties know where you areThe Place: Your smartphoneThe smartphone market is still in its infancy, really, and so are the threats. One possible concern is the use--or abuse--of geolocation. Although plenty of legitimate uses for location data exist, the potential for inappropriate uses also exists. In one case, a game listed on the Android Market was in reality a client for a spy app. In a less invidious example, a site called Please Rob Me showed that--for a time--a stream of FourSquare check-ins indicated that a person was away from their home (the site's goal, mind you, wasn't to condone theft, but to raise awareness of the issue).Apple recently updated its privacy policy to reflect changes in how it handles location data in iOS 4. The policy now states that "to provide location-based services on Apple products, Apple and our partners and licensees may collect, use and share precise location data." You can read more on Apple's new privacy terms and what they mean for you.If You Have to Go There: Be particular about the location-based sites, apps, and services that you use. As shown in the screenshot at right services such as Yelp provide good examples of useful location-aware apps. On the other hand, weigh the privacy implications of services like FourSquare or the new Facebook Places feature, and consider how much you feel comfortable divulging. (Read more on how to retain privacy on FourSquare and Facebook Places.)Threat 8 >> 'Poisoned' search engine results that go to malware-carrying WebsitesThe Place: Search enginesSearch engine poisoning is the practice of building tainted sites or pages that are designed to rank high in a search on a given topic. For example, according to a recent study by the security firm McAfee, 19 percent of search results for "Cameron Diaz and screensavers" had some sort of malicious payload. Breaking news topics and Facebook are also common search targets for attackers.If You Have to Go There: Pick and choose which sites to go to. Don't just blindly click search results; check each URL first to make sure that it really leads to the site you want.Threat 9 >> Malicious PDFs that try to fool you into installing malwareThe Place: Hacked Websites, plus your inboxAs Microsoft has become more serious about Windows security over the past few years, would-be attackers have had to find new ways to infect PCs. Attacking flaws in signNow is one of these newer methods. So-called poisoned PDFs are PDF files that have been crafted in such a manner that they trigger bugs in signNow and signNow; posted on a hijacked Website, they may let an attacker commandeer your PC and access your files and personal info.A newer variant takes an otherwise innocent-looking PDF document and inserts malware into it. signNow may pop up an alert asking if you want to run the malware, but hackers can edit those messages to trick you into opening the file.How serious is this problem? In 2009, attacks using malicious PDFs made up 49 percent of Web-based attacks, according to security firm Symantec.If You Have to Go There: First, always make sure that you're running the latest version of signNow.Threat 10 >> Malicious video files using flaws in player software to hijack PCsThe Place: Video download sitesAttackers have been known to exploit flaws in video players such as QuickTime Player and use them to attack PCs. The threats are often "malformed" video files that, like malicious PDFs, trigger bugs in the player software that let the attackers in to spy on you, plant other malware, and more.If You Have to Go There: Keep your player software up-to-date. Apple and Microsoft periodically release patches for QuickTime and Windows Media Player, respectively. Avoid downloading videos at random. Stick to well-known video sites such as YouTube, or to download services like iTunes.Threat 11 >> Drive-by downloads that install malware when you visit a siteThe Place: Hacked legitimate sitesA drive-by download occurs when a file downloads and/or installs to your PC without you realizing it. Such downloads can happen just about anywhere. Some sites are built to lure people into a drive-by download; but in a common attack method, criminals will hack a Web page, often on an otherwise legitimate site, and insert code that will download malware to your computer.If You Have to Go There: The first thing to do is to keep your security software up-to-date, and to run regular malware scans. Many security suites can flag suspicious downloads.Threat 12 >> Fake antivirus software that extorts money--and your credit card informationThe Place: Your inbox, hacked legitimate sitesFake antivirus programs look and act like the real thing, complete with alert messages. It isn't until you realize that these alerts are often riddled with typos that you know you're in trouble.Most fake antivirus software is best described as extortionware: The trial version will nag you until you purchase the fake antivirus software-which usually does nothing to protect your PC. Once you send the criminals your credit card information, they can reuse it for other purposes, such as buying a high-priced item under your name.Threat 13 >> Fraudulent ads on sites that lead you to scams or malwareThe Place: Just about any ad-supported WebsiteHey--ads aren't all bad! They help sites pay the bills. But cybercriminals have taken out ads on popular sites to lure in victims. Last year, the New York Times site ran an ad from scammers, and earlier this year some less-than-scrupulous companies were gaming Google's Sponsored Links ad program and placing ads that looked like links to major companies' Websites."The bad guys have become very clever at exploiting online advertising networks, tricking them into distributing ads that effectively load malicious content--especially nasty, scaremongering pop-ups for rogue antispyware," says Eric Howes, director of research services for security firm GFI Software.If You Have to Go There: Most large sites, such as PCWorld - News, tips and reviews from the experts on PCs, Windows, and more, have ad sales departments that work frequently with a core group of large advertisers, so it's probably safe to click a Microsoft ad on the New York Times site. But as the Google Sponsored Links incident shows, nothing is entirely fail-safe.Threat 