eSign Y Establecer Requisitos De Contraseña. Utilice Herramientas De Firma Electrónica Que Funcionan Donde Usted Trabaja.
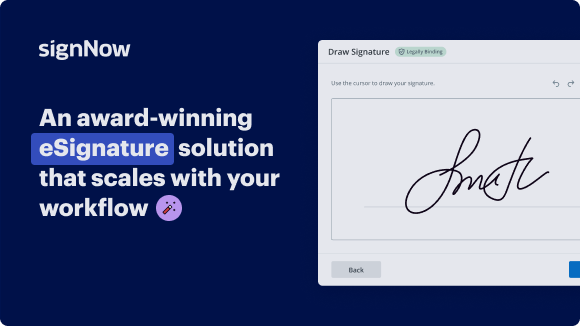
Mejore su flujo de trabajo de documentos con airSlate SignNow
Flujos de trabajo de firma electrónica ágiles
Visibilidad rápida del estado del documento
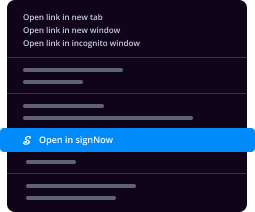
Configuración de integración fácil y rápida
Firma electrónica y establecimiento de requisitos de contraseña en cualquier dispositivo
Registro de auditoría completo
Normas de seguridad rigurosas
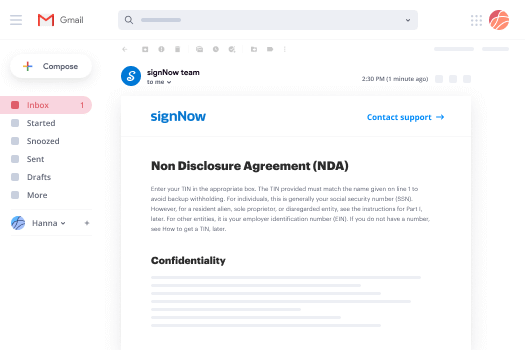
Vea las firmas electrónicas de airSlate SignNow en acción
Soluciones de airSlate SignNow para una mayor eficiencia
Las reseñas de nuestros usuarios hablan por sí mismas






Por qué elegir airSlate SignNow
-
Prueba gratuita de 7 días. Elige el plan que necesitas y pruébalo sin riesgos.
-
Precios honestos para planes completos. airSlate SignNow ofrece planes de suscripción sin cargos adicionales ni tarifas ocultas al renovar.
-
Seguridad de nivel empresarial. airSlate SignNow te ayuda a cumplir con los estándares de seguridad globales.

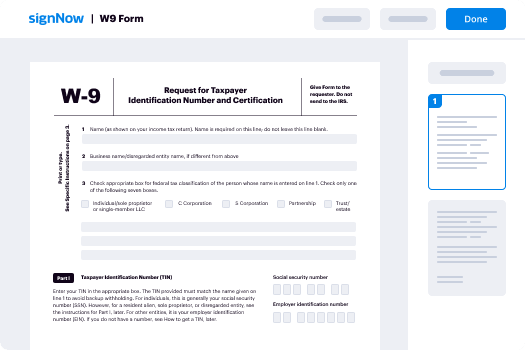
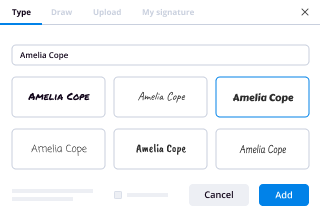
Tu guía paso a paso — e sign and set password requirements
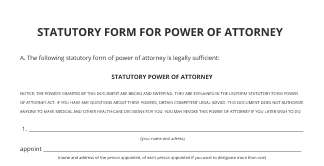
eSign y establezca requisitos de contraseña. Obtenga el máximo beneficio del sistema de firma electrónica más confiable y seguro. Simplifique sus acuerdos digitales empleando airSlate SignNow. Optimice los flujos de trabajo para todo, desde registros de personal básicos hasta acuerdos complejos y formularios de compra.
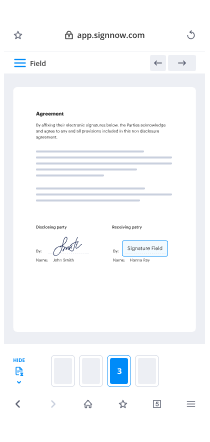
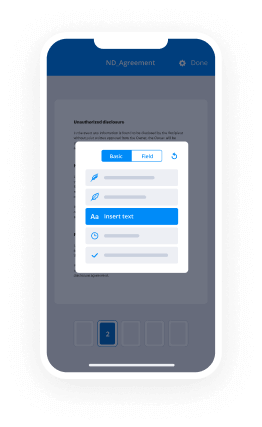
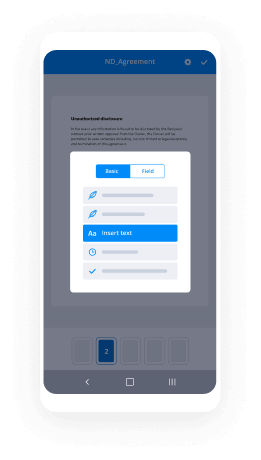
Sepa cómo eSign y establezca requisitos de contraseña:
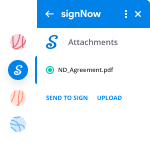
- Agregue una serie de documentos desde su unidad o almacenamiento en la nube.
