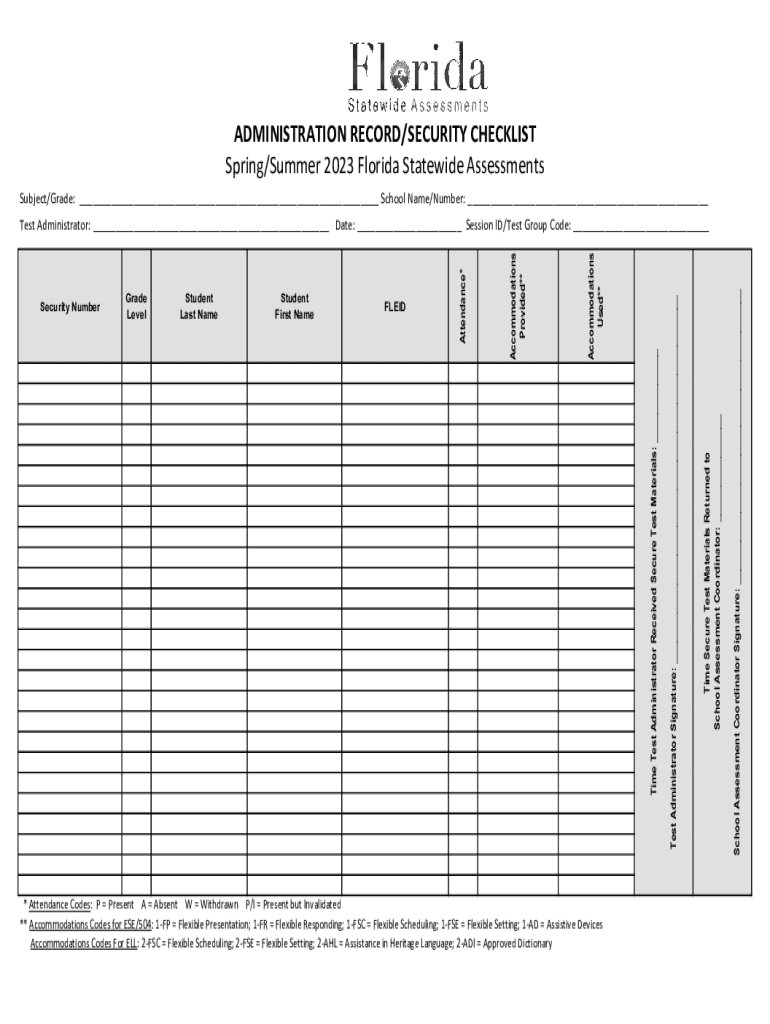
ADMINISTRATION RECORDSECURITY CHECKLIST Form


What is the Administration Record Security Checklist
The Administration Record Security Checklist is a critical document designed to ensure that organizations maintain proper security protocols for their administrative records. This checklist serves as a framework for assessing the security measures in place to protect sensitive information from unauthorized access, loss, or damage. It encompasses various aspects of record management, including data storage, access controls, and compliance with relevant regulations.
How to Use the Administration Record Security Checklist
Utilizing the Administration Record Security Checklist involves a systematic approach to evaluate current security practices. Organizations should begin by reviewing each item on the checklist to identify existing security measures and any gaps that may need addressing. This process typically includes:
- Assessing physical security measures for record storage locations.
- Reviewing digital access controls and user permissions.
- Ensuring compliance with federal and state regulations regarding record management.
- Documenting findings and developing action plans for any identified weaknesses.
Key Elements of the Administration Record Security Checklist
The checklist includes several key elements essential for robust record security. These elements often cover:
- Identification of sensitive records and their classification.
- Access control measures, including user authentication and authorization processes.
- Data encryption practices for both stored and transmitted information.
- Regular audits and monitoring of access logs to detect unauthorized activity.
- Incident response protocols for addressing data breaches or security incidents.
Steps to Complete the Administration Record Security Checklist
Completing the Administration Record Security Checklist involves several structured steps:
- Gather all relevant documentation regarding current security practices.
- Review each item on the checklist, marking those that are compliant and identifying areas needing improvement.
- Engage stakeholders to discuss findings and gather input on potential security enhancements.
