Request Electronic signature Word Mac
Make the most out of your eSignature workflows with airSlate SignNow
Extensive suite of eSignature tools
Robust integration and API capabilities
Advanced security and compliance
Various collaboration tools
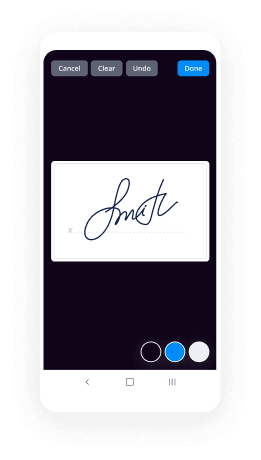
Enjoyable and stress-free signing experience
Extensive support
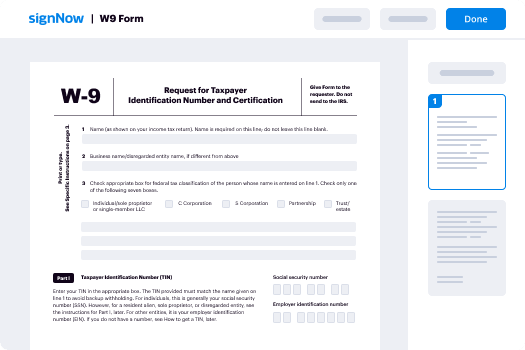
How Do I Add Electronic Signature in Grooper
Keep your eSignature workflows on track
Our user reviews speak for themselves






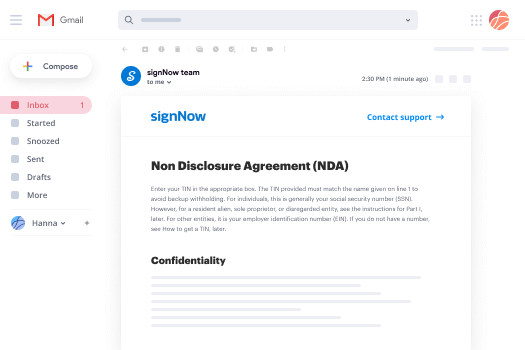
Request Electronic signature Word Mac. Check out one of the most user-warm and friendly exposure to airSlate SignNow. Deal with all of your document digesting and expressing method digitally. Go from hand-held, pieces of paper-dependent and erroneous workflows to automatic, digital and flawless. It is possible to create, supply and indicator any papers on any system anyplace. Make sure that your airSlate SignNow enterprise instances don't slide over the top.
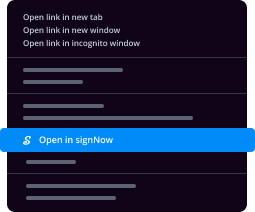
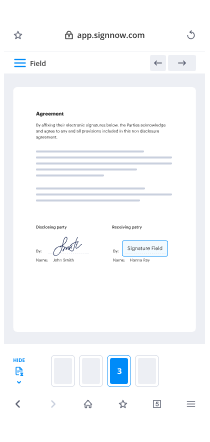
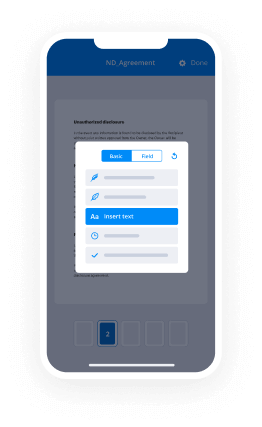
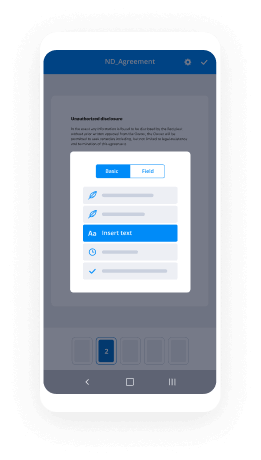
See how to Request Electronic signature Word Mac. Follow the basic information to begin:
- Design your airSlate SignNow bank account in clicks or log on with the Facebook or Google account.
- Take pleasure in the 30-time free trial version or select a pricing plan that's great for you.
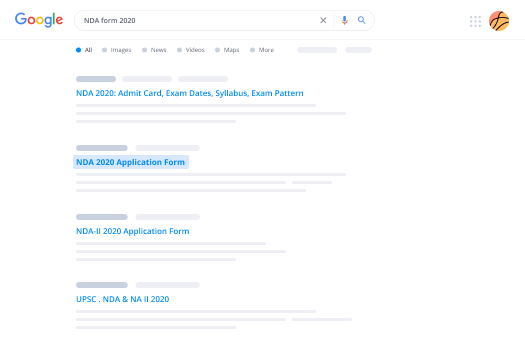
- Find any legitimate web template, construct on the internet fillable forms and reveal them tightly.
