Store Link Log with SignNow's Secure eSignature Solution
Improve your document workflow with airSlate SignNow
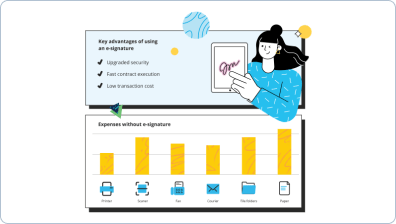
Versatile eSignature workflows
airSlate SignNow is a scalable solution that grows with your teams and organization. Build and customize eSignature workflows that fit all your business needs.
Fast visibility into document status
View and download a document’s history to monitor all alterations made to it. Get immediate notifications to understand who made what edits and when.
Simple and fast integration set up
airSlate SignNow effortlessly fits into your existing systems, enabling you to hit the ground running instantly. Use airSlate SignNow’s robust eSignature capabilities with hundreds of well-known applications.
Store link log on any device
Avoid the bottlenecks associated with waiting for eSignatures. With airSlate SignNow, you can eSign documents immediately using a desktop, tablet, or mobile phone
Detailed Audit Trail
For your legal protection and general auditing purposes, airSlate SignNow includes a log of all changes made to your documents, featuring timestamps, emails, and IP addresses.
Rigorous protection standards
Our top priorities are securing your documents and sensitive data, and ensuring eSignature authentication and system protection. Remain compliant with market standards and polices with airSlate SignNow.
Vea las firmas electrónicas de airSlate SignNow en acción
Soluciones de airSlate SignNow para una mayor eficiencia
Mantén los contratos protegidos
Mejora la seguridad de tus documentos y mantén los contratos a salvo de accesos no autorizados con opciones de autenticación de dos factores. Pide a tus destinatarios que demuestren su identidad antes de abrir un contrato para store link log.
Mantente móvil mientras firmas electrónicamente
Instala la aplicación de airSlate SignNow en tu dispositivo iOS o Android y cierra acuerdos desde cualquier lugar, 24/7. Trabaja con formularios y contratos incluso sin conexión y store link log más tarde cuando se restablezca tu conexión a internet.
Integra firmas electrónicas en tus aplicaciones empresariales
Incorpora airSlate SignNow en tus aplicaciones empresariales para store link log rápidamente sin cambiar entre ventanas y pestañas. Aprovecha las integraciones de airSlate SignNow para ahorrar tiempo y esfuerzo al firmar formularios electrónicamente en solo unos clics.
Genera formularios rellenables con campos inteligentes
Actualiza cualquier documento con campos rellenables, hazlos obligatorios u opcionales, o añade condiciones para que aparezcan. Asegúrate de que los firmantes completen tu formulario correctamente asignando roles a los campos.
Cierra acuerdos y recibe pagos rápidamente
Recoge documentos de clientes y socios en minutos en lugar de semanas. Pide a tus firmantes que store link log e incluye un campo de solicitud de pago en tu muestra para cobrar automáticamente durante la firma del contrato.
Recoger firmas
24x
más rápido
Reduce los costos en
$30
por documento
Guardar hasta
40h
por empleado / mes
Las reseñas de nuestros usuarios hablan por sí mismas






prepárate para obtener más
Por qué elegir airSlate SignNow
-
Prueba gratuita de 7 días. Elige el plan que necesitas y pruébalo sin riesgos.
-
Precios honestos para planes completos. airSlate SignNow ofrece planes de suscripción sin cargos adicionales ni tarifas ocultas al renovar.
-
Seguridad de nivel empresarial. airSlate SignNow te ayuda a cumplir con los estándares de seguridad globales.

