NVDCMS 2 0 Technical Fact Sheet Nvdcms Form


What is the NVDCMS 2 0 Technical Fact Sheet Nvdcms
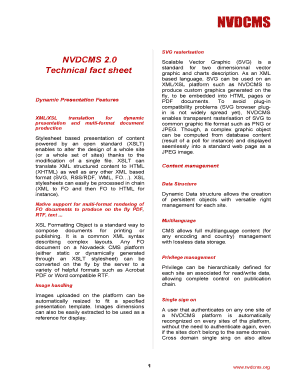
The NVDCMS 2 0 Technical Fact Sheet Nvdcms serves as a comprehensive document that outlines the technical specifications and guidelines related to the NVDCMS system. This fact sheet is essential for understanding the functionalities, requirements, and intended use of the NVDCMS framework. It provides users with critical information that aids in the effective implementation and utilization of the system.
How to use the NVDCMS 2 0 Technical Fact Sheet Nvdcms
To effectively use the NVDCMS 2 0 Technical Fact Sheet Nvdcms, users should first familiarize themselves with its structure and key sections. The fact sheet typically includes detailed descriptions of system features, operational guidelines, and troubleshooting tips. Users can refer to specific sections relevant to their needs, ensuring they adhere to the outlined procedures and recommendations for optimal performance.
Steps to complete the NVDCMS 2 0 Technical Fact Sheet Nvdcms
Completing the NVDCMS 2 0 Technical Fact Sheet Nvdcms involves several key steps:
- Review the introductory section to understand the purpose of the fact sheet.
- Identify and gather any required technical specifications or documentation.
- Follow the outlined procedures for data entry and submission.
- Ensure all information is accurate and complete before finalizing the document.
By following these steps, users can ensure that they complete the fact sheet efficiently and effectively.
Legal use of the NVDCMS 2 0 Technical Fact Sheet Nvdcms
The legal use of the NVDCMS 2 0 Technical Fact Sheet Nvdcms is governed by applicable regulations and standards. Users must ensure that they comply with all relevant laws when utilizing the fact sheet. This includes adhering to data protection regulations and ensuring that the information provided is used solely for its intended purposes, maintaining confidentiality and integrity throughout the process.
Key elements of the NVDCMS 2 0 Technical Fact Sheet Nvdcms
Key elements of the NVDCMS 2 0 Technical Fact Sheet Nvdcms include:
- System overview and objectives
- Technical specifications and requirements
- Operational guidelines and best practices
- Troubleshooting and support resources
Understanding these elements is crucial for users to navigate the NVDCMS system effectively.
Examples of using the NVDCMS 2 0 Technical Fact Sheet Nvdcms
Examples of using the NVDCMS 2 0 Technical Fact Sheet Nvdcms can include:
- Implementing system updates based on the fact sheet's guidelines.
- Training new staff on the technical requirements as outlined in the document.
- Utilizing troubleshooting tips to resolve common issues encountered during operation.
These examples illustrate the practical applications of the fact sheet in real-world scenarios.
Quick guide on how to complete nvdcms 2 0 technical fact sheet nvdcms
Effortlessly Complete [SKS] on Any Device
Managing documents online has become increasingly popular among businesses and individuals. It serves as an excellent eco-friendly alternative to traditional printed and signed paperwork, allowing you to easily locate the right form and securely store it online. airSlate SignNow provides all the tools necessary to swiftly create, modify, and electronically sign your documents without any delays. Manage [SKS] on any device with the airSlate SignNow applications for Android or iOS and streamline your document-related processes today.
How to Modify and Electronically Sign [SKS] with Ease
- Locate [SKS] and click on Get Form to begin.
- Utilize the tools we provide to complete your document.
- Mark important sections of the documents or redact sensitive information using tools specifically designed for that purpose by airSlate SignNow.
- Create your electronic signature with the Sign tool, which takes mere seconds and carries the same legal validity as a conventional wet ink signature.
- Review all details and click on the Done button to save your modifications.
- Choose your preferred method to share your form, whether via email, SMS, or invitation link, or download it to your computer.
Say goodbye to lost or misplaced documents, tedious form searches, or mistakes that necessitate printing new copies. airSlate SignNow addresses all your document management requirements in just a few clicks from your chosen device. Modify and electronically sign [SKS] to ensure superior communication at every stage of the form preparation process with airSlate SignNow.
