Importer Des Documents Depuis Un E-mail Avec SignNow
Comment configurer l'authentification par téléphone avec airSlate SignNow
Assurez-vous que vos documents sont signés uniquement par des parties autorisées. Avec l'authentification par appel téléphonique, vos destinataires ne pourront signer vos documents qu'après avoir reçu un appel téléphonique automatisé à leur numéro.
Personnalisez votre invitation au signataire
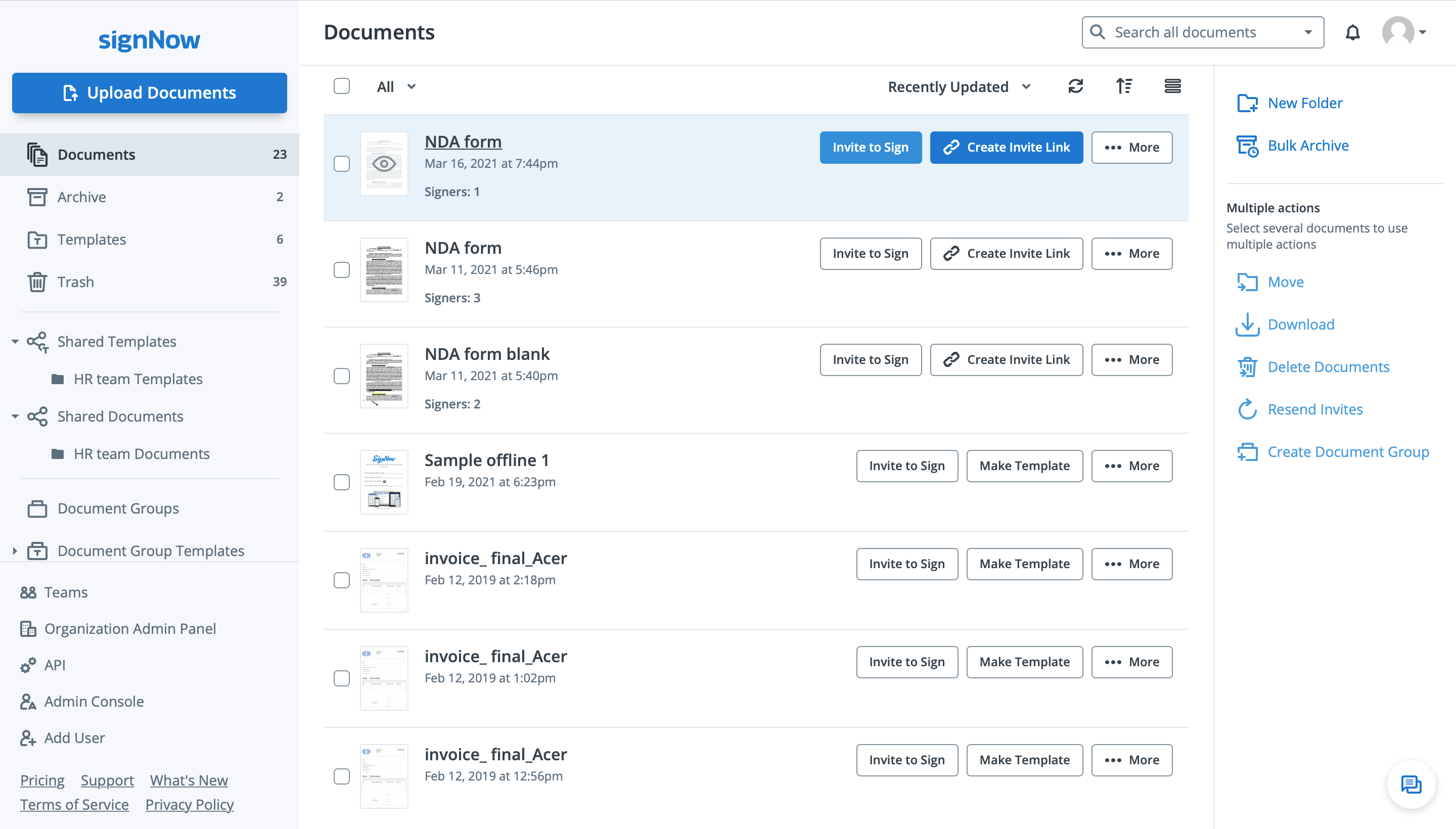
Cliquez sur Inviter à signer à côté d'un document que vous devez envoyer pour la signature électronique.
