EFFECTIVE DATE:_______________________________
Identity Theft Policy
Definitions
Identifying information means any name or number that may be used, alone or
in conjunction with any other information, to identify a specific person, including:
name, address, telephone number, social security number, date of birth,
government issued driver's license or identification number, alien registration
number, government passport number, employer or taxpayer identification
number, unique electronic identification number, computer's Internet Protocol address, or routing code. Identity theft means fraud committed or attempted using the identifying
information of another person without authority.Credit means the right granted by a creditor to a debtor to defer payment of debt
or to incur debts and defer its payment or to purchase property or services and defer payment therefor. Creditor means any person who regularly extends, renews, or continues credit;
any person who regularly arranges for the extension, renewal, or continuation of credit; or any assignee of an original creditor who participates in the decision to extend, renew, or continue credit. A covered account means:
1. An account that a financial institution or creditor offers or maintains, primarily
for personal, family, or household purposes that involves or is designed to
permit multiple payments or transactions. Covered accounts include credit card
accounts, mortgage loans, automobile loans, margin accounts, cell
phone accounts, utilityaccounts, checking accounts and savings accounts; and
2. Any other account that a financial institution or creditor, or municipality, offers
or maintains for which there is a reasonably foreseeable risk to customers/users
or to the safety and soundness of the financial institution or creditor or
municipality from identity theft, including financial, operational, compliance,
reputation or litigation risks. A red flag means a pattern, practice or specific activity that indicates the
possible existence of identity theft.
IDENTIFICATION OF RED FLAGS.
The Employer identifies the following red flags, in each of the listed categories:
1. Suspicious Documentsi. Identification document or card that appears to be forged, altered
or inauthentic;ii. Identification document or card on which a person's photograph
or physical description is not consistent with the person presenting
the document;iii. Other document with information that is not consistent with
existing customer/user information (such as if a person's signature on a
check appears forged); and
iv. Direct Payment Enrollment Form that appears to be altered or forged.
2. Suspicious Personal Identifying Information i. Identifying information presented that is inconsistent with
other information the customer/user provides (example: inconsistent
birth dates);ii. Identifying information presented that is inconsistent with other
sources of information (for instance, an address not matching an address
on a credit report);
iii. Identifying information presented that is the same as information shown on other applications that were found to be fraudulent;iv. Identifying information presented that is consistent with
fraudulent activity (such as an invalid phone number or fictitious billing address);v. An address or phone number presented that is the same as that
of another person;vi. A person's identifying information is not consistent with the
information that is on file for the customer/user.
3. Suspicious Account Activity or Unusual Use of Account
i. Change of address for an account followed by a request to change
the account holder's name;ii. Payments stop on an otherwise consistently up-to-date account; iii. Account used in a way that is not consistent with prior use
(example: very high activity);iv. Mail sent to the account holder is repeatedly returned as undeliverable;v. Notice to the Employer that a customer/user is not receiving mail sent
by the Employer;
vi. Notice to the Employer that an account has unauthorized activity;
vii. Breach in the Employer‘s computer system security; and viii. Unauthorized access to or use of customer/user account information.
4. Alerts from Others
i. Notice to the Employer from a customer/user, identity theft victim,
law enforcement or other person that it has opened or is maintaining a fraudulent account for a person engaged in Identity Theft. ii. Notifications and Warnings From Credit Reporting Agencies· Report of fraud accompanying a credit report;
· Notice or report from a credit agency of a credit freeze on a customer or applicant;
· Notice or report from a credit agency of an active duty alert for an applicant; and
· Indication from a credit report of activity that is inconsistent with a customer’s usual pattern or activity.
DETECTING RED FLAGS .
1. New Accounts. In order to detect any of the Red Flags identified
above associated with the opening of a new account, personnel will take
the following steps to obtain and verify the identity of the person opening
the account: i. Require certain identifying information such as residential or
business address;ii. Independently contact the customer/user.
