Protocol Family Encapsulations Form


What is the Protocol Family Encapsulations
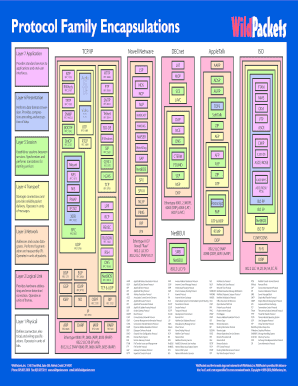
The protocol family encapsulations refer to a set of standardized formats used for transmitting data across various networking protocols. These encapsulations ensure that data packets are correctly formatted and understood by different systems within a network. Understanding these encapsulations is essential for effective communication between devices, especially in complex environments where multiple protocols interact. This knowledge is particularly relevant for businesses that rely on robust digital communication systems.
How to use the Protocol Family Encapsulations
To effectively use protocol family encapsulations, one must first identify the specific protocols involved in the communication process. This includes understanding the data link layer, network layer, and transport layer protocols. Once identified, the encapsulation process involves wrapping the data with the appropriate headers and trailers for each layer. This ensures that the data can be correctly interpreted by the receiving device. Proper implementation of these encapsulations is crucial for maintaining data integrity and ensuring seamless communication.
Legal use of the Protocol Family Encapsulations
Legal use of protocol family encapsulations is governed by various regulations that dictate how data must be handled and transmitted. Compliance with these regulations is vital for businesses to avoid legal repercussions. For instance, organizations must ensure that their data transmission methods adhere to standards set by the Federal Communications Commission (FCC) and other relevant bodies. This includes safeguarding sensitive information and ensuring that data is transmitted securely across networks.
Steps to complete the Protocol Family Encapsulations
Completing protocol family encapsulations involves several key steps:
- Identify the data to be transmitted and the protocols involved.
- Wrap the data in the appropriate headers for the data link layer.
- Add network layer headers to facilitate routing.
- Include transport layer headers to ensure proper delivery.
- Verify the encapsulated data for accuracy and completeness.
Following these steps ensures that the data is properly formatted for transmission and can be successfully interpreted by the receiving system.
Key elements of the Protocol Family Encapsulations
Key elements of protocol family encapsulations include:
- Headers: Information added at the beginning of the data packet that provides routing and addressing information.
- Trailers: Additional information at the end of the packet that may include error-checking data.
- Payload: The actual data being transmitted, which is encapsulated within the headers and trailers.
- Protocols: The specific rules governing how data is encapsulated and transmitted across different layers.
Understanding these elements is essential for anyone involved in network communications, as they play a critical role in ensuring data is transmitted accurately and securely.
Examples of using the Protocol Family Encapsulations
Examples of protocol family encapsulations can be seen in various networking scenarios:
- In a local area network (LAN), Ethernet frames encapsulate data for transmission between devices.
- Internet Protocol (IP) packets encapsulate data for routing across the internet.
- Transmission Control Protocol (TCP) segments encapsulate application data for reliable delivery.
These examples illustrate how encapsulations operate at different layers of the networking model, facilitating effective communication across diverse systems.
Quick guide on how to complete protocol family encapsulations
Effortlessly Prepare Protocol Family Encapsulations on Any Device
Digital document management has gained traction among businesses and individuals alike. It serves as an ideal eco-conscious alternative to traditional printed and signed paperwork, allowing you to access the correct version and securely save it online. airSlate SignNow equips you with all the necessary tools to create, modify, and electronically sign your documents promptly without interruptions. Handle Protocol Family Encapsulations on any device using airSlate SignNow's Android or iOS applications and enhance any document-related task today.
The Easiest Method to Modify and eSign Protocol Family Encapsulations Without Stress
- Obtain Protocol Family Encapsulations and then click Get Form to begin.
- Utilize the tools provided to fill out your form.
- Emphasize pertinent sections of your documents or obscure sensitive information with features specifically offered by airSlate SignNow.
- Create your signature using the Sign tool, which takes moments and carries the same legal validity as a conventional wet ink signature.
- Verify the details and then click on the Done button to save your changes.
- Choose your preferred method of delivering your form, via email, text message (SMS), or an invite link, or download it to your PC.