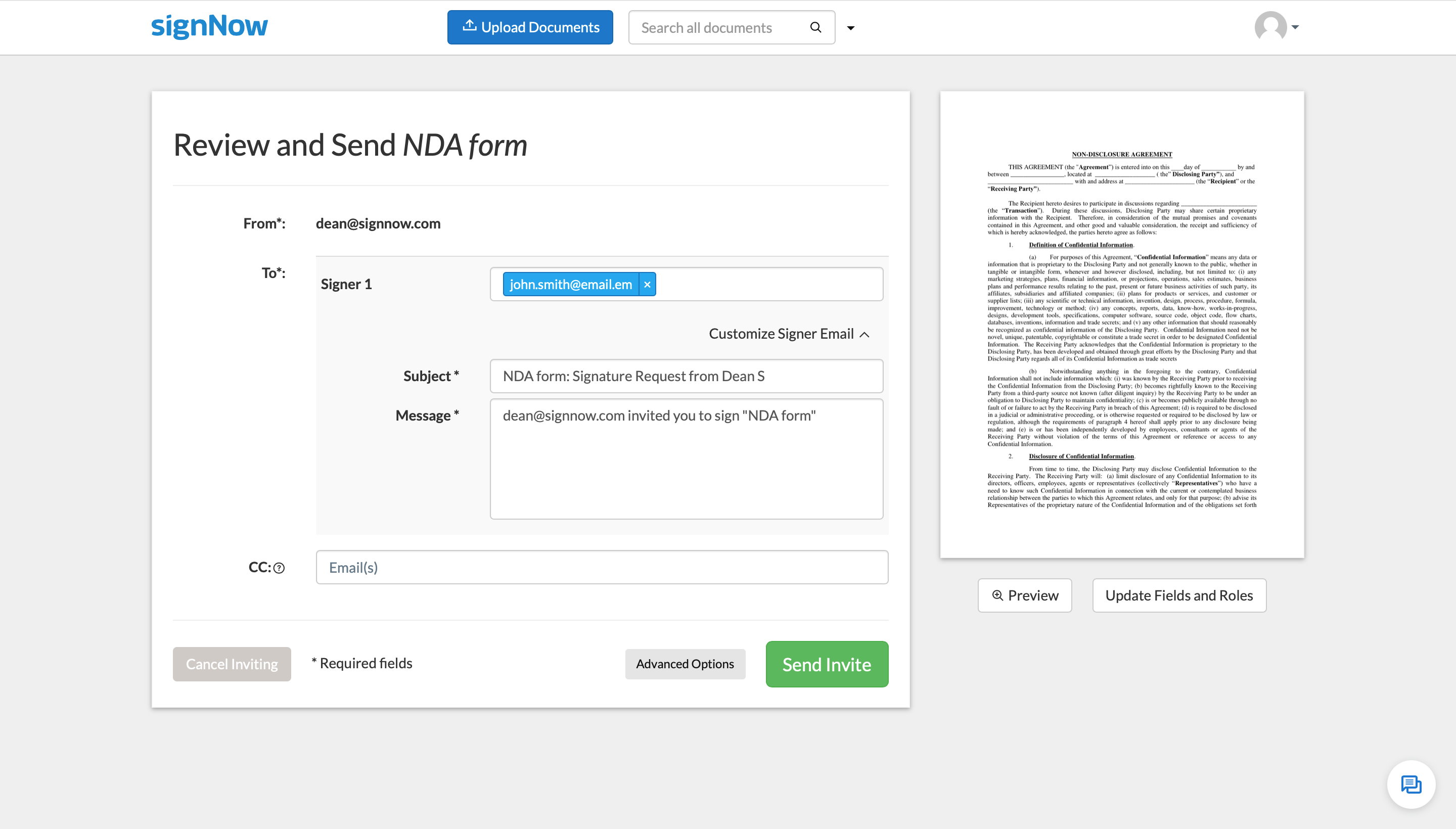
Entrez l'adresse e-mail de votre signataire et personnalisez le sujet et le message de l'invitation. Ajoutez des destinataires en copie carbone (CC) si vous souhaitez que d'autres parties reçoivent des copies signées de votre document. Ensuite, cliquez sur Options avancées.
