A signature has gone through many changes throughout history – from pictographic script to its present electronic form. Yet, its purpose has remained the same. For centuries, people used signatures to verify a source of writing and prove the intent of concluding an agreement or stating a point. A written signature served as the only way to confirm the identity of a signer (very unreliable at times). Lack of other authentication methods left plenty of room for document falsification and forgery.
Over time, the advances in technology made it possible to implement rudimentary forms of electronic signatures. In 1869, the New Hampshire Supreme Court in the United States accepted an eSignature sent via telegraph for the first time. In the 1980s, faxed signatures were deemed legally enforceable in administrative and legal proceedings nationwide. Fast forward to the late 1990s, the surge in e-commerce demanded the adoption of a legal framework governing the use of electronic signatures. Online business transactions had to become more efficient while also ensuring security for customers.
The Uniform Electronic Transactions Act (UETA) adopted in 1999 was the precursor to the ESIGN Act. It established the legal compliance of electronic records and signatures to their paper-based equivalents, thus facilitating e-commerce. The adoption of the ESIGN Act was only a matter of time, as over 40 US states had already been using electronic signatures in their business transactions.
In what year was the ESIGN law passed by the federal government?
The Electronic Signatures in Global and National Commerce Act (ESIGN Act) was passed on June 30, 2000. President Bill Clinton signed the bill into federal law using both wet ink and a smart card with his electronic signature encrypted. Twenty years later, the e signature market annual growth rate of 22.52% speaks volumes as to how important this technology has become. When it comes to the US legal framework governing the use of electronic signatures, it’s crucial to distinguish between the UETA and the ESIGN Act.
The ESIGN Act and UETA contain similar requirements validating the use of eSignatures:
- No electronic record or signature may be denied legal effect because of its electronic form.
- The signers have to give their consent to perform business transactions by electronic means.
- The signers must show a clear intent to eSign a document.
- An eSignature must be logically associated with the record.
- Electronic records must be capable of being retained and accurately reproduced.
The differences between UETA and the ESIGN Act:
|
The ESIGN Act
|
UETA
|
|
Federal law
|
State law, with jurisdiction in 47 US states, Puerto Rico, the Virgin Islands, and the District of Columbia.
|
|
Sets the guidelines for eSignatures, contracts, or other records within foreign and interstate commerce.
|
Governs only electronic records and signatures related to business, commercial, and governmental matters.
|
- Does not recognize oral communications as the purpose of eSignatures.
- Sets the limitations to the regulatory authority.
- Defines the status of transferable records.
|
- Regulates the attribution and effect of electronic records.
- Stipulates the time and place of sending messages.
- Makes the law of mistake applicable to resolve conflicts.
- Deems e-records admissible as court evidence.
|
What is the purpose of the ESIGN Act?
The ESIGN Act is a federal law that governs the use of electronic signatures in domestic interstate and foreign commerce. Section 101(a) spells out the general purpose of the Act – to prevent the denial of validity, enforceability, and legal standing of an eSigned document because of its electronic form. In other words, eSignatures and electronic records are deemed as legally valid as their paper-based counterparts.
What is ESIGN consent?
The ESIGN Consumer Disclosures stipulate the protection of information in electronic records. Section 101(c) requires institutions to get consent or confirmation from consumers before transmitting electronic information that a law requires to be in writing. Institutions must inform consumers of the rights and options they have in a clear and conspicuous statement. The consumer consent provisions indicate that consumers must be informed about:
- the option of having an electronic record provided in a paper copy or non-electronic form;
- ways to request a paper copy of a record and learn if any fee will be charged for that copy;
- the right to withdraw consent, including any conditions, consequences, and fees in the event of such withdrawal;
- the procedures used to withdraw consent and update information needed to contact the consumer electronically;
- the right to know whether the consent relates to a particular transaction or a broader range of records that may be provided in the course of the parties’ relationship.
Hardware and software requirements
Section 101(c) indicates that consumers must be informed about the hardware and software requirements needed to access and retain electronic records. If a consumer consents electronically, they must be able to access the information that subsequently will be used to provide knowledge related to the subject of the consent.
If a change in the hardware or software requirements creates a material risk that will make it impossible for the consumer to access and retain electronic records subject to the consent, an institution must:
- provide the consumer with a statement of the revised hardware and software requirements for access to and retention of electronic records;
- the right to withdraw consent without the imposition of any fee, condition, or consequence for such withdrawal.
After the statement is provided, an institution must request consumer consent once again.
Retention of contracts and records
Section 101 (d) contains provisions stipulating the retention of electronic contracts and records:
- electronic records must accurately reflect the information contained in the equivalent paper contracts, notices, or disclosures;
- electronic records must remain accessible to all parties for the period required by law;
- institutions must ensure that electronic records can be accurately reproduced for later reference.
The agreements concluded with consumers before October 1, 2000, are exempt from the requirements of the record retention provisions. However, any agreements with new or existing customers concluded on or after October 1, 2000, will fall under the Consumer Disclosures and requirements outlined in other regulations.
What does the ESIGN Act not cover?
Certain types of transactions are not subject to the ESIGN Act, as they fall under a specific legal framework. According to the U.S. Department of Commerce report, only state law governs if eSignatures and electronic records related to the ESIGN exceptions are deemed as legally valid and effective as paper documents.
The ESIGN consumer protection provisions govern the area of routine business interactions. Still, when it comes to highly personal and financial matters such as mortgage foreclosures or inheritance, protective mechanisms are underdeveloped. In case there’s a risk of loss or damage to personal interests, consumers choose to rely on paper-based workflows, which makes electronic transactions inapplicable.
As a form of consumer protection, Section 103 of the ESIGN Act contains the nine exceptions from the General Validity rule. These transactions do not imply any interactions in a commercial setting between consumers and companies. At that, each transaction not subject to the ESIGN Act is governed by state law partly or entirely.
The ESIGN exceptions below are specific contracts and records governed by laws and regulations in the following areas:
- wills and donative documents (codicils, testamentary trusts);
- adoption, divorce agreements, and other matters of family law;
- court orders, notices, or official court documents (briefs, pleadings, and other writings);
- contracts governed by the Uniform Commercial Code;
- notices of utility services cancellation or termination;
- notices of default, acceleration, repossession, foreclosure, or eviction regarding primary residence;
- notices for termination of health or life insurance benefits;
- recall notices of a product that risks endangering health or safety;
- documentation for transportation or handling of hazardous or toxic materials and pesticides.
Where the ESIGN Act is the only law applicable to the transaction, electronic documents in these nine areas are exempt from it, thus losing their legal effect.
Electronic signature laws around the world
Over sixty countries in the world have legal frameworks governing the use of electronic signatures and records. As the number of economies adopting eSignature laws and regulations is increasing, in many aspects this legislation is still imperfect. Take a look at the list of prominent electronic signature laws around the world:
- The United States - The Uniform Electronic Transactions Act (UETA, 1999) and the Electronic Signatures in Global and National Commerce Act (ESIGN, 2000).
UETA is a state law that protects the legal enforceability of electronic records and signatures related to business, commercial, and governmental affairs.
The ESIGN Act is a federal law that sets the guidelines for eSignatures and electronic records within foreign and interstate commerce.
The use of electronic signatures in the UK is subject to the Electronic Signatures Regulations (2002) and the Electronic Signatures Directive (1999) of the EU. In a very general sense, the UK law views an eSignature as any form of electronic data attached to or associated with another item of electronic data.
he PIPEDA protects the privacy and security of consumer data. The law aims to promote e-commerce interactions with businesses in the private sector. The PIPEDA prohibits the use of eSignatures for highly personal and financial affairs such as wills, real estate deals, power of attorney, etc.
The ETA facilitates the use of eSignatures in commercial transactions and ensures their legal validity and enforceability. The use of electronic signatures is forbidden for migration or citizenship workflows. Also, in some regions, electronic signatures are impossible to use for the power of attorney, wills, and real estate contracts.
The eIDAS law regulates the use of electronic signatures and records in the EU and its tiered jurisdictions. It specifies three types of electronic signatures - Simple Electronic Signature, Advanced Electronic Signature, and Qualified Electronic Signature and recognizes them as legally valid. The signatories are free to select the eSignature fit for the type of document and the nature of their business.
The Electronic Signature Law of the PRC, later the amended eSignature Law, recognizes eSignatures as legally valid for civil contracts. In some proceedings, it is advisable to use longhand signatures for sensitive documents. China prohibits the use of electronic signatures for documents related to personal affairs, real estate transactions, public utilities suspension.
The IT Act aimed to address the concerns of foreign businesses conducting electronic transactions within India. The law recognizes electronic records and signatures as legally valid and has consumer consent recommendations. In 2006 and 2008, the initial legal framework was amended. India prohibits the use of eSignatures for the power of attorney, wills, or real estate deals. The IT Act also defines the scope of transactions that require completion on officially stamped paper.
What’s the difference between an electronic and digital signature?
When it comes to certifying electronic records, the terms “electronic signature” and “digital signature” are often used interchangeably. However, these are two different concepts with regard to tracking and legal validity. The mistake stems from misunderstanding the differences in the functions and features that digital and electronic signatures have. Before we move on, both of these definitions need clarification.
- A digital signature is a mathematical technique used to validate a message or confirm the authenticity and integrity of a digital document. A valid digital signature ensures that the document was created by a known sender, and was not modified in transit.
- An electronic signature (eSignature) is an electronic sound, symbol, or process, attached to or associated with a document used by a person with the intent to sign it. As long as it complies with the applicable laws and regulations, an electronic signature has the same legal standing as a hardcopy signature.
What is a digital signature?
Since a digital signature is essentially a mathematical algorithm, it does not have a material representation. It is often referred to as a “virtual fingerprint” – unique to a person or institution – used to identify the source of a digital message or record and secure the information in it. Compared to electronic signatures, digital signatures are significantly more secure due to the use of cryptography.
Each digital signature is one-of-a-kind for a document and its signer, which makes it difficult to falsify. Hence, digital signatures provide additional proof of the origin and status of an electronic record and indicate the consent given by the signer. The use of digital signatures allows for transparency and confidence in online interactions between businesses, contractors, and customers.
Are digital signatures secure?
The concept of a digital signature was introduced by Whitfield Diffie and Martin Hellman in 1976. Later, in 1979, Leslie Lamport constructed the Lamport one-time signature scheme that used cryptographic hash functions. The ideas of public-key cryptography (PKC) and digital signatures are still the foundation for the most regularly-used security protocols on the internet today.
To understand how digital signatures work, we need to look into the principles of hash functions and PKC:
- Hash function, or “hash” is a fixed-length string of characters generated using a mathematical algorithm and sized into a file or other type of data. Each generated string is a one-way function unique to a specific hashed file. In the event you come across a new hash, it will be impossible to decipher the input data it represents.
- A hash value is an output returned by a hash function. Hash values represent large amounts of data as much smaller numeric values which makes them fit to use with digital signatures. Hash values help to verify the integrity of data transferred via insecure channels. Any modifications to the input data made accidentally or on purpose result in a completely different hash value.
- Public key cryptography (asymmetric encryption) is a cryptographic method that uses public and private keys in pairs to encrypt and decrypt data. Public key cryptography ensures authenticity, integrity, and safety of transferred data.