2. Existing Accounts. In order to detect any of the Red Flags identified above for an existing account, personnel will take the following steps to
monitor transactions with an account: i. Verify the identification of customers/users if they request information (in person, via telephone, via facsimile, via email);ii. Verify the validity of requests to change billing addresses; andiii. Verify changes in banking information, if any, given for billing
and payment purposes. Updated Direct Payment Enrollment
Form required.
PREVENTING AND MITIGATING IDENTITY THEFT.
1. Prevent and Mitigate. In the event personnel detect any identified Red Flags,
such personnel shall take one or more of the following steps, depending on the degree of risk posed by the Red Flag: i. Continue to monitor an account for evidence of Identity Theft;ii. Contact the customer/user;
iii. Change any passwords or other security devices that permit access
to accounts;iv. Not open a new account;v. Close an existing account;vi. Reopen an account with a new number;
vii. Notify the Employer (or his/her designee) for determination of
the appropriate step(s) to take;viii. Notify law enforcement; and/orix. Determine that no response is warranted under the
particular circumstances.
2. Protect customer/user identifying information. In order to further prevent the likelihood of identity theft occurring with respect to Employer accounts, the Employer will take the following steps with respect to its internal operating
procedures to protect customer/user identifying information: i. Ensure that its website is secure or provide clear notice that the website is not secure;ii. Ensure complete and secure destruction of paper documents
and computer files containing customer/user information;iii. Ensure that office computers are password protected and
that computer screens lock after a set period of time;iv. Keep offices clear of papers containing customer/user information;v. Ensure computer virus protection is up to date;
vi. Request only the last 4 digits of social security numbers (if any); andvii. Require and keep only the kinds of customer/user information that
are necessary for utility purposes.
PROGRAM ADMINISTRATION .
1. Oversight.
Responsibility for developing, implementing and updating this Program lies with
an Identity Theft Committee for the Employer. The Committee is headed by
_______________________________ (or his designee), with the _______________________________ and _______________________________ comprising the remainder of the
committee membership. _______________________________ (or his/her
designee) will be responsible for the Program administration, for ensuring
appropriate training of staff on the Program, for reviewing any staff reports
regarding the detection of Red Flags and the steps for preventing and mitigating
Identity Theft, determining which steps of prevention and mitigation should be
taken in particular circumstances and considering periodic changes to the
Program. The following will be taken into consideration: i. The experiences of the organization with identity theft;
ii. Changes in methods of identity theft;
iii. Changes in methods to detect, prevent and mitigate identity theft;iv. Changes in the types of accounts that the organization offers or maintains;
v. Changes in the business arrangements of the organization, including mergers, acquisitions, alliances, joint ventures and service provider arrangements.
After considering these factors, _______________________________ (or
his/her designee), with the assistance of _______________________________,
will determine whether changes to the Program, including the listing of Red
Flags, are warranted. If warranted, _______________________________ (or his/her designee), will present _______________________________ with
his/her recommended changes and the Board will make a determination
of whether to accept, modify or reject those changes to the Program. Oversight of the Program shall include: i. Assignment of specific responsibility for implementation of the Program to _______________________________;
ii. Review of reports prepared by staff regarding compliance; and
iii. Approval of material changes to the Program as necessary to address changing risks of identity theft.
Reports shall be prepared as follows: i. Staff responsible for development, implementation and administration of the Program shall report to _______________________________ (the governing body, an
appropriate committee of the governing body or a designated employee at the level of senior management) at least annually on compliance by the organization with the Program.
ii. The report shall address material matters related to the Program and evaluate issues such as: a. The effectiveness of the policies and procedures in addressing the risk of identity theft in connection with the opening of covered accounts and with respect to existing covered accounts;b. Service provider agreements;c. Significant incidents involving identity theft and management’s response; andd. Recommendations for material changes to the Program.
