Search Sign Presentation Computer
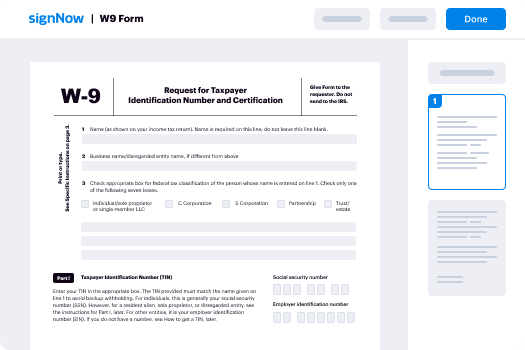
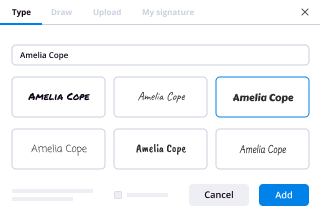
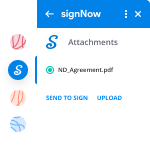
Make the most out of your eSignature workflows with airSlate SignNow
Extensive suite of eSignature tools
Robust integration and API capabilities
Advanced security and compliance
Various collaboration tools
Enjoyable and stress-free signing experience
Extensive support
How Can I eSign PPT for Administrative
Keep your eSignature workflows on track
Our user reviews speak for themselves






Search Sign Presentation Computer. Explore probably the most customer-pleasant exposure to airSlate SignNow. Manage your complete file finalizing and discussing program digitally. Move from hand-held, papers-structured and erroneous workflows to automatic, digital and faultless. You can actually create, supply and indicator any papers on any gadget everywhere. Make sure that your crucial business situations don't fall over the top.
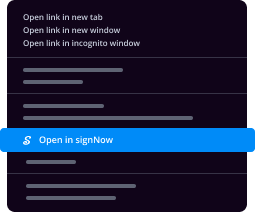
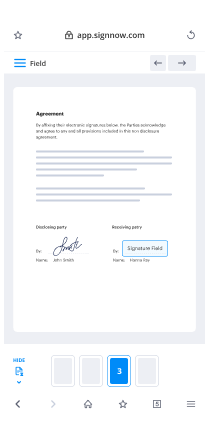
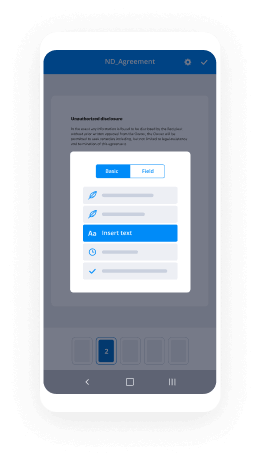
See how to Search Sign Presentation Computer. Stick to the easy information to get going:
- Make your airSlate SignNow accounts in click throughs or log in with the Facebook or Google bank account.
- Take pleasure in the 30-time trial offer or pick a costs prepare that's ideal for you.
- Locate any legitimate design, develop on-line fillable forms and talk about them securely.
- Use sophisticated features to Search Sign Presentation Computer.
- Signal, individualize signing order and collect in-individual signatures 10 times quicker.
- Established automated alerts and receive notices at every move.
Shifting your jobs into airSlate SignNow is uncomplicated. What practices is a simple method to Search Sign Presentation Computer, together with tips to keep your co-workers and lovers for far better cooperation. Inspire your employees with all the greatest equipment to be on top of company processes. Enhance productivity and size your business faster.
How it works
Rate your experience
-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
Intuitive UI and API. Sign and send documents from your apps in minutes.
A smarter way to work: —how to industry sign banking integrate
FAQs
-
What can I learn right now in just 10 minutes that could improve my algorithmic thinking?
