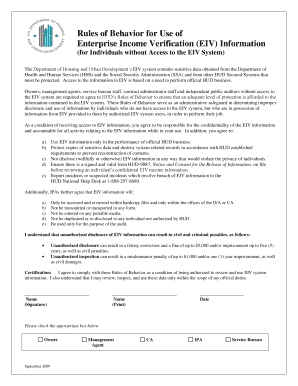
Rules of Behavior for Use of Enterprise Income Verification Eiv Information


Understanding the Rules of Behavior for Use of Enterprise Income Verification (EIV) Information
The Rules of Behavior for Use of Enterprise Income Verification (EIV) Information establish guidelines for authorized users regarding the handling and protection of sensitive data. These rules ensure that EIV information is used appropriately and securely, minimizing the risk of unauthorized access or misuse. They outline the responsibilities of users, including the necessity of confidentiality and the importance of safeguarding the integrity of the information. Understanding these rules is crucial for compliance and for maintaining the trust of individuals whose data is being verified.
How to Utilize the Rules of Behavior for Use of Enterprise Income Verification Information
To effectively use the Rules of Behavior for Use of Enterprise Income Verification Information, individuals must first familiarize themselves with the guidelines. This includes understanding the specific protocols for accessing, sharing, and storing EIV data. Users should ensure they only access information necessary for their job functions and refrain from discussing or disclosing EIV data outside of authorized contexts. Regular training and updates on these rules can help reinforce compliance and promote responsible data handling practices.
Key Elements of the Rules of Behavior for Use of Enterprise Income Verification Information
Several key elements define the Rules of Behavior for Use of Enterprise Income Verification Information. These include:
- Confidentiality: Users must keep EIV data confidential and share it only with authorized personnel.
- Integrity: Users are responsible for ensuring the accuracy and completeness of the information they handle.
- Accountability: Users must be aware of their responsibilities and the potential consequences of violating the rules.
- Compliance: Adherence to federal, state, and local laws regarding data protection is mandatory.
Legal Use of the Rules of Behavior for Use of Enterprise Income Verification Information
The legal use of the Rules of Behavior for Use of Enterprise Income Verification Information is governed by various federal regulations, including the Privacy Act and the Fair Information Practices. These laws dictate how personal data should be collected, used, and protected. Users must ensure their actions comply with these legal frameworks to avoid penalties and maintain the integrity of the EIV system. Understanding the legal implications is essential for all authorized users to ensure they operate within the law.
Steps to Complete the Rules of Behavior for Use of Enterprise Income Verification Information
Completing the Rules of Behavior for Use of Enterprise Income Verification Information involves several steps:
- Review the Document: Carefully read the rules to understand the expectations and requirements.
- Sign Acknowledgment: Confirm your understanding and agreement by signing the acknowledgment form.
- Participate in Training: Attend any required training sessions to reinforce your understanding of the rules.
- Regularly Update Knowledge: Stay informed about any changes to the rules or related laws.
Examples of Using the Rules of Behavior for Use of Enterprise Income Verification Information
Examples of applying the Rules of Behavior for Use of Enterprise Income Verification Information include scenarios such as:
- A housing authority employee accessing EIV data to verify an applicant's income while ensuring that the information is not shared with unauthorized individuals.
- A caseworker discussing EIV findings in a private meeting with authorized staff only, avoiding any public discussions that could lead to data breaches.
- Implementing security measures, such as password protection and encryption, when storing EIV information to prevent unauthorized access.
Create this form in 5 minutes or less
Create this form in 5 minutes!
How to create an eSignature for the rules of behavior for use of enterprise income verification eiv information
How to create an electronic signature for a PDF online
How to create an electronic signature for a PDF in Google Chrome
How to create an e-signature for signing PDFs in Gmail
How to create an e-signature right from your smartphone
How to create an e-signature for a PDF on iOS
How to create an e-signature for a PDF on Android
People also ask
-
What are the Rules Of Behavior For Use Of Enterprise Income Verification eiv Information?
The Rules Of Behavior For Use Of Enterprise Income Verification eiv Information outline the guidelines and protocols that users must follow to ensure the secure and ethical use of sensitive income data. These rules are designed to protect both the integrity of the information and the privacy of individuals. Adhering to these rules is crucial for compliance and maintaining trust.
