Comsec Briefing Form


What is the Comsec Briefing?
The Comsec briefing is a formal document used to provide essential information regarding the handling of sensitive information and cryptographic materials. It ensures that individuals understand their responsibilities when dealing with classified data. This briefing is crucial for maintaining national security and protecting sensitive information from unauthorized access. The Comsec briefing and acknowledgment form serves as a record of compliance, confirming that the individual has received and understood the necessary protocols and regulations.
Steps to Complete the Comsec Briefing
Completing the Comsec briefing involves several key steps to ensure that all necessary information is accurately provided and understood. First, individuals should carefully read the instructions included with the briefing. Next, they must fill out the required fields, which may include personal identification information and acknowledgment of understanding the guidelines. After completing the form, it is essential to review all entries for accuracy before submitting. Finally, the signed document should be securely stored to maintain compliance with security protocols.
Legal Use of the Comsec Briefing
The legal use of the Comsec briefing is governed by various regulations that ensure the protection of sensitive information. To be considered legally binding, the Comsec secure form must comply with established laws such as the Electronic Signatures in Global and National Commerce Act (ESIGN) and the Uniform Electronic Transactions Act (UETA). These laws provide a framework for the validity of electronic signatures and documents, ensuring that the Comsec briefing is recognized in legal contexts. Utilizing a reliable electronic signature platform enhances the legal standing of the document.
Key Elements of the Comsec Briefing
Several critical elements make up the Comsec briefing, each contributing to its effectiveness in safeguarding sensitive information. These elements include:
- Identification of Sensitive Information: Clearly defines what constitutes sensitive data.
- Responsibilities: Outlines the obligations of individuals handling such information.
- Security Protocols: Details the measures required to protect sensitive information.
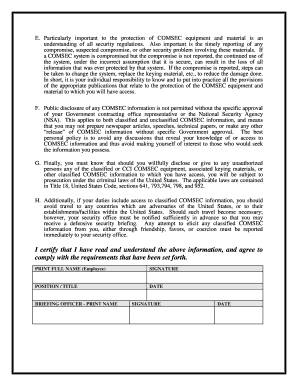
- Acknowledgment: A section for individuals to confirm their understanding and acceptance of the briefing.
These components work together to create a comprehensive understanding of the necessary precautions and responsibilities involved in handling classified information.
How to Obtain the Comsec Briefing
Obtaining the Comsec briefing typically involves a straightforward process. Individuals may receive the briefing through their organization, often as part of onboarding or training related to information security. In some cases, the briefing may be available online through secure portals maintained by relevant authorities. It is important to ensure that the source of the briefing is legitimate and complies with applicable regulations, as this ensures the information provided is accurate and up-to-date.
Examples of Using the Comsec Briefing
The Comsec briefing can be applied in various scenarios where sensitive information is handled. For instance, government employees working with classified materials must complete the briefing to understand their responsibilities. Additionally, contractors who access secure facilities or systems may also be required to undergo the Comsec briefing to ensure compliance with security protocols. These examples illustrate the importance of the briefing in maintaining the integrity of sensitive information across different sectors.
Quick guide on how to complete comsec briefing
Prepare Comsec Briefing effortlessly on any device
Online document management has become increasingly popular among businesses and individuals. It offers an ideal eco-friendly alternative to traditional printed and signed documents, allowing you to access the correct form and securely store it online. airSlate SignNow provides all the necessary tools to create, modify, and electronically sign your documents quickly and efficiently. Manage Comsec Briefing on any device with airSlate SignNow Android or iOS applications and simplify any document-related task today.
How to modify and eSign Comsec Briefing with ease
- Obtain Comsec Briefing and click Get Form to begin.
- Utilize the tools we provide to fill out your document.
- Highlight important sections of the documents or obscure sensitive details with tools that airSlate SignNow specifically offers for that purpose.
- Create your eSignature using the Sign feature, which takes mere seconds and carries the same legal validity as a conventional wet ink signature.
- Review the details and click on the Done button to save your modifications.
- Choose how you would like to send your form, via email, SMS, or a sharing link, or download it to your computer.