- Public key infrastructure (PKI) is a set of roles, policies, procedures, and systems needed to administer digital certificates and manage the public-key encryption. PKI supports the distribution of public keys and facilitates the identity validation of individuals or institutions with digital certificates and a certificate authority.
- A certificate authority (CA) is an entity empowered to issue digital certificates. A CA acts as a trusted third-party validating the identity of a document owner. A certificate authority either generates a key pair on behalf of an individual or associates an existing key provided by the individual to its holder. Once a CA verifies someone's identity, they issue a digital certificate that can be used to verify an individual associated with a public key when requested.
- A digital certificate is an electronic “password” used to identify the certificate holder. Digital certificates allow individuals and institutions to transfer data online securely with the help of the public key infrastructure. Digital Certificates are also referred to as “public key certificates” or “identity certificates”.
- Pretty Good Privacy (PGP) is a cryptographic algorithm used for sending encrypted emails and encrypting sensitive files. Pretty Good Privacy also works for digital signatures. A user signs an encrypted message with their private key, thus providing a way for the recipient to check if the message has been modified. If any part of the message got modified before decryption, the signature will become invalid. In cryptography, this concept is referred to as the “web of trust”.
The protection of a user’s private key is crucial to keeping a digital signature secure. The use of PKI, PGP, or other applicable cryptographic algorithms eliminates the possibility of a security breach. PGP and/or PKI are essential to validating a user's identity, making a corrupted key impossible to revoke. Alternatively, this may result in stealing another user’s digital identity and other malpractices.
How do digital signatures work?
Now that you know the key concepts of a digital signature, let’s take a closer look at how it works. Here is the sequence of steps needed to generate a digital signature:
- Use a hash algorithm to generate a hash value of the document.
- Generate a unique pair of public and private keys.
- Encrypt the hash value generated earlier.
- Store the digital certificate associated with the key pair on your device.
To put it simply, a digital signature is a digital code attached to a document or message. After being generated, this digital code serves as proof that the message hasn’t been altered on its way from the sender to the recipient. Modifying any part of a document – on purpose or by accident – changes the hash value entirely.
Once the encryption procedure ends, the sender signs the document using their digital signature and sends it to the recipient. To decrypt the sender’s hash attached to the document, the recipient has to generate a unique digital code with the sender’s public key.
Finally, both digital codes get compared to ensure a match. If the digital document has not been tampered with, the sender is authenticated.
What is an electronic signature?
The global health crisis of 2020 facilitated digital transformation in many spheres of human life. Social distancing and other public health measures put a limit on in-person interactions, thus making paper-based workflows inappropriate. The pandemic took a heavy toll on SMBs and enterprises relying on contracts, forms, and other documents in their daily practices. Hence the rising need to adopt digital workflows alongside credible document validation mechanisms such as eSignatures.
Modern-day technology has helped many companies abandon paper-based workflows which proved to be burdensome, expensive, and unsustainable. Research suggests enterprises spend a shocking $8 billion only on paper management expenses. Moreover, 70% of US businesses would fail within three weeks if they lost the majority of paper-based records due to force majeure.
Using eSignatures reduces expenses associated with printing, sending, storing, and reproducing documents. On average, businesses spend about $20 to file a document, $120 to track down a misfiled document, and $220 to reproduce a lost document. Besides, going paperless is environment friendly and helps to lower the carbon footprint of copying paper.
Are electronic signatures secure?
In comparison to digital signatures, eSignatures seem to be relatively easy to use. To eSign a document, you need to upload an image of your signature from your device or draw it using a trackpad or touchscreen. The simplicity of eSignatures tricks users into thinking they are less secure than digital signatures. However, it all depends on the particular eSignature service and business requirements in terms of security measures. The choice of signing method must meet the demands of security and usability.
Malicious software, hacking attacks, and identity theft are the most common hazards associated with eSigning. When choosing an eSignature service, you have to make sure it comes with extra security measures. Advanced threat protection, multi-factor authentication, downloadable document history, and detailed audit trails will ensure each of your documents is safe and secure.
How to make electronic signatures more secure?
To protect electronic documents from third-party access and ensure enhanced eSignature security, these most common security measures are taken:
- Two-factor authentication (2FA) is a security mechanism that requires extra forms of user identification beyond the username and password before accessing the document. Typically, a signer is required to enter their credentials once more to ensure they are the intended recipient of your document.
- Authentication timeout sets the amount of time in minutes until the user authentication expires and they will be forced to re-login. This technique prevents third-party access to a document in the event a user did not perform any actions within a given timeframe.
- Caller ID authentication ensures document protection by identity verification through a phone call. To prevent caller ID spoofing, industry stakeholders turn to STIR/SHAKEN standards for credible caller identity verification.
- Document password is an extra layer of protection to guarantee that a recipient is the only person viewing, editing, and signing your document.
- Advanced threat protection (ATP) is a combination of enterprise-level security solutions that defend against malware, phishing, and other cybersecurity attacks targeting sensitive data.
What makes an eSignature legally valid?
The eSigning process represents a single-factor authorization with the signer's identity verification and the proof of signing. The ESIGN Act stipulates the conditions making electronic signatures legally valid and enforceable:
- All parties involved in the signing process must give affirmative consent to using an electronic signature.
- The process of creating an eSignature must be recorded with relevant software used for this purpose.
- Records of electronic signatures must be retained and accessible for reproduction.
In exceptional cases, electronically signed records may be inadmissible as an item of evidence in court despite being legally valid. This may happen due to the absence of audit logs or weaknesses in authentication. That’s why, when choosing an eSignature solution, it must meet a broader scope of requirements:
- Each user must have a unique eSignature. A one-of-a-kind signature is attributed to each signer involved in the signing process.
- A selection of signer authentication options. The signer’s identity can be verified using a scope of authentication methods – an email address, IP address, and time of document access. The option of adding two-factor authentication to any document should be made available.
- Cloud document retention. Electronic records must be retained in a secure cloud storage. Any party involved in the signing process must be able to view and download a copy of the eSigned document.
- Comprehensive audit log. All parties involved in the signing process must be able to access a detailed document history within the eSignature app. An audit log must include the history of uploading, adding elements, viewing, signing, attributed to each signatory.
- Compliance with security standards. The eSignature solution must ensure the security of sensitive data and comply with security standards.
How to create an eSignature
Small to medium-sized businesses and enterprises need advanced eSignature apps to make complex digital workflows more streamlined. airSlate SignNow’s functionality range lets users create and eSign documents, refine the contract management process, accept payments, and more. As a part of the airSlate Business Cloud, airSlate SignNow provides access to a comprehensive database of legal documents and forms.
Follow the steps below to create an electronic signature using airSlate SignNow:
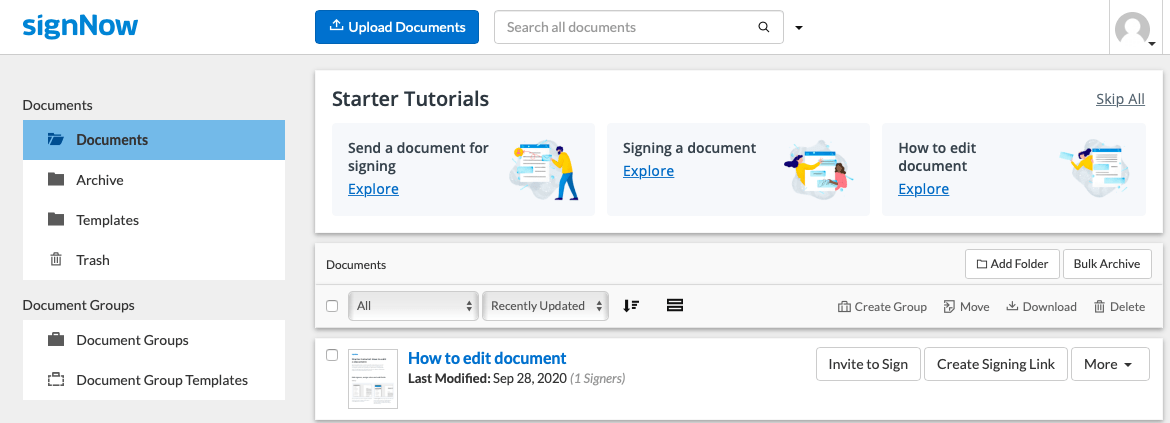
1. Log in to your airSlate SignNow account and select a document you want to sign electronically.
Note: if you are new to using eSignature apps, use starter tutorials on the airSlate SignNow’s Homepage to figure out the main features.
Pick an existing document or template from the Documents folder on the left or import a new document from your device. airSlate SignNow supports a variety of document formats: PDF, DOCX, PPTX, GIF, JPG/JPEG, and PNG.
2. Make necessary changes to the document in the airSlate SignNow editor before eSigning a document or sending it to other signers.