- Develop a timeline for implementing necessary changes and assign responsibilities.
- Schedule regular reviews of the checklist to ensure ongoing compliance and adaptation to new security threats.
Legal Use of the Administration Record Security Checklist
The Administration Record Security Checklist is not only a best practice but also a legal necessity for many organizations. Compliance with federal laws, such as the Health Insurance Portability and Accountability Act (HIPAA) and the Family Educational Rights and Privacy Act (FERPA), mandates that organizations protect sensitive information. Utilizing the checklist helps demonstrate due diligence in safeguarding records and can be crucial in legal proceedings or audits.
Examples of Using the Administration Record Security Checklist
Organizations across various sectors can implement the Administration Record Security Checklist to enhance their record security. For instance:
- A healthcare provider may use the checklist to ensure patient records are securely stored and accessed only by authorized personnel.
- An educational institution might apply the checklist to protect student records and comply with FERPA regulations.
- A financial institution could leverage the checklist to safeguard client information against cyber threats.
Quick guide on how to complete administration recordsecurity checklist
Effortlessly Prepare ADMINISTRATION RECORDSECURITY CHECKLIST on Any Device
Digital document management has become increasingly popular among businesses and individuals. It offers an ideal eco-friendly alternative to traditional printed and signed documents, allowing you to obtain the necessary form and securely store it online. airSlate SignNow equips you with all the resources needed to create, alter, and electronically sign your documents quickly without any hold-ups. Manage ADMINISTRATION RECORDSECURITY CHECKLIST on any platform using airSlate SignNow's Android or iOS applications and enhance any document-focused procedure today.
The simplest way to modify and electronically sign ADMINISTRATION RECORDSECURITY CHECKLIST with ease
- Locate ADMINISTRATION RECORDSECURITY CHECKLIST and click Obtain Form to begin.
- Utilize the tools we provide to fill out your form.
- Emphasize important portions of your documents or redact sensitive information with tools that airSlate SignNow specifically offers for this purpose.
- Generate your signature using the Sign tool, which takes just seconds and holds the same legal validity as a conventional handwritten signature.
- Review all the details and click the Complete button to save your modifications.
- Select your preferred method to deliver your form, whether by email, SMS, invitation link, or download it to your PC.
Say goodbye to lost or misplaced documents, tedious form searches, or mistakes that require printing new document copies. airSlate SignNow addresses your document management needs in just a few clicks from any device of your choice. Edit and electronically sign ADMINISTRATION RECORDSECURITY CHECKLIST to ensure outstanding communication at every stage of your form preparation journey with airSlate SignNow.
Create this form in 5 minutes or less
Create this form in 5 minutes!
How to create an eSignature for the administration recordsecurity checklist
How to create an electronic signature for a PDF online
How to create an electronic signature for a PDF in Google Chrome
How to create an e-signature for signing PDFs in Gmail
How to create an e-signature right from your smartphone
How to create an e-signature for a PDF on iOS
How to create an e-signature for a PDF on Android
Get more for ADMINISTRATION RECORDSECURITY CHECKLIST
Find out other ADMINISTRATION RECORDSECURITY CHECKLIST
- eSignature Illinois House rental agreement Free
- How To eSignature Indiana House rental agreement
- Can I eSignature Minnesota House rental lease agreement
- eSignature Missouri Landlord lease agreement Fast
- eSignature Utah Landlord lease agreement Simple
- eSignature West Virginia Landlord lease agreement Easy
- How Do I eSignature Idaho Landlord tenant lease agreement
- eSignature Washington Landlord tenant lease agreement Free
- eSignature Wisconsin Landlord tenant lease agreement Online
- eSignature Wyoming Landlord tenant lease agreement Online
- How Can I eSignature Oregon lease agreement
- eSignature Washington Lease agreement form Easy
- eSignature Alaska Lease agreement template Online
- eSignature Alaska Lease agreement template Later
- eSignature Massachusetts Lease agreement template Myself
- Can I eSignature Arizona Loan agreement
- eSignature Florida Loan agreement Online
- eSignature Florida Month to month lease agreement Later
- Can I eSignature Nevada Non-disclosure agreement PDF
- eSignature New Mexico Non-disclosure agreement PDF Online