Eliminate concerns about lost or misplaced documents, tedious form searching, or mistakes that require printing new copies. airSlate SignNow meets your document management needs in just a few clicks from any device you prefer. Edit and eSign Protocol Family Encapsulations and ensure outstanding communication at every stage of the document preparation process with airSlate SignNow.
Create this form in 5 minutes or less
Create this form in 5 minutes!
How to create an eSignature for the protocol family encapsulations
How to create an electronic signature for a PDF online
How to create an electronic signature for a PDF in Google Chrome
How to create an e-signature for signing PDFs in Gmail
How to create an e-signature right from your smartphone
How to create an e-signature for a PDF on iOS
How to create an e-signature for a PDF on Android
People also ask
-
What are protocol family encapsulations and how do they benefit my business?
Protocol family encapsulations refer to the methods used to encapsulate data packets for transmission across networks. They enable your business to ensure data integrity and communication efficiency. By utilizing protocol family encapsulations, you can streamline your document signing processes while maintaining security and compliance.
-
How does airSlate SignNow support different protocol family encapsulations?
airSlate SignNow is designed to support various protocol family encapsulations, ensuring that your eSigning process is secure and effective. This flexibility allows businesses to integrate their existing systems smoothly while leveraging the advantages of our platform. By supporting multiple encapsulation methods, we help enhance your document workflow.
-
Is there a free trial available for airSlate SignNow for testing protocol family encapsulations?
Yes, airSlate SignNow offers a free trial that allows you to explore our features, including protocol family encapsulations. This enables prospective customers to experience how our solution can improve their document management and signing processes. You can evaluate the effectiveness without any financial commitment.
-
What pricing plans does airSlate SignNow offer for access to protocol family encapsulations?
airSlate SignNow provides flexible pricing plans designed to accommodate various business needs and sizes. Each plan includes access to protocol family encapsulations, ensuring that all users can benefit from robust document signing capabilities. You can choose a plan that best fits your organization's requirements.
-
What features does airSlate SignNow offer in relation to protocol family encapsulations?
airSlate SignNow offers a range of features that support protocol family encapsulations, such as customizable templates and automated workflows. These tools help enhance efficiency and security when signing documents. By leveraging these features, businesses can improve the overall user experience while ensuring compliance.
-
Can I integrate airSlate SignNow with other tools using protocol family encapsulations?
Yes, airSlate SignNow integrates seamlessly with various applications and services using protocol family encapsulations. This capability allows businesses to connect their existing software ecosystem for better overall functionality. Integrating these tools helps streamline workflows and improves document management efficiency.
-
How does using protocol family encapsulations enhance document security?
Using protocol family encapsulations enhances document security by providing layers of encryption and data integrity checks. This ensures that your sensitive information remains protected throughout the signing process. airSlate SignNow prioritizes security, making it a reliable choice for businesses concerned about data safety.
Get more for Protocol Family Encapsulations
Find out other Protocol Family Encapsulations
- Electronic signature Construction Form California Fast
- Help Me With Electronic signature Colorado Construction Rental Application
- Electronic signature Connecticut Construction Business Plan Template Fast
- Electronic signature Delaware Construction Business Letter Template Safe
- Electronic signature Oklahoma Business Operations Stock Certificate Mobile
- Electronic signature Pennsylvania Business Operations Promissory Note Template Later
- Help Me With Electronic signature North Dakota Charity Resignation Letter
- Electronic signature Indiana Construction Business Plan Template Simple
- Electronic signature Wisconsin Charity Lease Agreement Mobile
- Can I Electronic signature Wisconsin Charity Lease Agreement
- Electronic signature Utah Business Operations LLC Operating Agreement Later
- How To Electronic signature Michigan Construction Cease And Desist Letter
- Electronic signature Wisconsin Business Operations LLC Operating Agreement Myself
- Electronic signature Colorado Doctors Emergency Contact Form Secure
- How Do I Electronic signature Georgia Doctors Purchase Order Template
- Electronic signature Doctors PDF Louisiana Now
- How To Electronic signature Massachusetts Doctors Quitclaim Deed
- Electronic signature Minnesota Doctors Last Will And Testament Later
- How To Electronic signature Michigan Doctors LLC Operating Agreement
- How Do I Electronic signature Oregon Construction Business Plan Template