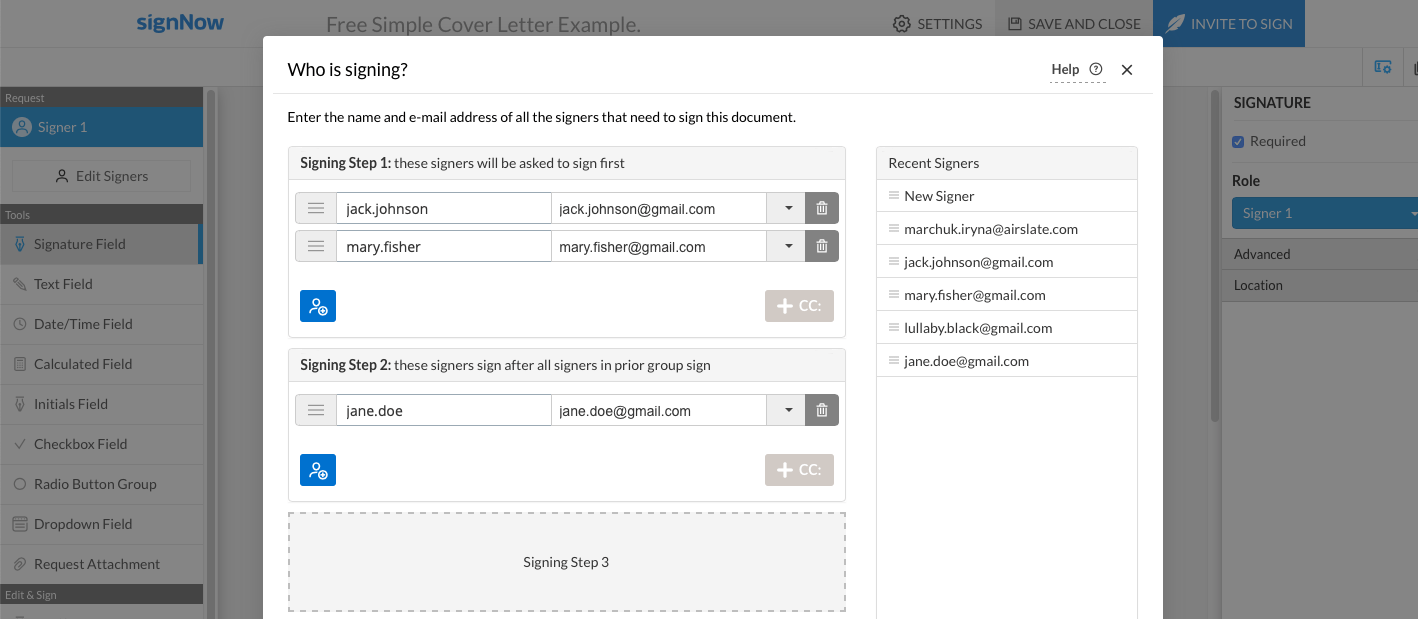
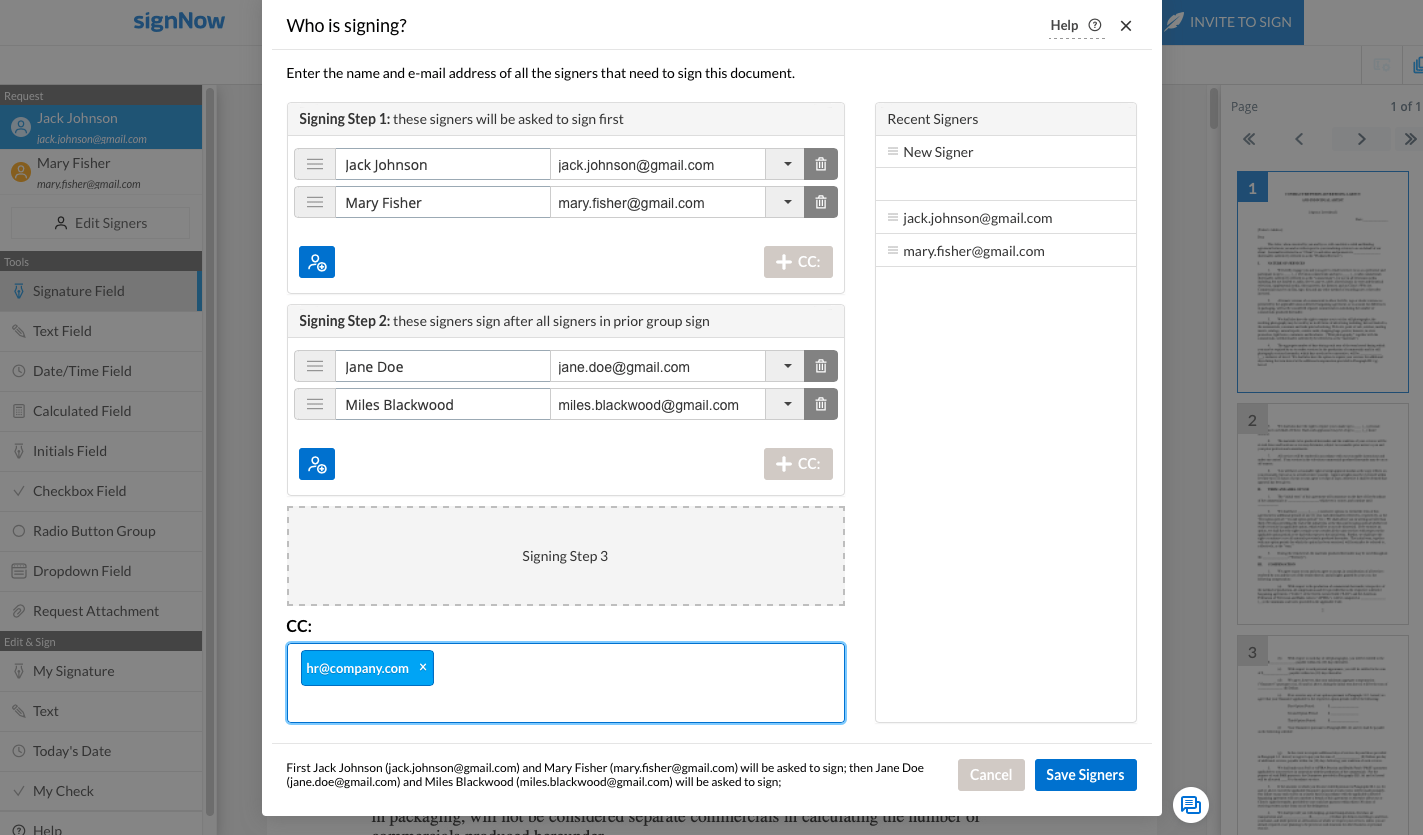
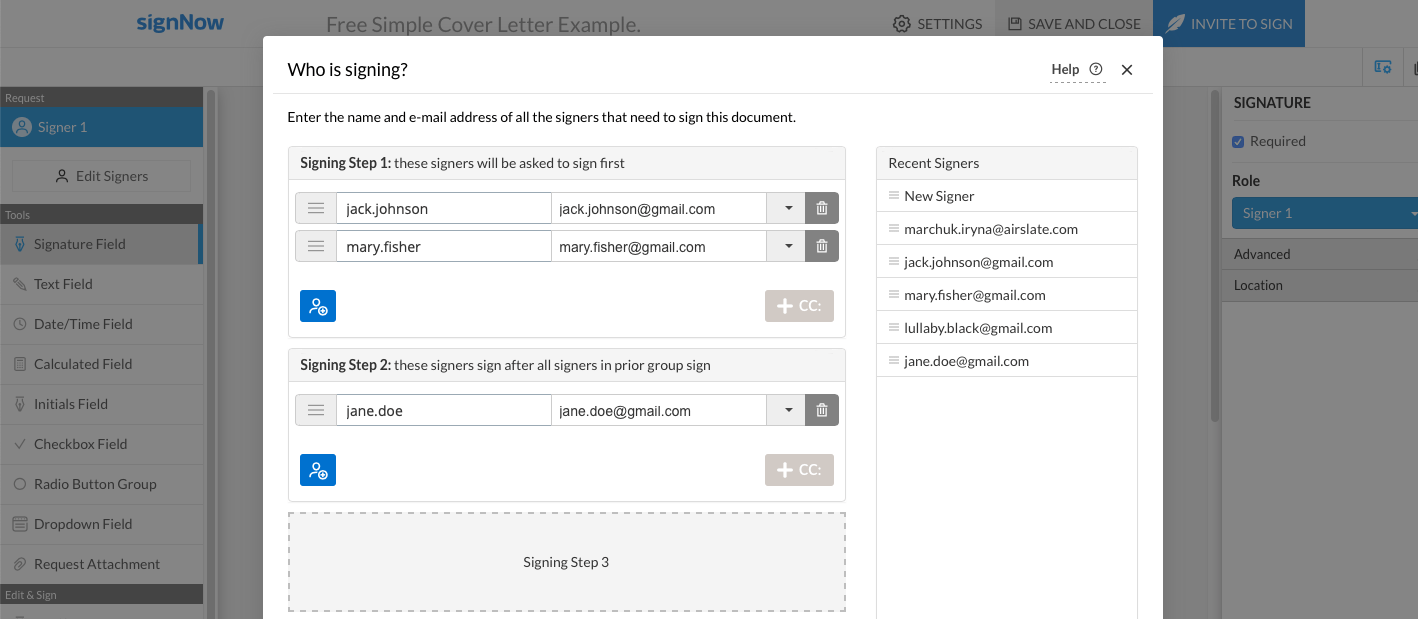
In airSlate SignNow, you can create an eSignature workflow by choosing the signing order for the document. Click the Edit Signers button under the Request section in the top-right corner to add or remove signers. In the “Who Is Signing?” pop-up window, enter the names and email addresses of the prospective signers. To specify the signing order, add signers to the respective Signing steps.
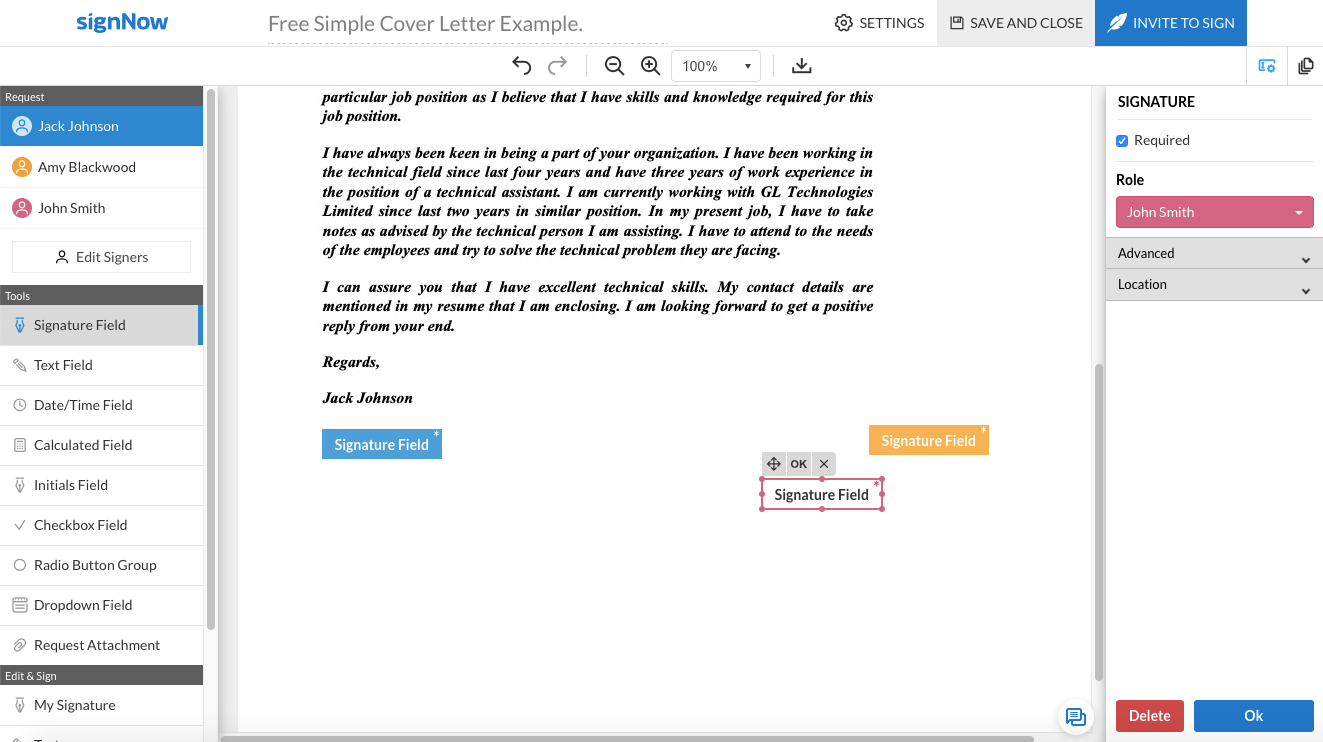
3. airSlate SignNow allows users to add signature fields for a single or multiple signers anywhere in the document. To create a new signature field, click the Signature Field button in the Tools section. Place the cursor on the document and click OK to save the newly-created signature field. Feel free to move the signature field around by dragging and dropping it where you see fit.
