Dot Security Plan Example Form


What is the Dot Security Plan Example
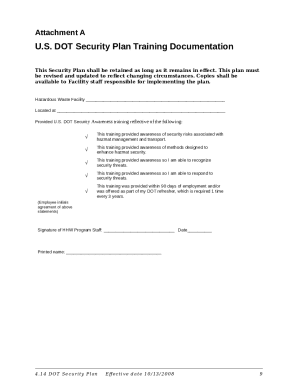
The dot security plan example serves as a structured document designed to outline safety and security protocols for businesses, particularly those handling hazardous materials. This example provides a framework for compliance with federal regulations, ensuring that organizations meet the necessary legal requirements for safety management. It typically includes sections detailing risk assessments, emergency response procedures, and employee training protocols, all aimed at safeguarding both personnel and the environment.
Key Elements of the Dot Security Plan Example
A comprehensive dot security plan example includes several critical components:
- Risk Assessment: Identifying potential hazards and evaluating risks associated with operations.
- Emergency Response Procedures: Outlining steps to take in case of an incident, including evacuation plans and communication strategies.
- Employee Training: Detailing training requirements for staff to ensure they are equipped to handle emergencies safely.
- Regulatory Compliance: Ensuring all aspects of the plan align with federal and state regulations relevant to hazardous materials.
- Documentation and Record Keeping: Maintaining accurate records of safety inspections, training sessions, and incident reports.
Steps to Complete the Dot Security Plan Example
Completing the dot security plan example involves several key steps:
- Gather Necessary Information: Collect data on materials used, potential risks, and existing safety protocols.
- Conduct a Risk Assessment: Evaluate the likelihood and impact of potential hazards.
- Draft the Plan: Use the collected information to create a structured document, incorporating all required elements.
- Review and Revise: Have stakeholders review the draft for completeness and compliance, making necessary adjustments.
- Implement the Plan: Distribute the finalized plan to all employees and conduct training sessions.
- Regularly Update: Schedule periodic reviews of the plan to ensure it remains current and effective.
Legal Use of the Dot Security Plan Example
The legal use of the dot security plan example hinges on its compliance with relevant regulations, such as those set forth by the Department of Transportation (DOT) and the Occupational Safety and Health Administration (OSHA). An effectively executed plan can serve as a legal document that demonstrates a business's commitment to safety and compliance. This can be crucial in the event of inspections or incidents, as it provides evidence of proactive measures taken to mitigate risks.
How to Use the Dot Security Plan Example
To effectively use the dot security plan example, businesses should follow these guidelines:
- Customize the Template: Tailor the example to fit specific operational needs and regulatory requirements.
- Engage Employees: Involve staff in the development and implementation process to ensure buy-in and understanding.
- Train Regularly: Conduct ongoing training sessions to keep employees informed about safety protocols and updates to the plan.
- Monitor Compliance: Regularly check adherence to the plan and make adjustments as necessary to improve safety measures.
Examples of Using the Dot Security Plan Example
Businesses can apply the dot security plan example in various scenarios, including:
- Hazardous Material Transportation: Ensuring compliance with regulations while transporting dangerous goods.
- Workplace Safety Audits: Utilizing the plan as a guide during safety inspections and assessments.
- Emergency Drills: Implementing the plan during training exercises to prepare employees for real-life situations.
Quick guide on how to complete dot security plan example
Prepare Dot Security Plan Example effortlessly on any device
Digital document management has gained popularity among organizations and individuals. It serves as an ideal eco-friendly alternative to conventional printed and signed paperwork, allowing you to locate the right form and securely store it online. airSlate SignNow provides all the resources necessary to create, edit, and eSign your documents promptly without delays. Manage Dot Security Plan Example on any device using airSlate SignNow Android or iOS applications and streamline any document-related process today.
The easiest method to modify and eSign Dot Security Plan Example without hassle
- Obtain Dot Security Plan Example and then click Get Form to begin.
- Utilize the tools we offer to submit your document.
- Emphasize relevant sections of your documents or obscure sensitive data with tools that airSlate SignNow specifically offers for that purpose.
- Create your signature using the Sign tool, which takes seconds and carries the same legal authority as a traditional wet ink signature.
- Review all the details and then click on the Done button to save your changes.
- Choose how you would like to share your form, via email, text message (SMS), invitation link, or download it to your computer.
Eliminate concerns about lost or misplaced files, tedious form searching, or mistakes that necessitate printing new document copies. airSlate SignNow meets your document management needs in just a few clicks from any device of your preference. Modify and eSign Dot Security Plan Example and ensure superior communication at every stage of the form preparation process with airSlate SignNow.
Create this form in 5 minutes or less
Create this form in 5 minutes!
How to create an eSignature for the dot security plan example
How to create an electronic signature for a PDF online
How to create an electronic signature for a PDF in Google Chrome
How to create an e-signature for signing PDFs in Gmail
How to create an e-signature right from your smartphone
How to create an e-signature for a PDF on iOS
How to create an e-signature for a PDF on Android
People also ask
-
What is a dot security plan template?
A dot security plan template is a structured document that outlines the security measures and strategies an organization must implement to safeguard its data. It serves as a guideline for developing a comprehensive security framework and is crucial for compliance and risk management.
-
How can airSlate SignNow assist with my dot security plan template?
airSlate SignNow provides an intuitive platform that enables you to securely send, eSign, and store your dot security plan template. By using our solution, you can ensure that your documents are signed and shared efficiently while maintaining the confidentiality and integrity of your security plans.
-
What features should I look for in a dot security plan template tool?
When choosing a tool for your dot security plan template, look for features such as user-friendly eSignature capabilities, robust security measures, document tracking, and compliance with industry standards. airSlate SignNow offers all these functionalities to make your security planning seamless.
-
Is airSlate SignNow affordable for small businesses needing a dot security plan template?
Yes, airSlate SignNow offers a cost-effective solution that caters to businesses of all sizes. Our pricing plans are designed to be budget-friendly, making it easier for small businesses to create and manage their dot security plan template without incurring high costs.
-
Can I integrate airSlate SignNow with other software while using a dot security plan template?
Absolutely! airSlate SignNow seamlessly integrates with a variety of applications such as Google Drive, Microsoft Office, and more. This flexibility allows you to enhance your workflow when creating and managing your dot security plan template alongside your other business tools.
-
What are the benefits of using airSlate SignNow for my dot security plan template?
Using airSlate SignNow for your dot security plan template offers several benefits, including improved document security, faster turnaround times for signatures, and enhanced collaboration among team members. Our platform streamlines the entire process, saving you time and increasing efficiency.
-
How secure is my dot security plan template when using airSlate SignNow?
airSlate SignNow prioritizes security with industry-leading encryption protocols and compliance with regulations such as GDPR. You can trust that your dot security plan template and other sensitive documents are protected and accessible only to authorized individuals.
Get more for Dot Security Plan Example
Find out other Dot Security Plan Example
- How To Integrate Sign in Banking
- How To Use Sign in Banking
- Help Me With Use Sign in Banking
- Can I Use Sign in Banking
- How Do I Install Sign in Banking
- How To Add Sign in Banking
- How Do I Add Sign in Banking
- How Can I Add Sign in Banking
- Can I Add Sign in Banking
- Help Me With Set Up Sign in Government
- How To Integrate eSign in Banking
- How To Use eSign in Banking
- How To Install eSign in Banking
- How To Add eSign in Banking
- How To Set Up eSign in Banking
- How To Save eSign in Banking
- How To Implement eSign in Banking
- How To Set Up eSign in Construction
- How To Integrate eSign in Doctors
- How To Use eSign in Doctors