Hybrid Analysis Com Sample F6ac66a6720cbfc79httpsapi45 Ilovepdf Comv1download Form


Understanding the global affairs authentication request form
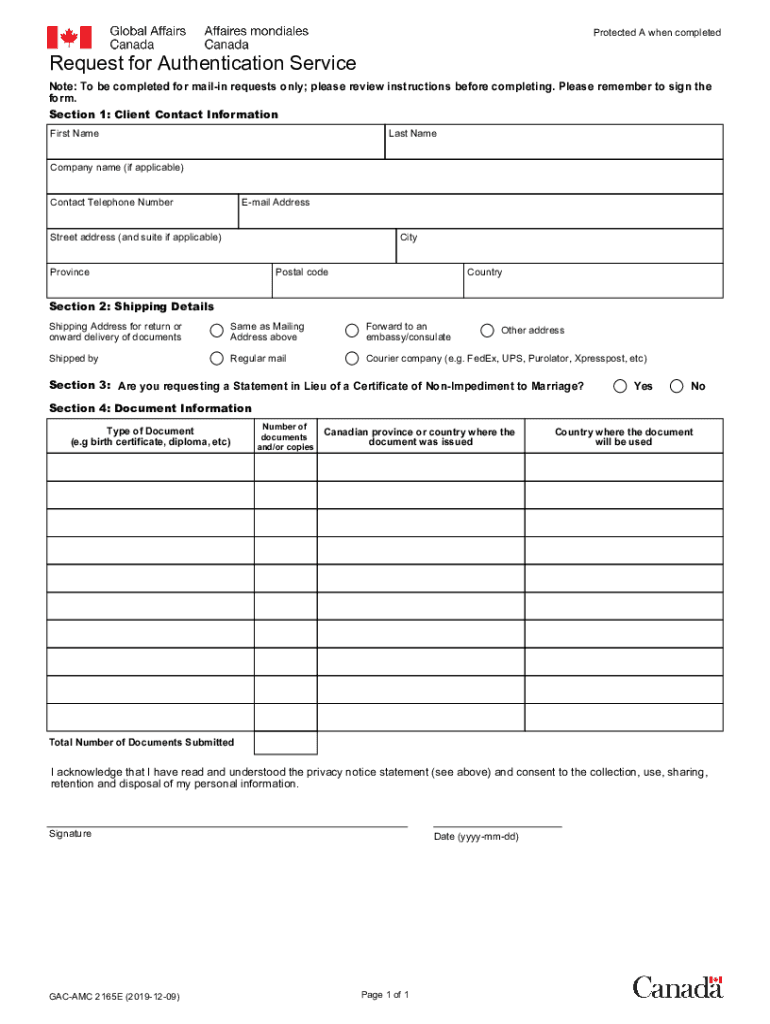
The global affairs authentication request form, also known as form ext2165, is essential for individuals seeking authentication services from Global Affairs Canada. This form is specifically designed for those needing to verify documents for use outside of Canada. It plays a crucial role in ensuring that your documents are recognized and accepted internationally.
Key components of the authentication request form
The authentication request form includes several important sections that must be completed accurately. Key components typically include:
- Personal Information: This section requires your full name, contact details, and any relevant identification numbers.
- Document Details: You must specify the type of documents you are submitting for authentication, including their purpose.
- Payment Information: Include details regarding any applicable fees associated with the authentication process.
Steps to complete the global affairs authentication request form
Completing the global affairs authentication request form involves several straightforward steps:
- Gather all necessary documents that require authentication.
- Fill out the form with accurate personal and document information.
- Review the form to ensure all information is correct and complete.
- Submit the form along with the required documents and payment.
Legal considerations for using the authentication request form
When using the global affairs authentication request form, it is important to understand the legal implications. The form must be filled out truthfully, as providing false information can lead to legal consequences. Additionally, the authentication process adheres to specific regulations that ensure the legitimacy of the documents being authenticated.
Form submission methods
The global affairs authentication request form can typically be submitted in several ways, depending on your preference and the requirements of Global Affairs Canada:
- Online Submission: Many users opt to submit their forms electronically for faster processing.
- Mail: You can send the completed form and documents via postal service, which may take longer.
- In-Person Submission: If you prefer, you may also submit the form in person at designated offices.
Who processes the authentication request form?
The global affairs authentication request form is processed by Global Affairs Canada. This government department is responsible for managing international relations and ensuring that Canadian documents meet the necessary standards for authenticity. Understanding who processes your form can help you navigate any questions or issues that may arise during the authentication process.
Quick guide on how to complete hybrid analysiscom sample f6ac66a6720cbfc79httpsapi45ilovepdfcomv1download
Effortlessly Prepare Hybrid analysis com Sample F6ac66a6720cbfc79httpsapi45 ilovepdf comv1download on Any Device
Managing documents online has gained traction among businesses and individuals. It offers an ideal eco-friendly alternative to conventional printed and signed paperwork, as you can easily locate the necessary form and securely keep it online. airSlate SignNow equips you with all the tools required to create, modify, and electronically sign your documents quickly without delays. Handle Hybrid analysis com Sample F6ac66a6720cbfc79httpsapi45 ilovepdf comv1download on any device using the airSlate SignNow Android or iOS applications and streamline any document-related workflow today.
The Simplest Way to Modify and eSign Hybrid analysis com Sample F6ac66a6720cbfc79httpsapi45 ilovepdf comv1download Effortlessly
- Locate Hybrid analysis com Sample F6ac66a6720cbfc79httpsapi45 ilovepdf comv1download and click Retrieve Form to begin.