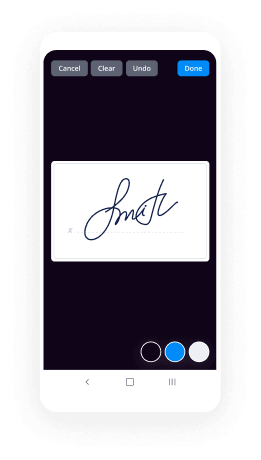
- Arrastre y suelte cuadros rellenables personalizados (firma, texto, fecha/hora).
- Modifique el tamaño de los campos, tocándolos y seleccionando Ajustar tamaño.
- Inserte casillas de verificación y listas desplegables, y grupos de botones de opción.
- Agregue firmantes y solicite adjuntos.
- eSign y establezca requisitos de contraseña.
- Agregue la fórmula donde necesita que aparezca el campo.
- Agregue comentarios y anotaciones para los destinatarios en cualquier parte de la página.
- Apruebe todos los ajustes haciendo clic en HECHO.
Conecte usuarios de fuera y dentro de su organización para trabajar electrónicamente en documentos importantes y eSign y establecer requisitos de contraseña en cualquier momento y en cualquier sistema usando airSlate SignNow. Puede monitorear cada actividad realizada en sus documentos, recibir alertas y un estado de auditoría. Manténgase enfocado en su negocio y en las interacciones con los clientes, mientras comprende que sus datos son precisos y seguros.
Cómo funciona
Funciones de airSlate SignNow que los usuarios adoran
Vea resultados excepcionales eSign y establecer requisitos de contraseña. Utilice herramientas de firma electrónica que funcionan donde usted trabaja.
¡Obtenga firmas legalmente vinculantes ahora!
Preguntas frecuentes
-
¿Qué es el pin de eSign?
eSign permite a bancos y uniones de crédito asociar un número PIN con cada documento de préstamo. El PIN puede ser emitido por mensaje de texto, por correo electrónico o verbalmente. Los destinatarios no pueden acceder al documento sin el PIN. -
¿Qué es un PIN de eSign?
A diferencia de airSlate SignNow, los documentos electrónicos están sellados después de firmar. Son imposibles de alterar de ninguna manera. eSign permite a bancos y uniones de crédito asociar un número PIN con cada documento de préstamo. El PIN puede ser emitido por mensaje de texto, por correo electrónico o verbalmente. Los destinatarios no pueden acceder al documento sin el PIN. -
¿Qué es el PIN de E sign?
Estudiante - Creando PIN de eSign. ... El enlace Crear mi PIN de eSign está en la parte inferior de la pantalla de revisión y firma en el formulario web del estudiante que están completando en StudentForms. La primera vez que un estudiante firma electrónicamente un formulario web, debe crear un PIN de eSign para firmar electrónicamente. -
¿Cómo restablezco mi contraseña de eSign?
Luego haga clic en el enlace 'Olvidé mi contraseña' en el cuadro "Iniciar sesión en su cuenta". Se abrirá un cuadro de texto y deberá ingresar la dirección de correo electrónico que usa para iniciar sesión en airSlate SignNow. Haga clic en Enviar para recibir un correo electrónico de airSlate SignNow. Establezca su nueva contraseña usando el enlace proporcionado en el correo electrónico para iniciar sesión. -
¿Cómo firmo electrónicamente mi FAFSA?
Cuando firma su solicitud electrónicamente usando su FSA ID, su solicitud se procesa en 3-5 días. Para firmar su solicitud electrónicamente, haga clic en el botón Iniciar sesión en la página principal de FAFSA en línea y luego en el botón Proporcionar firmas. -
¿Ambos padres deben firmar el FAFSA?
¿Ambos padres necesitan un FSA ID? Si usted es un padre de un estudiante dependiente, necesitará su propio FSA ID si desea firmar electrónicamente el formulario FAFSA de su hijo. Si tiene más de un hijo que asiste a la universidad, puede usar el mismo FSA ID para firmar todas las solicitudes, pero cada hijo debe tener su propio FSA ID. -
¿Puedo enviar mi FAFSA sin la firma de un padre?
Si su padre aún no tiene un FSA ID, puede crear uno. ... Si no tiene una impresora ni un FSA ID, puede seleccionar la opción de firma Enviar sin firmas y enviar su FAFSA. Su solicitud será procesada parcialmente sin firmas.
Lo que dicen los usuarios activos — e sign and set password requirements
Preguntas frecuentes
¿Cómo agrego una firma electrónica a un documento de Word?
¿Qué es una firma electrónica y digital?
¿Cómo puedo agregar una firma electrónica a un PDF para que otros puedan firmarlo?
Obtén más para e sign and set password requirements
- Firma electrónica para gestión de clientes potenciales para servicios financieros
- Firma electrónica para gestión de Leads para Gobierno
- Firma electrónica para gestión de clientes potenciales en atención médica
- Firma electrónica para gestión de Leads para Educación Superior
- Firma electrónica para gestión de clientes potenciales para la industria de seguros
- Firma electrónica para gestión de clientes potenciales para servicios legales
- Firma electrónica para gestión de Leads para Ciencias de la Vida
- Firma electrónica para gestión de clientes potenciales para Hipotecas
Todo sobre la firma electrónica