Consider that most optimization-type problems can be solved with a very simple tree structure that explores all possibilities. For instance, if you wanted to create a change-making algorithm, which calculates the fewest number of commonly-used US coins needed to make change, you can simply explore every possible combination of coins. If this simple tree algorithm was used to calculate the coins for $.26 it would include:26 pennies (26 coins)21 pennies & 1 nickel (22 coins)16 pennies & 2 nickels (18 coins)...1 quarter and 1 penny (2 coins)And once all of the possibilities are calculated, you can easily see that 2 coins, the quarter and penny together, is the optimal solution. So now that you have created an algorithm to solve your optimization problem, you can start the task of optimization. Optimization of a tree-based algorithm revolves around two things: The algorithm should make a guess as to where to start looking for the optimal solution, and start there.Entire branches of non-optimal solutions should be eliminated as quickly as possible without evaluating every possible solution.So back to the change-making algorithm. This problem is trivial enough to make an intuitive leap: using large coins is better. So for the $.26 solution, if we started by using a quarter for one of the coins, we can instantly eliminate dozens of branches that use smaller coins to make the first $.25. This makes the calculation much faster. Also, by doing this, we are starting closer to the solution, because we know that if any solution includes a quarter, then that solution is better than all solutions that do not include a quarter. Starting with the largest possible type that fits is the basis of the "greedy algorithm" which is one of the most common algorithms used in optimization.Next time you run into any optimization problem, first consider if it can be solved (non-optimally) by a simple tree. If so, start there and then optimize the algorithm.edit: The generalization that larger coins are always better works for the US coin system, but perhaps not ALL coin systems (read comments for more info.) The greedy algorithm often needs to be tweaked to individual problems. Thank you Jimmy Kim for the catch.
-
What are some of the best technical hacks?
Here are few of my favourite technical hacks:1. If you accidentally close a tab, Ctrl +shift+T opens it.2. If you lost an android phone in your house and it’s on vibration, you can find it by going to Google Play > Android device manager > ‘Ring’3. An iPad charger will charge your iPhone much faster.4. If you want to buy the cheapest airline tickets, use your browser's incognito mode. Prices go up if you visit a site multiple times.5. If you’re at a hotel and run out of charges, the TV usually has USB plugin.6. Putiing your phone on airplane mode will stop ads while playing games.7. The pr...
-
What is the most asked question on Quora (by the number of questions merged into it)?
As someone who writes mostly technology-related answers, I see the following question so much it makes me want to tear my hair out:“Can iCloud Activation Lock be Bypassed?”For those who don’t know, Apple devices that have an iCloud account active on them with Find My iPhone enabled will lock the device to that Apple ID even if it is restored to factory defaults. This is designed to prevent thievery, since stolen devices (typically iPhones) are useless without the Apple ID password they are locked with to unlock it. It is incredibly common for people to sell devices without removing the lock beforehand (likely because they don’t know it exists, or how to remove it) or because it is stolen. Either way, the lock cannot be bypassed without that password… but that doesn’t stop everyone and their mother from asking if it can be done as if the rules somehow don’t apply to them.Instead of viewing the answers on an existing question, or even asking new people to answer that existing question, they make a new one. Every. Single. Time. Quora is absolutely flooded with these questions, and I get A2A requests for them more than anything else.
-
What was the most unsettling thing you’ve ever found in someone’s browser history?