Configurer l'authentification à deux facteurs
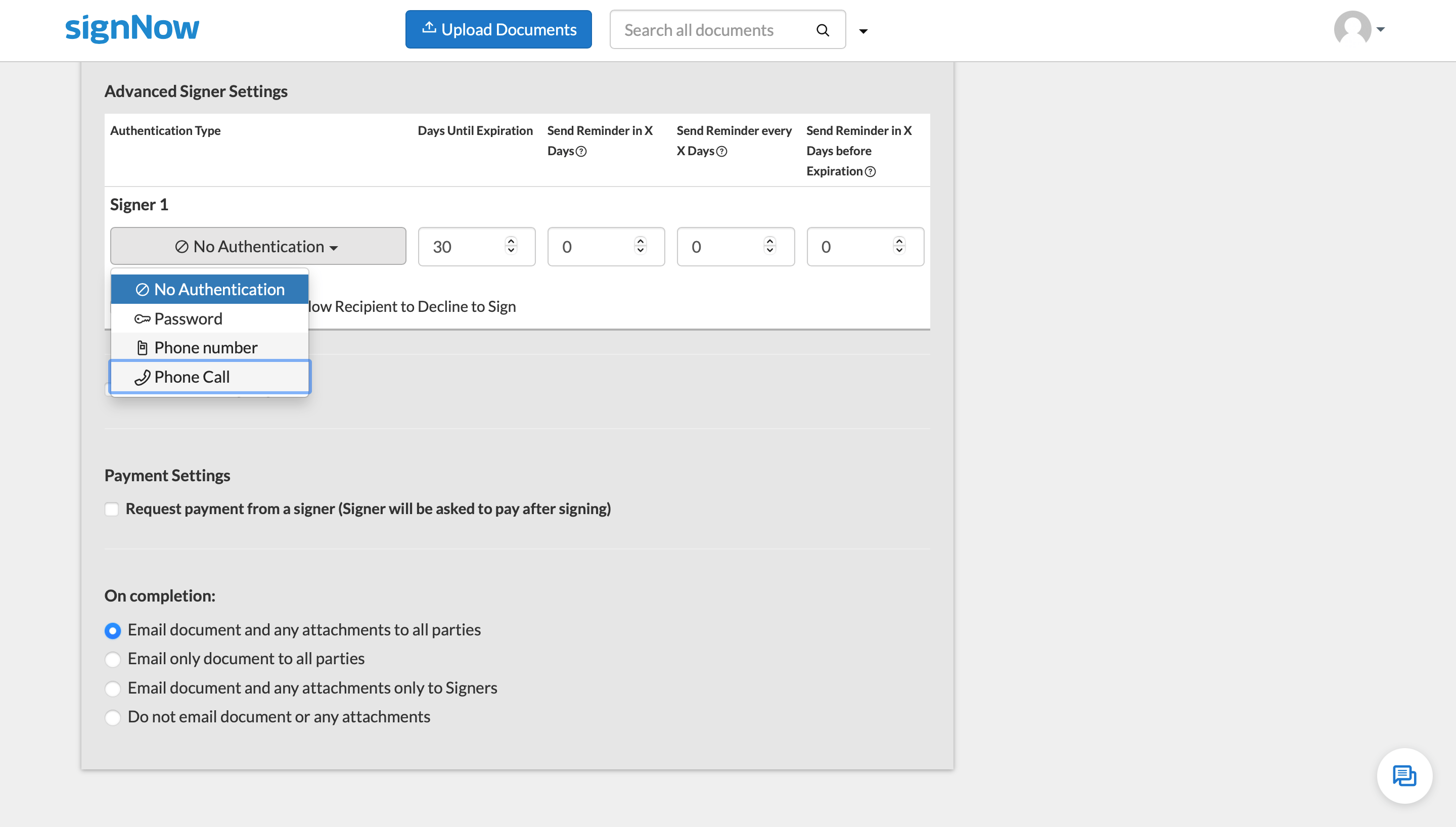
Dans la section Paramètres avancés du signataire, cliquez sur le menu déroulant Aucune authentification et sélectionnez Appel téléphonique.