- Utilize the tools we offer to complete your form.
- Emphasize important sections of the documents or obscure confidential information with tools that airSlate SignNow provides specifically for that purpose.
- Create your signature with the Sign tool, which takes mere seconds and holds the same legal significance as a traditional ink signature.
- Review all the information and click on the Finish button to save your modifications.
- Select how you wish to send your form, through email, SMS, an invitation link, or download it to your computer.
Say goodbye to lost or misplaced files, tedious form searches, or mistakes that necessitate printing new document copies. airSlate SignNow fulfills your document management needs in just a few clicks from any device of your choice. Modify and eSign Hybrid analysis com Sample F6ac66a6720cbfc79httpsapi45 ilovepdf comv1download and ensure exceptional communication throughout the document preparation process with airSlate SignNow.
Create this form in 5 minutes or less
Create this form in 5 minutes!
How to create an eSignature for the hybrid analysiscom sample f6ac66a6720cbfc79httpsapi45ilovepdfcomv1download
How to generate an electronic signature for a PDF file online
How to generate an electronic signature for a PDF file in Google Chrome
The way to create an electronic signature for signing PDFs in Gmail
How to generate an e-signature straight from your mobile device
How to make an e-signature for a PDF file on iOS
How to generate an e-signature for a PDF document on Android devices
People also ask
-
What is the global affairs authentication request form?
The global affairs authentication request form is a specialized document designed to streamline the authentication process for international transactions. This form helps businesses ensure compliance with global standards while maintaining the integrity of their documents. By utilizing this form, you can enhance the efficiency and reliability of your international dealings.
-
How does airSlate SignNow simplify the global affairs authentication request form process?
airSlate SignNow simplifies the global affairs authentication request form process by providing an intuitive platform for users to create, send, and eSign documents effortlessly. Our user-friendly interface allows you to manage multiple request forms seamlessly, reducing time spent on paperwork. Additionally, robust tracking features keep you updated on the status of each request.
-
Is there a cost associated with using the global affairs authentication request form through airSlate SignNow?
Yes, there is a cost associated with using airSlate SignNow for the global affairs authentication request form, but our pricing is competitive and designed to fit various business needs. We offer flexible subscription plans that allow businesses to choose the best option for their budget and document volume. Investing in an efficient eSigning solution can ultimately save you time and resources.
-
Can I integrate airSlate SignNow with other platforms for the global affairs authentication request form?
Absolutely! airSlate SignNow offers seamless integrations with various platforms, such as CRM systems and cloud storage services, to enhance the global affairs authentication request form workflow. This connectivity ensures that your documents are easily accessible and can be managed within your existing ecosystem. Integrating with other platforms increases productivity and streamlines your overall document management process.
-
What benefits does the global affairs authentication request form provide for businesses?
The global affairs authentication request form provides numerous benefits for businesses, including improved compliance, faster processing times, and enhanced security features. By utilizing this form, organizations can demonstrate their commitment to following international protocols, which can improve credibility and reduce risks. Moreover, the electronic signature capability ensures a quicker turnaround for document approval.
-
What types of documents can I send with the global affairs authentication request form?
With the global affairs authentication request form, you can send a wide range of documents, including contracts, agreements, and certifications needed for international transactions. This versatility allows businesses to manage all their authentication needs in one platform. Moreover, every document sent using SignNow is encrypted, ensuring confidentiality and security.
-
How secure is the global affairs authentication request form when using airSlate SignNow?
The security of the global affairs authentication request form is paramount when using airSlate SignNow. Our platform employs advanced encryption methods to protect your documents and data during transfer and storage. Additionally, Identity verification and audit trails provide an extra layer of security, ensuring that all signatures and actions are traceable.
Get more for Hybrid analysis com Sample F6ac66a6720cbfc79httpsapi45 ilovepdf comv1download
- Verizon bill template form
- Cagayan de oro business permit online application form
- Sh 4 word format
- Key checkout form
- Indlela trade test application form
- Sco im 206 confidential employment inquirypdf suffolk county bb suffolkcountyny form
- Cash handover format in excel
- Job application form pope county co pope mn
Find out other Hybrid analysis com Sample F6ac66a6720cbfc79httpsapi45 ilovepdf comv1download
- Help Me With eSignature New Mexico Healthcare / Medical Form
- How Do I eSignature New York Healthcare / Medical Presentation
- How To eSignature Oklahoma Finance & Tax Accounting PPT
- Help Me With eSignature Connecticut High Tech Presentation
- How To eSignature Georgia High Tech Document
- How Can I eSignature Rhode Island Finance & Tax Accounting Word
- How Can I eSignature Colorado Insurance Presentation
- Help Me With eSignature Georgia Insurance Form
- How Do I eSignature Kansas Insurance Word
- How Do I eSignature Washington Insurance Form
- How Do I eSignature Alaska Life Sciences Presentation
- Help Me With eSignature Iowa Life Sciences Presentation
- How Can I eSignature Michigan Life Sciences Word
- Can I eSignature New Jersey Life Sciences Presentation
- How Can I eSignature Louisiana Non-Profit PDF
- Can I eSignature Alaska Orthodontists PDF
- How Do I eSignature New York Non-Profit Form
- How To eSignature Iowa Orthodontists Presentation
- Can I eSignature South Dakota Lawers Document
- Can I eSignature Oklahoma Orthodontists Document