In software development, ensuring secure, clearly implementable, and reliable communication between applications is paramount. An API, or Application Programming Interface, is an implementation or specification that enables a software system or module to be called in a standard way by other systems or modules. An API signature is a specific security and verification component of an API call.
- Enhanced security: An API signature protects your HTTP request message from interception, ensuring that only authorized users can access your system.
- Guaranteed data integrity: By using a hash function, signatures confirm that the request body has not been altered during transit.
- Fraud prevention: Unique timestamps and signature values help prevent replay attacks, keeping malicious actors from duplicating API requests.
- Streamlined compliance: Secure API calls support legally-binding digital signatures and electronic signatures, meeting strict regulations in the US and beyond.
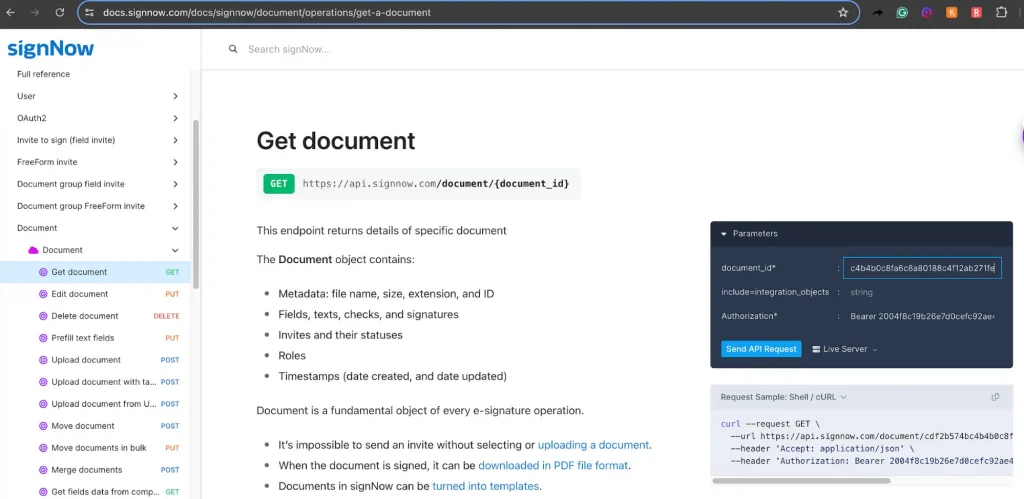
- Seamless integration: Platforms like SignNow provide robust documentation to help developers authenticate requests quickly and save time.
If you find yourself asking, “What is an API signature and why does my business need it?”, this guide breaks down the core benefits, security advantages, and practical applications of using signed requests.
APIs in context: Driving business efficiency
Typically, an API has code that can be called in a special, documented way by an external service. An API call is often a single request to obtain or alter information, allowing the person invoking the API to incorporate the software’s functionality without understanding the inner workings of its code. APIs might internally face other parts of the same software system, or they might connect software created by different organizations.
A clearly documented and convenient-to-use API can make invocation of a service much more convenient. An internal API can be important for the development of a large codebase. An API available to external organizations can be an important product feature. The SignNow API supports automated sharing of legally binding agreements and other documents, for recipients to fill out and send.
Users of the SignNow REST APIs can add pre-built features to fully automate eSignature workflows, improving the efficiency of standard office processes. The SignNow REST API offers a robust platform for an outstanding eSignature experience for all users—signers, preparers, and senders alike. It allows for real-time tracking of signature status, pre-filling of documents, requesting payments, and the creation of embedded, branded workflows for multiple signers. With the SignNow API, you can guarantee a simple, secure, and intuitive signing process on any device.
What API signature means for your security
Since it is open to being invoked by other software, including by potential attackers, an API must take precautions to remain secure. To ensure API use is authorized, potentially vulnerable API endpoints require authentication credentials. These credentials need to be properly encrypted if transmitted over the network.