A number of years ago I testified on behalf of the defence as an expert witness in a Crown v. the accused in an invitation to sexual touching and possession of child pornography case in a Canadian criminal court.Those are pretty serious charges and someone that engages in such behaviour should be separated from society for an extended period of time and then monitored afterwards.The police investigation started with a complaint by the mother to NCMEC that the accused had tried to lure her daughter into sexual relationship.When the Toronto police obtained a warrant and seized the accused’s computer they found evidence that he used the IRC online name in the mother’s complaint and they found hundreds of child porn images. Resulting in the charges.So why would I act for the defence?When I was first asked, I was given all kinds of assurances that the accused was innocent even though the police had seized his computer and found hundreds of images and had evidence that he had chatted online with an underage girl.I explained that I would examine the images of the hard disk that the police forensic team had prepared and I would examine the evidence submitted by the girl’s mother and then make my decision as to what assistance I would provide.At first it was extremely challenging to perform my examination. The police would not release a copy of the disk image, and rather insisted that I use their computer equipment using their software at their premises.I tried working in a tiny windowless room at one of the precincts on their laptop running their software - a copy of Encase on a Windows machine. Yuk. Severely limiting. Not only that the officer entered the room every 5 minutes to ‘chat’ and I would stop what I was doing, and turn the laptop away from him.What a joke. They claimed that I could not be in possession of the image as that would be a crime. Uh.. no it wouldn’t. The act specifically allows possession.Section 163.(6) No person shall be convicted of an offence under this section if the act that is alleged to constitute the offence(a) has a legitimate purpose related to the administration of justice or to science, medicine, education or art; and(b) does not pose an undue risk of harm to persons under the age of eighteen years.The defence lawyer was able to win a motion allowing me proper access to the evidence and I was given copies of the drive image to examine using my own tools and software. However the forensic team Sgt told me that he disagreed with the ruling and could have me arrested if I was ‘caught’ with the evidence.I knew it to be bs, but for quite some some time while working on the case I kept a copy of that section of the criminal code in my car and in my office.Since the girl’s mother has presented evidence of what she purported to be logs of an online chat I requested an image of her hard drive as well. The police refused as that they claimed would create a hardship for the victim.Hardship - Huh?I testified in a motion that since she was out of the country, she was in the U.S., that the police in that state could assist if require and all that really needed to be done, if both the Crown and the defence agreed, was to take the machine to a local computer shop and ask them to install a new drive of the same size and copy the contents across so they could continue to use their computer. Then to put the original disk in a box and ship it to the good Sgt of the Toronto Police along with a signed statement from the technician that he did that without making any deliberate changes to the original contents.The judge was pretty agreeable to that but the crown argued against it. I testified that it was the best evidence but I was prepared to offer my assessment of the printed logs and my assessment of the transcript of the mother’s testimony.The judge ended hearing only my assessment of that. No copy of the victim’s disk was ever obtained, nor required.In the end, I had the image of the accused’s computer and photocopies of the victim’s log and the transcript of the mother’s testimony.Let’s start with the ‘log’. It was doctored. It was not a real log from IRC. It certainly looked like one, but there were inconsistencies from what an actual log produced by the IRC client she was using and what was presented. Moreover, she ended up referring to a different conversation log in her testimony, one that had time stamps. The one originally submitted to NCMEC had no timestamp. That was a setting in that software. On or off. Moreover in the testimony she and the girl testified that they had never chatted with the accused before that conversation, yet..At the start of the log there was a line item..“nickname of the accused” is online.That meant that the user of that IRC client had created an alert to notify them when the accused came online in IRC. Interesting.I proposed to the court that a more likely scenario was that the mother had set a trap for the accused. Set the alert so she would know he when he was online, enter into a chat with him, and then fabricate a conversation.edit added: this gave the mother the IP address and a date and time when he was online. Subsequent warrant and examination of the accused’s ISP’s records identified him as the user of that IP address at the time.To demonstrate, I fabricated a fictitious log for the court involving an online chat between Hamlet and Horatio. With time stamps.I read Hamlet in open court. How cool is that?It had also been presented into evidence that the mother worked for a local ISP and had taken some computer forensic courses.I testified that I could not theorize motive for a deception other than perhaps some prior online argument of some unknown nature but that the mother certainly had method and opportunity to deceive.The judge asked me