Configuración De Autenticación De Doble Factor Para eSignature
Cómo subir una imagen de un documento desde la galería a airSlate SignNow
Fácilmente mueva una foto de un documento desde el almacenamiento de su dispositivo a su cuenta de airSlate SignNow. El documento importado puede ser editado rápidamente, transformado en un formulario rellenables y enviado para firma electrónica directamente desde su teléfono inteligente o tableta.
Comience con un toque de su dedo
Toque el icono más en la esquina inferior derecha de la pantalla de inicio de la aplicación móvil de airSlate SignNow para abrir el menú de carga.
Seleccione Galería en el menú y busque en su dispositivo la imagen del documento que necesita.
Editar y guardar imágenes de documentos en segundos
Después de seleccionar la foto que necesita, se abrirá en el editor de airSlate SignNow. Puede agregar anotaciones y campos rellenables usando las herramientas en la parte inferior de la pantalla.
Una vez terminado, toque el icono de marca de verificación en la esquina superior derecha de la pantalla para guardar un documento.
Ingrese el título de su documento en la ventana emergente y pulse Guardar.
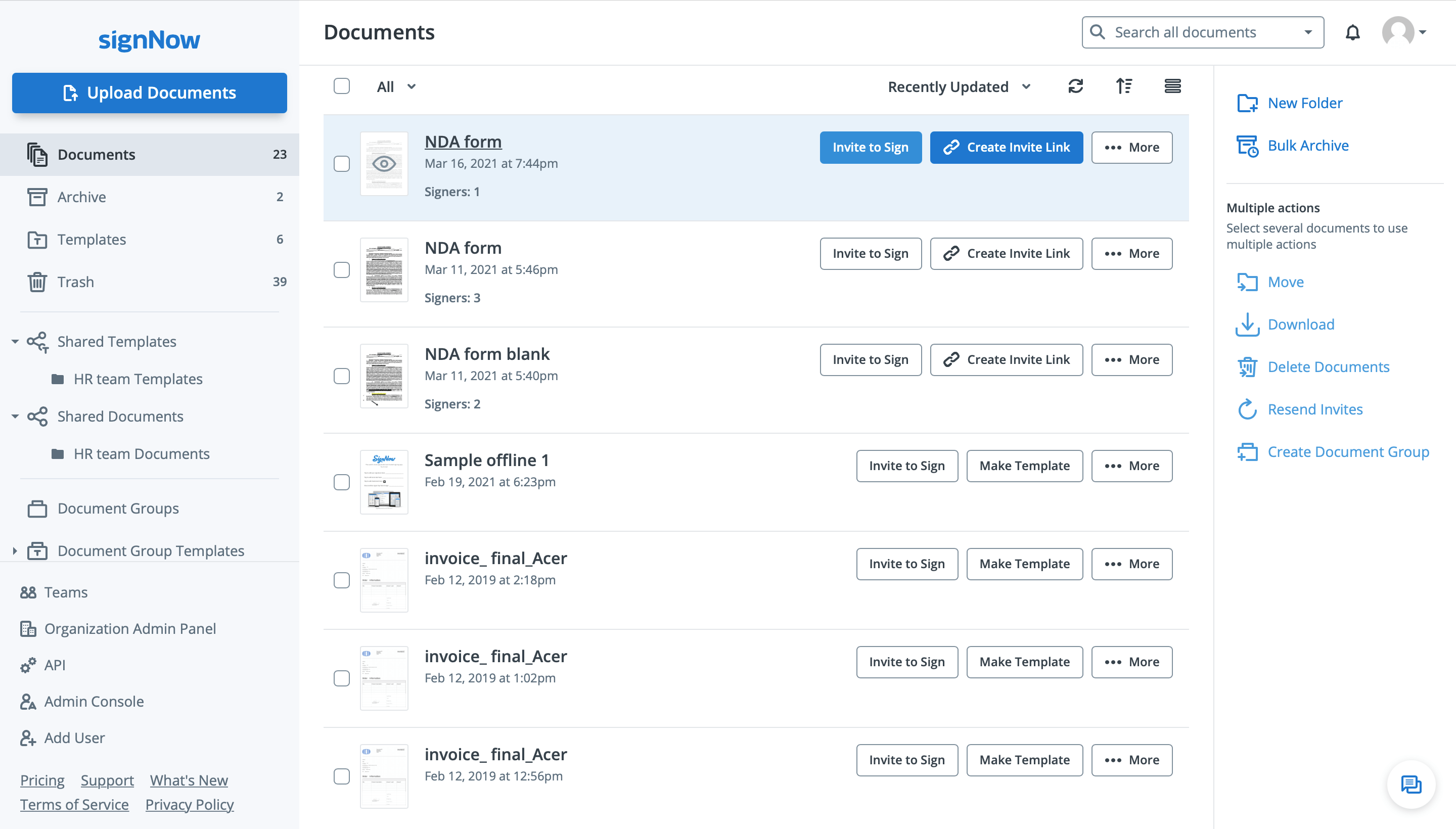
El documento que acaba de subir desde su galería aparecerá en la parte superior de su lista de ‘recientes’, dentro de la carpeta Documentos.