-
How does airSlate SignNow ensure compliance with the Rules Of Behavior For Use Of Enterprise Income Verification eiv Information?
airSlate SignNow incorporates robust security measures and user training to ensure compliance with the Rules Of Behavior For Use Of Enterprise Income Verification eiv Information. Our platform includes features like access controls, audit trails, and encryption to safeguard sensitive data. This commitment to compliance helps businesses operate within legal frameworks while using our services.
-
What features does airSlate SignNow offer to support the Rules Of Behavior For Use Of Enterprise Income Verification eiv Information?
airSlate SignNow offers features such as customizable workflows, secure document storage, and electronic signatures that align with the Rules Of Behavior For Use Of Enterprise Income Verification eiv Information. These features facilitate efficient document management while ensuring that sensitive information is handled appropriately. Users can easily track compliance and maintain accountability.
-
Is airSlate SignNow cost-effective for businesses needing to comply with the Rules Of Behavior For Use Of Enterprise Income Verification eiv Information?
Yes, airSlate SignNow is a cost-effective solution for businesses that need to comply with the Rules Of Behavior For Use Of Enterprise Income Verification eiv Information. Our pricing plans are designed to accommodate various business sizes and needs, ensuring that compliance does not come at an exorbitant cost. This affordability allows businesses to focus on their operations while maintaining compliance.
-
Can airSlate SignNow integrate with other systems to support the Rules Of Behavior For Use Of Enterprise Income Verification eiv Information?
Absolutely! airSlate SignNow offers seamless integrations with various third-party applications that can help support the Rules Of Behavior For Use Of Enterprise Income Verification eiv Information. These integrations enhance workflow efficiency and ensure that all systems work together to maintain compliance and security. Users can easily connect their existing tools with our platform.
-
What benefits does airSlate SignNow provide in relation to the Rules Of Behavior For Use Of Enterprise Income Verification eiv Information?
airSlate SignNow provides numerous benefits, including enhanced security, streamlined processes, and improved compliance with the Rules Of Behavior For Use Of Enterprise Income Verification eiv Information. By using our platform, businesses can reduce the risk of data bsignNowes and ensure that sensitive information is handled according to established guidelines. This leads to greater operational efficiency and peace of mind.
-
How can businesses train their employees on the Rules Of Behavior For Use Of Enterprise Income Verification eiv Information?
Businesses can utilize airSlate SignNow's training resources and documentation to educate employees on the Rules Of Behavior For Use Of Enterprise Income Verification eiv Information. We provide comprehensive guides and best practices to ensure that all users understand their responsibilities when handling sensitive data. Regular training sessions can also reinforce compliance and promote a culture of security.
Get more for Rules Of Behavior For Use Of Enterprise Income Verification eiv Information
Find out other Rules Of Behavior For Use Of Enterprise Income Verification eiv Information
- Electronic signature South Carolina Partnership agreements Online
- How Can I Electronic signature Florida Rental house lease agreement
- How Can I Electronic signature Texas Rental house lease agreement
- eSignature Alabama Trademark License Agreement Secure
- Electronic signature Maryland Rental agreement lease Myself
- How To Electronic signature Kentucky Rental lease agreement
- Can I Electronic signature New Hampshire Rental lease agreement forms
- Can I Electronic signature New Mexico Rental lease agreement forms
- How Can I Electronic signature Minnesota Rental lease agreement
- Electronic signature Arkansas Rental lease agreement template Computer
- Can I Electronic signature Mississippi Rental lease agreement
- Can I Electronic signature Missouri Rental lease contract
- Electronic signature New Jersey Rental lease agreement template Free
- Electronic signature New Jersey Rental lease agreement template Secure
- Electronic signature Vermont Rental lease agreement Mobile
- Electronic signature Maine Residential lease agreement Online
- Electronic signature Minnesota Residential lease agreement Easy
- Electronic signature Wyoming Rental lease agreement template Simple
- Electronic signature Rhode Island Residential lease agreement Online
- Electronic signature Florida Rental property lease agreement Free