Hacking Agreement Form


What is the hacking agreement?
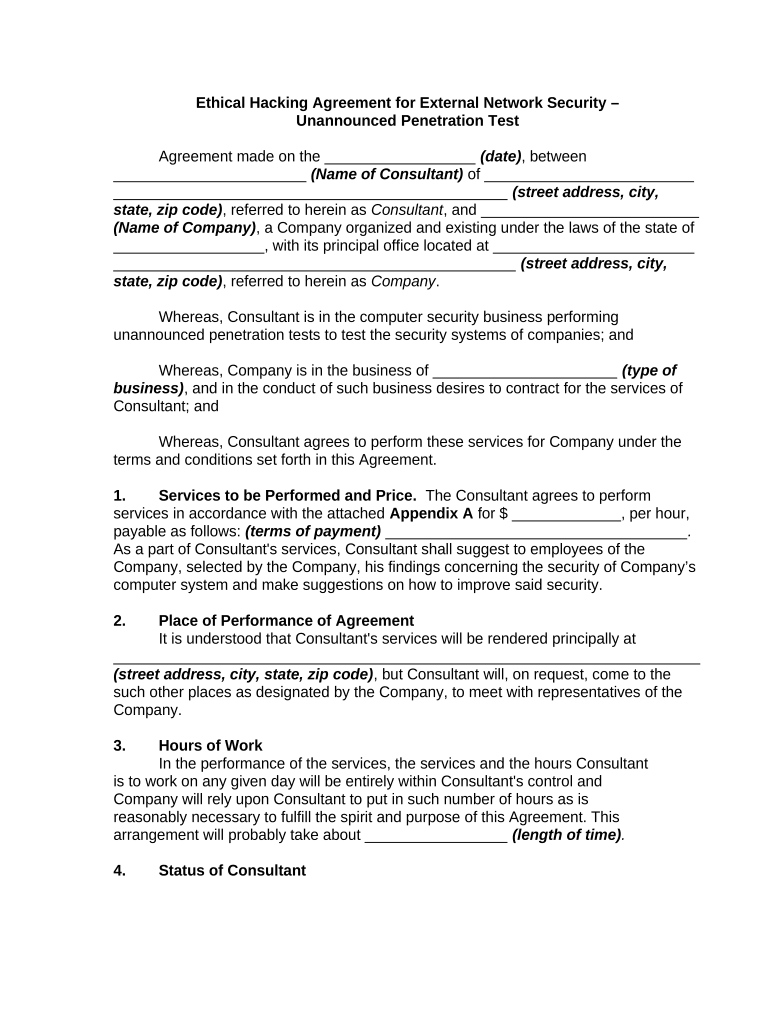
A hacking agreement is a legal document that outlines the terms and conditions under which one party may engage in hacking activities, typically for legitimate purposes such as security testing or ethical hacking. This agreement serves to protect both the hacker and the organization by clearly defining the scope of work, responsibilities, and limitations. It ensures that all parties understand their rights and obligations, thereby minimizing the risk of legal repercussions.
How to use the hacking agreement
To use a hacking agreement effectively, both parties should review the document thoroughly before signing. It is essential to discuss the specific objectives of the hacking activities, including the systems to be tested and the methods to be employed. Both parties should agree on the duration of the agreement and the confidentiality of any sensitive information encountered during the process. Once both parties are satisfied with the terms, they can proceed to sign the document electronically, ensuring compliance with relevant eSignature laws.
Key elements of the hacking agreement
A comprehensive hacking agreement typically includes several key elements:
- Scope of Work: Clearly defines the specific hacking activities permitted.
- Confidentiality Clause: Protects sensitive information and trade secrets.
- Liability Limitations: Outlines the extent of liability for both parties in case of damages.
- Duration: Specifies the time frame for which the agreement is valid.
- Termination Conditions: Details how either party can terminate the agreement.
Steps to complete the hacking agreement
Completing a hacking agreement involves several important steps:
- Draft the Agreement: Create a document that includes all necessary terms and conditions.
- Review: Both parties should carefully read through the agreement to ensure clarity and mutual understanding.
- Negotiate Terms: Discuss any changes or additional clauses that may be necessary.
- Sign the Agreement: Use a secure eSignature platform to sign the document electronically.
- Store the Document: Keep a copy of the signed agreement for future reference.
Legal use of the hacking agreement
The legal use of a hacking agreement hinges on its compliance with relevant laws and regulations. It is crucial that both parties understand the legal implications of the activities outlined in the agreement. This includes adhering to federal and state laws regarding computer security and privacy. By establishing a legally binding contract, both parties can engage in hacking activities with a clear understanding of their rights and responsibilities, thereby reducing the risk of potential legal issues.
Examples of using the hacking agreement
Hacking agreements are commonly used in various scenarios, including:
- Penetration Testing: Organizations hire ethical hackers to identify vulnerabilities in their systems.
- Security Audits: Firms may engage hackers to assess their cybersecurity measures.
- Software Development: Developers may require hacking agreements when testing new applications for security flaws.