Vea las firmas electrónicas de airSlate SignNow en acción
Elige una mejor solución
Elimine la papeleo rutinario con airSlate SignNow
Solución de firma en línea
Creador de formularios rellenables
Plantillas de documentos
API de firma electrónica
Integraciones nativas en la aplicación
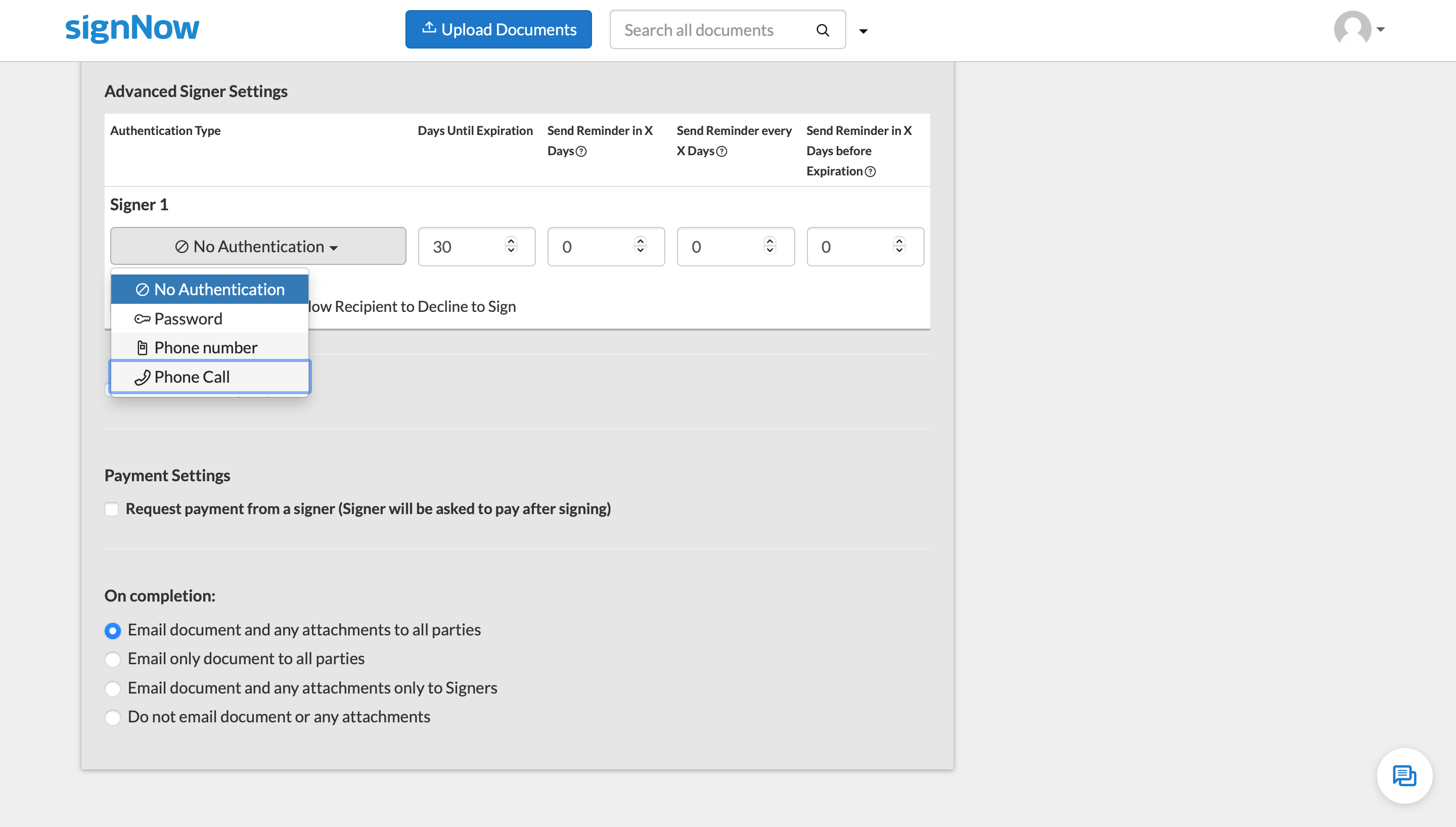
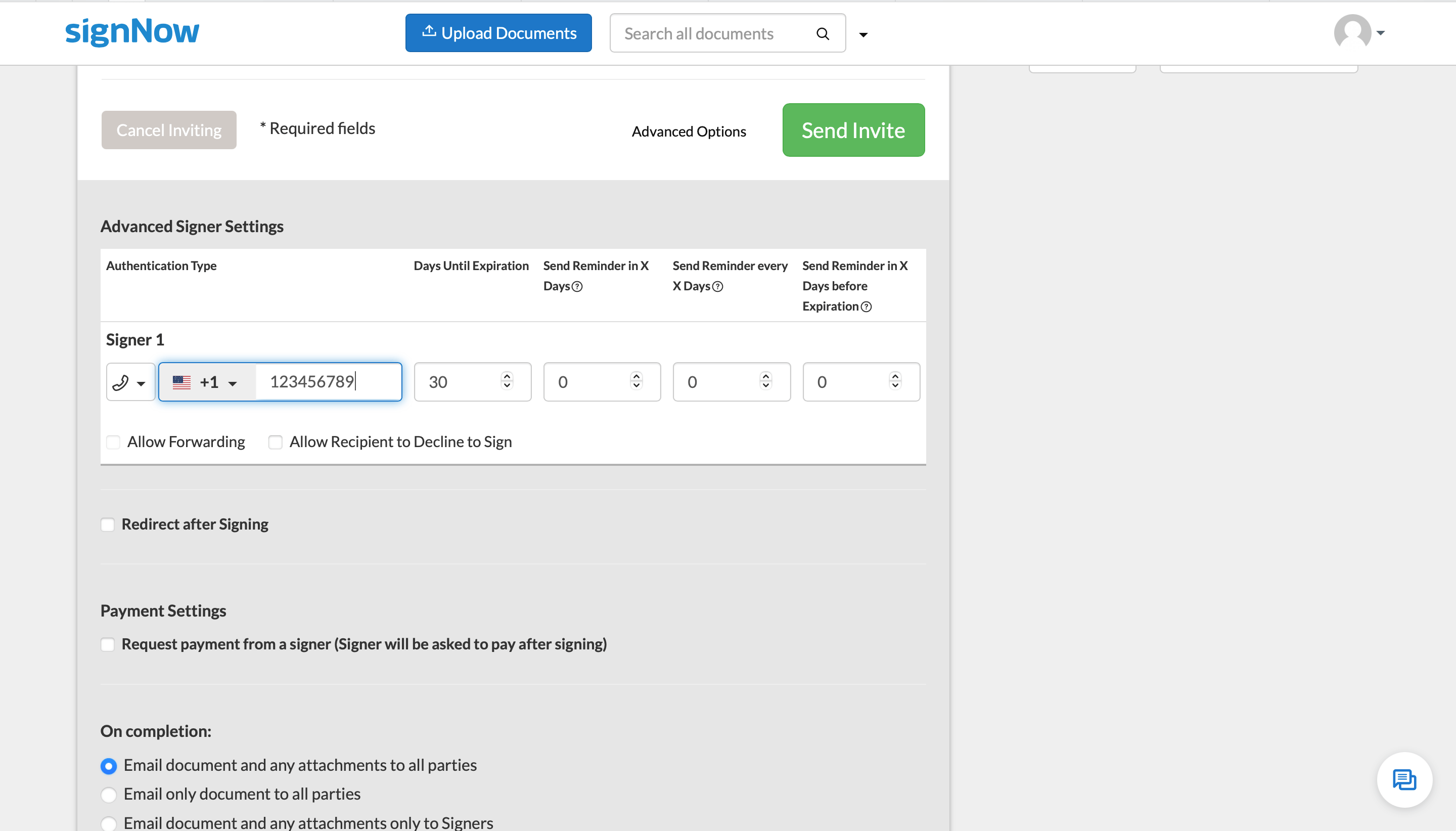
Capacidad para configurar autenticación de doble factor
Las reseñas de nuestros usuarios hablan por sí mismas






Soluciones de airSlate SignNow para una mayor eficiencia
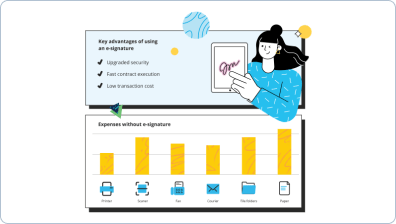
Por qué elegir airSlate SignNow
-
Prueba gratuita de 7 días. Elige el plan que necesitas y pruébalo sin riesgos.
-
Precios honestos para planes completos. airSlate SignNow ofrece planes de suscripción sin cargos adicionales ni tarifas ocultas al renovar.
-
Seguridad de nivel empresarial. airSlate SignNow te ayuda a cumplir con los estándares de seguridad globales.

