Unlocking Digital Signature Legitimacy for Assignment of Intellectual Property in UAE
- Quick to start
- Easy-to-use
- 24/7 support
Simplified document journeys for small teams and individuals




We spread the word about digital transformation
Why choose airSlate SignNow
-
Free 7-day trial. Choose the plan you need and try it risk-free.
-
Honest pricing for full-featured plans. airSlate SignNow offers subscription plans with no overages or hidden fees at renewal.
-
Enterprise-grade security. airSlate SignNow helps you comply with global security standards.







Your complete how-to guide - digital signature legitimacy for assignment of intellectual property in uae
Digital Signature Legitimacy for Assignment of Intellectual Property in UAE
In the UAE, digital signature legitimacy is crucial for the assignment of intellectual property. Using airSlate SignNow provides a secure and legally recognized platform for businesses to sign and send documents with ease. The following steps will guide you through the process.
User Flow:
- Launch the airSlate SignNow web page in your browser.
- Sign up for a free trial or log in.
- Upload a document you want to sign or send for signing.
- If you're going to reuse your document later, turn it into a template.
- Open your file and make edits: add fillable fields or insert information.
- Sign your document and add signature fields for the recipients.
- Click Continue to set up and send an eSignature invite.
airSlate SignNow benefits businesses by empowering them to send and eSign documents effortlessly with a cost-effective solution. It offers great ROI with a feature-rich set that fits within budget, easy scalability for small and mid-sized businesses, transparent pricing without hidden fees, and superior 24/7 support for all paid plans.
Experience the convenience and efficiency of airSlate SignNow today for seamless document signing and sharing.
How it works
Rate your experience
What is the digital signature legitimacy for assignment of intellectual property in UAE
The digital signature legitimacy for the assignment of intellectual property in the UAE refers to the legal recognition and acceptance of electronic signatures in the transfer of intellectual property rights. This legitimacy ensures that digital signatures hold the same weight as traditional handwritten signatures, provided they meet specific legal requirements. In the UAE, the Electronic Transactions and Commerce Law governs the use of digital signatures, establishing that they can be used to authenticate documents related to intellectual property assignments, such as patents, trademarks, and copyrights.
How to use the digital signature legitimacy for assignment of intellectual property in UAE
Using digital signatures for the assignment of intellectual property in the UAE involves several steps. First, the parties involved must agree on the terms of the assignment and prepare the necessary documentation. Once the document is ready, it can be uploaded to an eSignature platform like airSlate SignNow. Users can fill out the document electronically, ensuring all required fields are completed. After that, the document can be sent for signature to the relevant parties. Each party can review and eSign the document securely, ensuring compliance with legal standards.
Steps to complete the digital signature legitimacy for assignment of intellectual property in UAE
To complete the digital signature legitimacy for the assignment of intellectual property, follow these steps:
- Draft the assignment agreement, detailing the intellectual property being transferred.
- Upload the document to airSlate SignNow, where you can fill in any necessary information.
- Send the document to the other party or parties for their review and signature.
- Each party should eSign the document using their secure digital signature.
- Once all signatures are collected, the completed document can be securely stored or shared as needed.
Legal use of the digital signature legitimacy for assignment of intellectual property in UAE
For a digital signature to be legally valid in the assignment of intellectual property in the UAE, it must comply with the Electronic Transactions and Commerce Law. This includes ensuring that the digital signature is unique to the signatory, capable of identifying the signatory, and created using secure means. Additionally, the signatory must have sole control over the signature creation data, and the signature must be linked to the document in such a way that any changes to the document invalidate the signature. Adhering to these guidelines ensures the legal enforceability of the assignment agreement.
Security & Compliance Guidelines
When using digital signatures for the assignment of intellectual property, it is essential to adhere to security and compliance guidelines. This includes using a reputable eSignature platform like airSlate SignNow that complies with industry standards for data protection. Ensure that all documents are encrypted during transmission and storage. Additionally, implement access controls to restrict who can view and sign the documents. Regular audits of the eSignature process can also help maintain compliance with legal requirements and ensure that all parties are protected throughout the transaction.
Sending & Signing Methods (Web / Mobile / App)
airSlate SignNow offers various methods for sending and signing documents, making it convenient for users to manage their intellectual property assignments. Users can access the platform via web browsers, mobile devices, or dedicated applications. To send a document, simply upload it to the platform, specify the recipients, and initiate the signing process. Recipients can then review and eSign the document using their preferred method, whether on a desktop or mobile device. This flexibility ensures that all parties can participate in the signing process efficiently, regardless of their location.
-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
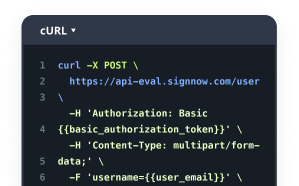
Intuitive UI and API. Sign and send documents from your apps in minutes.
FAQs
-
What is the digital signature legitimacy for assignment of intellectual property in UAE?
In the UAE, digital signatures are recognized as legally binding under the Electronic Transactions and Commerce Law. This means that the digital signature legitimacy for assignment of intellectual property in UAE is upheld, ensuring that electronic agreements are enforceable in a court of law.
-
How does airSlate SignNow ensure the security of digital signatures?
airSlate SignNow employs advanced encryption and authentication methods to secure digital signatures. This ensures the digital signature legitimacy for assignment of intellectual property in UAE, protecting sensitive information and maintaining the integrity of signed documents.
-
What are the benefits of using digital signatures for intellectual property assignments?
Using digital signatures streamlines the process of assigning intellectual property, making it faster and more efficient. The digital signature legitimacy for assignment of intellectual property in UAE also reduces the risk of fraud and enhances the overall security of the transaction.
-
Are there any specific features in airSlate SignNow that support intellectual property assignments?
Yes, airSlate SignNow offers features such as customizable templates, audit trails, and secure storage that are particularly beneficial for intellectual property assignments. These features enhance the digital signature legitimacy for assignment of intellectual property in UAE, ensuring compliance and ease of use.
-
What is the pricing structure for airSlate SignNow?
airSlate SignNow offers flexible pricing plans that cater to businesses of all sizes. By providing a cost-effective solution, it supports the digital signature legitimacy for assignment of intellectual property in UAE, making it accessible for various organizations.
-
Can airSlate SignNow integrate with other software tools?
Yes, airSlate SignNow integrates seamlessly with various software tools, including CRM and document management systems. This integration enhances the digital signature legitimacy for assignment of intellectual property in UAE by allowing for a more streamlined workflow.
-
How can I ensure compliance with UAE laws when using digital signatures?
To ensure compliance with UAE laws, it is essential to use a trusted digital signature provider like airSlate SignNow. Their platform guarantees the digital signature legitimacy for assignment of intellectual property in UAE, helping you meet legal requirements effortlessly.
Related searches to digital signature legitimacy for assignment of intellectual property in uae
Join over 28 million airSlate SignNow users
Get more for digital signature legitimacy for assignment of intellectual property in uae
- ESignature Licitness for Affidavit of Identity in ...
- Unlock the Legality of eSignatures for Affidavit of ...
- Unlock the eSignature Licitness for Affidavit of ...
- ESignature licitness for Affidavit of Identity in UAE
- Unlock the Power of eSignature Licitness for Affidavit ...
- Unlock eSignature Licitness for Affidavit of Service in ...
- Secure eSignature Licitness for Affidavit of Service in ...
- Unlock the Power of eSignature Licitness for Affidavit ...