14 >> Questionable Facebook appsThe Place: FacebookFacebook apps have long been an issue for security experts. You don't always know who's developing the apps, what they're doing with the data they may be collecting, or the developers' data security practices. Even though you have to approve apps before they can appear on your profile and access your personal information, from there the security of your data is in the developer's hands.If You Have to Go There: Be selective about the apps you add to your profile--don't take every quiz, for example. Check your privacy settings for Facebook apps, as well: Click the Account drop-down menu in the upper-right corner of Facebook's site, select Privacy Settings, and then click Edit your settings under ‘Applications and Websites'. There, you can control which apps have access to your data, and which of your friends can see what information from apps (such as quiz results); you can also turn off Facebook apps altogether.Threat 15 >> Sites that lure you in, get you to sign up, then sell your e-mail address for spamThe Place: 'Free electronics' sitesYou've no doubt seen sites around the Web blaring, Get a free iPad! Get a free notebook! A free iPod! It's easy! These sites aren't typically dangerous in the classical sense--you probably won't get infected with malware--but your personal information could be sold to other businesses, who can then use it to sell more stuff to you.If You Have to Go There: Read the privacy policies. And then read them again. Also, beware of privacy policy loopholes--even though a site says that it won't sell your private data to third parties, depending on the language of the policy, they may still be able to give your information to "affiliates."Threat 16 >> Phishing 2.0 on social networks that tricks you into downloading malware or giving your Facebook login information to a criminalThe Place: Social networksQuestionable Facebook apps and malicious shortened links aren't the only dangers lurking on social networks. Sites like Facebook have given rise to new forms of phishing. Scammers might hijack one person's Facebook account, then use it to lure that person's friend into clicking a malicious link, going to spam sites, or giving up their Facebook login information--thereby giving scammers one more Facebook account to hijack."One of the bigger dangers currently facing users is malware, adware, and spyware spread through social networks like Facebook and Twitter," says Eric Howes, director of malware research with Sunbelt Software. "Users may receive spam via these networks offering them free deals, links to interesting videos, or even widgets to enhance their Facebook profiles. In many cases what's really being pushed on users is adware, spyware, or even malicious software that can exploit users' PCs."If You Have to Go There: Don't trust every link posted to Facebook, even if one of your friends posted it. Be especially suspicious if the post is out of the ordinary for that person. Check the person's wall or Twitter @-replies to see if anyone is concerned that the person's account has been compromised.And if you suspect that your account has been hijacked, change your password immediately. Both Facebook and Twitter have resources to help you keep up-to-date on the latest threats on both sites. Facebook users should visit its security page; if you're on Twitter, be sure to follow @spam and @safety for Twitter security best practices.Threat 17 >> Oversharing--exposing too much personal information on your social network profilesThe Place: Social networksHow many times have you seen friends on Facebook or Twitter publicly divulge a bit more information than is necessary? Oversharing isn't just a matter of getting a little too personal--it can leave your private information viewable to the general public. But it's avoidable."There is a subtle danger that few people understand with the social networking sites, and that is the idea of information leakage," says AVG's Roger Thompson. "People, particularly teens, put all sorts of information online, without realizing that many more people than just their friends can see that data."Oversharing could very well lead to more serious privacy issues further down the road, Thompson adds. "As today's young teens signNow an age to apply for a credit card, I fully expect an onslaught of fraudulent card applications on their behalf, because they unwittingly divulged so much information. Harvesting is going on now, and we have no idea who is doing the harvesting."If You Have to Go There: This particular threat is relatively easy to avoid, in that a little common sense can go a long way: Just be mindful of what you post. Do you really need to publish your home address and phone number to your Facebook profile?Finally, be certain to check your privacy settings to make sure that you're not divulging your deepest, darkest secrets to all 500 million Facebook users.
-
What are the best property management systems?
There is no one property management system that is ideal for every use case. It depends on who you are and what you are looking for in the system.For residential property managers:If you are a professional property manager and have full service clients, then I have found the best softwares are Yardi and Appfolio. Yardi is a bit more of a “legacy” system — robust but not as fresh as Appfolio, promoting a great UI/UX (user interface and user experience). If you are a property manager and do not use software, then IMO - you are failing at your business. Software will reduce your overhead costs and help mitigate risks of forgetting lease renewals, late fees, etc.. The cost and time related to the setup can be gruesome, but it is well worth it in the end. You’ll be able to take on more clients and provide them with a much better experience.For residential property owners:The majority of owners across the US (80%) self manage their properties. Most of them do not use software, because it is a relatively new concept for them. From a systems perspective, it will depend on what you are looking to accomplish with your real estate goals.Here is an article that all owners should read to understand what kind of management system they want (passive or involved) and what type of solutions cater to their needs.