Tu guía paso a paso — setup dual factor authentication
El beneficio conceptual crítico de la plataforma de firma electrónica airSlate SignNow para la automatización empresarial es un entorno de datos único que amplía la organización pero muestra un procedimiento comercial original. Puede habilitar el Tiempo de Inactividad de la Sesión en iOS para firmar de manera segura, proporcionar un enlace de invitación a sus socios, distribuidores o compañeros de equipo. Nuestro servicio líder en la industria simplifica las fases de auditoría y análisis. Permite gestionar el flujo de trabajo de manera mucho más flexible sin involucrar a personas adicionales. Puede perfeccionar indirectamente la interacción entre socios y habilitarlos para mejorar la experiencia del cliente.
Cómo habilitar el Tiempo de Inactividad de la Sesión en iOS para firmar de manera segura con airSlate SignNow:
- Cree su cuenta completamente gratis o inicie sesión si ya tiene una.
- Puede ingresar usando la funcionalidad de Inicio de Sesión Único si posee la cuenta de usuario de airSlate SignNow.|Si posee el perfil de airSlate SignNow, puede iniciar sesión usando la funcionalidad de Inicio de Sesión Único.
- Transfiera el archivo desde su dispositivo móvil o de escritorio.
- Además, puede cargar el archivo necesario desde su almacenamiento en la nube. Nuestra plataforma en línea es compatible con los repositorios más recomendados: Google Drive, OneDrive, DropBox.
- Realice fácilmente modificaciones en su plantilla usando nuestro avanzado pero fácil de usar Editor de PDF.
- Escriba el texto, incluya imágenes, deje sus anotaciones o comentarios, etc..
- Puede configurar elementos rellenables de varios tipos: texto o fecha específica, calculada o desplegable, y más.
- Organice y configure el requisito de adjunto.