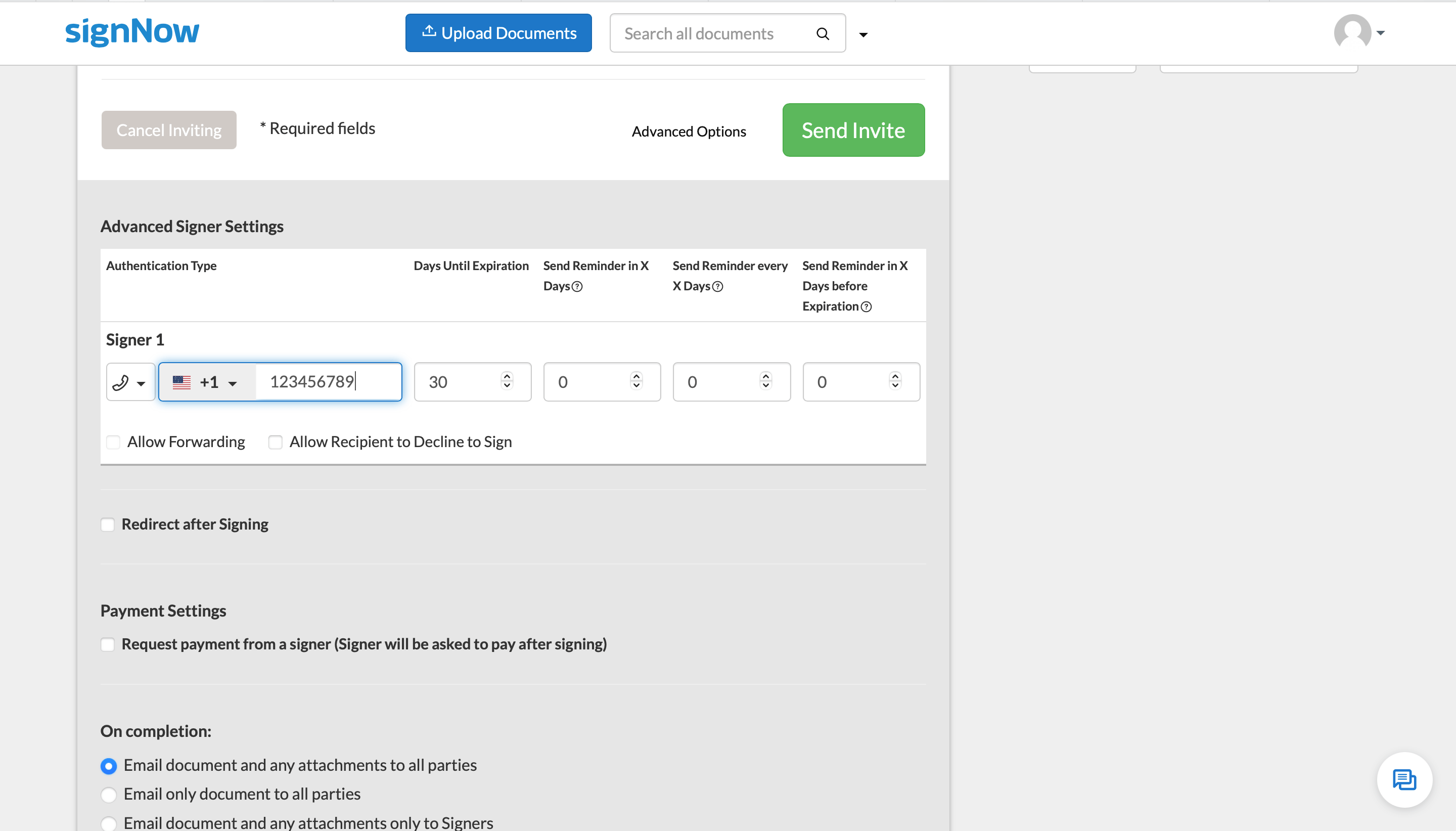
Entrez le numéro de téléphone de votre signataire et définissez la date d'expiration du document. Vous pouvez également planifier des rappels pour le signataire afin de vous assurer que votre document est signé à temps. Une fois terminé, cliquez sur Envoyer l'invitation pour envoyer votre demande de signature.