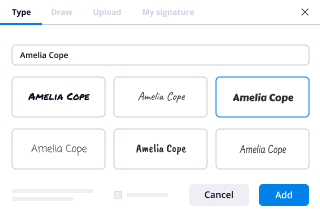
- Use innovative characteristics to Request Electronic signature Word Mac.
- Indicator, individualize signing buy and accumulate in-person signatures 10 times faster.
- Established intelligent reminders and acquire notifications at every stage.
Relocating your duties into airSlate SignNow is straightforward. What comes after is a straightforward method to Request Electronic signature Word Mac, along with tips and also hardwearing . co-workers and lovers for better collaboration. Inspire your workers with all the very best tools to keep on the top of organization processes. Enhance output and range your small business speedier.
How it works
Rate your experience
-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
Intuitive UI and API. Sign and send documents from your apps in minutes.
A smarter way to work: —how to industry sign banking integrate
FAQs
-
What are the information security procedures and practices that attorneys and law offices must follow in order to properly disch
My basic practical answer to the question is that there are no specific information security practices that lawyers must follow in order to fulfill their professional ethics responsibilities.Ansel Halliburton's answer references the correct ABA rule, but the case law on what "reasonable efforts to prevent the inadvertent or unauthorized disclosure of, or unauthorized access to" client information (ABA Model Rule 1.6) has never been tested as far as I know. The Model Rule and the comments do not specify any single security measure that lawyers must undertake under any set of circumstances. In practice, while some sensitive clients request their outside counsel follow particular security procedures, I think it would be incredibly difficult to make a case that an attorney violated their professional responsibilities by anything short of an intentional disclosure or something akin to a gross negligence standard or a total disregard for client information security. For example, if an attorney accidentally left a box of clearly marked confidential client documents in a coffee shop, became aware of the incident, took no steps to recover the documents, and failed to alert the client that the documents were lost, there may have been an ethical violation.Here are some situations that I have observed in practice or heard second-hand from other attorneys. I do not believe any of these would rise to the level of an ethical violation under the Model Rules, though they are not best practice. My understanding that these are not ethical violations is based on my personal judgment regarding reasonable information security measures, the reactions of other experienced attorneys, and the frequency with which such events occur.Taking confidential paper documents home from the office in a cardboard box (via means of their personal cars and kept in their shared residence with other family members);Leaving confidential paper documents on printers on open office floors or in unlocked offices or conference rooms (though there is usually a reception desk you would have to get past to get into office spaces);Having confidential client communications using third-party e-mail services, such as Gmail, Yahoo!, or Outlook (many solo practitioners or small law firms use such e-mail services);Storing confidential client documents on personal computers or personal phones;Having confidential client calls in public places (airport lounges, etc.); andWorking on confidential client matters on a laptop in a public place without a privacy screen.In all of these situations, the attorneys still may be taking reasonable measures to protect the client information and are not disregarding client confidentiality, but I don't think anyone would view these activities as best practices for information security. I think the acknowledgement of that reality motivated part of the ABA comment to Model Rule 1.6, which notes that some of the factors to consider in determining the reasonableness of the lawyer's efforts are: "the difficulty of implementing the safeguards, and the extent to which the safeguards adversely affect the lawyer’s ability to represent clients (e.g., by making a device or important piece of software excessively difficult to use)."
-
Who wins in a battle, The Predator or Deathstroke?
Depends on the Predator.A human one wouldn't pose much of a challenge. Jokes aside.There is no one Predator, they are a Species called Yautja and they have several ranks to explain their skill and experience.I am just going to say my knowledge on yautjas isn't as expanded as mine on Deathstrokes so feel free to correct me.For this Battle i will be using An Elite Yautja/PredatorVsCurrent Deathstroke from Earth 0 (Rebirth) wearing his classic uniform.This will be a random encounter, with standard gear in a neutral enviroment and will be to the Death, Incapacitation, Immobilization, or Surrender. They are also in character.Yautja AdvantagesShould be quite stronger based off casual feats.Should be more experienced in combat and older.Has alien tech Deathstroke wouldn't be familar with.Has more versatile and powerful weaponryCan use cloakingHas several forms of vision such as seeing heat due to mask.Deathstrokes advantagesHe should be quite faster and have better reflexesHe should be quite smarterHe should have an almost as versatile arsenal.He should heal faster from “non limb severing” wounds.He Should have weapons the Yautja haven't encountered such as a Promethium Blade, and a Titanium Plasma/Energy blasting staff.Honestly this fight is kind of a toss up in my opinion.While An Elite Yautja holds the strength and versatility advantages, Deathstroke holds the speed and intelligence advantages.In durability they are about equal.Skill is also debatable, seeing as how humans have managed to beat Predators but not usually elites while elites can take on multiple Xenomorphs, but Deathstroke can take on groups of Metahumans. I think i would give it to Deathstroke simply because he fights more versatile opponents, then just the same kind of hunts they were taught to fight and prepared to fight like Predators.Anyway this fight will have a lot of pauses and testing each other to see what their opponent can do or will do next.Id place my bet on Deathstroke but i again admit to knowing more about him than the Yautja.
