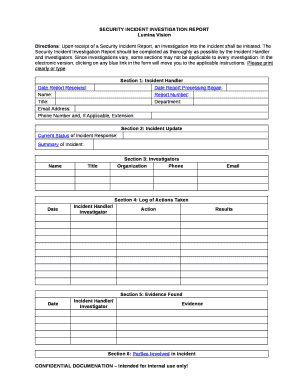
Security Investigation Report Sample Form


Key elements of the theft investigation report format
A theft investigation report format typically includes several essential components that ensure clarity and comprehensiveness. Key elements often found in this format are:
- Incident details: This section should include the date, time, and location of the theft, along with a brief description of the incident.
- Involved parties: List the names and contact information of individuals involved, including witnesses, victims, and suspects.
- Evidence collected: Document any physical evidence, such as photographs, video footage, or items recovered, that supports the investigation.
- Statements: Include a summary of statements from witnesses and involved parties, detailing their observations and accounts of the incident.
- Investigation findings: Present the conclusions drawn from the investigation, including any leads or suspects identified.
- Recommendations: Offer suggestions for further action, such as security improvements or additional investigations.
Steps to complete the theft investigation report format
Completing a theft investigation report format requires a systematic approach to ensure all necessary information is captured accurately. The following steps can guide you through the process:
- Gather information: Collect all relevant details about the incident, including the time, date, and location.
- Interview witnesses: Speak with anyone who may have seen or heard something related to the theft. Document their statements carefully.
- Document evidence: Take photographs and collect any physical evidence that may support the investigation.
- Compile the report: Organize the information into the theft investigation report format, ensuring all key elements are included.
- Review for accuracy: Check the report for any errors or missing information before finalizing it.
- Distribute as necessary: Share the completed report with relevant parties, such as law enforcement or security personnel.
Legal use of the theft investigation report format
The legal use of a theft investigation report format is crucial for ensuring that the document holds up in court or during an investigation. To maintain its legal validity, consider the following:
- Accuracy: Ensure that all information is factual and supported by evidence. Any inaccuracies can undermine the report's credibility.
- Signature requirements: Depending on the jurisdiction, the report may need to be signed by the investigator or other involved parties to be considered valid.
- Compliance with regulations: Familiarize yourself with local laws regarding theft reporting and ensure the report adheres to these regulations.
- Retention policies: Keep a copy of the report for your records, as it may be required for future reference or legal proceedings.
How to use the theft investigation report format
Using the theft investigation report format effectively involves understanding its purpose and how to apply it in various situations. Here are some practical tips:
- Tailor the format: Adjust the format to fit the specific requirements of your organization or jurisdiction, ensuring all necessary sections are included.
- Utilize digital tools: Consider using electronic signature solutions to facilitate the signing process and enhance the report's legal standing.
- Train personnel: Ensure that all staff involved in the investigation process are familiar with the report format and its importance.
- Regular updates: Revise the report format periodically to incorporate any changes in legal requirements or organizational policies.
Examples of using the theft investigation report format
Understanding how to apply the theft investigation report format can be enhanced through real-world examples. Here are a few scenarios:
- Retail theft: A store manager documents a shoplifting incident using the report format, detailing the suspect's description and any video evidence.
- Workplace theft: An HR representative uses the format to report missing company property, including interviews with employees who may have seen suspicious activity.
- Residential burglary: A homeowner files a report with local law enforcement, using the format to outline the details of the break-in and any stolen items.
How to obtain the theft investigation report sample
Obtaining a theft investigation report sample can streamline the process of creating your own report. Here are some ways to access these samples:
- Online resources: Many websites provide downloadable templates or samples that can be customized to fit your needs.
- Legal offices: Contact local law enforcement or legal offices, as they may offer standardized forms or samples for public use.
- Professional organizations: Industry associations often provide resources, including report samples, to their members.
- Peer sharing: Network with colleagues in your field to share and exchange report samples that have been effective in their practices.
Quick guide on how to complete security investigation report sample
Complete Security Investigation Report Sample effortlessly on any device
Web-based document management has become increasingly favored by businesses and individuals alike. It offers an ideal eco-friendly alternative to conventional printed and signed documentation, as you can easily locate the necessary form and securely store it online. airSlate SignNow provides you with all the resources required to create, modify, and eSign your documents rapidly without delays. Manage Security Investigation Report Sample on any device using airSlate SignNow's Android or iOS applications and enhance any document-centric process today.