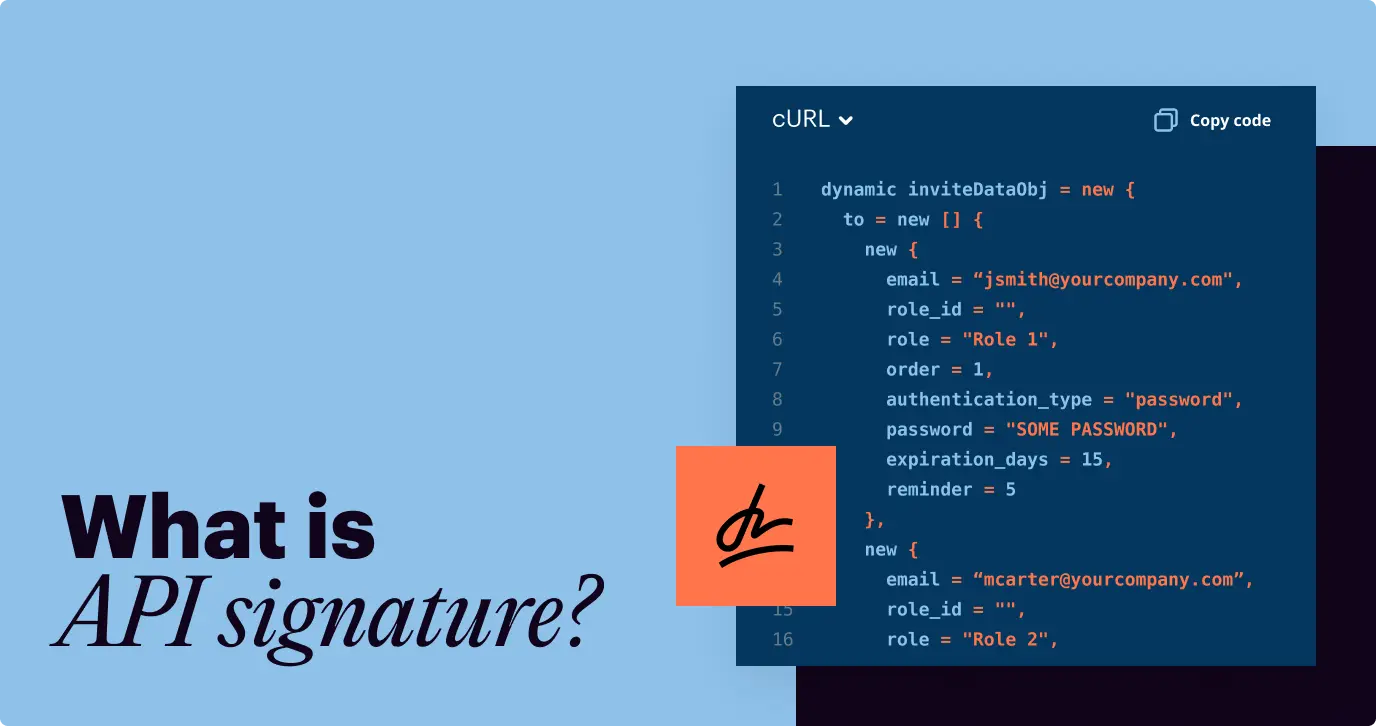
The API signature is the component of the API call with the encrypted user credentials, which can be used to verify user authenticity and message integrity. It includes the user credentials encoded as a single encrypted string, possibly with other data, to be passed along with the rest of the API call.
It is standard and secure to pass these authentication credentials encoded using the 64-character Base64 encoding scheme. Base64 stores data as strings with an “alphabet” of 64 unique characters, with 6 bits for each character.
Two separate keys are used for encryption and decryption — the public and private keys. These are associated with one another and with a given user of the service. The private key — also known as the secret key — is used to encrypt the API signature and is stored securely by the holder.
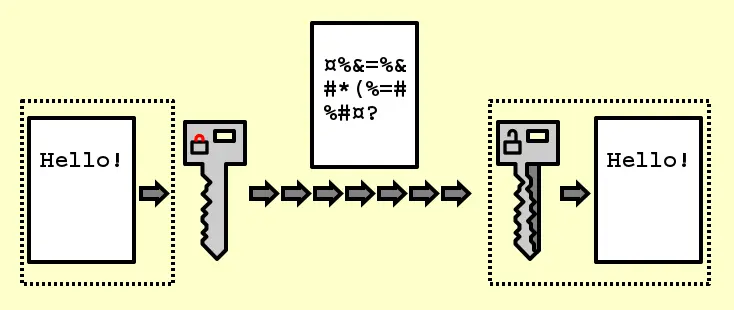
The public key of the key pair is publicly available. The API provider uses the public key associated with the user’s private key for decryption and verifies that the data is valid.
