Adjuntar Registro De Imagen. Utilice Herramientas De Firma Electrónica Que Funcionan Donde Usted Trabaja.
Obtenga las capacidades de firma electrónica que necesita de la solución en la que confía
Seleccione el servicio profesional creado para profesionales
Configure la API de firma electrónica rápidamente
Colabore mejor juntos
Adjuntar registro de imagen, en minutos
Reduzca el tiempo de cierre
Mantenga la información sensible segura
Vea las firmas electrónicas de airSlate SignNow en acción
Soluciones de airSlate SignNow para una mayor eficiencia
Las reseñas de nuestros usuarios hablan por sí mismas






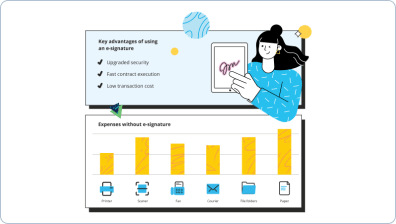
Por qué elegir airSlate SignNow
-
Prueba gratuita de 7 días. Elige el plan que necesitas y pruébalo sin riesgos.
-
Precios honestos para planes completos. airSlate SignNow ofrece planes de suscripción sin cargos adicionales ni tarifas ocultas al renovar.
-
Seguridad de nivel empresarial. airSlate SignNow te ayuda a cumplir con los estándares de seguridad globales.

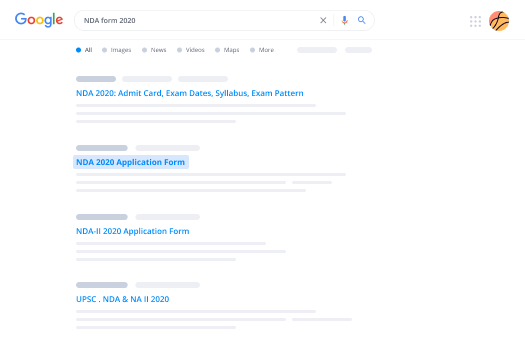
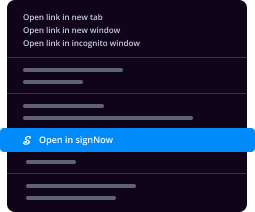
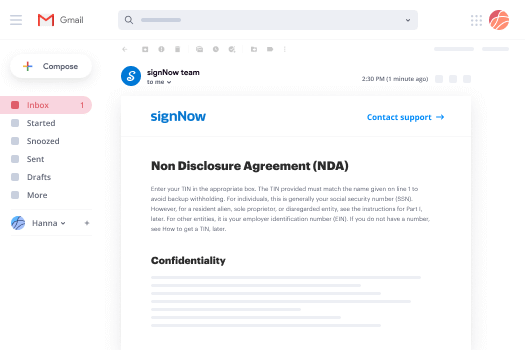
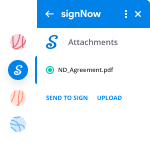
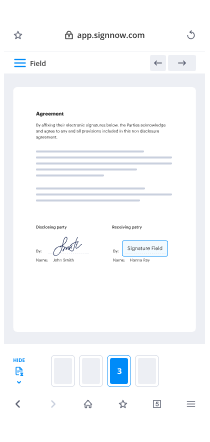
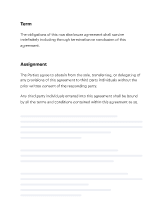
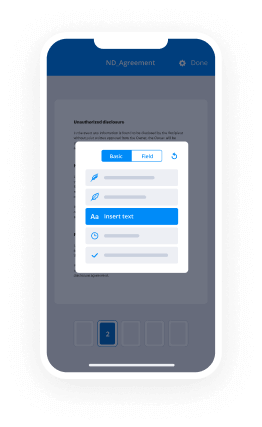
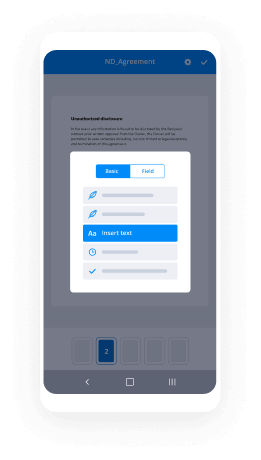
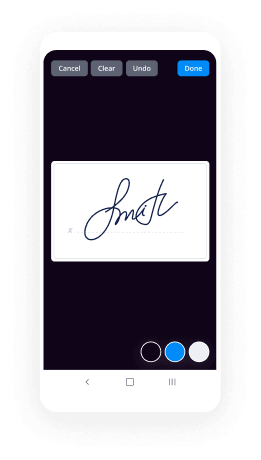
Tu guía paso a paso — affix image log
Adjuntar registro de imagen. Obtenga el mayor valor del sistema de firma electrónica más confiable y seguro. Mejore sus transacciones digitales usando airSlate SignNow. Optimice los flujos de trabajo para todo, desde documentos básicos de empleados hasta acuerdos complejos y formularios de marketing.
