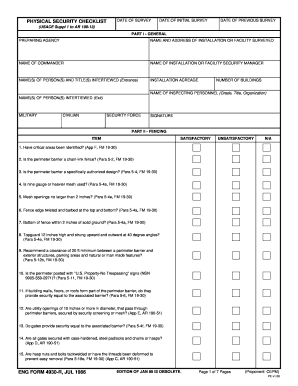
Security Checklist Form


What is the Security Checklist Form
The end of day security check form is a crucial document used to ensure that all security measures have been completed at the close of business. This form typically includes a series of checks that verify the security of physical and digital assets. By documenting these checks, businesses can maintain compliance with security protocols and provide a record for audits. The form serves as a safeguard against potential breaches and ensures that all necessary precautions are taken to protect company resources.
How to Use the Security Checklist Form
Using the end of day security check form involves a systematic approach to ensure all security tasks are completed. First, gather all necessary materials and access the form digitally. Next, review each item on the checklist, which may include verifying alarm systems, securing entry points, and ensuring that sensitive information is properly stored. As each task is completed, mark it off on the form. This process not only enhances security but also provides a clear record of compliance for future reference.
Steps to Complete the Security Checklist Form
Completing the end of day security check form involves several key steps:
- Begin by reviewing the checklist to understand all required security measures.
- Conduct a physical walkthrough of the premises, checking all entry points and security systems.
- Verify that all sensitive documents and digital data are secured.
- Document any discrepancies or issues found during the checks.
- Sign and date the form to confirm that the checks have been completed.
Following these steps ensures that the security checklist is thorough and effective.
Key Elements of the Security Checklist Form
The end of day security check form typically includes several key elements that are essential for effective security management:
- Identification: Name of the individual completing the form and the date of the check.
- Checklist Items: A comprehensive list of security tasks to be completed.
- Notes Section: Space for documenting any issues or observations during the checks.
- Signature Line: A place for the individual to sign, confirming that all checks have been performed.
These elements contribute to the form's effectiveness in maintaining security standards.
Legal Use of the Security Checklist Form
The end of day security check form is legally binding when completed accurately and signed. It serves as evidence that a business has taken necessary precautions to secure its assets, which can be critical in legal situations. Compliance with relevant regulations, such as those outlined by the Occupational Safety and Health Administration (OSHA) and other federal guidelines, is essential. Businesses should ensure that their security checklist aligns with these legal requirements to avoid potential liabilities.
Digital vs. Paper Version
Both digital and paper versions of the end of day security check form have their advantages. The digital version allows for easier storage, retrieval, and sharing among team members. It can also facilitate real-time updates and modifications. In contrast, a paper version may be preferred in environments where technology is limited or where physical signatures are required. Regardless of the format, the key is to ensure that the form is completed accurately and stored securely.
Quick guide on how to complete security checklist form
Effortlessly Prepare Security Checklist Form on Any Device
The management of online documents has gained traction among businesses and individuals alike. It offers an ideal eco-friendly substitute for traditional printed and signed documents, allowing you to obtain the right format and securely store it online. airSlate SignNow provides all the tools necessary to quickly create, modify, and electronically sign your documents without delays. Manage Security Checklist Form on any platform with the airSlate SignNow mobile applications for Android or iOS, and enhance any document-centric process today.
Edit and Electronically Sign Security Checklist Form with Ease
- Obtain Security Checklist Form and then click Get Form to begin.
- Utilize the tools we provide to complete your document.
- Highlight important parts of your documents or obscure sensitive information with the tools specifically designed for this purpose by airSlate SignNow.
- Create your electronic signature with the Sign tool, which takes mere seconds and carries the same legal validity as a conventional wet ink signature.
- Recheck the details and then click on the Done button to save your changes.
- Choose how you wish to send your form, whether by email, SMS, invitation link, or download it to your computer.
Eliminate the worries of lost or misplaced files, tedious form searching, or errors requiring the printing of new document copies. airSlate SignNow addresses your document management needs with just a few clicks from any device of your preference. Modify and electronically sign Security Checklist Form to ensure exceptional communication at every stage of your form preparation process with airSlate SignNow.
Create this form in 5 minutes or less
Create this form in 5 minutes!
How to create an eSignature for the security checklist form
How to create an electronic signature for a PDF online
How to create an electronic signature for a PDF in Google Chrome
How to create an e-signature for signing PDFs in Gmail
How to create an e-signature right from your smartphone
How to create an e-signature for a PDF on iOS
How to create an e-signature for a PDF on Android
People also ask
-
What is the end of day security check form?
The end of day security check form is a digital document that helps businesses verify security protocols at the close of each day. Using airSlate SignNow, you can easily create and send this form for eSignature, ensuring compliance and accountability.
-
How does airSlate SignNow simplify the end of day security check form process?
airSlate SignNow streamlines the end of day security check form process by allowing you to customize forms, automate workflows, and securely collect digital signatures. This eliminates paperwork, saving time and reducing errors while enhancing security.
-
Is there a cost associated with using the end of day security check form on airSlate SignNow?
Pricing for using the end of day security check form on airSlate SignNow varies based on your subscription plan. Each plan offers different features, making it a cost-effective solution tailored to your business needs and helping you stay within budget.
-
What features can I utilize for the end of day security check form?
With airSlate SignNow, you can utilize features such as customizable templates, automated reminders, and secure cloud storage for your end of day security check form. These tools enhance efficiency and ensure that all necessary data is captured accurately.
-
Can the end of day security check form be integrated with other software?
Yes, airSlate SignNow allows for seamless integration of the end of day security check form with other popular applications and software. This enhances productivity by ensuring data flows smoothly between your systems without manual entry.
-
How does using an end of day security check form improve workplace security?
Implementing an end of day security check form through airSlate SignNow enhances workplace security by ensuring that key security measures are consistently addressed. Regular completion of this form promotes accountability in maintaining safety standards across your organization.
-
What benefits does the end of day security check form provide to businesses?
The end of day security check form offers numerous benefits, including increased efficiency, improved accuracy in record-keeping, and enhanced compliance with security protocols. By adopting airSlate SignNow, businesses can signNowly reduce the time spent on manual documentation.
Get more for Security Checklist Form
Find out other Security Checklist Form
- How Can I Electronic signature Alabama Finance & Tax Accounting Document
- How To Electronic signature Delaware Government Document
- Help Me With Electronic signature Indiana Education PDF
- How To Electronic signature Connecticut Government Document
- How To Electronic signature Georgia Government PDF
- Can I Electronic signature Iowa Education Form
- How To Electronic signature Idaho Government Presentation
- Help Me With Electronic signature Hawaii Finance & Tax Accounting Document
- How Can I Electronic signature Indiana Government PDF
- How Can I Electronic signature Illinois Finance & Tax Accounting PPT
- How To Electronic signature Maine Government Document
- How To Electronic signature Louisiana Education Presentation
- How Can I Electronic signature Massachusetts Government PDF
- How Do I Electronic signature Montana Government Document
- Help Me With Electronic signature Louisiana Finance & Tax Accounting Word
- How To Electronic signature Pennsylvania Government Document
- Can I Electronic signature Texas Government PPT
- How To Electronic signature Utah Government Document
- How To Electronic signature Washington Government PDF
- How Can I Electronic signature New Mexico Finance & Tax Accounting Word