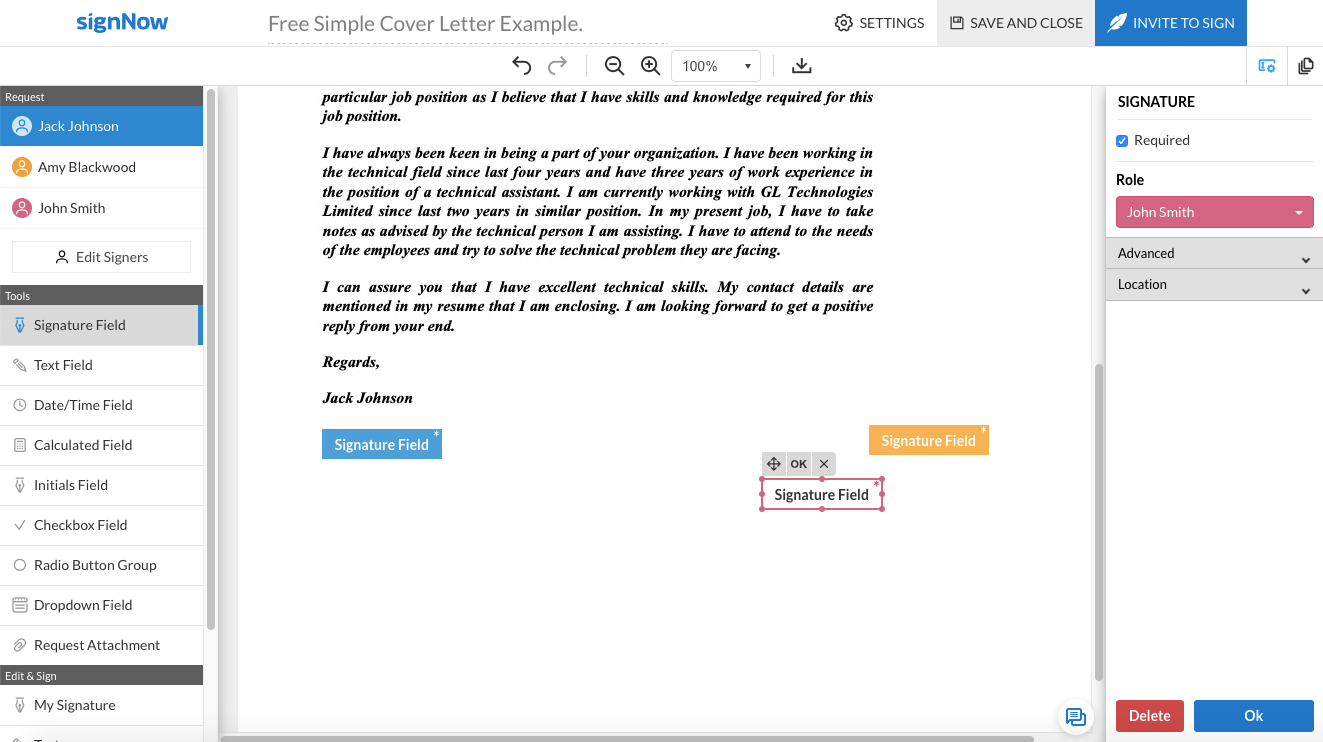
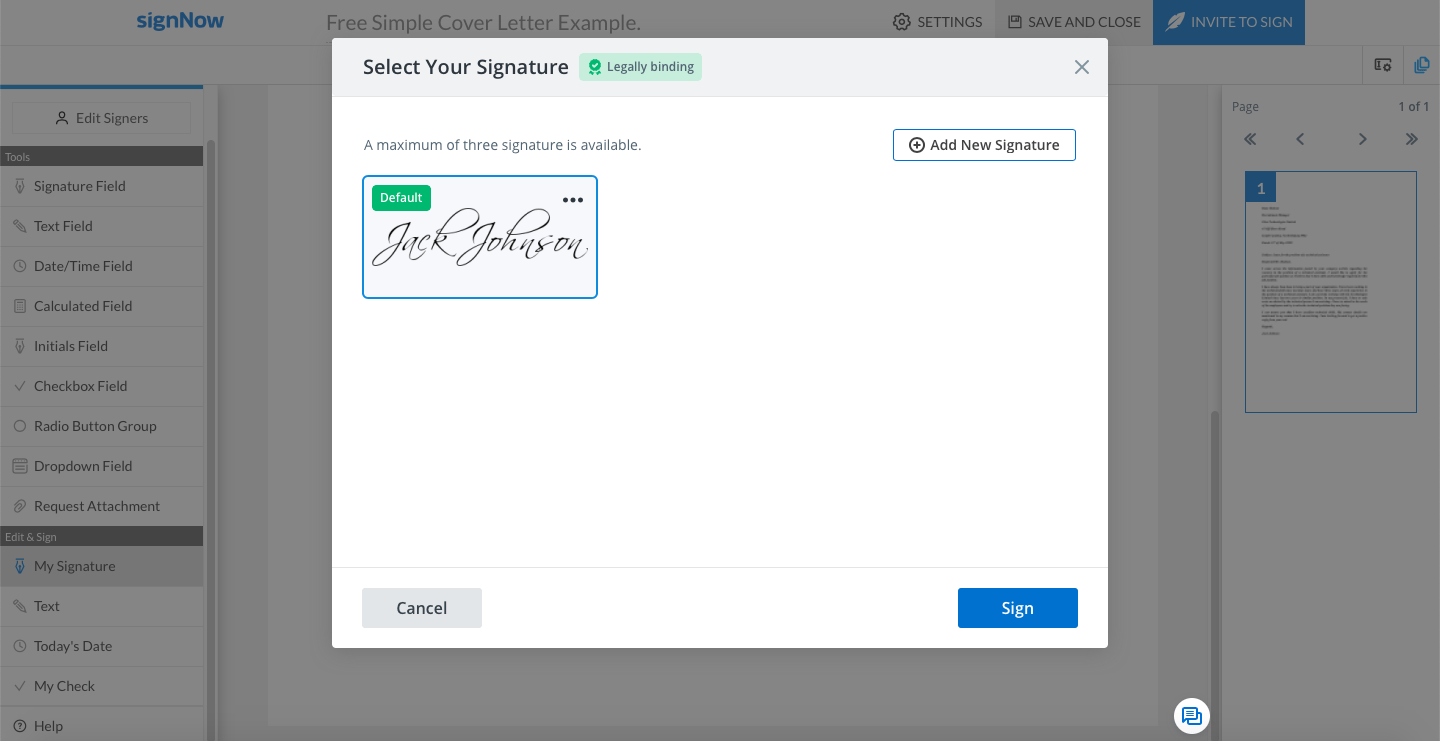
4. In case you need to be the first to eSign a document, click the My Signature button in the Edit & Sign section.
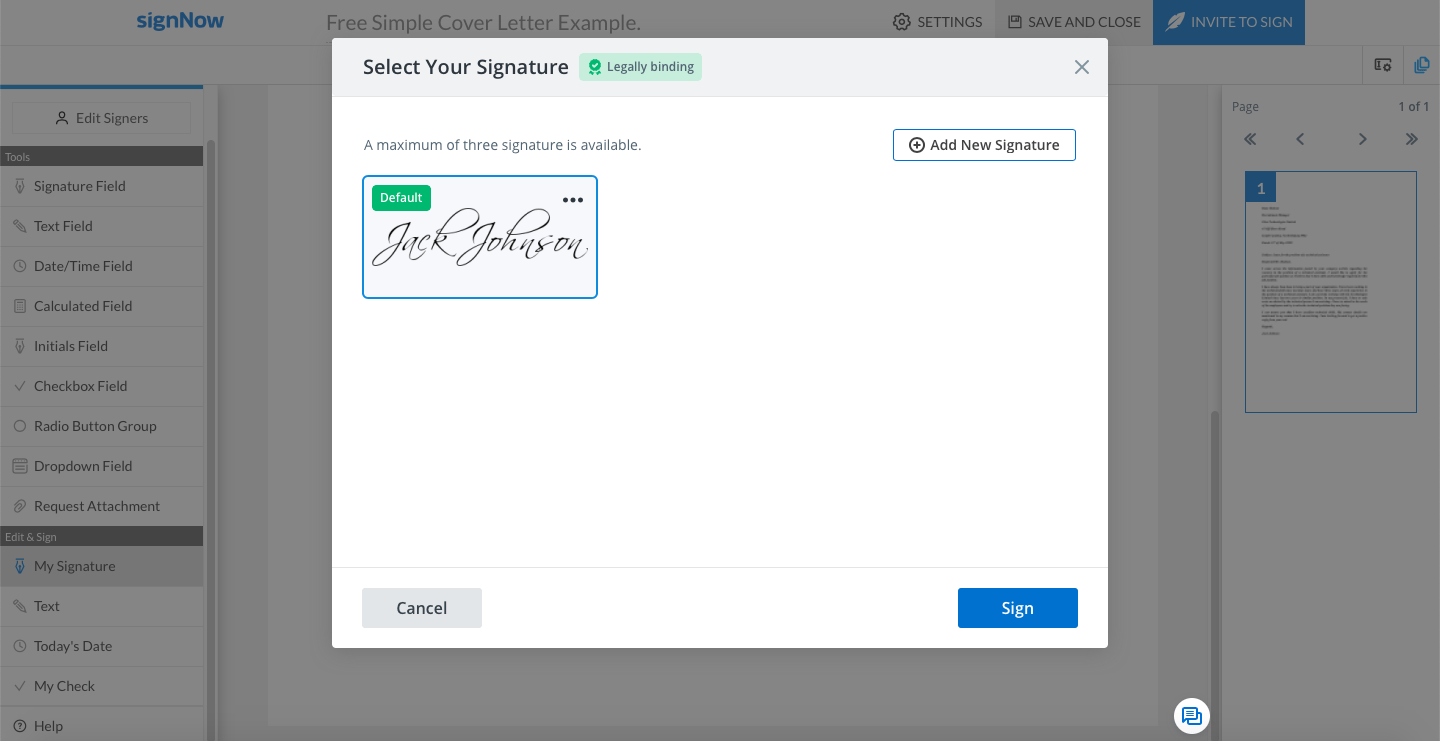
Place a cursor on the document to access the eSignature pop-up window. If you’ve previously signed documents using airSlate SignNow, your electronic signature is already stored in the app. Just select the suitable eSignature to use it.