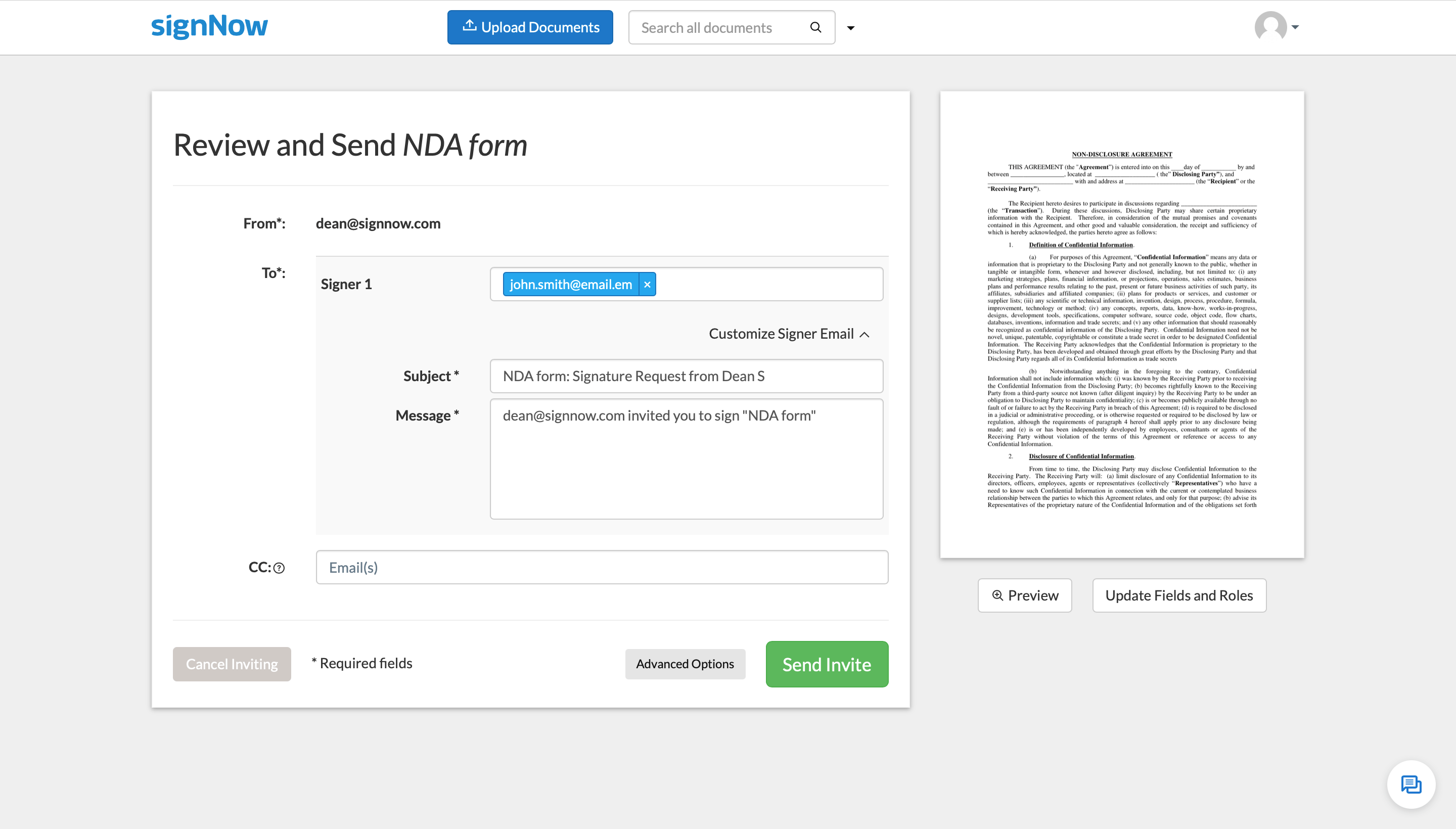
- Coloque el Campo de Firma para enviar por correo electrónico para firmar y recopilar firmas en persona o múltiples firmas electrónicas. Puede firmar el formulario usted mismo si es aplicable.
- Finalice los ajustes usando el botón Hecho y proceda a habilitar el Tiempo de Inactividad de la Sesión en iOS para firmar de manera segura.
airSlate SignNow es la mejor alternativa para la automatización de procedimientos empresariales y la solución para habilitar el Tiempo de Inactividad de la Sesión en iOS para firmar de manera segura y tareas rápidas para empresas de todos los niveles en términos de empleados y estructura. Los usuarios pueden colaborar tanto interna como externamente con proveedores y consumidores. ¡Descubra todas las ventajas ahora!
Cómo funciona
Vea resultados excepcionales Configuración de autenticación de doble factor para eSignature
¡Obtenga firmas legalmente vinculantes ahora!
Preguntas frecuentes
-
¿Cómo puedo subir documentos a airSlate SignNow desde un dispositivo Android?
