Certificado De Encabezado Dividido. Use Herramientas De Firma Electrónica Que Funcionan Donde Usted Trabaja.
Mejore su flujo de trabajo de documentos con airSlate SignNow
Flujos de trabajo de firma electrónica versátiles
Visibilidad rápida sobre el estado del documento
Configuración de integración fácil y rápida
Certificado de encabezado dividido en cualquier dispositivo
Registro de auditoría avanzado
Normas de seguridad estrictas
Vea las firmas electrónicas de airSlate SignNow en acción
Soluciones de airSlate SignNow para una mayor eficiencia
Las reseñas de nuestros usuarios hablan por sí mismas






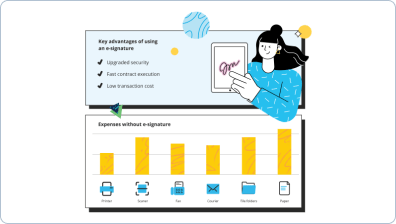
Por qué elegir airSlate SignNow
-
Prueba gratuita de 7 días. Elige el plan que necesitas y pruébalo sin riesgos.
-
Precios honestos para planes completos. airSlate SignNow ofrece planes de suscripción sin cargos adicionales ni tarifas ocultas al renovar.
-
Seguridad de nivel empresarial. airSlate SignNow te ayuda a cumplir con los estándares de seguridad globales.

Tu guía paso a paso — split header certificate
Certificado de encabezado dividido. Obtenga el máximo beneficio del sistema de firma electrónica más confiable y seguro. Mejore sus transacciones electrónicas empleando airSlate SignNow. Optimice los flujos de trabajo para todo, desde registros simples de empleados hasta acuerdos complejos y plantillas de pago.
Aprenda cómo dividir el certificado de encabezado:
- Suba varios documentos desde su computadora o almacenamiento en la nube.
- Arrastre y suelte campos rellenables inteligentes (firma, texto, fecha/hora).
- Cambie el tamaño de los campos, tocándolos y seleccionando Ajustar tamaño.
- Coloque casillas de verificación, listas desplegables y grupos de botones de opción.
- Agregue firmantes y cree la solicitud de adjuntos.
- Certificado de encabezado dividido.
- Incluya la fórmula donde necesita que aparezca el campo.
- Agregue comentarios y anotaciones para los destinatarios en cualquier parte de la página.
- Apruebe todas las modificaciones haciendo clic en HECHO.
Conecte personas dentro y fuera de su empresa para acceder electrónicamente a signNowwork esencial y al certificado de encabezado dividido en cualquier momento y en cualquier dispositivo usando airSlate SignNow. Puede rastrear cada acción realizada en sus muestras, recibir notificaciones y un informe de auditoría. Manténgase enfocado en su negocio y en las interacciones con los clientes mientras sabe que sus datos son precisos y seguros.
Cómo funciona
Funciones de airSlate SignNow que los usuarios adoran
Vea resultados excepcionales Certificado de encabezado dividido. Use herramientas de firma electrónica que funcionan donde usted trabaja.
¡Obtenga firmas legalmente vinculantes ahora!
Preguntas frecuentes
-
¿Qué es SSL split?
SSLsplit es una herramienta para ataques de hombre en el medio contra conexiones de red cifradas SSL/TLS. ... Para conexiones SSL y HTTPS, SSLsplit genera y firma certificados X509v3 falsificados en tiempo real, basados en el DN del sujeto del certificado original y la extensión subjectAltName. -
¿Cómo funciona SSL MITM?
Funcionan enviando al cliente un certificado SSL creado en tiempo real con los detalles copiados del certificado SSL "real", pero firmado con una cadena de certificados diferente. Si esta cadena termina en alguna de las CA confiables del navegador, este MITM será invisible para el usuario. -
¿Cómo funciona un ataque MITM?
En criptografía y seguridad informática, un ataque de hombre en el medio (MITM) es un ataque donde el atacante retransmite y posiblemente altera las comunicaciones entre dos partes que creen que están comunicándose directamente entre sí. -
¿Cómo previene SSL al hombre en el medio?
SSL prev
Lo que dicen los usuarios activos — split header certificate
Preguntas frecuentes
¿Cómo firmo una página en un PDF y la envío de vuelta?
¿Cómo puedo agregar un espacio de firma (campo) a mi PDF para poder firmarlo?
¿Cómo firmar documentos escaneados electrónicamente?
Obtén más para split header certificate
- Beneficios de airSlate SignNow CRM vs. Freshsales CRM para Investigación y Desarrollo
- Beneficios de airSlate SignNow CRM vs. Freshsales CRM para gestión
- Beneficios de airSlate SignNow CRM vs. Freshsales CRM para Administración
- Beneficios de airSlate SignNow CRM vs. Freshsales CRM para Atención al Cliente
- Beneficios de airSlate SignNow CRM vs. Freshsales CRM para soporte al cliente
- Beneficios de airSlate SignNow CRM vs. Freshsales CRM para Soporte Técnico
- Beneficios de airSlate SignNow CRM vs. Freshsales CRM para Marketing
- Beneficios de airSlate SignNow CRM vs. Freshsales CRM para logística
Todo sobre la firma electrónica

Descubre otros split header certificate
- Desbloqueando la legitimidad de la eSignature para la ...
- Legalidad de la Firma Digital para el Comercio ...
- Asegurando la Legalidad de la Firma Digital para la ...
- Legalidad de la Firma Digital para la Industria de ...
- Comprendiendo la Legalidad de las Firmas Digitales para ...
- Asegurando la Legalidad de la Firma Digital para la ...
- Legitimidad de la Firma Digital para el Gobierno en el ...
- Desbloquea el Poder de la Legitimidad de la Firma ...
- Impulsando la Legitimidad de la Firma Digital para la ...
- Desbloqueando la Legitimidad de la Firma Digital para ...
- Licitud de firma digital para servicios financieros en ...
- Desbloquea el Poder de la Licitud de Firma Digital para ...
- Legalidad de la Firma Electrónica para Hipotecas en ...
- Legalidad de la Firma Electrónica para Contabilidad y ...
- Asegurando la Legalidad de la Firma Electrónica para ...
- Asegurando la Legitimidad de la Firma Electrónica para ...
- Desbloquea el Poder de la Legitimidad de la Firma ...
- Aumenta la Legitimidad de la Firma Electrónica para ...
- Legitimidad de la Firma Electrónica para Bienes ...
- Maximiza la Legitimidad de la Firma Electrónica para ...













