Oversight of Service Provider Arrangements In the event the Employer engages a service provider to perform an activity in
connection with one or more accounts, it will take the following steps to ensure
the service provider performs its activity in accordance with reasonable policies and procedures designed to detect, prevent, and mitigate the risk of Identity Theft:
· Require, by contract, that service providers have such policies and procedures in place; and
· Require, by contract, that service providers review the Employer’s Program and report any Red Flags to the Program Administrator. 2. Staff Training And Reports.
Staff responsible for implementing the Program shall be trained either by or under the direction of _______________________________ (or his/her
designee) in the detection of Red Flags, and the responsive steps to be taken
when a Red Flag is detected. Staff is required to provide reports to the Program
Administrator on incidents of Identity Theft, the Employer’s compliance with the Program and the effectiveness of the Program. The Program shall train staff, as necessary, to effectively implement the
Program; and the Program shall exercise appropriate and effective oversight of service provider arrangements. 3. Duties Regarding Address DiscrepanciesThe Employer shall develop policies and procedures designed to enable the organization to form a reasonable belief that a credit report relates to the consumer for whom it was requested if the organization receives a notice of address discrepancy from a nationwide consumer reporting agency indicating the
address given by the consumer differs from the address contained in the consumer report.
The Employer may reasonably confirm that an address is accurate by any of the following means:i. Verification of the address with the consumer;ii. Review of the utility’s records;iii. Verification of the address through third-party sources; oriv. Other reasonable means.
If an accurate address is confirmed, the Employer shall furnish the consumer’s address to the nationwide consumer reporting agency from which it received the notice of address discrepancy if:
i. The organization establishes a continuing relationship with the consumer; andii. The organization, regularly and in the ordinary course of business,
furnishes information to the consumer reporting agency.
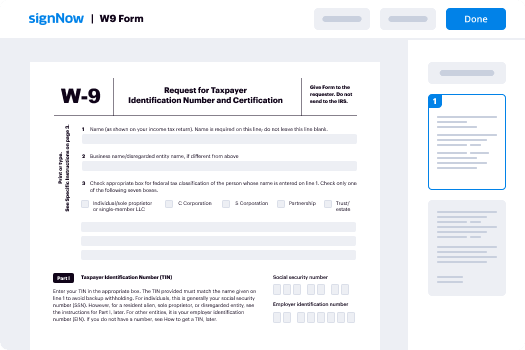
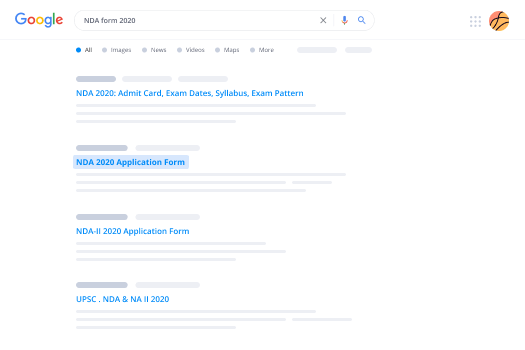
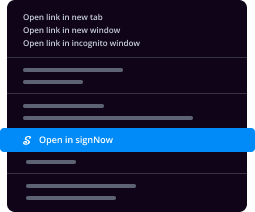
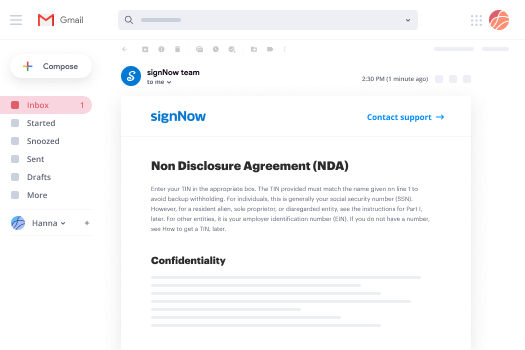
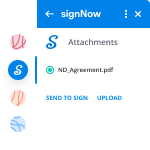
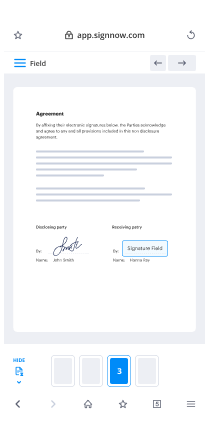
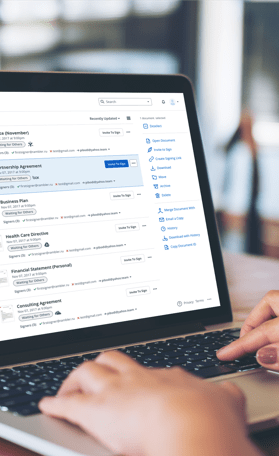
Valuable tips on preparing your ‘Identity Theft Detection Prevention And Mitigation Program ’ online
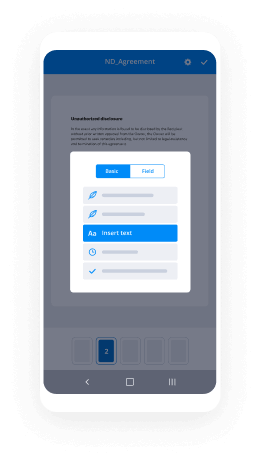
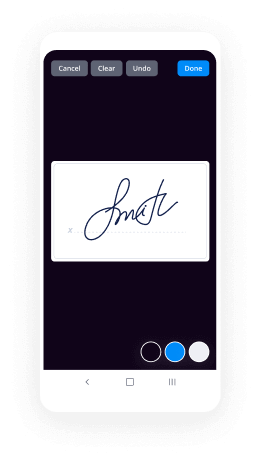
Are you fed up with the inconvenience of dealing with paperwork? Look no further than airSlate SignNow, the leading eSignature solution for individuals and businesses. Bid farewell to the monotonous procedure of printing and scanning documents. With airSlate SignNow, you can effortlessly finish and sign forms online. Leverage the robust features integrated into this user-friendly and cost-effective platform and transform your method of handling paperwork. Whether you need to approve forms or collect signatures, airSlate SignNow manages everything effortlessly, requiring just a few clicks.
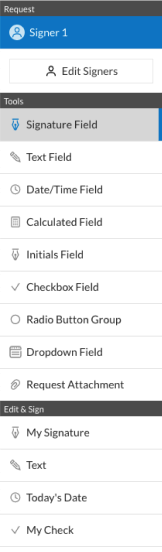
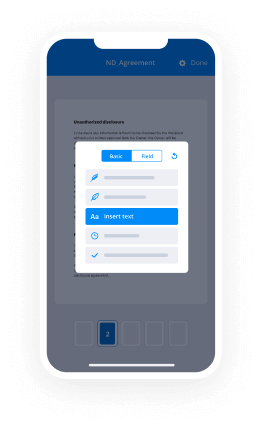
Adhere to this comprehensive guide:
- Log in to your account or register for a complimentary trial with our service.
- Click +Create to upload a file from your device, cloud storage, or our template repository.
- Open your ‘Identity Theft Detection Prevention And Mitigation Program ’ in the editor.
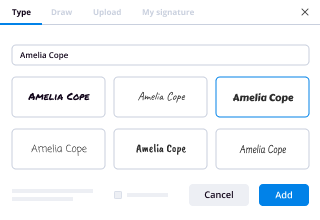
- Click Me (Fill Out Now) to prepare the document on your behalf.
- Add and allocate fillable fields for others (if needed).
- Proceed with the Send Invite options to request eSignatures from others.
- Save, print your version, or convert it into a reusable template.
Rest assured if you need to collaborate with your colleagues on your Identity Theft Detection Prevention And Mitigation Program or submit it for notarization—our solution has you covered with everything necessary to accomplish those tasks. Sign up with airSlate SignNow today and elevate your document management to new levels!