Para subir un documento a tu cuenta de airSlate SignNow, toca el icono de más en la esquina inferior derecha de la pantalla principal de la aplicación móvil de airSlate SignNow. En el menú de carga, selecciona Cargar desde el dispositivo. También puedes optar por subir un documento desde tu almacenamiento en la nube o tomar una foto del documento en el momento y luego subirlo directamente a airSlate SignNow. -
¿Cómo capturo una foto de un documento con airSlate SignNow?
Toca el icono de más en la esquina inferior derecha de la pantalla principal de la aplicación móvil de airSlate SignNow y selecciona Cámara. Permite que airSlate SignNow acceda a la cámara digital de tu dispositivo y toma una foto de un documento. La foto se abrirá automáticamente en el editor donde podrás agregar anotaciones y campos rellenables. Cuando termines, toca el icono de marca de verificación en la esquina superior derecha para guardar el documento. -
¿Puedo agregar campos rellenables a documentos que capturé con una cámara?
Por supuesto, puedes hacer todo tipo de ediciones en las imágenes de tus documentos. Puedes agregar campos rellenables o anotar documentos (agregar texto, fecha, iniciales, firmas, etc.) igual que en los archivos PDF. -
¿Cómo creo una plantilla a partir de un documento en un dispositivo móvil?
Para hacer una plantilla, simplemente toca un documento y selecciona Hacer plantilla en el menú que aparece a continuación. Ingresa un nombre para la plantilla en la ventana emergente y toca Crear. Tu plantilla ya está lista. -
¿Puedo firmar electrónicamente documentos en un dispositivo móvil?
Sí, airSlate SignNow te permite firmar electrónicamente y gestionar documentos desde cualquier dispositivo, ya sea tu PC o smartphone. Si eres usuario móvil, es recomendable descargar la aplicación de airSlate SignNow para Android o iOS desde Google Play Market o Apple Store, respectivamente. -
¿Cómo firmo electrónicamente documentos en un dispositivo móvil?
Sube tu documento a airSlate SignNow, tócala y selecciona Abrir en el editor. Una vez abierto, toca Firma en la barra de herramientas inferior (la pestaña Herramientas) y luego toca en cualquier parte del documento para colocar tu firma. Para guardar tu documento, toca el icono de marca de verificación en la esquina superior derecha de la interfaz del editor. -
¿Cómo envío un documento para firma electrónica en un dispositivo móvil?
Sube un documento a tu cuenta usando la aplicación móvil de airSlate SignNow, tócala y selecciona Invitar a firmar. Luego, ingresa la dirección de correo electrónico del destinatario y pulsa Enviar. Tu firmante recibirá una invitación en formato libre para que pueda colocar una firma en cualquier parte del documento. También puedes agregar campos de firma al documento y asignar roles de firma en el editor antes de enviar la invitación. En este caso, tus destinatarios solo podrán colocar sus firmas en los cuadros correspondientes. -
¿Cómo creo mi firma electrónica en un dispositivo móvil?
Sube un documento a tu cuenta usando la aplicación móvil de airSlate SignNow, ábrelo en el editor, selecciona Firma en la barra de herramientas inferior y toca en cualquier parte del documento. Si es la primera vez que firmas electrónicamente un documento con airSlate SignNow, verás un menú para crear la firma. Toca el botón Agregar firma nueva y dibuja tu firma usando la pantalla táctil. Para guardar la firma, toca el icono de marca de verificación en la esquina superior derecha. -
¿Cómo configuro la autenticación de dos factores para mi ID de Apple?
Ve a Configuración > [tu nombre]. Si usas iOS 10.2 o anterior, ve a Configuración > iCloud y toca tu ID de Apple. Toca Contraseña y seguridad. Si se te solicita, ingresa la contraseña de tu ID de Apple. Toca Activar autenticación de dos factores. -
¿Cómo habilito 2fa?
Inicia sesión en tu cuenta en EpicGames.com y ve a Configuración de la cuenta. Allí, haz clic en Contraseña y seguridad. En la parte inferior de esa página, verás una opción llamada "Autenticación de dos factores". Haz clic para habilitar ya sea una aplicación de autenticación o la opción de autenticación por correo electrónico. -
¿Cómo habilito 2fa en Fortnite?