Découvrez les signatures électroniques airSlate SignNow en action
Choisissez une meilleure solution
Déléguez la paperasserie routinière à airSlate SignNow
Solution de signature en ligne
Créateur de modèles remplissables
Modèles de documents
API de signature électronique
Intégrations natives d'applications
Capacité à configurer l'authentification par appel téléphonique
Les avis de nos utilisateurs parlent d'eux-mêmes






Solutions airSlate SignNow pour une meilleure efficacité
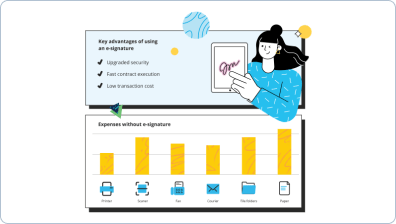
Pourquoi choisir airSlate SignNow
-
Essai gratuit de 7 jours. Choisissez le forfait dont vous avez besoin et essayez-le sans risque.
-
Tarification honnête pour des forfaits complets. airSlate SignNow propose des abonnements sans frais supplémentaires ni frais cachés lors du renouvellement.
-
Sécurité de niveau entreprise. airSlate SignNow vous aide à respecter les normes de sécurité mondiales.

Votre guide étape par étape — set phone call authentication
L'avantage conceptuel principal de la plateforme de signature électronique airSlate SignNow pour l'automatisation des entreprises est un seul champ de données qui dépasse l'entreprise mais affiche un flux de travail commercial distinctif. Vous pouvez sécuriser les fichiers avec des ID de document uniques pour signer en toute sécurité, donner un lien d'invitation à vos partenaires, distributeurs ou coéquipiers. Notre plateforme avancée simplifie les étapes analytiques et d'audit. Elle vous permet de contrôler le flux de travail de manière plus flexible sans impliquer du personnel externe. Vous pouvez indirectement améliorer l'interaction entre partenaires et leur permettre d'augmenter l'expérience client.
Comment sécuriser les fichiers avec des ID de document uniques pour signer en toute sécurité avec airSlate SignNow :
- Créez votre nom d'utilisateur et mot de passe gratuitement ou connectez-vous si vous en avez déjà un.
- Vous pouvez vous connecter avec la fonction Single sign-on si vous possédez le profil airSlate SignNow.|Si vous avez le compte airSlate SignNow, vous pouvez vous connecter en utilisant la fonction Single sign-on
- Transférez le fichier de données depuis votre appareil portable ou votre ordinateur de bureau.
- Alternativement, vous pouvez télécharger le fichier requis depuis votre stockage cloud. Notre plateforme en ligne fonctionne avec les dépôts les plus recommandés : Google Drive, OneDrive, DropBox.
- Modifiez facilement votre modèle avec l'éditeur PDF innovant mais facile à utiliser.
- Tapez le contenu textuel, ajoutez des graphiques, laissez vos annotations ou remarques, etc..
- Vous pouvez configurer des éléments remplissables de divers types : texte ou date spécifique, calculé ou déroulant, et bien plus encore.
- Organisez et mettez en place la pièce jointe requise.
- Insérez le champ de signature pour l'envoi à signer et recueillir des signatures en personne ou multiples. Vous pouvez signer vous-même le modèle si nécessaire.
