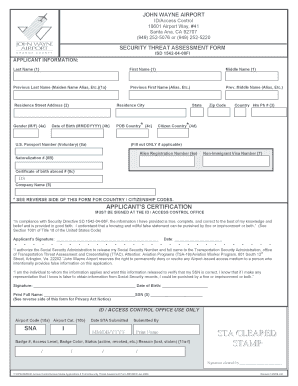
Threat Assessment Form


What is the threat assessment form?
The threat assessment form is a structured document designed to evaluate potential threats within various environments, such as schools or workplaces. It serves as a vital tool for identifying, assessing, and addressing risks that may pose a danger to individuals or organizations. The form typically includes sections for detailing the nature of the threat, the individuals involved, and any relevant context that may help in understanding the situation. By utilizing this form, organizations can create a systematic approach to managing threats, ensuring a safer environment for all stakeholders.
How to use the threat assessment form
Using the threat assessment form involves several key steps to ensure its effectiveness. First, gather all necessary information regarding the threat, including specifics about the individuals involved, the context of the situation, and any previous incidents. Next, fill out the form methodically, ensuring that each section is completed with accurate and detailed information. After completing the form, it should be reviewed by relevant personnel, such as school administrators or law enforcement officials, to determine the appropriate course of action. Finally, maintain a record of the assessment for future reference and follow-up actions.
Steps to complete the threat assessment form
Completing the threat assessment form requires a systematic approach to ensure thoroughness and accuracy. Follow these steps:
- Begin by identifying the individual or group involved in the threat.
- Describe the nature of the threat, including any specific actions or statements made.
- Provide context by detailing any relevant history or background information.
- Assess the level of risk associated with the threat, considering factors such as intent and capability.
- Document any immediate actions taken in response to the threat.
- Review the completed form with appropriate stakeholders for further evaluation.
Legal use of the threat assessment form
For the threat assessment form to be legally valid, it must adhere to specific guidelines and regulations. In the United States, compliance with laws such as the Family Educational Rights and Privacy Act (FERPA) is essential, especially when dealing with student information. Additionally, the form should be filled out with accuracy and honesty, as any misrepresentation could lead to legal consequences. Utilizing a secure platform for electronic signatures, such as signNow, can enhance the legal standing of the document by ensuring that all signatures are verifiable and compliant with eSignature laws.
Key elements of the threat assessment form
The threat assessment form typically includes several key elements that are crucial for effective evaluation. These elements may consist of:
- Identification of the individual making the threat.
- Details of the threat itself, including specific language or actions.
- Contextual information, such as the environment where the threat occurred.
- Assessment of the threat's seriousness and potential impact.
- Recommendations for follow-up actions or interventions.
Examples of using the threat assessment form
Examples of using the threat assessment form can vary widely based on the context. In a school setting, a teacher may complete the form after a student makes a concerning statement. In a workplace, an employee might report a colleague's aggressive behavior. In both scenarios, the completed form helps administrators or security personnel assess the situation and determine the necessary steps to ensure safety. These examples illustrate the form's versatility in addressing threats across different environments.
Quick guide on how to complete threat assessment form
Effortlessly Prepare Threat Assessment Form on Any Device
Digital document management has become increasingly popular among organizations and individuals. It offers an ideal environmentally friendly alternative to conventional printed and signed documents, as you can easily find the appropriate form and securely store it online. airSlate SignNow provides all the tools necessary to create, modify, and eSign your documents swiftly and without delays. Manage Threat Assessment Form on any device using airSlate SignNow's Android or iOS applications and enhance any document-based workflow today.
The easiest way to modify and eSign Threat Assessment Form effortlessly
- Find Threat Assessment Form and click Get Form to begin.
- Utilize the tools we provide to complete your form.
- Highlight pertinent sections of your documents or obscure sensitive information using tools that airSlate SignNow offers specifically for that purpose.
- Generate your eSignature using the Sign feature, which takes only seconds and holds the same legal validity as a traditional handwritten signature.
- Review all the details and click the Done button to save your modifications.
- Choose how you'd like to send your form, whether by email, SMS, invitation link, or download it to your computer.