Ve a epicgames.com e inicia sesión en tu cuenta. Abre la configuración de la cuenta pasando el cursor sobre tu nombre de usuario en la esquina superior derecha. Selecciona contraseña y seguridad. En la parte inferior, haz clic en el botón que dice habilitar inicio de sesión de dos factores. -
¿Cómo activo 2fa en Xbox?
Inicia sesión en Xbox Live con tu cuenta de Microsoft como de costumbre. Ve a la página de Configuración de seguridad. Bajo verificación en dos pasos, selecciona "Configurar verificación en dos pasos" para activarla. ¡Casi terminas! Ingresa la información solicitada para finalizar el proceso. -
¿Cómo habilito la autenticación de dos factores en mi iPhone?
Ve a Configuración > [tu nombre]. Si usas iOS 10.2 o anterior, ve a Configuración > iCloud y toca tu ID de Apple. Toca Contraseña y seguridad. Si se te solicita, ingresa la contraseña de tu ID de Apple. Toca Activar autenticación de dos factores. -
¿Qué es 2fa en Fortnite?
Los jugadores de "Fortnite" pueden activar la autenticación de dos factores (2FA) para agregar una capa adicional de seguridad a su cuenta de Epic Games. Habilitar 2FA también desbloqueará un baile especial, Boogiedown, para "Fortnite: Battle Royale". -
¿Cómo se autentican las firmas electrónicas?
Opciones de autenticación multifactor para firmas electrónicas. La autenticación de firma electrónica requiere que los usuarios prueben su identidad. airSlate SignNow ofrece muchas opciones de autenticación, incluyendo correo electrónico, SMS y preguntas basadas en conocimientos. Usar múltiples capas de autenticación reduce el riesgo de repudiación. -
¿Las firmas electrónicas son vinculantes?
Ley ESIGN: 5 factores que hacen que las firmas electrónicas sean legalmente vinculantes en EE. UU. ... Sin embargo, 17 años después, la mayoría de las empresas aún no comprenden la legalidad de las firmas electrónicas. Durante las consultas, nuestros clientes nos preguntan con frecuencia cómo pueden asegurarse de que sus documentos firmados electrónicamente sean válidos en un tribunal de justicia ...
Lo que dicen los usuarios activos — setup dual factor authentication
Preguntas frecuentes
¿Cómo generas un documento y aplicas una firma electrónica en él?
¿Cómo agrego una firma electrónica a un documento de Word?
¿Cómo puedo hacer que un PDF sea fácil de firmar?
Obtén más para setup dual factor authentication
Todo sobre la firma electrónica

Descubre otros setup dual factor authentication
- Desbloqueando la Legitimidad de la Firma Electrónica ...
- Legitimidad de la Firma Electrónica para Servicios ...
- Legalidad de la eSignature para el Servicio al Cliente ...
- Desbloquea el Poder de la Legalidad de la eFirma para ...
- Desbloqueando la Legitimidad de la eSignature para la ...
- Desbloquea el Poder de la Legitimidad de la eFirma para ...
- Desbloqueando el Poder de la Legalidad de la eFirma ...
- Impulsa tu Adquisición con eFirmas Legítimas en ...
- Desbloquea la Legitimidad de la eSignature para la ...
- Asegurando la Legalidad de la Firma Digital para ...
- La Guía Definitiva sobre la Legalidad de la Firma ...
- Asegurando la Legalidad de las Firmas Digitales para la ...
- Desbloquea el Poder de la Legalidad de la Firma Digital ...
- Legalidad de la Firma Digital para Aseguramiento de ...
- Legitimidad de la Firma Digital para la Adquisición en ...
- Desbloquea la Legitimidad de la Firma Digital para la ...
- Legalidad de la Firma Electrónica para TI en Canadá - ...
- Desbloqueando el Poder de la Legalidad de la Firma ...
- Legalidad de la Firma Electrónica para Ventas en ...
- Legalidad de la Firma Electrónica para Aseguramiento ...










