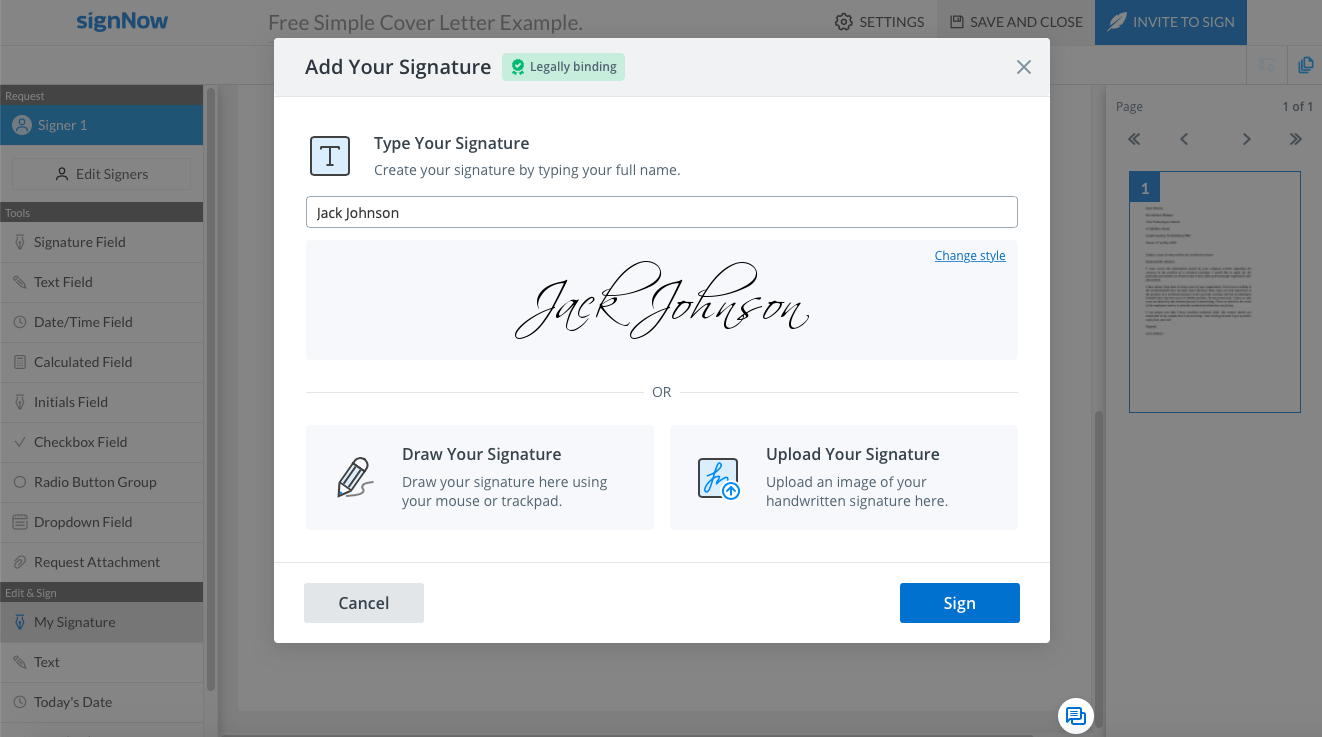
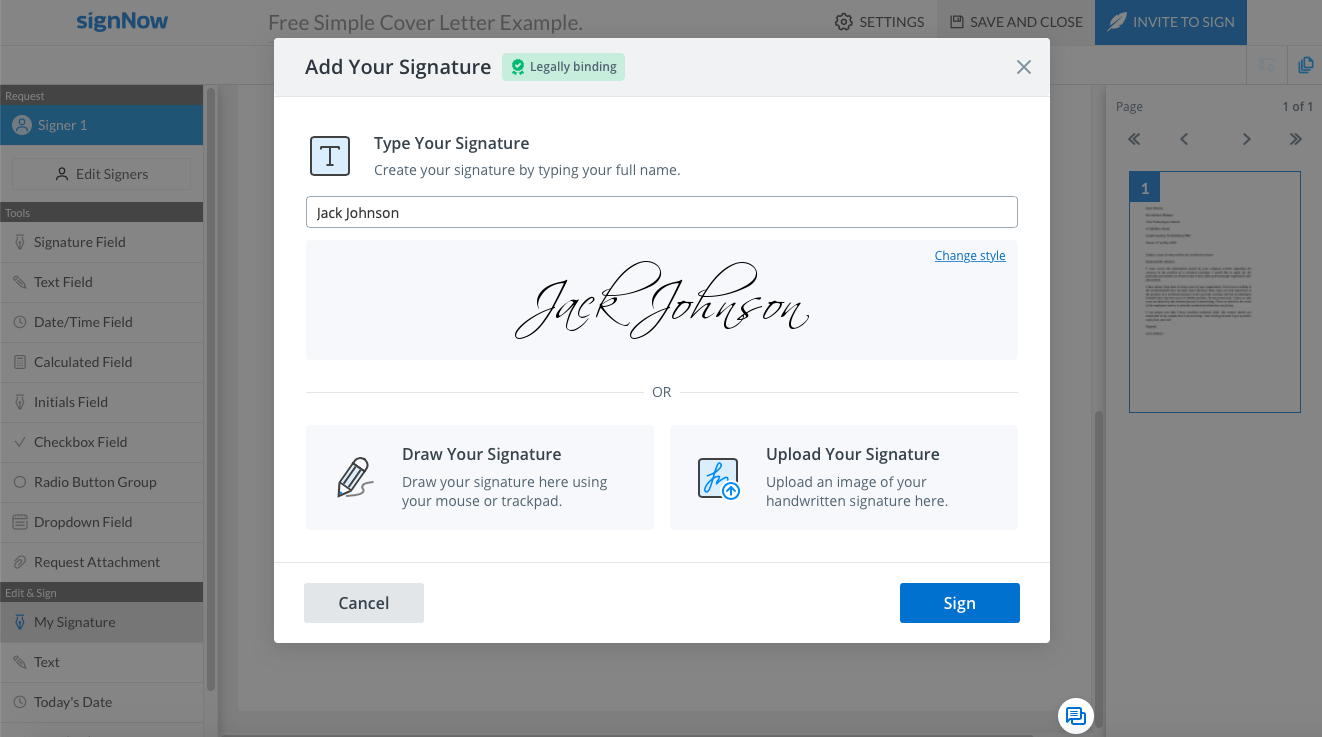
If you need to create a new eSignature to sign a document, click the Add New Signature button. Next, you’ll be offered to use one of the three eSignature creation options:
- Type Your Signature. Type your full name to create a new eSignature.
Click Change Style to alter the look of your signature. For instance, you can select a tilted typeface to make it look like a handwritten signature.

- Draw Your Signature. Create a new eSignature by drawing it with your finger on a trackpad or using a mouse cursor within the empty field.

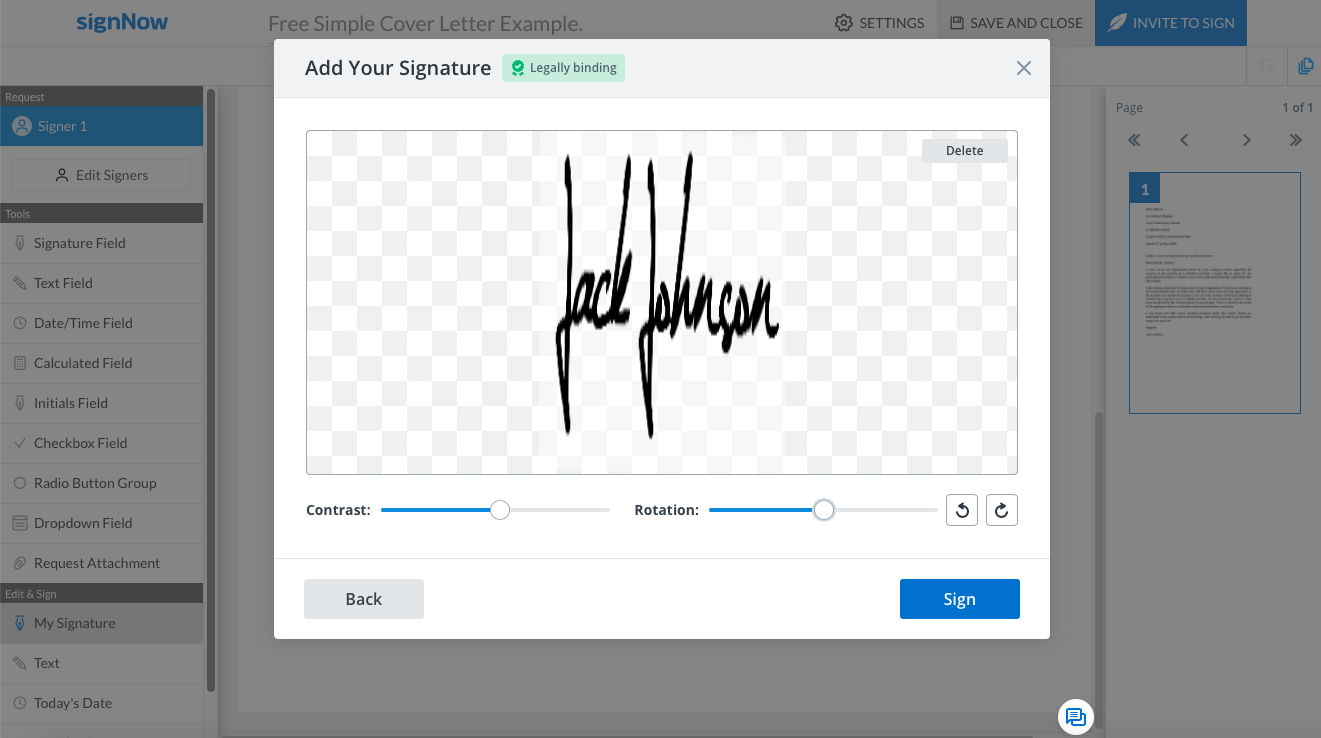
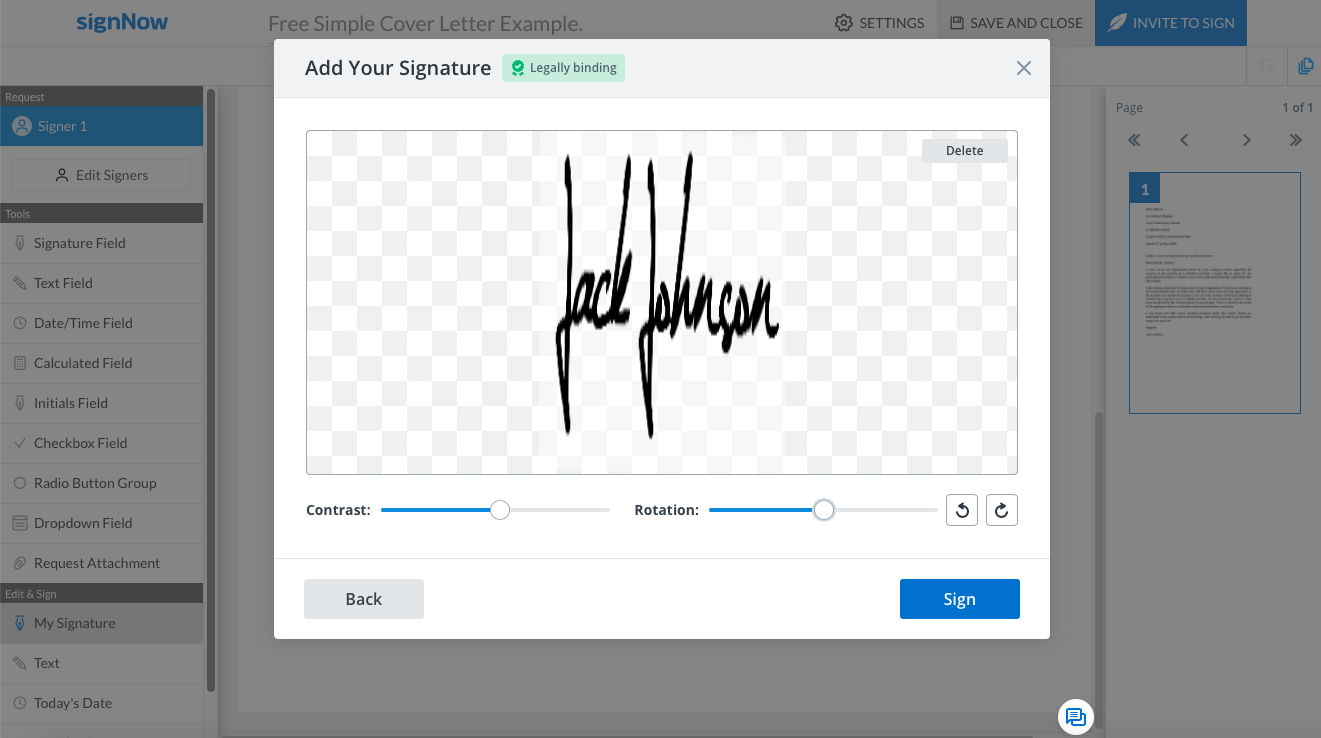
- Upload Your Signature. If you have an image of your hard copy signature in JPG, GIF, or PNG format on your device, you can upload it to airSlate SignNow. Make sure the image size is under 4 Mb. You can enhance the image by using the Contrast and Rotation settings.