Say goodbye to lost or misplaced documents, tedious form searching, or errors that require printing new document copies. airSlate SignNow meets your document management needs in just a few clicks from any device you prefer. Alter and eSign Threat Assessment Form and ensure excellent communication at every stage of the form preparation process with airSlate SignNow.
Create this form in 5 minutes or less
Create this form in 5 minutes!
How to create an eSignature for the threat assessment form
How to create an electronic signature for a PDF online
How to create an electronic signature for a PDF in Google Chrome
How to create an e-signature for signing PDFs in Gmail
How to create an e-signature right from your smartphone
How to create an e-signature for a PDF on iOS
How to create an e-signature for a PDF on Android
People also ask
-
What is a threat assessment template?
A threat assessment template is a structured document that helps organizations identify and evaluate potential threats. Using a well-designed template allows for a thorough analysis of vulnerabilities and mitigation strategies, ensuring a proactive approach to risk management.
-
How can airSlate SignNow help with my threat assessment template?
airSlate SignNow provides features that allow you to easily create, send, and eSign your threat assessment template. The platform streamlines the process, making it efficient to gather necessary signatures and documentation, thus enhancing your threat assessment efforts.
-
Is airSlate SignNow cost-effective for using a threat assessment template?
Yes, airSlate SignNow offers competitive pricing plans that make it accessible for businesses of all sizes. This cost-effective solution will allow you to implement a threat assessment template without stretching your budget, ensuring you get great value.
-
What features does airSlate SignNow offer for managing a threat assessment template?
airSlate SignNow includes features such as customizable templates, cloud storage, and integrated eSigning capabilities, all of which are beneficial for managing your threat assessment template. These functionalities enhance collaboration and ensure that all parties can work efficiently on the document.
-
Are there integrations available for the threat assessment template?
Absolutely! airSlate SignNow integrates with numerous applications, allowing you to connect your threat assessment template with tools you already use. This seamless integration enhances workflow efficiency and ensures that your data remains synchronized across platforms.
-
What benefits does using a structured threat assessment template provide?
Using a structured threat assessment template ensures a comprehensive approach to identifying risks, making it easier to prioritize actions. It facilitates better communication among stakeholders and provides a clear framework for assessing and responding to threats.
-
Can I collaborate with my team on a threat assessment template using airSlate SignNow?
Yes, airSlate SignNow supports real-time collaboration, allowing your team to work together on the threat assessment template. This feature enhances teamwork and ensures that all relevant insights are included in the final document.
Get more for Threat Assessment Form
- Nozha language school sheets form
- Gap cancellation form protective asset protection
- Impoundment inspection form
- Gid 242 nt form
- Bureau of motor vehicles letterhead state of indiana state in form
- Frontier lifeline application ny form
- Ahca medicaid authorization for the use and disclosure of protected health form
- Film producer agreement template form
Find out other Threat Assessment Form
- Electronic signature Pennsylvania Police Executive Summary Template Free
- Electronic signature Pennsylvania Police Forbearance Agreement Fast
- How Do I Electronic signature Pennsylvania Police Forbearance Agreement
- How Can I Electronic signature Pennsylvania Police Forbearance Agreement
- Electronic signature Washington Real Estate Purchase Order Template Mobile
- Electronic signature West Virginia Real Estate Last Will And Testament Online
- Electronic signature Texas Police Lease Termination Letter Safe
- How To Electronic signature Texas Police Stock Certificate
- How Can I Electronic signature Wyoming Real Estate Quitclaim Deed
- Electronic signature Virginia Police Quitclaim Deed Secure
- How Can I Electronic signature West Virginia Police Letter Of Intent
- How Do I Electronic signature Washington Police Promissory Note Template
- Electronic signature Wisconsin Police Permission Slip Free
- Electronic signature Minnesota Sports Limited Power Of Attorney Fast
- Electronic signature Alabama Courts Quitclaim Deed Safe
- How To Electronic signature Alabama Courts Stock Certificate
- Can I Electronic signature Arkansas Courts Operating Agreement
- How Do I Electronic signature Georgia Courts Agreement
- Electronic signature Georgia Courts Rental Application Fast
- How Can I Electronic signature Hawaii Courts Purchase Order Template