what I would look for if I had access to the mother’s hard drive. I explained how a filing system works and how logs are created with sequential allocations to a file entry and that I would expect to find only one version of a legitimate log, even if copies were made. But I would expect to find multiple versions of this log since I believe it to be true that it was fabricatedThe Crown eventually in his own statements referred to “the less than compelling evidence of the mother”, but the Crown still had the huge amount of irrefutable evidence of the possession charge.Now.. what about those hundreds of child pornography images?Yes, they existed. There were two sets.One set existed in a download directory for IRC. Virtually all were deleted. The ones that weren’t were quite new to the directory. I examined the IRC configuration and found that the accused’s IRC would auto-accept sent files from anyone.This guy’s machine had a huge number of images and files of all description in that directory and it appeared that he would go in maybe once a week and delete everything he did not want and move off what he did.No child pornography images were moved to other directories and the vast majority had already been deleted. I theorized that the ones that were not deleted simply had not been reviewed yet; and moreover the files that were deleted would have become unretrievable over the natural course of operating the computer.Now then, the other set.These were all in the browser cache, and they were virtually all thumbnail images. Hundreds of them. But..When I examined the raw browser history logs I found an interesting timeline.The accused was searching for different music genres for download. Several times during a one session he followed links that appeared to be for downloads of music but were for porn. Porn of every type imaginable.Several of these pages had large numbers of thumbnails. What was interesting is the time spent on the pages before the user attempted to go to another site or page. Seconds.It was also interesting that several of the pages caused new browser windows to open with more porn.In total, there was a 15 minute period on one day when all of the images that the Crown submitted as evidence were downloaded into the cache of the accused’s browser. Moreover it was doubtful that the accused even realized the full extent of the images since as I showed the court that one had to scroll down on the pages to see the thumbnails as across the top were simply more ads for more sites.I also testified that over the natural course of operating the computer these thumbnails would have been deleted by the browser and would have never been retrievable by the user.The judge had more questions for me in his attempt to understand the situation more clearly. The defence lawyer sat back and was feeling pretty good.The Crown and the good Sgt sat there clicking their pens for quite some time.The Crown ended up asking the court for a stay of prosecution in exchange for an undertaking by the accused to promise not to engage in chats with underage girls for the purposes of exploitation.This could have had a terrible ending for the accused. If he could not afford the professional fees that I charged, or could not afford a decent lawyer he would have been found guilty or he would have just plead guilty.A follow up, I saw that Sgt a few days later and he told me he was still positive that the accused was guilty and that I helped a guilty man go free. I asked him if he had any other evidence except that which I showed was all bs, and he said no, but he knew he was guilty. Guilty of what I wondered aloud.Sorry for any typos - written on my phone.
-
Is Quora turning into College Confidential?
The beauty of Quora is that it provides a forum for discussion on so many different and often self-contained topics. For people who, for example, are most interested in reading about college admissions, Quora might start to feel like College Confidential because those are the boards they're following.Here are some examples of Quora boards that might feel like other forum sites:College and University Admissions: College ConfidentialGraduate School Education: The GradCafe ForumsRecruiting: Glassdoor – an inside look at jobs & companiesEngineering Recruiting and Programming Interviews: Programming Interview Questions | CareerCup Investment Banking: Investment Banking & Finance Community Technology: Hacker News Computer Programming: Stack Overflow Web Search, Search Engines: Search Engine LandThe people on these boards might be talking about similar topics as their respective boards, which could be a sign that users from those sites are now coming to Quora instead to get their information. And an added benefit of using Quora instead of these other sites is that the answers are usually higher quality and presented in an order that is conveniently sorted by answer relevance. With Quora, you get all of the information from these other sites, without all of the noise.
-
What did your boss do or say to you that made you quit your job?
“Yeah, this little shit needs to stop making us clean up after him…”I was working an awesome job that I really liked. I was a cashier at a local health food grocery store. Since I was vegetarian, I loved chatting with most of the customers who visited; most of them were hippies, health nuts, or they just had a good amount of money and wanted the best food.When I have a job, I’m extremely committed to it. It was more important to me than school, so I told them I would come in on Monday mornings every week during the school year just because that’s when they needed me. I was working there for...
-
If Dennis Nedry didn't sabotage the computer system in Jurassic Park 1, could the park have operated safely?
