Penetration Testing Agreement PDF Form


What is the penetration testing agreement PDF?
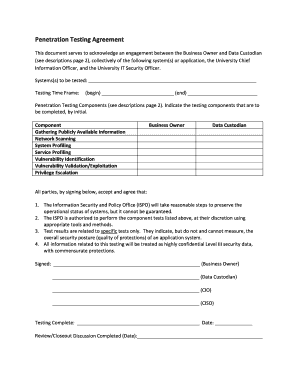
A penetration testing agreement PDF is a legal document that outlines the terms and conditions between a client and a service provider engaged in penetration testing services. This agreement is essential for defining the scope of the testing, the responsibilities of each party, and the confidentiality of the information accessed during the testing process. It serves as a safeguard for both parties, ensuring that the testing is conducted ethically and legally.
Typically, this document includes details such as the duration of the testing, the specific systems or applications to be tested, and the methodologies to be employed. It may also address liability issues, data protection measures, and the procedures for reporting findings. By formalizing these aspects, the penetration testing agreement helps mitigate risks associated with unauthorized access and data breaches.
Key elements of the penetration testing agreement PDF
Understanding the key elements of a penetration testing agreement is crucial for both clients and service providers. This document generally includes the following components:
- Scope of Work: Clearly defines what systems or applications will be tested and the extent of the testing.
- Confidentiality Clause: Ensures that sensitive information accessed during testing remains protected.
- Liability and Indemnification: Outlines the responsibilities of each party in case of damages or breaches.
- Reporting Requirements: Specifies how findings will be communicated and the timeline for reporting.
- Compliance Standards: Addresses adherence to relevant laws and regulations, such as GDPR or HIPAA.
These elements help establish a clear understanding between both parties, reducing the potential for disputes and ensuring a smooth testing process.
Steps to complete the penetration testing agreement PDF
Completing a penetration testing agreement PDF involves several important steps to ensure that all necessary information is accurately captured. Here are the typical steps to follow:
- Identify the Parties: Include the names and contact information of both the client and the service provider.
- Define the Scope: Clearly outline the systems, applications, and specific tests to be conducted.
- Set the Timeline: Specify the start and end dates for the testing engagement.
- Review Legal Requirements: Ensure compliance with applicable laws and regulations relevant to the testing.
- Sign and Date: Both parties should sign and date the agreement to make it legally binding.
Following these steps helps ensure that the agreement is comprehensive and legally enforceable, providing protection for both parties involved.
How to use the penetration testing agreement PDF
Using a penetration testing agreement PDF effectively requires understanding its purpose and how it fits into the testing process. Here are some guidelines for utilizing this document:
- Review Before Signing: Both parties should thoroughly review the agreement to ensure all terms are acceptable and clear.
- Maintain Copies: Keep signed copies of the agreement for record-keeping and future reference.
- Follow the Terms: Adhere to the stipulations outlined in the agreement during the testing process to avoid breaches.
- Update as Necessary: If the scope or terms change, amend the agreement to reflect these updates and have both parties sign the new version.
By following these practices, both clients and service providers can ensure that their engagement is conducted smoothly and in accordance with the agreed terms.
Quick guide on how to complete penetration testing agreement pdf
Prepare Penetration Testing Agreement Pdf seamlessly on any device
Online document management has gained traction among businesses and individuals alike. It offers an excellent environmentally friendly substitute to conventional printed and signed papers, as you can easily locate the necessary form and securely save it online. airSlate SignNow equips you with all the features required to create, edit, and eSign your documents promptly without delays. Manage Penetration Testing Agreement Pdf on any device using airSlate SignNow Android or iOS applications and streamline any document-related process today.
How to edit and eSign Penetration Testing Agreement Pdf effortlessly
- Find Penetration Testing Agreement Pdf and click on Get Form to begin.
- Use the tools we offer to fill out your document.
- Mark essential portions of the documents or obscure sensitive data with tools specifically designed for that purpose by airSlate SignNow.
- Generate your signature using the Sign tool, which takes just seconds and carries the same legal validity as a traditional ink signature.
- Review the details and then click the Done button to save your modifications.
- Select your preferred method for sending your form, whether by email, SMS, invite link, or download it to your computer.
