Elevate the Legitimacy of Affidavit of Identity in India with Digital Signature Licitness
- Quick to start
- Easy-to-use
- 24/7 support
Simplified document journeys for small teams and individuals




We spread the word about digital transformation
Why choose airSlate SignNow
-
Free 7-day trial. Choose the plan you need and try it risk-free.
-
Honest pricing for full-featured plans. airSlate SignNow offers subscription plans with no overages or hidden fees at renewal.
-
Enterprise-grade security. airSlate SignNow helps you comply with global security standards.







Your complete how-to guide - digital signature licitness for affidavit of identity in india
Digital Signature Licitness for Affidavit of Identity in India
In India, digital signature licitness is crucial for the Affidavit of Identity. Using airSlate SignNow, individuals and businesses can easily create and sign digital documents with legal validity. This guide will walk you through the steps to ensure a smooth signing process.
How to Sign Documents Using airSlate SignNow:
- Launch the airSlate SignNow web page in your browser.
- Sign up for a free trial or log in.
- Upload a document you want to sign or send for signing.
- If you're going to reuse your document later, turn it into a template.
- Open your file and make edits: add fillable fields or insert information.
- Sign your document and add signature fields for the recipients.
- Click Continue to set up and send an eSignature invite.
airSlate SignNow empowers businesses by offering an easy-to-use and cost-effective solution for sending and signing documents. With great ROI, tailored features for SMBs and Mid-Market, transparent pricing, and superior 24/7 support for all paid plans, airSlate SignNow stands out as a trusted eSignature platform.
Experience the benefits of airSlate SignNow today and streamline your document signing process!
How it works
Rate your experience
What is the digital signature licitness for affidavit of identity in India
The digital signature licitness for affidavit of identity in India refers to the legal recognition and validity of electronic signatures used in affidavits. In India, digital signatures are governed by the Information Technology Act, 2000, which outlines the framework for electronic signatures and their admissibility in legal proceedings. This ensures that an affidavit of identity signed electronically holds the same legal weight as a traditional handwritten signature, provided it meets specific criteria set forth by the law.
How to use the digital signature licitness for affidavit of identity in India
To effectively use the digital signature licitness for an affidavit of identity in India, individuals must first ensure they have a valid digital signature certificate issued by a certifying authority. Once the certificate is obtained, users can fill out the affidavit form electronically. After completing the form, they can apply their digital signature using eSignature software, such as airSlate SignNow, which simplifies the process of signing and sending documents securely. This electronic workflow enhances efficiency and ensures compliance with legal standards.
Steps to complete the digital signature licitness for affidavit of identity in India
Completing the digital signature licitness for an affidavit of identity involves several key steps:
- Obtain a digital signature certificate from a recognized certifying authority.
- Prepare the affidavit of identity document in a digital format.
- Use airSlate SignNow to upload the document and fill in the required details.
- Apply your digital signature to the document.
- Review the completed document for accuracy.
- Save and securely share the signed affidavit as needed.
Legal use of the digital signature licitness for affidavit of identity in India
The legal use of digital signatures for affidavits of identity in India is well-established under the Information Technology Act. Digital signatures must be created using a secure method that ensures authenticity and integrity. This legal framework allows individuals and businesses to submit affidavits electronically, streamlining processes in various sectors, including banking, real estate, and government services. It is essential for users to understand the legal implications and requirements of using digital signatures to ensure compliance.
Security & Compliance Guidelines
When using digital signatures for affidavits of identity, it is crucial to adhere to security and compliance guidelines to protect sensitive information. Users should ensure that their digital signature certificates are obtained from trusted certifying authorities. Additionally, employing secure eSignature platforms like airSlate SignNow helps safeguard documents during the signing process. Regularly updating security protocols and educating users on best practices for electronic signatures can further enhance compliance and reduce risks associated with digital transactions.
Sending & Signing Methods (Web / Mobile / App)
airSlate SignNow offers versatile options for sending and signing documents, accommodating various user preferences. Users can access the platform via web browsers, mobile devices, or dedicated applications. This flexibility allows individuals to fill and sign affidavits of identity from anywhere, at any time. The intuitive interface guides users through the signing process, ensuring that they can complete their documents efficiently and securely, regardless of the method chosen.
-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
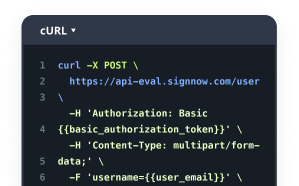
Intuitive UI and API. Sign and send documents from your apps in minutes.
FAQs
-
What is the digital signature licitness for affidavit of identity in India?
The digital signature licitness for affidavit of identity in India refers to the legal validity of electronic signatures used in affidavits. Under the Information Technology Act, 2000, digital signatures are recognized as legally binding, ensuring that your affidavit of identity is secure and compliant with Indian law.
-
How does airSlate SignNow ensure the digital signature licitness for affidavit of identity in India?
airSlate SignNow complies with the legal requirements set forth by the Indian government for digital signatures. Our platform uses advanced encryption and authentication methods to ensure that your affidavit of identity is signed securely and is legally valid in India.
-
What are the benefits of using airSlate SignNow for digital signatures?
Using airSlate SignNow for digital signatures offers numerous benefits, including enhanced security, faster processing times, and reduced paperwork. This ensures that your affidavit of identity is executed efficiently while maintaining the digital signature licitness for affidavit of identity in India.
-
Is there a cost associated with using airSlate SignNow for digital signatures?
Yes, airSlate SignNow offers various pricing plans to cater to different business needs. Our cost-effective solutions ensure that you can obtain digital signature licitness for affidavit of identity in India without breaking the bank, making it accessible for businesses of all sizes.
-
Can I integrate airSlate SignNow with other applications?
Absolutely! airSlate SignNow offers seamless integrations with various applications, enhancing your workflow. This allows you to manage documents and ensure digital signature licitness for affidavit of identity in India efficiently within your existing systems.
-
What features does airSlate SignNow provide for managing digital signatures?
airSlate SignNow provides features such as document templates, real-time tracking, and customizable workflows. These features help streamline the signing process while ensuring the digital signature licitness for affidavit of identity in India, making it easier for users to manage their documents.
-
How secure is airSlate SignNow for digital signatures?
Security is a top priority for airSlate SignNow. We utilize advanced encryption protocols and secure servers to protect your documents and ensure the digital signature licitness for affidavit of identity in India, giving you peace of mind when signing important documents.