Aprenda cómo adjuntar registro de imagen:
- Importe múltiples archivos desde su unidad o almacenamiento en la nube.
- Arrastre y suelte campos rellenables inteligentes (firma, texto, fecha/hora).
- Cambie el tamaño de los campos, tocándolos y eligiendo Ajustar tamaño.
- Agregue casillas de verificación y listas desplegables, y grupos de botones de opción.
- Agregue firmantes y solicite materiales adicionales.
- Adjunte registro de imagen.
- Agregue la fórmula donde requiera que se genere el campo.
- Agregue comentarios y anotaciones para los destinatarios en cualquier parte de la página.
- Guarde todas las modificaciones haciendo clic en HECHO.
Conecte a usuarios dentro y fuera de su organización para trabajar electrónicamente en signNow y adjuntar registro de imagen en cualquier momento y en cualquier dispositivo usando airSlate SignNow. Puede rastrear cada actividad realizada en sus muestras, recibir alertas y un informe de auditoría. Manténgase enfocado en su negocio y en las relaciones con los clientes, sabiendo que sus datos son precisos y están protegidos.
Cómo funciona
Funciones de airSlate SignNow que los usuarios adoran
Vea resultados excepcionales Adjuntar registro de imagen. Utilice herramientas de firma electrónica que funcionan donde usted trabaja.
¡Obtenga firmas legalmente vinculantes ahora!
Preguntas frecuentes
-
¿Cómo puedo poner mi logo en una imagen?
Comience con un logo. Abra su logo o diseñe uno con nuestras herramientas. ... Abra su foto. Abra la foto que desea marcar con marca de agua en el Editor. Agregue su logo. Añada su logo como un gráfico con la opción Su Propio. Posiciónelo y atenúe. Mueva su logo a la posición correcta y luego ajuste el control deslizante de Atenuación. -
¿Cómo pongo un logo en una imagen en mi iPhone?
Inicie eZy Watermark lite. Toque en Imagen Única o Imágenes Múltiples. Toque para seleccionar la fuente de la imagen que desea marcar. Seleccione la imagen que desea marcar. Toque en la opción que desea agregar a la imagen — firma o texto son las más comunes para marcas de agua. -
¿Qué aplicación puedo usar para agregar mi logo a una imagen?
iWatermark es una aplicación para marcar con marca de agua fotos en iPhone y Android. La aplicación ofrece a los usuarios la posibilidad de insertar tanto texto (nombre, sitio web, fecha y hora) como marcas gráficas (logo o firma). -
¿Cómo hago una imagen PNG en iPhone?
Agregue la imagen a su carrete de cámara tocando y manteniendo la imagen. Luego, seleccione "Guardar imagen" cuando se le solicite. Toque en la aplicación "Cámara" y luego seleccione el botón Carrete de Cámara. Deslice hacia la izquierda en la pantalla hasta localizar el archivo que desea ver. -
¿Cómo pongo una marca de agua en las fotos?