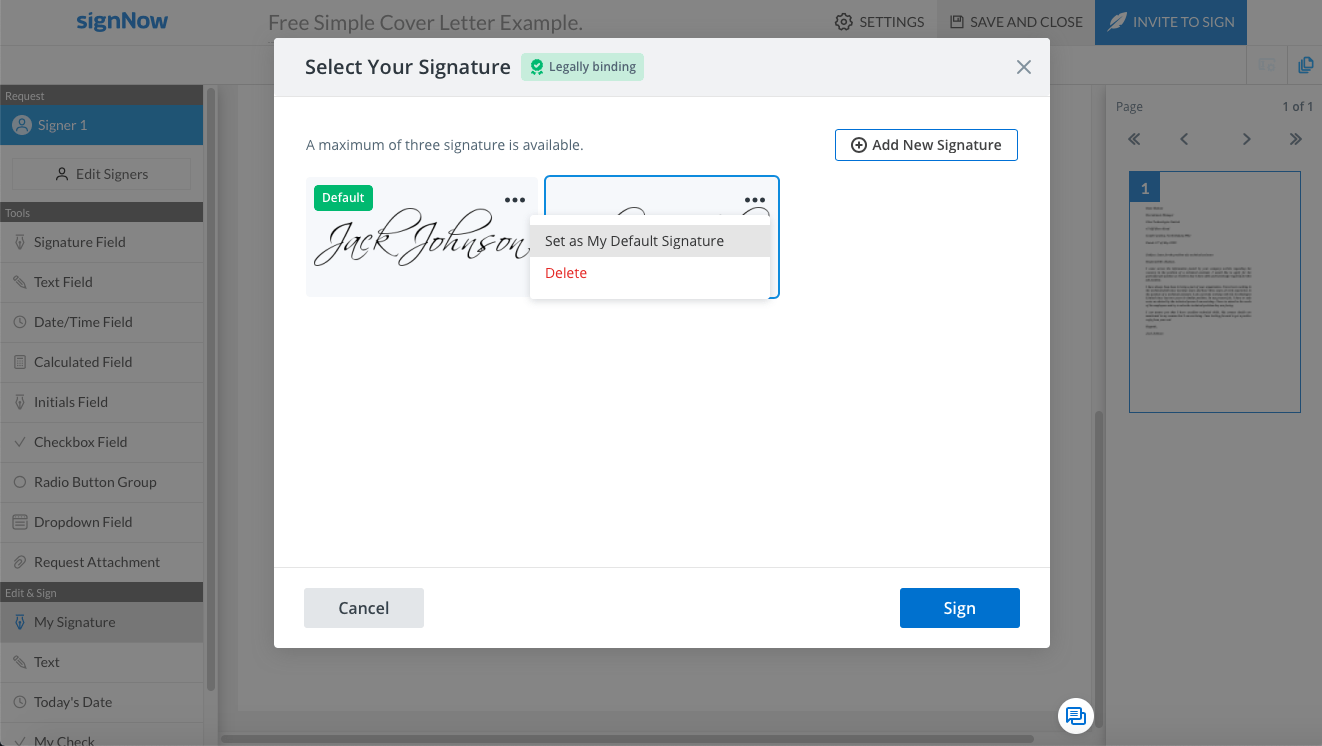
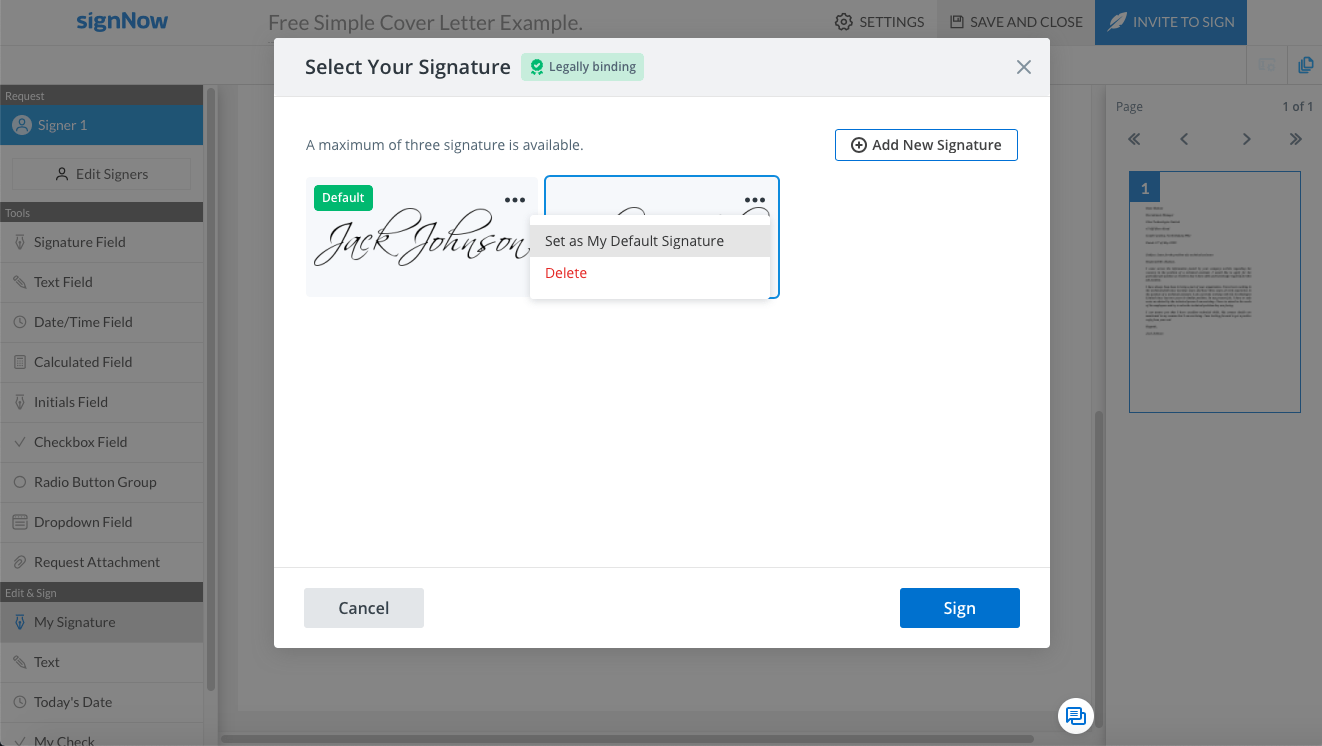
5. airSlate SignNow allows using up to three electronic signatures. Feel free to set one of them as your default. In the Select Your Signature pop-up, select the eSignature you need and click “Set as My Default Signature”.
6. To finalize the signing process, click the Sign button in the bottom-right corner of the pop-up. Click Save and Close to go back to the Homepage.
airSlate SignNow’s functionality is not only limited to eSignatures. The app allows for the creation of document templates, the viewing of History with an audit trail, the downloading of documents with History, plus a whole lot more.