Oh god, no. Remember the poor bastard who got torn to death at the start of the film trying to move a Raptor? The facilities were unsafe even when things were working, bringing the computers down only exacerbated the existing problems caused by extremely shoddy design.Had the park been properly designed, the electric fence going down wouldn't have mattered. Everything would have been built in such a way that would make it next to impossible for any dangerous specimens to signNow the areas the humans were located in. Just take a look at some of the ways modern zoos are built:Physical barriers, not electric fences. The movie did a pretty good job in showing how an electric fence stops being an effective barrier once the power goes out, but it wouldn't even be that reliable when the power was on. Imagine, for example, that two dinosaurs get into a fight and one knocks the other into the fence. No matter how badly it hurts, there's nothing that the dinosaur being electrocuted can do to avoid contact. And if the fence isn't strong enough to support that dinosaur's entire weight (which they clearly weren't, given how the larger dinosaurs walked straight through them) then it's going to collapse and probably break the circuit in the process. A big freaking wall on the other hand, built thick enough so that ten dinosaurs wouldn't be able to break it down with a concerted effort, isn't going to have that problem.Keep the visitors and the animals at separate elevations. It's one of the most basic and effective means of containing a dangerous predator out there - either put them in a pit or put your customers at the top of a cliff. If the T-Rex had needed to scale a seventy foot sheer wall of concrete and somehow swing around an angled guard fence at the top of it in order to signNow the cars full of tasty humans, she wouldn't have bothered. Maybe she'd have spent a couple minutes butting her head against the wall or scrabbling for purchase with her comically tiny forearms, but after that she'd have lost interest and gone in search of easier prey.Build absolutely everything to fail safe. I didn't see a single instance where this basic engineering principle was adhered to. The cars ferrying customers through the park stopped in the middle of the road when power was lost rather than continuing on their track back to the visitor's center, exposing their passengers to danger while also creating a traffic hazard. Manual overrides for power and backup generators were located in a remote, unstaffed location rather than immediately adjacent to the command center. The computers were apparently so complex that only a single person could figure out how to run them, and had no redundancy built in. They didn't even take basic precautions to prevent people from leaving protected areas (like the cars) and climbing into the fenced off areas. Apparently they just figured they'd be equally deterred by the electric fence that's been provisioned with enough power to warn off a twelve ton armored death lizard, which would be easily enough to kill a human if it arced through their heart (which very nearly happened).In short despite the repeated protestations made by Dr. Hammond that Ingen had spared no expense, Jurassic Park has every indication of being built on the cheap by a firm more concerned with cutting costs and presenting the illusion of elaborate protections rather than actually guaranteeing the safety of its visitors or staff. One might wonder if the actual reason for constructing it on Isla Nublar was actually to spare them from the obstacles of regular safety inspections or getting the government to sign off on a building permit. Though it's doubtful that would have shielded them from a barrage of civil suits from the survivors and the families of those who died in the disaster.
Trusted esignature solution— what our customers are saying
Get legally-binding signatures now!
Related searches to Search Sign Presentation Computer
Frequently asked questions
How do i add an electronic signature to a word document?
How to do electronic signature in docs?
How to dual sign pdf?
Get more for Search Sign Presentation Computer
- How To Electronic signature New Jersey Orthodontists PDF
- Help Me With Electronic signature New Jersey Orthodontists PDF
- How Can I Electronic signature New Jersey Orthodontists PDF
- Help Me With Electronic signature New Jersey Orthodontists PDF
- Can I Electronic signature New Jersey Orthodontists PDF
- How Do I Electronic signature New Jersey Orthodontists PDF
- Help Me With Electronic signature New Jersey Orthodontists PDF
- How Can I Electronic signature New Jersey Orthodontists PDF
Find out other Search Sign Presentation Computer
- Af form 4422
- Ayso card form
- Social security forms
- Arbeitgeberbescheinigung l bank fr geburten ab 01 07 15 form
- Family fund application form online
- Medical claims travel insurance center form
- Motor carrier accident report form
- Nutrena coupon form
- Lettera di invito form
- Wendy mass book order form rtmsdorg
- Lighting maintenance checklist form
- Camp orkila liability waiver form
- Copyright transfer the cleft palate craniofacial journal form
- Magnetic particle inspection report sample form
- Foreign visitor request form at wwwl 3arcom
- Assessment a dividing nation form
- Corrective action form 380601889
- Wageworks claim forms
- American heritage girls penpal explorer form
- Private event contract template form