Eliminate concerns about lost or misplaced files, tedious form searching, or errors that require reprinting new document copies. airSlate SignNow addresses your document management needs in just a few clicks from any device you prefer. Modify and eSign Comsec Briefing and ensure excellent communication at every stage of your form preparation process with airSlate SignNow.
Create this form in 5 minutes or less
Create this form in 5 minutes!
How to create an eSignature for the comsec briefing
How to create an electronic signature for a PDF online
How to create an electronic signature for a PDF in Google Chrome
How to create an e-signature for signing PDFs in Gmail
How to create an e-signature right from your smartphone
How to create an e-signature for a PDF on iOS
How to create an e-signature for a PDF on Android
People also ask
-
What is a comsec briefing?
A comsec briefing is a communication security presentation designed to inform teams about secure communication practices and protocols. It ensures that all personnel are aware of the necessary measures to protect sensitive information. Understanding these principles is vital, especially when using tools like airSlate SignNow for document management.
-
How can airSlate SignNow assist with comsec briefings?
airSlate SignNow offers a secure platform for delivering and signing documents, which can be integrated into your comsec briefing process. With features like encrypted storage and audit trails, it enhances the security of the briefings themselves. This makes it easier to ensure that all information shared is both secure and legally binding.
-
What are the pricing options for airSlate SignNow?
airSlate SignNow offers several pricing plans, which are designed to fit different business needs and sizes. Each plan provides features that can enhance your comsec briefing processes, ensuring you have the right tools without overspending. It's best to visit our pricing page for the most current options and features included.
-
Are there integrations available with airSlate SignNow?
Yes, airSlate SignNow integrates seamlessly with various applications to streamline workflows, including those related to comsec briefings. Integrations with tools like CRM and project management software help in aligning your secure communication practices with daily operations. This ultimately enhances productivity while safeguarding sensitive information.
-
What features does airSlate SignNow offer for enhancing comsec briefings?
Key features of airSlate SignNow include advanced encryption, customizable templates, and user-friendly dashboards that facilitate effective comsec briefings. These features help ensure that all communications are secure and compliant with legal standards. Additionally, the ability to track document statuses ensures clarity in the briefing process.
-
How does airSlate SignNow ensure document security during comsec briefings?
airSlate SignNow employs military-grade encryption and secure cloud storage to protect documents during comsec briefings. These measures ensure that sensitive information is not just accessible to authorized users but also stored in a secure environment. You can have peace of mind knowing that your communications are safeguarded.
-
Can I use airSlate SignNow for mobile comsec briefings?
Yes, airSlate SignNow is accessible on mobile devices, making it ideal for conducting comsec briefings on the go. Its mobile-friendly design allows users to sign documents and manage communication securely from anywhere. This flexibility is crucial for teams that operate in various locations.
Get more for Comsec Briefing
Find out other Comsec Briefing
- eSignature Hawaii Sports Living Will Safe
- eSignature Hawaii Sports LLC Operating Agreement Myself
- eSignature Maryland Real Estate Quitclaim Deed Secure
- eSignature Idaho Sports Rental Application Secure
- Help Me With eSignature Massachusetts Real Estate Quitclaim Deed
- eSignature Police Document Florida Easy
- eSignature Police Document Florida Safe
- How Can I eSignature Delaware Police Living Will
- eSignature Michigan Real Estate LLC Operating Agreement Mobile
- eSignature Georgia Police Last Will And Testament Simple
- How To eSignature Hawaii Police RFP
- Can I eSignature Minnesota Real Estate Warranty Deed
- How Do I eSignature Indiana Police Lease Agreement Form
- eSignature Police PPT Kansas Free
- How Can I eSignature Mississippi Real Estate Rental Lease Agreement
- How Do I eSignature Kentucky Police LLC Operating Agreement
- eSignature Kentucky Police Lease Termination Letter Now
- eSignature Montana Real Estate Quitclaim Deed Mobile
- eSignature Montana Real Estate Quitclaim Deed Fast
- eSignature Montana Real Estate Cease And Desist Letter Easy