How to create signature workflows with airSlate SignNow
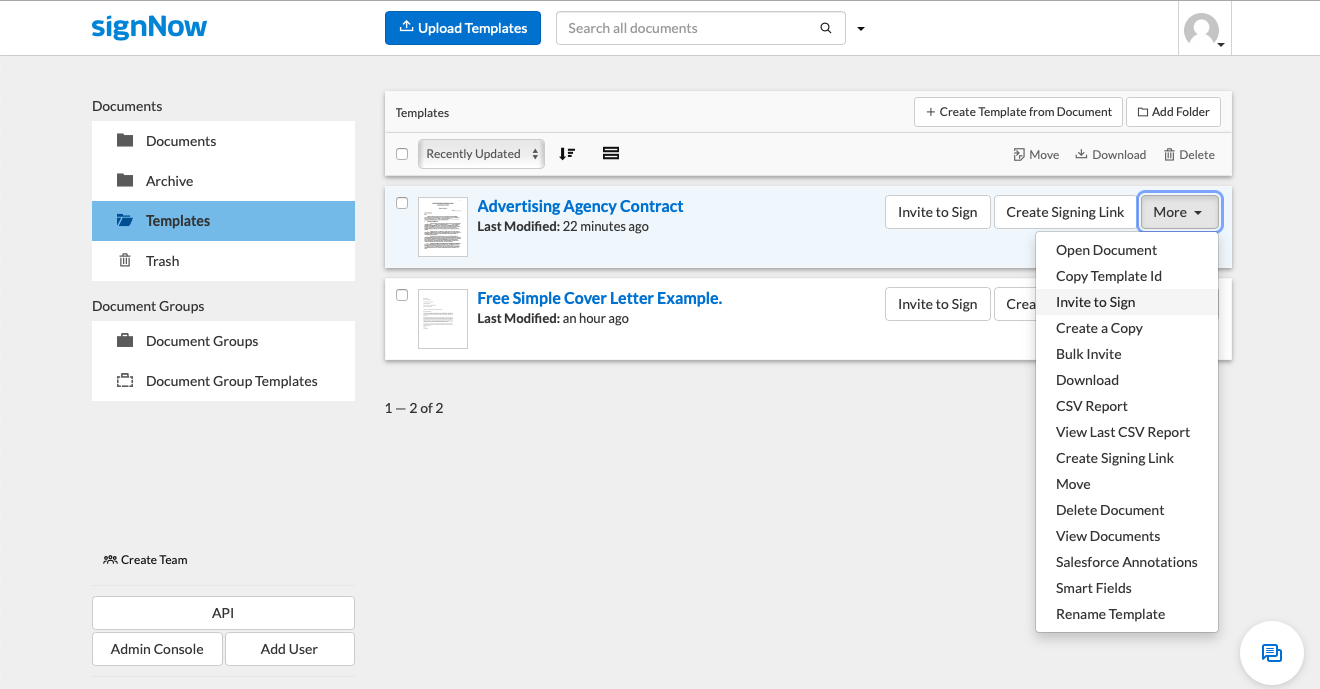
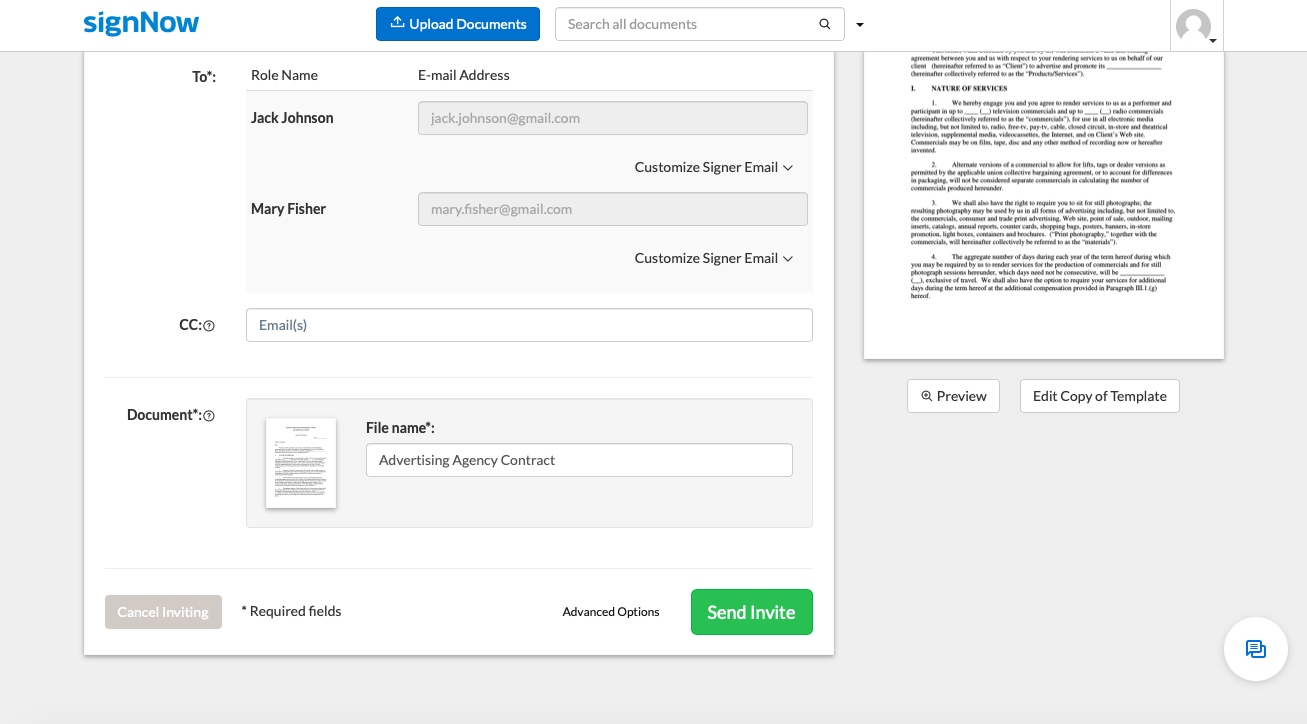
With airSlate SignNow, it’s possible to create signature workflows for a particular document. The most straightforward way to do this is by using the Invite to Sign feature.
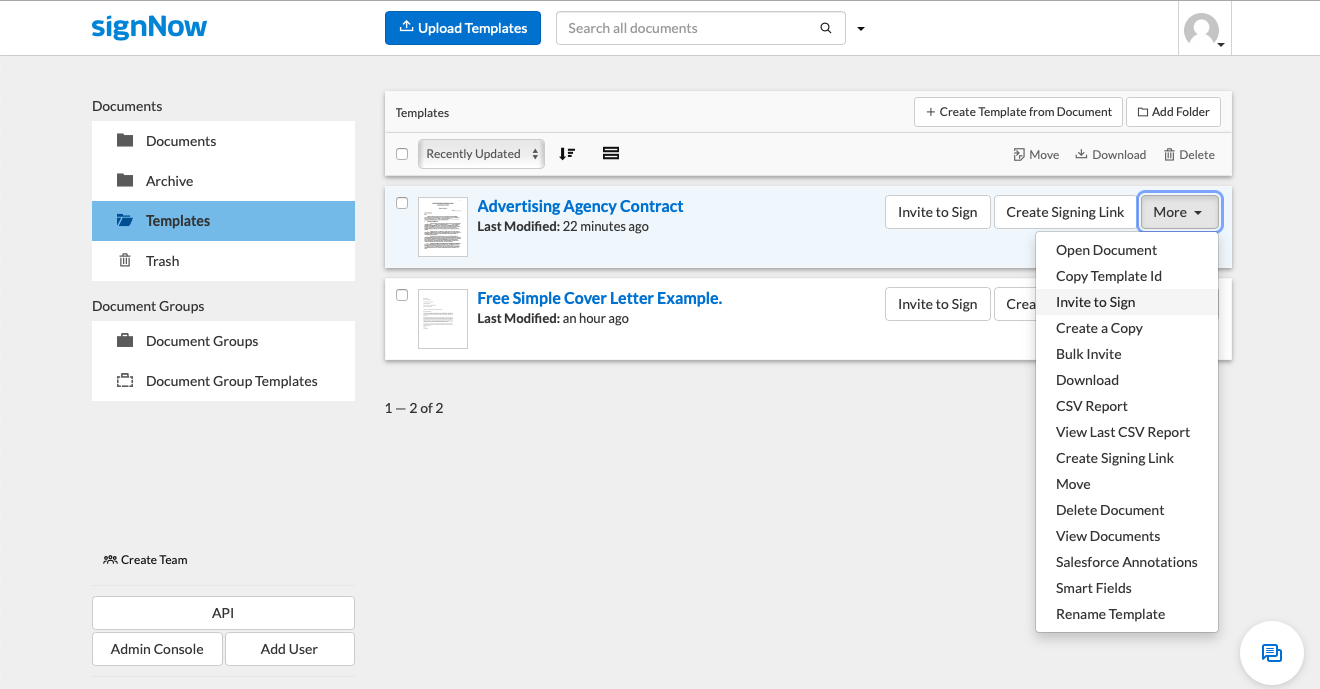
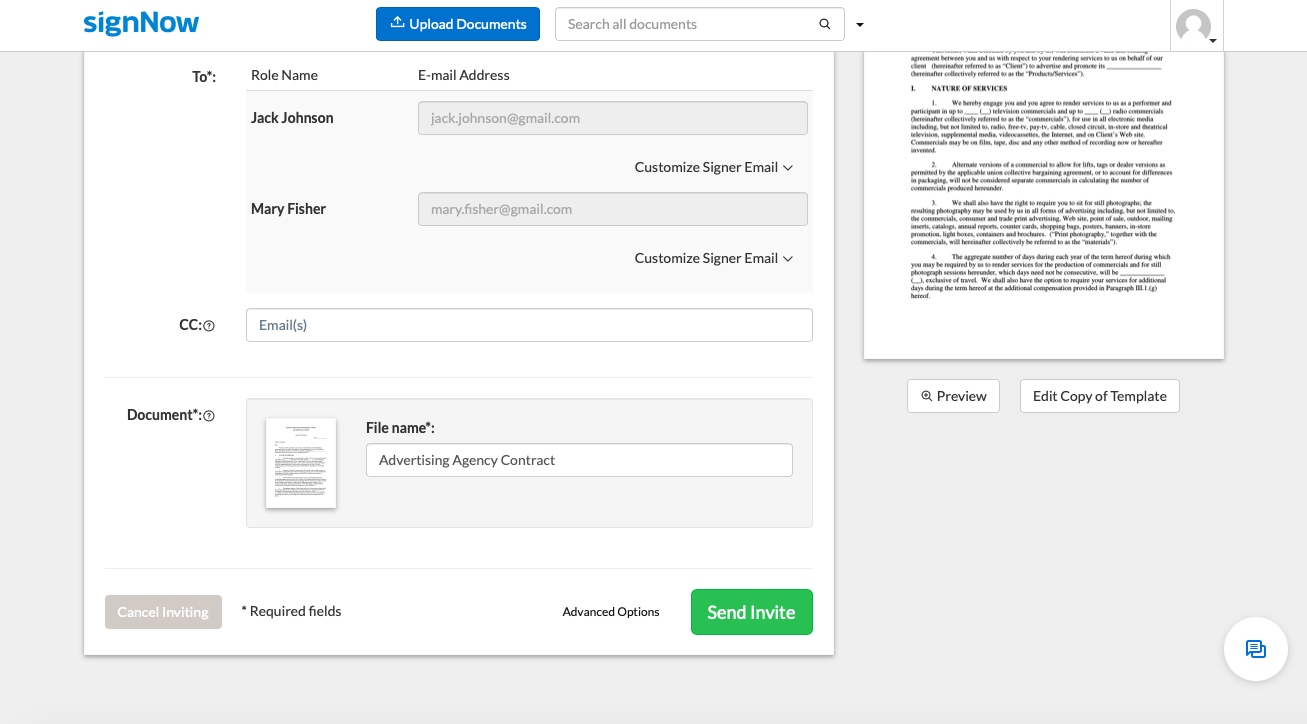
1. On your Homepage, pick a document and click the More button on the far right. In the dropdown menu, select Invite to Sign. Next, you’ll be redirected to the “Who is signing?” window where you can type in the signer’s name and email.
Add multiple signers and forward a carbon copy to a third party if necessary. In case you need to invite signers to a document in a particular order, type in the signers’ names and email addresses into the respective Signing Step. Alternatively, you can drag and drop the signers’ emails from the Recent Signers section on the right.