Protecting sensitive data
When an application sends a post request, the server receives the data and must verify its origin. An API signature guarantees that the sender is authentic. If a hacker tries to intercept the request and modify the JSON format or the request body, the server side will reject it. The signature generated at the source will no longer match the hash calculated by the server, preserving data integrity.
Preventing replay attacks
Security protocols must also account for duplicated messages. To prevent replay attacks, developers often include a timestamp or a unique string in the HTTP header. If a malicious user intercepts the message and tries to resend the exact same HTTP request later, the server will recognize the expired timestamp and deny access.
The role of keys in the signing process
Two separate keys manage encryption and decryption during the signing process: the public key and the private key. These keys associate with one another and with a specific user account.
The sender’s private key—also known as the secret key—encrypts the API signature. The account holder stores this secret securely. Meanwhile, the public key remains publicly available. The API provider uses the public key associated with the user’s private key for decryption. This verifies that the data is valid and confirms the identity of the sender.
By running the data through the same hash function on both ends, the system ensures that the information remains exactly as intended. This process builds the foundation for secure digital signatures and reliable electronic signatures.
API signature example in practice
In real-world applications, an API signature acts as the blueprint that tells developers exactly how to interact with a service. For example, when integrating an eSignature solution like SignNow, a developer might use an endpoint to send a document for signing. The API signature defines the request method (e.g., POST), the endpoint URL (such as /document/send), required parameters (like document ID, signer email, and message), and the expected response format. By following this structure precisely, the application can reliably trigger document workflows—uploading a file, assigning recipients, and initiating the signing process. Without a clearly defined API signature, even a powerful API becomes difficult to use, but with it, developers can seamlessly automate complex tasks like collecting legally binding signatures within their own platforms.
Watch the video below for more information and insights on this topic:
Why choose SignNow for your API integration?
Integrating eSignature capabilities into your app requires a platform that prioritizes both usability and strict security. The SignNow API empowers developers to create embedded branded workflows, request payments, and track document status automatically.
Whether you need to support electronic signatures across your enterprise or authenticate users securely, the platform provides the tools you need. With comprehensive documentation, code examples, and dedicated support, developers can seamlessly integrate features that comply with major security regulations, including those governing the European Union.
Disclaimer: The information contained in this blog post is provided for general informational purposes only and does not constitute formal legal advice.
Final thoughts
API signatures use rigorous cryptographic methods to ensure that user credentials are correct, can pass over the network securely, and that the API provider can verify the message remains uncorrupted. They make it possible to use APIs to transmit highly sensitive private data without fear of interception.
In a more general context, encryption and decryption using public and private keys power the digital signing ecosystems we rely on daily. Securing your data is not just a technical requirement; it is a business imperative.
Ready to streamline your document workflows with industry-leading security? Start building secure, scalable eSignature integrations today. Try the SignNow API and empower your users with a seamless, protected signing experience.
Glossary
- API Request: A message sent by a software application to an API to retrieve data or perform a specific action.
- Data Integrity: The assurance that information remains accurate, consistent, and unaltered during storage or transit.
- Hash Function: A mathematical algorithm that transforms input data of any size into a fixed-size string of characters, used for verifying data authenticity.
- Private Key: A secret cryptographic key used to encrypt data or generate digital signatures, known only to the owner.
- Replay Attack: A cyberattack where a valid data transmission is maliciously intercepted and delayed or repeated to unauthorizedly access a system.
FAQ
An API signature verifies the identity of the sender and ensures that the request body has not been tampered with during transit, maintaining strict data integrity.
By including a unique timestamp and a specific string value in the HTTP header, the server can identify and reject duplicate requests that fall outside the acceptable time window.
A private key is kept strictly confidential by the sender to generate the signature. The public key is shared with the receiving server to decrypt and verify that signature.
While the signature itself secures the API request, the underlying technology facilitates the secure transfer of data that powers legally binding digital signatures and electronic signatures.
The SignNow API provides secure, well-documented tools to easily embed document signing workflows into any app, ensuring compliance, saving time, and protecting sensitive data automatically.