Quick guide on how to complete hacking agreement
Prepare Hacking Agreement effortlessly on any device
Digital document management has become increasingly popular among companies and individuals. It offers an ideal eco-friendly substitute for conventional printed and signed paperwork, as you can easily locate the necessary form and securely store it online. airSlate SignNow equips you with all the tools you need to create, edit, and eSign your documents quickly without delays. Manage Hacking Agreement on any device using airSlate SignNow's Android or iOS applications and simplify any document-related task today.
The easiest way to modify and eSign Hacking Agreement with minimal effort
- Obtain Hacking Agreement and click Get Form to begin.
- Use the tools we provide to fill out your form.
- Highlight important sections of the documents or redact sensitive information with tools that airSlate SignNow offers specifically for this purpose.
- Create your eSignature using the Sign tool, which takes seconds and carries the same legal validity as a traditional handwritten signature.
- Review all the details and click the Done button to save your changes.
- Decide how you want to send your form—via email, text (SMS), or invitation link—or download it to your computer.
Eliminate concerns about lost or misfiled documents, tedious form searches, or errors that necessitate printing new copies. airSlate SignNow addresses your document management needs in just a few clicks from any device you prefer. Edit and eSign Hacking Agreement and ensure seamless communication throughout the document preparation process with airSlate SignNow.
Create this form in 5 minutes or less
Create this form in 5 minutes!
People also ask
-
What is a hacking agreement?
A hacking agreement is a legal document that outlines the terms and conditions under which hacking activities are performed. This agreement ensures that all parties involved understand their rights and responsibilities, emphasizing legal compliance and ethical practices. airSlate SignNow makes it easy to create, customize, and sign hacking agreements online.
-
Why do I need a hacking agreement?
A hacking agreement is essential for protecting both parties involved in a hacking project. It clarifies the scope of work, data security measures, and the consequences of misuse. By using airSlate SignNow, you can ensure that your hacking agreements are both legally binding and easily accessible to all stakeholders.
-
How much does it cost to create a hacking agreement with airSlate SignNow?
Creating a hacking agreement with airSlate SignNow is cost-effective, with flexible pricing plans based on your business needs. Plans often include unlimited document signing and customizable templates for various agreements. Check our pricing page for detailed information on costs and features.
-
Can I integrate my hacking agreement with other tools?
Yes, airSlate SignNow supports integrations with various business tools like CRM systems and project management software. This integration allows you to streamline the workflow associated with your hacking agreements. By connecting airSlate SignNow with your existing applications, you can enhance document management efficiency.
-
What features does airSlate SignNow offer for managing hacking agreements?
airSlate SignNow offers a range of features for managing hacking agreements, including customizable templates, document storage, and secure eSignature capabilities. These features empower businesses to handle agreements efficiently while ensuring legal compliance and data protection. Experience user-friendly navigation and robust functionalities with airSlate SignNow.
-
How can airSlate SignNow enhance the signing process of my hacking agreement?
airSlate SignNow streamlines the signing process of your hacking agreement by allowing electronic signatures that can be completed anytime, anywhere. This convenience reduces turnaround time and enhances collaboration between parties. With real-time notifications and tracking, you’ll never miss an important update on your agreement.
-
Is my hacking agreement safe with airSlate SignNow?
Absolutely! airSlate SignNow prioritizes the security of your hacking agreements with advanced encryption and compliance with legal standards. We ensure that your documents are protected from unauthorized access and data bsignNowes, giving you peace of mind while managing sensitive information.
Get more for Hacking Agreement
- Individuals west virginia state tax department wvgov form
- Form 3372 michigan sales and use tax certificate of
- Form n 35 rev 2020 s corporation income tax return forms 2020 fillable
- Place quotxquot in box form
- N 11 rev 2020 individual income tax return resident forms 2020
- If amending form
- Annual recertification letter streamlined sales tax form
- 5076 small business property tax state of michigan form
Find out other Hacking Agreement
- Can I Sign Utah Executive Summary Template
- Sign Washington Executive Summary Template Free
- Sign Connecticut New Hire Onboarding Mobile
- Help Me With Sign Wyoming CV Form Template
- Sign Mississippi New Hire Onboarding Simple
- Sign Indiana Software Development Proposal Template Easy
- Sign South Dakota Working Time Control Form Now
- Sign Hawaii IT Project Proposal Template Online
- Sign Nebraska Operating Agreement Now
- Can I Sign Montana IT Project Proposal Template
- Sign Delaware Software Development Agreement Template Now
- How To Sign Delaware Software Development Agreement Template
- How Can I Sign Illinois Software Development Agreement Template
- Sign Arkansas IT Consulting Agreement Computer
- Can I Sign Arkansas IT Consulting Agreement
- Sign Iowa Agile Software Development Contract Template Free
- How To Sign Oregon IT Consulting Agreement
- Sign Arizona Web Hosting Agreement Easy
- How Can I Sign Arizona Web Hosting Agreement
- Help Me With Sign Alaska Web Hosting Agreement