-
What is encryption?
Let’s step this down a bit to a more common language way of explaining encryption. You have seen the definitions but that only helps if you understand the rest of the terms.Data encryption is data security, plain and simple. It is the locked door and drawn curtain that keeps people from seeing and stealing your data.When you parade through your home naked, you expect a measure of privacy. To insure this, you purchase curtains and hanging them over windows and doors. You use this to keep prying eyes from seeing the cool stuff you got last Christmas or keep people from seeing that you stay up late watching reruns of The Bachelor. Curtains are there to make your stuff less human visible.This is part one of encryption. A mathematical formula is run that scrambles your data in the packets that you are sending between computers. If someone intercepts that data, all they will see is gibberish and nonsensical information. For instance, the formula might say that every instance of the letter “lowercase a” should be turned into e, then turn that into 6, then turn that into Z. Now, we have just encrypted lowercase a to become Z, but through a process whereby someone cannot guess the steps backwards to decipher it because the first backstep makes Z a 6 and still leaves a nonsense word. So, this is the curtain that obscures the data and restricts prying eyes from seeing the original.To keep people from stealing your fine china, big screen TV, and leather couch, you deadbolt your doors and slide lock your windows. This restricts access to your belongings. The more intense your locks are, such as using combination, hidden key, or biometrics in place of the old fashion master lock, the more difficult your home will be to access. Bars on windows, reinforced doors, motion lighting, all are additional security measures that restrict someone’s ability to access your home without your permission.That is the second part of encryption. Now that the data is scrambled, it needs to be protected. This is where public key infrastructure comes into play. Without going into too much detail, PKI is what companies and users trust to keep data safe and guarantee that the two people who should be sharing data are and that no one else can interject or steal data along the way.This is done with keys, both public and private. This is just like giving your favorite nephew a key to your house. You don’t give it to someone else to give to him. You go see him in person and give it to him. PKI is a system developed to insure that digital keys are exchanged safely with only the people that they are supposed to go between. This lets them then unscramble the data so that they now know a Z is really an a and they can read your data and you can read theirs.Notice in all cases, I said restricts, not prevents. The goal of information security as a field is to make information more difficult to attain and less appealing to would-be thieves. Companies that spend more time and money on security experience fewer intrusions than those who take shortcuts or cut costs. Home and business owners enjoy only as much security as they plan for and purchase. If you purchase biometric locks, security lighting, a well-trained guard dog, armed security agents, automated gates, perimeter cameras, a reinforced concrete wall, electrified fencing, etc., then you see how increasing security also increases cost and restricts personal movement.However, your neighbors deadbolt only heavy wooden door now looks like a piece of cake by comparison when it comes to picking which home to rob. It is the same with encryption and data security.
Trusted esignature solution— what our customers are saying
Get legally-binding signatures now!
Related searches to Request Electronic signature Word Mac
Frequently asked questions
How do i add an electronic signature to a word document?
What is the original on an electronic signature document?
What is webpage error missing parameter installkey mean when trying to esign?
Get more for Request Electronic signature Word Mac
- Can I Electronic signature Iowa Police Presentation
- How To Electronic signature Iowa Police Presentation
- How Do I Electronic signature Iowa Police Presentation
- Help Me With Electronic signature Iowa Police Presentation
- How To Electronic signature Iowa Police Presentation
- How Do I Electronic signature Iowa Police Presentation
- How Can I Electronic signature Iowa Police Presentation
- How Do I Electronic signature Iowa Police Presentation
Find out other Request Electronic signature Word Mac
- Financial economics fabozzi solutions form
- Tertiary dance council physiotherapist examination form
- Ladder safety toolbox talk form
- Form 5119
- State form 390 r9 12 04
- Dd form 1586 instructions
- Bsa activity consent form
- Sf042 form
- Georgia cna registry form
- Unit remittance form the california state pta
- Grammar form and function 2b answer key
- Person participating form
- Shg grading sheet form
- Dcb bank forms
- Tanker inspection form
- Cancellation request form techchoice
- California apartment association lease agreement pdf form
- Storytown grade 1 pdf form
- Florida contracting classification premium adjustment program form
- Property damage claim form template