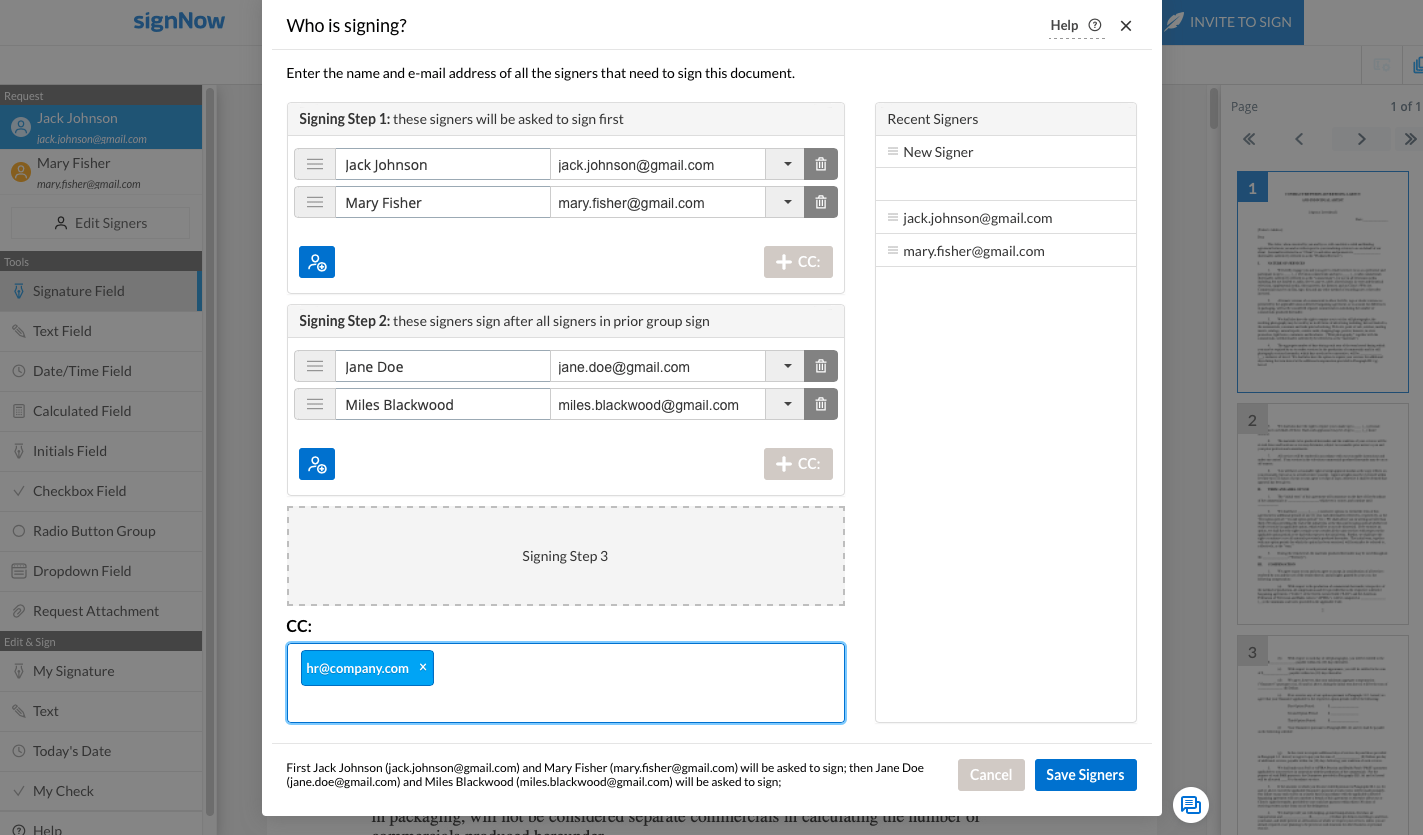
2. Once you’re satisfied with the signing order, click the Save Signers button at the bottom of the pop-up. Continue with adding the signature fields to the document. Click the Invite to Sign button in the top-right corner of the screen to complete the process.

3. Next, proceed to the final screen to check if the recipient’s name and email address are correct. If everything looks fine, click the Send Invite button. After that, the recipient will get an invitation to eSign your document.
Take note: airSlate SignNow provides you with a possibility to revoke your signature invitation(s) by clicking the Cancel Inviting button
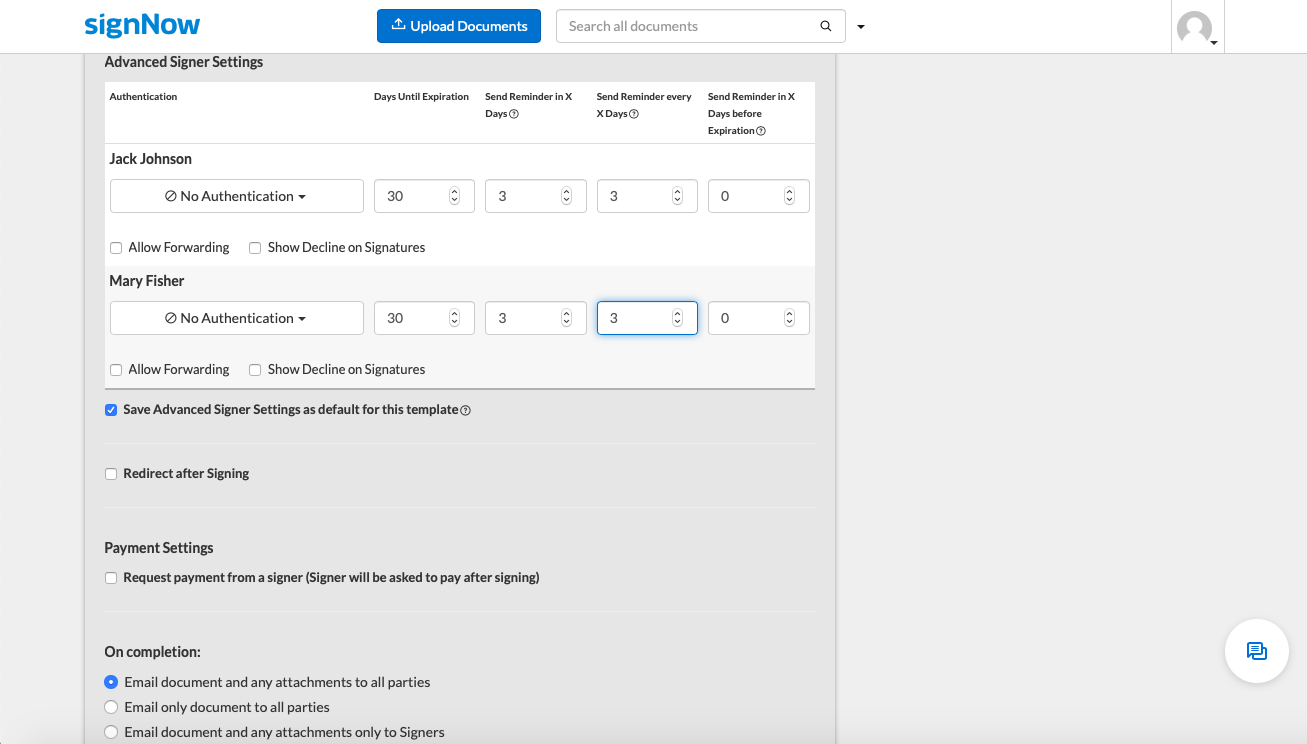
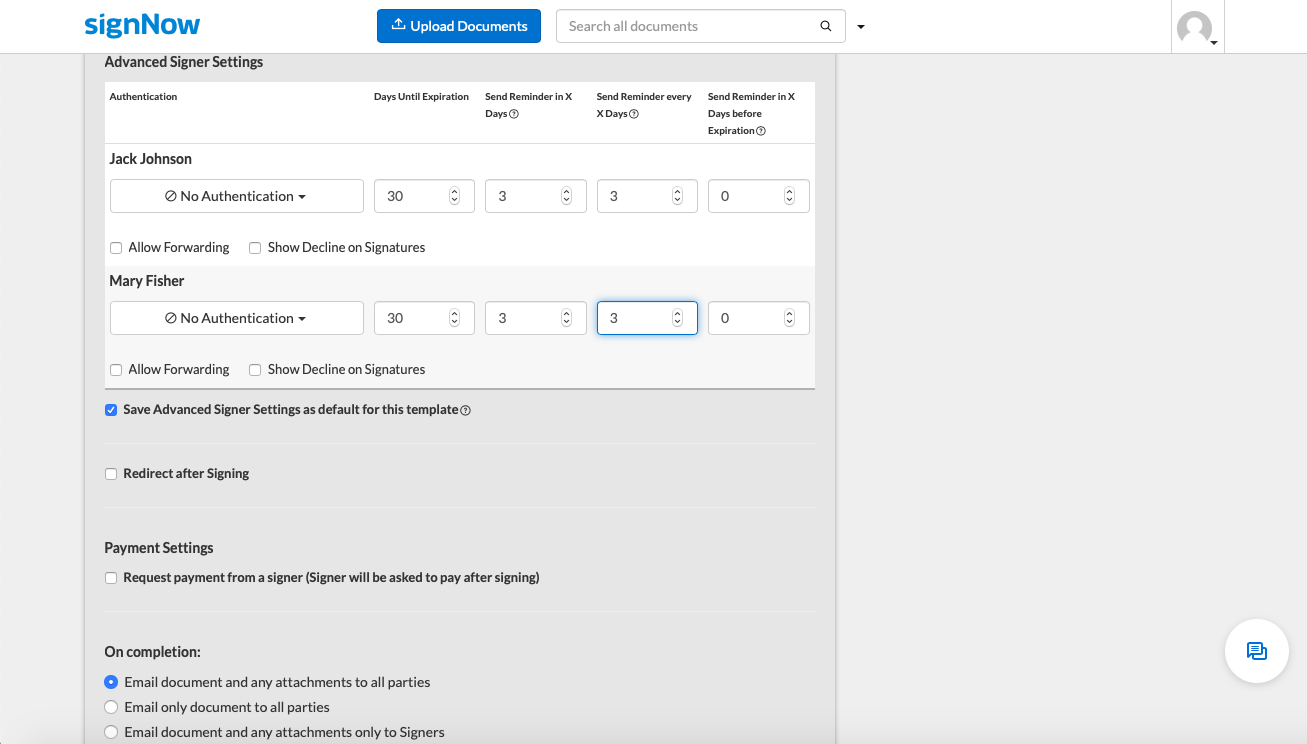
4. The Advanced Options button gives access to extra settings. Feel free to set an expiration date between 3 to 180 days and automatically remind signers if the document hasn’t been eSigned. Enable the Allow Forwarding and Show Decline on Signatures settings if necessary.
Is airSlate SignNow ESIGN compliant?
Absolutely! In this article, we have discussed the essential provisions of the Electronic Signatures in Global and National Commerce (ESIGN) Act of 2000 and learned about the laws and regulations stipulating the legal effect of eSignatures. Also, we have emphasized the difference between digital and electronic signatures and learned what makes both of them secure and valid. Finally, we have provided step-by-step instructions on how to create electronic signatures, eSign documents, and set up signature workflows with airSlate SignNow.
What are the key benefits of using airSlate SignNow for SMBs and enterprises?
- Refined signature workflows — invite multiple users to eSign documents in one click. Set up a signing order and elevate the signing experience both in-office and off-site.
- Eliminate the risk of human error – get the document ready for signing by adding all necessary fields and define conditional fields to collect specific information. Ensure no field is left out using the automated signing guidance.
- Surprise the signers with an effortless signing experience — owing to the highly-intuitive user interface, eSigning documents in airSlate SignNow is a matter of moments on desktop and on mobile.
- Keep your business transactions secure and ESIGN compliant — airSlate SignNow complies with security standards (PCI DSS, SOC 2 Type II), and relevant legislation (HIPAA, eIDAS, 21 CFR Part 11). This guarantees the security and compliance of the eSignature process.
- Ensure transparency and accountability — make every step of the signing process visible with instant notifications and deadline reminders for signers. Track the eSignature sequence through court-admissible audit logs.
- Elevate your team’s performance — airSlate SignNow allows for secure document exchange and collaboration on documents and templates. Help your team stay abreast of all document changes with instant notifications.
The bottom line
eSignature solutions like airSlate SignNow help businesses, enterprises, and governments stay in compliance with UETA and the ESIGN Act, and other laws and regulations. In the times of COVID-19, airSlate SignNow facilitates remote business interactions by saving time and money while eliminating health threats. airSlate SignNow provides its users with a powerful eSignature toolset making it possible to sign documents on any device, both online and offline. airSlate SignNow caters to the needs of different users – whether they prefer a web-based app or iOS/Android mobile apps.
Make your business interactions ESIGN compliant. Try airSlate SignNow today!