-
What is a Demat Account?
A Demat account is very similar to a bank account. In bank accounts you electronically hold money, whereas in Demat accounts you electronically hold shares. All buying and selling of shares happens through a Demat account. The Securities and Exchange Board of India (SEBI) mandates a demat account for share trading above 500 shares.With growing financial awareness, more and more people now want to dabble in the share market. To do this, one should understand the basic requirements to trade in shares.A company enlisted in a stock exchange, is under obligation to offer the securities in both physical and dematerialised mode. As the name suggests physical securities mean actual certificates giving information about the shares of a company owned by a person. In the same manner, Dematerialisation is the process of converting physical shares (share certificates) into an electronic form. Shares once converted into dematerialised form are held in a Demat account. Today, almost all of the shares trading happens using the Demat mode of shares.What is a Demat Account?A Demat account is very similar to a bank account. In bank accounts you electronically hold money, whereas in Demat accounts you electronically hold shares. All buying and selling of shares happens through a Demat account. The Securities and Exchange Board of India (SEBI) mandates a demat account for share trading above 500 shares.Why to use such an exclusive account?By using a Demat account, you need not be worried about mutilated share certificates, postal delays, and counterfeit shares. Demat account is a safe and convenient means of holding securities just like a bank account is for funds.What are the features and benefits of a Demat account?As opposed to the earlier form of dealing in physical certificates with delays in transaction, holding and trading in Demat form has the following benefits:Settlement of Securities traded on the exchanges as well as off market transactionsRisks like forgery, thefts, bad delivery, delays in transfer etc, associated with physical certificates, are eliminatedShorter settlements thereby enhancing liquidityPledging of SecuritiesShares allotted in public issues are directly credited into demat account of the applicants in quick timeAuto Credit of Rights / Bonus / Public Issues / Dividend credit through ECSAuto Credit of Public Issue refunds to the bank accountNo stamp duty on transfer of securities held in Demat form (as against 0.5 per cent payable on physical shares)Increased liquidity, as securities can be sold at any time during the trading hours (between 9:55 AM to 3:30 PM on all working days), and payment can be received in a very short period of timeChange of address, Signature, Dividend Mandate, registration of power of attorney, transmission etc. can be effected across companies held in Demat form by a single instruction to the Depository Participant (DP)Holding / Transaction details through Internet / emailWhat steps does on need to take to open a Demat account?As majority of shares trading happens through a Demat account, it is imperative that an individual dealing in shares has such an account. The minimum age for opening a Demat account is 18 years. To open a Demat account, you must:Choose a Depository Participant or DP (A Depository Participant can be a financial organization like banks, brokers, financial institutions, custodians, etc., acting as an agent of the Depository to make its services available to the investors)Fill up an account opening form provided by DP, attach relevant documents, and sign an agreement with DP in a standard format prescribed by the depositoryThe DP provides the investor with a copy of the agreement and schedule of charges for his future referenceDP opens the account and provides the investor with a unique account number, also known as Beneficiary Owner Identification Number (BO ID)Are there any important things that one must remember about Demat accounts?There are some things that you must know remember about Demat accounts:Pan card is mandatory for opening a Demat account (effective from April 01, 2006)Charges applicable (vary from DP to DP):Account Opening FeeAnnual Maintenance FeeCustodian FeeTransaction FeeSimilar to a bank account a Demat account may be closed after a period of inactivity. Check with the DP about the period and the charges associated with reactivating it.
Trusted esignature solution— what our customers are saying
Get legally-binding signatures now!
Related searches to E mail Electronic signature PDF Simple
Frequently asked questions
How do i add an electronic signature to a word document?
How to sign a pdf in paint?
When trying to esign a document i get error(273)?
Get more for E mail Electronic signature PDF Simple
- How Do I Electronic signature Idaho Sports Document
- Help Me With Electronic signature Idaho Sports Document
- How Do I Electronic signature Idaho Sports Document
- How Can I Electronic signature Idaho Sports Document
- Can I Electronic signature Idaho Sports Document
- Help Me With Electronic signature Idaho Sports Document
- How To Electronic signature Idaho Sports Form
- How Do I Electronic signature Idaho Sports Form
Find out other E mail Electronic signature PDF Simple
- Dxn product price list 2021 pdf form
- Hulamin job application forms
- Quantum mechanics by zettili 2nd edition solution manual pdf download form
- Esayidi application form
- Hostel form
- Pcso lotto online application form
- Hansen econometrics solution manual pdf form
- The statistics of inheritance pogil blank document form
- Echocardiography report template doc form
- North west college of nursing mafikeng campus form
- Free pdf to word converter online form
- Edd unclaimed money form
- Form f vlr
- Abhibus form
- Norwegian shareholder benefit request form 2021
- Ibbl debit approval form
- Ufeministi katika kilio cha haki form
- Pivot point cosmetology study guide answer key form
- Tsotsi full book pdf download form
- 451152921 form