Abra el documento que tiene la imagen en la que desea colocar la marca de agua. Vaya a la pestaña Diseño de página. Seleccione Grupo Fondo de página. Haga clic en Marca de agua. Haga clic en Marca de agua personalizada. Haga clic en Marca de agua de texto. Se abrirá un cuadro. Escriba el texto que desea usar como marca de agua en el cuadro. Haga clic en Insertar. -
¿Cómo pongo mi logo en fotos de Instagram?
Inicie sesión en su cuenta de Instagram en su teléfono. Vaya a su perfil haciendo clic en el icono de la persona. Haga clic en su foto de perfil y seleccione Subir foto. Seleccione su archivo de logo y haga clic en Elegir. En móvil, toque en Editar perfil y seleccione Cambiar foto de perfil. Una vez que haya seleccionado un archivo, toque en Listo. -
¿Debería poner marca de agua en mis fotos de Instagram?
Por lo general, poner marca de agua en Instagram no es bien visto, por lo que el 99% de las personas no lo hace. Disuadirá a las personas de seguirte si marcas tus imágenes con marca de agua. -
¿Cómo pongo mi logo en mis fotos en mi iPhone?
Inicie eZy Watermark lite. Toque en Imagen Única o Imágenes Múltiples. Toque para seleccionar la fuente de la imagen que desea marcar. Seleccione la imagen que desea marcar. Toque en la opción que desea agregar a la imagen — firma o texto son las más comunes para marcas de agua. -
¿Cómo crear una marca de agua para fotos?
Abra su logo, hágalo blanco sobre un fondo transparente y guárdelo como PNG. Abra la imagen en la que desea colocar una marca de agua. Haga clic en Agregar una imagen, seleccione dónde está guardado su logo y añádalo. Redimensione su logo y colóquelo en una esquina de su imagen. -
¿Cómo creo una marca de agua personalizada?
En la pestaña Diseño, seleccione Marca de agua > Marca de agua personalizada. Elija Marca de agua de imagen y seleccione una imagen, o elija Marca de agua de texto y escriba su texto de marca de agua en el cuadro de texto. Haga clic en Aceptar.
Lo que dicen los usuarios activos — affix image log
Preguntas frecuentes
¿Cómo agrego una firma electrónica a un documento de Word?
¿Cómo agregar una firma electrónica a un PDF?
¿Cómo puedo firmar mi nombre en un archivo PDF?
Obtén más para affix image log
- ESign para gestión de contactos y organizaciones para Producción
- ESign para gestión de contactos y organizaciones para Supervisión
- ESign para gestión de Contactos y organizaciones para Calidad del Producto
- ESign para gestión de Contactos y organizaciones para Inventario
- ESign para gestión de contactos y organizaciones para Seguridad
- ESign para gestión de contactos y organizaciones para I+D
- ESign para gestión de contactos y organizaciones para Personal
- Firma electrónica de airSlate SignNow para ROI de CRM
Todo sobre la firma electrónica

Descubre otros affix image log
- Enviar un documento con una firma por correo ...
- Cómo firmar un documento en línea y enviarlo por ...
- Cómo usar un certificado de firma digital en PDF de ...
- Cómo usar la firma electrónica en Acrobat de manera ...
- Cómo usar una firma digital en MacBook para ...
- Métodos para firmar un PDF en línea de manera fácil ...
- Comando para firmar PDF en Linux simplificado con ...
- Cómo firmar documentos PDF en Windows de manera ...
- Cómo firmar un archivo PDF y enviarlo de vuelta por ...
- Firma tu documento PDF en el teléfono con facilidad
- Firma tu documento PDF con certificado de manera ...
- Cómo firmar un documento PDF en mi iPhone con airSlate ...
- Firma PDF en línea con firma electrónica de manera ...
- Cómo firmar un archivo PDF con Google Chrome de forma ...
- Firma archivos PDF en Chrome con airSlate SignNow
- Descubre las maneras de agregar una firma electrónica ...
- Formas de agregar una firma digital a un PDF de manera ...
- Add CAC Signature to PDF Quickly and Securely with ...
- Cómo agregar firma en Pages Mac de manera sencilla
- Agrega firma a un PDF en Mac de forma sencilla