Create this form in 5 minutes or less
Related searches to NVDCMS 2 0 Technical Fact Sheet Nvdcms
Create this form in 5 minutes!
How to create an eSignature for the nvdcms 2 0 technical fact sheet nvdcms
How to create an electronic signature for a PDF online
How to create an electronic signature for a PDF in Google Chrome
How to create an e-signature for signing PDFs in Gmail
How to create an e-signature right from your smartphone
How to create an e-signature for a PDF on iOS
How to create an e-signature for a PDF on Android
People also ask
-
What is the NVDCMS 2 0 Technical Fact Sheet Nvdcms?
The NVDCMS 2 0 Technical Fact Sheet Nvdcms provides detailed information about the capabilities and specifications of the NVDCMS 2.0 system. It serves as a comprehensive guide for users and businesses looking to understand the technical aspects and benefits of this solution.
-
How much does the NVDCMS 2 0 Technical Fact Sheet Nvdcms cost?
The pricing for access to the NVDCMS 2 0 Technical Fact Sheet Nvdcms may vary based on subscription plans and user requirements. Our pricing structures are designed to be cost-effective, ensuring that businesses of any size can benefit from our services.
-
What features are included in the NVDCMS 2 0 Technical Fact Sheet Nvdcms?
The NVDCMS 2 0 Technical Fact Sheet Nvdcms includes features such as document generation, automated workflows, and eSigning capabilities. These features are designed to streamline document management and enhance operational efficiency for businesses.
-
How can the NVDCMS 2 0 Technical Fact Sheet Nvdcms benefit my business?
By utilizing the NVDCMS 2 0 Technical Fact Sheet Nvdcms, businesses can improve their workflow by reducing the time spent on document management. This can lead to faster transaction times and improved collaboration among teams, ultimately enhancing productivity.
-
Is the NVDCMS 2 0 Technical Fact Sheet Nvdcms easy to integrate with other systems?
Yes, the NVDCMS 2 0 Technical Fact Sheet Nvdcms is designed for easy integration with various business applications. This ensures a seamless experience for users looking to incorporate our solution into their existing workflows and systems.
-
How secure is the NVDCMS 2 0 Technical Fact Sheet Nvdcms?
The NVDCMS 2 0 Technical Fact Sheet Nvdcms prioritizes data security and compliance. We implement advanced encryption protocols and adhere to industry standards to safeguard sensitive information, ensuring a secure eSigning and document management environment.
-
Can I access the NVDCMS 2 0 Technical Fact Sheet Nvdcms from mobile devices?
Yes, the NVDCMS 2 0 Technical Fact Sheet Nvdcms is optimized for mobile access. This allows users to manage documents and eSign on-the-go, providing flexibility and convenience for busy professionals.
Get more for NVDCMS 2 0 Technical Fact Sheet Nvdcms
Find out other NVDCMS 2 0 Technical Fact Sheet Nvdcms
- Electronic signature Banking Document Iowa Online
- Can I eSignature West Virginia Sports Warranty Deed
- eSignature Utah Courts Contract Safe
- Electronic signature Maine Banking Permission Slip Fast
- eSignature Wyoming Sports LLC Operating Agreement Later
- Electronic signature Banking Word Massachusetts Free
- eSignature Wyoming Courts Quitclaim Deed Later
- Electronic signature Michigan Banking Lease Agreement Computer
- Electronic signature Michigan Banking Affidavit Of Heirship Fast
- Electronic signature Arizona Business Operations Job Offer Free
- Electronic signature Nevada Banking NDA Online
- Electronic signature Nebraska Banking Confidentiality Agreement Myself
- Electronic signature Alaska Car Dealer Resignation Letter Myself
- Electronic signature Alaska Car Dealer NDA Mobile
- How Can I Electronic signature Arizona Car Dealer Agreement
- Electronic signature California Business Operations Promissory Note Template Fast
- How Do I Electronic signature Arkansas Car Dealer Claim
- Electronic signature Colorado Car Dealer Arbitration Agreement Mobile
- Electronic signature California Car Dealer Rental Lease Agreement Fast
- Electronic signature Connecticut Car Dealer Lease Agreement Now