FCPS Threat Assessment Documentation Date Readiness and Rems Ed Form


Understanding the FCPS Threat Assessment Documentation Date Readiness and Rems Ed
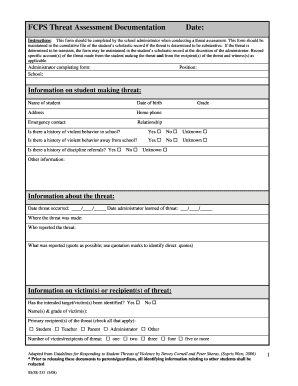
The FCPS Threat Assessment Documentation Date Readiness and Rems Ed is a critical form used within the educational system to assess and document potential threats to safety. This form is designed to ensure that schools can effectively evaluate risks and implement appropriate responses. The documentation serves as a formal record that outlines the assessment process, findings, and any actions taken to mitigate threats. It is essential for maintaining a safe learning environment and complying with federal and state regulations regarding student safety.
Steps to Complete the FCPS Threat Assessment Documentation Date Readiness and Rems Ed
Completing the FCPS Threat Assessment Documentation involves several key steps:
- Gather relevant information regarding the incident or concern.
- Conduct a thorough assessment using established criteria.
- Document findings clearly, ensuring all sections of the form are filled out accurately.
- Review the documentation with appropriate stakeholders, such as school administrators or safety officers.
- Submit the completed form to the designated authority for further action.
Each step is vital for ensuring that the assessment is comprehensive and actionable.
Key Elements of the FCPS Threat Assessment Documentation Date Readiness and Rems Ed
Several key elements must be included in the FCPS Threat Assessment Documentation to ensure its effectiveness:
- Identification of the individual involved: Document the name and relevant details of the person being assessed.
- Nature of the threat: Clearly outline the specific concerns or behaviors that prompted the assessment.
- Assessment findings: Summarize the results of the evaluation, including any risk factors identified.
- Recommended actions: Provide suggestions for intervention or support based on the assessment outcomes.
- Follow-up procedures: Outline any necessary follow-up actions to monitor the situation.
Legal Use of the FCPS Threat Assessment Documentation Date Readiness and Rems Ed
The FCPS Threat Assessment Documentation is governed by various legal requirements aimed at protecting student safety and privacy. Schools must comply with federal laws such as the Family Educational Rights and Privacy Act (FERPA) when handling sensitive information. Proper documentation helps ensure that schools can demonstrate due diligence in assessing threats, which is crucial in legal contexts. It also aids in maintaining transparency and accountability within the educational institution.
Obtaining the FCPS Threat Assessment Documentation Date Readiness and Rems Ed
To obtain the FCPS Threat Assessment Documentation, individuals typically need to request it through their school district's administrative office. The form may also be available on the district's official website or through school safety coordinators. It is important to ensure that the most current version of the form is used, as updates may occur based on changes in policy or best practices.
Examples of Using the FCPS Threat Assessment Documentation Date Readiness and Rems Ed
Examples of when the FCPS Threat Assessment Documentation may be used include:
- A student exhibiting concerning behavior that raises safety alarms.
- Reports of threats made against individuals or the school community.
- Incidents involving bullying or harassment that may escalate into more serious situations.
In each case, the documentation serves as a vital tool for assessing risks and determining appropriate responses.
Quick guide on how to complete fcps threat assessment documentation date readiness and rems ed
Finalize FCPS Threat Assessment Documentation Date Readiness And Rems Ed effortlessly on any device
Managing documents online has gained popularity among businesses and individuals. It offers an excellent eco-friendly substitute for traditional printed and signed paperwork, as you can locate the right form and securely save it online. airSlate SignNow provides you with all the necessary tools to create, edit, and eSign your documents swiftly without delays. Handle FCPS Threat Assessment Documentation Date Readiness And Rems Ed on any platform with airSlate SignNow Android or iOS applications and enhance any document-focused operation today.
The easiest way to modify and eSign FCPS Threat Assessment Documentation Date Readiness And Rems Ed with ease
- Locate FCPS Threat Assessment Documentation Date Readiness And Rems Ed and click Get Form to begin.
- Utilize the tools we offer to fill out your form.
- Highlight pertinent sections of your documents or obscure sensitive information with tools that airSlate SignNow provides specifically for that purpose.
- Create your signature using the Sign tool, which takes moments and carries the same legal validity as a conventional wet ink signature.
- Review all the details and then click on the Done button to save your modifications.
- Select how you wish to share your form, via email, text message (SMS), or invite link, or download it to your computer.
Eliminate worries about lost or misplaced files, tedious form searching, or mistakes that necessitate printing new copies of documents. airSlate SignNow meets your document management needs in just a few clicks from any device of your preference. Edit and eSign FCPS Threat Assessment Documentation Date Readiness And Rems Ed and guarantee exceptional communication at any stage of your form preparation process with airSlate SignNow.