- Complétez la modification avec le bouton Terminé et commencez à sécuriser les fichiers avec des ID de document uniques pour signer en toute sécurité.
airSlate SignNow est la première solution pour l'automatisation des processus d'entreprise et la sécurisation des fichiers avec des ID de document uniques pour signer en toute sécurité et réaliser rapidement des tâches pour des entreprises de tous niveaux, employés et complexité. Les utilisateurs peuvent interagir à la fois en interne et en externe avec des fournisseurs et des consommateurs. Essayez toutes les fonctionnalités dès maintenant!
Comment ça marche
Découvrez des résultats exceptionnels Importer des documents depuis un e-mail avec signNow
Obtenez des signatures juridiquement contraignantes dès maintenant !
FAQ
-
Est-il sécurisé d'envoyer des documents pour signature via airSlate SignNow?
Oui. En plus des protocoles de cryptage avancés pour le stockage et la transmission des données maintenus par airSlate SignNow, vous pouvez également ajouter une couche supplémentaire de protection à tout document que vous envoyez. Par exemple, les utilisateurs peuvent activer l'authentification du signataire par mot de passe, numéro de téléphone ou appel téléphonique. -
Est-il sûr de stocker et gérer mes documents dans airSlate SignNow?
Absolument! airSlate SignNow maintient une sécurité de niveau industriel et garantit que vos données sont stockées et partagées en toute sécurité conformément au HIPAA, GDPR, 21 CFR Part 11, PCI DSS, SOC 2 Type II. -
Qu'est-ce que l'authentification à deux facteurs?
L'authentification à deux facteurs vous permet de protéger vos documents contre tout accès non autorisé et de vous assurer qu'ils sont signés par les bonnes personnes. Avec airSlate SignNow, vous pouvez authentifier les signataires par mot de passe, numéro de téléphone ou appel téléphonique. -
Comment envoyer un document pour une signature électronique?
Téléchargez un document sur airSlate SignNow et ouvrez-le dans l'éditeur. Sélectionnez Champ de signature dans la barre latérale gauche et cliquez n'importe où sur le document pour y placer un champ de signature. Ensuite, cliquez sur Inviter à signer en haut à droite de l'écran, entrez l'adresse e-mail du destinataire, et cliquez sur Envoyer l'invitation. -
Qu'est-ce qu'une copie carbone (CC) d'un document?
Une copie carbone est une copie signée d'un document que vous pouvez envoyer automatiquement aux parties concernées. Lors de l'envoi de documents pour signature avec airSlate SignNow, entrez les adresses e-mail de vos destinataires en copie carbone, et tous recevront leur copie une fois le document signé. -
Puis-je modifier la date d'expiration d'un document après l'avoir envoyé?
Oui, cliquez sur l'adresse e-mail du signataire sous le nom d'un document envoyé, puis sélectionnez Modifier l'expiration dans le menu déroulant. -
Comment puis-je définir un rappel pour que les signataires terminent mon document?
Lors de l'envoi de vos documents pour signature, cliquez sur Options avancées en bas du formulaire de départ. Vous trouverez les paramètres de rappel dans la section Paramètres avancés du signataire ci-dessous.
Ce que disent les utilisateurs actifs — set phone call authentication
Questions fréquemment posées
Comment générer un document et y appliquer une signature électronique ?
Comment ajouter une signature électronique à un document Word ?
Comment signer un PDF en ligne ?
Obtenez plus pour set phone call authentication
Tout savoir sur la signature électronique

Découvrez d'autres set phone call authentication
- Ajoutez facilement une signature électronique à ...
- Comment utiliser Google Docs pour signer des documents ...
- Comment ajouter une signature numérique à un ...
- Découvrez des solutions de signature électronique ...
- Découvrez notre solution de signature conforme à la ...
- Connexion de signature en ligne sans effort pour une ...
- Mettre une signature électronique sur Google Doc ...
- Découvrez le créateur de signatures en tamoul qui ...
- Modèle de signature HTML pour des signatures ...










