Tu guía paso a paso — store link log
Store link log. Get greatest performance from the most trusted and secure eSignature platform. Enhance your digital deals using airSlate SignNow. Automate workflows for everything from basic staff records to complex agreements and purchase templates.
Know how to Store link log:
- Import multiple files from your device or cloud storage.
- Drag & drop custom fillable boxes (signature, text, date/time).
- Modify the fields sizing, by tapping it and choosing Adjust Size.
- Place dropdowns and checkboxes, and radio button groups.
- Add signers and request attachments.
- Store link log.
- Include the formula where you need the field to appear.
- Apply remarks and annotations for the recipients anywhere on the page.
- Save all modifications by clicking DONE.
Connect users from outside and inside your company to electronically work on important signNowwork and Store link log anytime and on any device using airSlate SignNow. You may monitor every activity carried out to your samples, get notifications an audit report. Stay focused on your business and consumer partnerships while with the knowledge that your data is precise and safe.
Cómo funciona
Almacena y comparte documentos de forma segura
Guarda tus cambios y compártelos
Reenvía el formulario firmado a tu destinatario
Funciones de airSlate SignNow que los usuarios adoran
Vea resultados excepcionales Store Link Log with signNow's Secure eSignature Solution
prepárate para obtener más
¡Obtenga firmas legalmente vinculantes ahora!
Preguntas frecuentes
-
How can I log into my iTunes account?
Click Sign In. iTunes & App Store: Go to iTunes > Account > Sign In. Enter your Apple ID and password. Click Sign In. -
Why has my account been disabled in the app store?
Here are a few possible reasons why your account may have been disabled: Repeatedly entering an incorrect Apple ID and password. Not using your Apple account for an extended amount of time. Billing issues such as unpaid iTunes or App Store orders. -
Why is my account disabled in the app store?
Here are a few possible reasons why your account may have been disabled: Repeatedly entering an incorrect Apple ID and password. Not using your Apple account for an extended amount of time. Billing issues such as unpaid iTunes or App Store orders. -
Why does it say my account is disabled in the app store?
Here are a few possible reasons why your account may have been disabled: Repeatedly entering an incorrect Apple ID and passwo
Lo que dicen los usuarios activos — store link log
Preguntas frecuentes
¿Cómo firmo una página en un PDF y la envío de vuelta?
airSlate SignNow te da la capacidad de insertar tu firma en las páginas que la requieren. Puedes firmar una página de PDF, cada página o varias páginas, usando el elemento Mi Firma. Coloca tu firma donde y cuántas veces necesites. Después de crear tu firma una vez, no es necesario generarla de nuevo cada vez. Tu firma electrónica se guarda automáticamente, lo que significa que puedes reutilizarla con un solo clic. Una vez que hayas firmado el documento, simplemente envíalo por email a quien te lo envió.
¿Cómo firmar un PDF y enviarlo por correo?
Si el remitente tiene una cuenta de airSlate SignNow, esto sucederá automáticamente. Tan pronto como firmes un documento, se enviará una copia ejecutada a ti, al remitente y a cualquier otra parte añadida. Sin embargo, si recibes un documento en tu correo electrónico, tienes algunos pasos adicionales que hacer. Primero, necesitas subir un PDF a tu cuenta de airSlate SignNow. Agrega el complemento de airSlate SignNow para Gmail para que puedas hacerlo sin salir de tu bandeja de entrada. Luego, usando la herramienta Mis firmas, firma electrónicamente el documento y envíalo de vuelta por correo electrónico.
¿Qué puedo usar para firmar electrónicamente un documento?
Para gestionar un negocio en línea y firmar documentos electrónicamente, necesitas una solución confiable que cumpla con todos los requisitos de la Ley ESIGN. airSlate SignNow cumple con los estándares globales de firma electrónica, lo que significa que solo recopilas firmas electrónicas legalmente vinculantes y obtienes contratos ejecutables. Además, cada uno de tus registros tiene un historial que puedes usar fácilmente para saber quién firmó o llenó tu formulario y cuándo. Además, varias funciones adicionales te ayudan a configurar fácilmente las opciones de seguridad y los niveles de acceso para documentos y usuarios individuales.
Obtén más para store link log
- Beneficios de airSlate SignNow CRM vs. Streak CRM para Finanzas
- Beneficios de airSlate SignNow CRM vs. Streak CRM para TI
- Beneficios de airSlate SignNow CRM vs. Streak CRM para Legal
- Beneficios de airSlate SignNow CRM vs. Streak CRM para compras
- Beneficios de airSlate SignNow CRM vs. Streak CRM para gestión de productos
- Beneficios de airSlate SignNow CRM vs. Streak CRM para ventas
- Beneficios de airSlate SignNow CRM vs. Streak CRM para soporte
- Beneficios de airSlate SignNow CRM vs. Streak CRM para Contabilidad
Todo sobre la firma electrónica
Cómo firmar un PDF en Mac
Descubre lo fácil que es firmar documentos PDF en Mac. Usa nuestros consejos y trucos y la instrucción paso a paso para crear tu firma electrónica única y firmar con airSlate SignNow.
Edición y firma de PDFs fácil: Cómo editar y firmar electrónicamente un PDF para negocios
Comienza a hacer negocios electrónicamente. Obtén una evaluación completa de airSlate SignNow y cómo editar documentos y firmarlos electrónicamente. Optimiza tus flujos de firma electrónica.

¿Cómo firmar electrónicamente un W9 en PDF
¡Usa airSlate SignNow para asegurar que tu Formulario W9 esté firmado electrónicamente de forma segura y conforme al IRS!
Descubre otros store link log
- Desbloquea el Poder de la Legitimidad de la eFirma para ...
- Desbloqueando el Poder de la Legalidad de la eFirma ...
- Impulsa tu Adquisición con eFirmas Legítimas en ...
- Desbloquea la Legitimidad de la eSignature para la ...
- Asegurando la Legalidad de la Firma Digital para ...
- La Guía Definitiva sobre la Legalidad de la Firma ...
- Asegurando la Legalidad de las Firmas Digitales para la ...
- Desbloquea el Poder de la Legalidad de la Firma Digital ...
- Legalidad de la Firma Digital para Aseguramiento de ...
- Legitimidad de la Firma Digital para la Adquisición en ...
- Desbloquea la Legitimidad de la Firma Digital para la ...
- Legalidad de la Firma Electrónica para TI en Canadá - ...
- Desbloqueando el Poder de la Legalidad de la Firma ...
- Legalidad de la Firma Electrónica para Ventas en ...
- Legalidad de la Firma Electrónica para Aseguramiento ...
- Desbloquea el Poder de la Legalidad de la Firma ...
- Desbloquea la Legitimidad de la Firma Electrónica para ...
- Aumenta las Ventas con la Legitimidad de la Firma ...
- Legitimidad de la Firma Electrónica para la Logística ...
- Desbloquea la Legitimidad de la Firma Electrónica para ...
esté listo para obtener más













