Create this form in 5 minutes or less
Create this form in 5 minutes!
How to create an eSignature for the fcps threat assessment documentation date readiness and rems ed
How to create an electronic signature for a PDF online
How to create an electronic signature for a PDF in Google Chrome
How to create an e-signature for signing PDFs in Gmail
How to create an e-signature right from your smartphone
How to create an e-signature for a PDF on iOS
How to create an e-signature for a PDF on Android
People also ask
-
What is the FCPS Threat Assessment Documentation Date Readiness And Rems Ed. feature in airSlate SignNow?
The FCPS Threat Assessment Documentation Date Readiness And Rems Ed. feature in airSlate SignNow allows organizations to efficiently manage and document threat assessments. This ensures compliance with educational standards and enhances safety measures. By streamlining this process, organizations can focus on proactive measures rather than administrative tasks.
-
How does airSlate SignNow support the FCPS Threat Assessment Documentation Date Readiness And Rems Ed.?
airSlate SignNow supports the FCPS Threat Assessment Documentation Date Readiness And Rems Ed. by providing a secure platform for documenting assessments and signatures. This enhances the accountability and traceability of each action taken. Furthermore, our collaborative tools allow for instant sharing and updates among team members.
-
Is airSlate SignNow cost-effective for managing FCPS Threat Assessment Documentation Date Readiness And Rems Ed.?
Yes, airSlate SignNow offers a cost-effective solution for managing FCPS Threat Assessment Documentation Date Readiness And Rems Ed. by reducing paper usage and streamlining processes. Our pricing plans are designed for businesses of all sizes, ensuring that you can choose an option that fits your budget while still addressing your documentation needs.
-
What are the key benefits of using airSlate SignNow for FCPS Threat Assessment Documentation?
The key benefits of using airSlate SignNow for FCPS Threat Assessment Documentation include enhanced security, ease of use, and compliance assurance. Our platform helps organizations to quickly gather signatures and manage documents without the hassle of traditional methods. This translates to faster decision-making and improved operational efficiency.
-
Can I integrate airSlate SignNow with other tools for FCPS Threat Assessment Documentation Date Readiness And Rems Ed.?
Absolutely! airSlate SignNow offers integration capabilities with a variety of popular tools and applications. This ensures seamless workflow management for FCPS Threat Assessment Documentation Date Readiness And Rems Ed., allowing you to connect your existing systems and maintain data consistency.
-
How user-friendly is airSlate SignNow for FCPS Threat Assessment Documentation Date Readiness And Rems Ed.?
airSlate SignNow is designed with user-friendliness in mind, providing an intuitive interface that simplifies the process of managing FCPS Threat Assessment Documentation Date Readiness And Rems Ed. Users can easily navigate the features without extensive training, making the transition to our platform smooth and efficient.
-
What security measures does airSlate SignNow implement for FCPS Threat Assessment Documentation?
Security is a top priority at airSlate SignNow. For FCPS Threat Assessment Documentation, we implement advanced encryption, secure data storage, and compliance with industry standards. You can trust that your sensitive information is safeguarded, providing peace of mind as you manage your documentation.
Get more for FCPS Threat Assessment Documentation Date Readiness And Rems Ed
Find out other FCPS Threat Assessment Documentation Date Readiness And Rems Ed
- eSignature Delaware Business Operations Forbearance Agreement Fast
- How To eSignature Ohio Banking Business Plan Template
- eSignature Georgia Business Operations Limited Power Of Attorney Online
- Help Me With eSignature South Carolina Banking Job Offer
- eSignature Tennessee Banking Affidavit Of Heirship Online
- eSignature Florida Car Dealer Business Plan Template Myself
- Can I eSignature Vermont Banking Rental Application
- eSignature West Virginia Banking Limited Power Of Attorney Fast
- eSignature West Virginia Banking Limited Power Of Attorney Easy
- Can I eSignature Wisconsin Banking Limited Power Of Attorney
- eSignature Kansas Business Operations Promissory Note Template Now
- eSignature Kansas Car Dealer Contract Now
- eSignature Iowa Car Dealer Limited Power Of Attorney Easy
- How Do I eSignature Iowa Car Dealer Limited Power Of Attorney
- eSignature Maine Business Operations Living Will Online
- eSignature Louisiana Car Dealer Profit And Loss Statement Easy
- How To eSignature Maryland Business Operations Business Letter Template
- How Do I eSignature Arizona Charity Rental Application
- How To eSignature Minnesota Car Dealer Bill Of Lading
- eSignature Delaware Charity Quitclaim Deed Computer