Service Authorization Form


What is the Service Authorization?
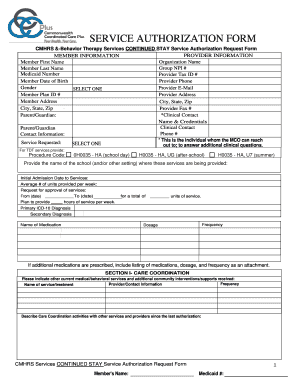
The service authorization form is a critical document used primarily in healthcare and social services to grant permission for specific services to be provided to an individual. This form ensures that the necessary approvals are in place before services are rendered, allowing providers to deliver care efficiently and in compliance with regulations. It typically includes information about the individual receiving services, the type of services requested, and the duration of authorization.
How to Obtain the Service Authorization
To obtain a service authorization, individuals or their representatives must typically contact the relevant service provider or agency. This may involve filling out an initial application or request form. In some cases, the provider may require supporting documentation, such as medical records or proof of eligibility. It is essential to follow the specific guidelines set forth by the agency to ensure a smooth approval process.
Steps to Complete the Service Authorization
Completing a service authorization form involves several key steps:
- Gather necessary information, including personal details and service requirements.
- Fill out the form accurately, ensuring all sections are completed.
- Attach any required documentation that supports the request.
- Review the form for accuracy and completeness.
- Submit the form through the designated method, whether online, by mail, or in person.
Key Elements of the Service Authorization
Understanding the key elements of a service authorization form is crucial for effective completion. These elements typically include:
- Client Information: Name, address, and contact details of the individual receiving services.
- Service Details: Description of the services requested, including frequency and duration.
- Provider Information: Name and contact information of the service provider.
- Signature: Required signatures from the client or their representative to authorize services.
Legal Use of the Service Authorization
The legal use of a service authorization form is governed by various regulations and laws, including privacy laws that protect client information. It is essential for providers to ensure that the form is completed in compliance with state and federal regulations. This includes maintaining confidentiality and obtaining informed consent from the client before services commence.
Examples of Using the Service Authorization
Service authorizations are commonly used in various scenarios, such as:
- Healthcare settings, where a patient authorizes a provider to deliver specific treatments or therapies.
- Social services, where individuals seek approval for assistance programs or support services.
- Educational environments, where parents may authorize services for their children, such as special education resources.
Quick guide on how to complete service authorization
Prepare Service Authorization effortlessly on any device
Online document management has become increasingly popular among businesses and individuals. It offers an ideal eco-friendly alternative to traditional printed and signed documents, allowing you to access the correct form and securely store it online. airSlate SignNow provides you with all the tools necessary to create, modify, and eSign your documents quickly without delays. Manage Service Authorization on any device using airSlate SignNow's Android or iOS applications and enhance any document-based procedure today.
How to modify and eSign Service Authorization with ease
- Find Service Authorization and then click Get Form to begin.
- Use the tools we provide to complete your form.
- Highlight important sections of the documents or mask sensitive information with tools that airSlate SignNow offers specifically for that purpose.
- Create your eSignature using the Sign feature, which takes just seconds and holds the same legal validity as a conventional wet ink signature.
- Review the information and then click on the Done button to save your modifications.
- Choose how you would like to send your form, by email, SMS, or invitation link, or download it to your computer.
Say goodbye to lost or misplaced documents, tedious form searching, or mistakes that require printing new document copies. airSlate SignNow fulfills your document management needs in just a few clicks from any device of your choice. Edit and eSign Service Authorization and ensure excellent communication at every stage of the form preparation process with airSlate SignNow.
Create this form in 5 minutes or less
Create this form in 5 minutes!
How to create an eSignature for the service authorization
How to create an electronic signature for a PDF online
How to create an electronic signature for a PDF in Google Chrome
How to create an e-signature for signing PDFs in Gmail
How to create an e-signature right from your smartphone
How to create an e-signature for a PDF on iOS
How to create an e-signature for a PDF on Android
People also ask
-
What is a service authorization form?
A service authorization form is a document used to formalize permission for a service to be rendered. It outlines the specifics of the service being authorized, ensuring all parties are on the same page. Using airSlate SignNow, you can easily create and sign these forms electronically.
-
How can I create a service authorization form with airSlate SignNow?
Creating a service authorization form with airSlate SignNow is simple and efficient. You can use our templates or start from scratch, adding custom fields as needed. Once your form is ready, you can invite signers to eSign it electronically.
-
Is there a cost associated with using the service authorization form feature?
Yes, there are pricing plans available for using the service authorization form feature on airSlate SignNow. Our plans are competitively priced and designed to be cost-effective for businesses of all sizes. You can choose a plan that fits your company's needs and budget.
-
What benefits does an electronic service authorization form offer?
Using an electronic service authorization form streamlines the process, reduces paperwork, and speeds up approvals. It also ensures secure storage and easy retrieval of documents when needed. With airSlate SignNow, you can enhance your workflow efficiency while maintaining compliance.
-
Can I integrate airSlate SignNow with other tools for managing service authorization forms?
Absolutely! airSlate SignNow offers integrations with various applications such as CRM systems, cloud storage, and project management tools. This allows you to streamline your processes further and manage your service authorization forms more effectively alongside your other business tools.
-
What security features does airSlate SignNow provide for service authorization forms?
airSlate SignNow prioritizes document security for all transactions, including service authorization forms. We employ encryption for data transmission and storage, as well as user authentication measures. This ensures that your critical documents remain secure and accessible only to authorized personnel.
-
Is it easy to track the status of service authorization forms sent for signing?
Yes, airSlate SignNow offers real-time tracking for all service authorization forms sent out for signatures. You can monitor who has signed, who is still pending, and receive notifications upon completion. This feature helps you manage the signing process effortlessly and stay organized.
Get more for Service Authorization
Find out other Service Authorization
- Help Me With Sign Colorado Mutual non-disclosure agreement
- Sign Arizona Non disclosure agreement sample Online
- Sign New Mexico Mutual non-disclosure agreement Simple
- Sign Oklahoma Mutual non-disclosure agreement Simple
- Sign Utah Mutual non-disclosure agreement Free
- Sign Michigan Non disclosure agreement sample Later
- Sign Michigan Non-disclosure agreement PDF Safe
- Can I Sign Ohio Non-disclosure agreement PDF
- Help Me With Sign Oklahoma Non-disclosure agreement PDF
- How Do I Sign Oregon Non-disclosure agreement PDF
- Sign Oregon Non disclosure agreement sample Mobile
- How Do I Sign Montana Rental agreement contract
- Sign Alaska Rental lease agreement Mobile
- Sign Connecticut Rental lease agreement Easy
- Sign Hawaii Rental lease agreement Mobile
- Sign Hawaii Rental lease agreement Simple
- Sign Kansas Rental lease agreement Later
- How Can I Sign California Rental house lease agreement
- How To Sign Nebraska Rental house lease agreement
- How To Sign North Dakota Rental house lease agreement