The easiest way to modify and eSign Security Investigation Report Sample without breaking a sweat
- Locate Security Investigation Report Sample and click on Get Form to begin.
- Utilize the tools we offer to fill out your document.
- Highlight pertinent sections of the documents or redact sensitive information with tools that airSlate SignNow offers specifically for that purpose.
- Create your signature with the Sign tool, which takes mere seconds and carries the same legal validity as a traditional wet ink signature.
- Review the information and click on the Done button to save your changes.
- Choose how you wish to send your form, whether by email, SMS, invitation link, or download it to your computer.
Say goodbye to lost or misplaced documents, tedious form searching, or errors that necessitate printing new document copies. airSlate SignNow meets your document management requirements in just a few clicks from your preferred device. Edit and eSign Security Investigation Report Sample and ensure effective communication at every stage of your form preparation process with airSlate SignNow.
Create this form in 5 minutes or less
Create this form in 5 minutes!
How to create an eSignature for the security investigation report sample
How to create an electronic signature for a PDF online
How to create an electronic signature for a PDF in Google Chrome
How to create an e-signature for signing PDFs in Gmail
How to create an e-signature right from your smartphone
How to create an e-signature for a PDF on iOS
How to create an e-signature for a PDF on Android
People also ask
-
What is the theft investigation report format used for?
The theft investigation report format is specifically designed to document incidents of theft in a structured way. It allows businesses to record essential details about the incident, providing clarity and facilitating follow-ups with authorities. It's essential for various businesses seeking accountability and legal protection.
-
How can airSlate SignNow help with creating a theft investigation report format?
With airSlate SignNow, you can easily create, send, and eSign theft investigation reports using customizable templates. Our platform provides a secure environment to ensure documents are safely stored and efficiently accessed. This streamlines your reporting process, making it quick and hassle-free.
-
Is the theft investigation report format customizable?
Yes, the theft investigation report format within airSlate SignNow is highly customizable. You can add or remove fields according to your specific needs, ensuring that every report captures the necessary details relevant to your incident. This flexibility enhances the effectiveness of your reporting.
-
What are the pricing options for airSlate SignNow?
airSlate SignNow offers various pricing plans to accommodate different business sizes and needs. Each plan provides features, including access to the theft investigation report format, eSigning capabilities, and integrations with other software. You can choose a plan that best fits your business requirements and budget.
-
Are there any integrations available for the theft investigation report format in airSlate SignNow?
Absolutely! airSlate SignNow integrates seamlessly with various tools and software, enhancing your workflow. This includes popular applications like Google Workspace and Microsoft Office, allowing you to incorporate the theft investigation report format within your existing systems effortlessly.
-
What benefits does the theft investigation report format provide?
The theft investigation report format allows businesses to document incidents systematically, improving accountability and response strategies. It supports legal record-keeping and enhances communication with law enforcement. Investing in a structured format expedites the investigation process and reduces potential losses.
-
Can airSlate SignNow enhance the efficiency of creating a theft investigation report format?
Yes, airSlate SignNow drastically enhances efficiency by simplifying document creation and signing. With our user-friendly interface, users can rapidly fill out the theft investigation report format, saving time and ensuring accuracy. This efficient process minimizes delays in reporting incidents.
Get more for Security Investigation Report Sample
Find out other Security Investigation Report Sample
- How To Integrate Sign in Banking
- How To Use Sign in Banking
- Help Me With Use Sign in Banking
- Can I Use Sign in Banking
- How Do I Install Sign in Banking
- How To Add Sign in Banking
- How Do I Add Sign in Banking
- How Can I Add Sign in Banking
- Can I Add Sign in Banking
- Help Me With Set Up Sign in Government
- How To Integrate eSign in Banking
- How To Use eSign in Banking
- How To Install eSign in Banking
- How To Add eSign in Banking
- How To Set Up eSign in Banking
- How To Save eSign in Banking
- How To Implement eSign in Banking
- How To Set Up eSign in Construction
- How To Integrate eSign in Doctors
- How To Use eSign in Doctors