Forget about lost or misplaced documents, tedious form searching, or errors that require printing new copies. airSlate SignNow meets all your document management requirements with just a few clicks from any device of your choice. Edit and eSign Penetration Testing Agreement Pdf to ensure exceptional communication at every phase of your form preparation process with airSlate SignNow.
Create this form in 5 minutes or less
Create this form in 5 minutes!
How to create an eSignature for the penetration testing agreement pdf
How to create an electronic signature for a PDF online
How to create an electronic signature for a PDF in Google Chrome
How to create an e-signature for signing PDFs in Gmail
How to create an e-signature right from your smartphone
How to create an e-signature for a PDF on iOS
How to create an e-signature for a PDF on Android
People also ask
-
What is a pentest agreement template?
A pentest agreement template is a legal document that outlines the terms and conditions between an organization and a cybersecurity firm conducting a penetration test. It clarifies the scope, responsibilities, and liabilities involved in the testing process, ensuring both parties understand their obligations. Using a pentest agreement template helps secure your organization's data while facilitating clear communication.
-
Why do I need a pentest agreement template?
Having a pentest agreement template is crucial for protecting both your organization and the cybersecurity provider during the testing process. It establishes necessary legal protections, defines the range of testing, and sets clear expectations. This minimizes the risk of misunderstandings and legal disputes, making it an essential part of any security assessment.
-
How can I customize a pentest agreement template?
You can easily customize a pentest agreement template to fit your organization's specific needs and requirements by modifying sections such as scope, timelines, and confidentiality clauses. airSlate SignNow allows for seamless editing and eSigning of documents, making it simple to tailor the template according to the nature of your testing engagement. This customization ensures that all unique aspects of your agreement are accurately reflected.
-
What features should I look for in a pentest agreement template?
An effective pentest agreement template should include comprehensive sections on scope, rules of engagement, confidentiality, and liability disclaimers. Look for a template that provides clear guidance on what is to be tested, the duration of the test, and how the findings will be handled. Utilizing airSlate SignNow ensures that your template is also user-friendly and ready for secure digital signatures.
-
Is there a cost associated with using a pentest agreement template?
The cost of using a pentest agreement template can vary depending on where you obtain it. While some templates are available for free, others may come at a price, especially if they include additional legal protections or customizations. With airSlate SignNow, you can access both free and premium templates that offer competitive pricing and great value for your cybersecurity investments.
-
Can I integrate my pentest agreement template with other tools?
Yes, airSlate SignNow allows you to integrate your pentest agreement template with various tools and platforms, enhancing your workflow and management processes. You can connect with project management, customer relationship management, and document storage platforms to streamline your operations. This integration ensures that your pentest agreement template is easily accessible and efficiently managed.
-
What are the benefits of using a pentest agreement template?
Using a pentest agreement template helps ensure that both parties are aligned on expectations and legal responsibilities. It provides a clear framework for conducting penetration tests, reducing the risk of legal complications and promoting a smooth testing process. By utilizing airSlate SignNow's easy-to-use platform, businesses can efficiently manage these agreements and ensure compliance.
Get more for Penetration Testing Agreement Pdf
Find out other Penetration Testing Agreement Pdf
- Can I Electronic signature Hawaii Real Estate PPT
- How Can I Electronic signature Illinois Real Estate Document
- How Do I Electronic signature Indiana Real Estate Presentation
- How Can I Electronic signature Ohio Plumbing PPT
- Can I Electronic signature Texas Plumbing Document
- How To Electronic signature Michigan Real Estate Form
- How To Electronic signature Arizona Police PDF
- Help Me With Electronic signature New Hampshire Real Estate PDF
- Can I Electronic signature New Hampshire Real Estate Form
- Can I Electronic signature New Mexico Real Estate Form
- How Can I Electronic signature Ohio Real Estate Document
- How To Electronic signature Hawaii Sports Presentation
- How To Electronic signature Massachusetts Police Form
- Can I Electronic signature South Carolina Real Estate Document
- Help Me With Electronic signature Montana Police Word
- How To Electronic signature Tennessee Real Estate Document
- How Do I Electronic signature Utah Real Estate Form
- How To Electronic signature Utah Real Estate PPT
- How Can I Electronic signature Virginia Real Estate PPT
- How Can I Electronic signature Massachusetts Sports Presentation