Adaptive Authentication
Adjusts required factors dynamically based on risk signals such as location, device trust, or transaction size to increase security only when risk is elevated.
Implementing double factor authentication to protect documents markedly reduces account takeover risk and unauthorized signing. It strengthens identity verification for sensitive agreements and supports compliance requirements in regulated sectors without substantially changing user workflows.

IT administrators configure authentication settings, integrate identity providers, and maintain recovery and logging procedures. They establish policies for 2FA enforcement, manage user provisioning, and ensure cryptographic and transport layers meet organizational security standards.
Compliance officers map 2FA controls to regulatory frameworks like ESIGN and UETA, maintain audit records for legal defensibility, and oversee retention and access policies for sensitive signed documents.
Organizations handling protected health information, student records, financial contracts, and high-value transactions commonly require stronger authentication methods.
These use cases prioritize non-repudiation and auditability while balancing user experience and compliance obligations.
Adjusts required factors dynamically based on risk signals such as location, device trust, or transaction size to increase security only when risk is elevated.
Automates user lifecycle and enforces enterprise multi-factor rules by connecting to Active Directory or cloud identity services, reducing manual account management.
Allows administrators to choose SMS, email, or app-based one-time passwords and to set expiration windows and retry limits that balance security and usability.
Applies cryptographic seals to final documents to detect alterations post-signature and to preserve evidentiary integrity alongside authentication records.
Predefined policy templates let administrators quickly apply consistent 2FA and retention settings across departments or document types, simplifying governance.
Sends signers clear prompts for required steps and notifies administrators of repeated authentication failures or suspicious activity for rapid response.
Connects corporate SSO, SAML, or OIDC providers to offload authentication to enterprise identity systems, enabling centralized user provisioning and enforcement of multi-factor policies without duplicating credential management in the signing platform.
Supports delivery of time-limited codes via SMS, email, or authenticator apps. Platforms should allow configurable expiry and retry limits to balance security and accessibility for signers in diverse environments.
Comprehensive logs capture authentication events, IP addresses, timestamps, and verification outcomes to create a defensible trail for each signed document, useful in legal or compliance reviews.
Granular role and permission controls limit who can change authentication policies, who can send 2FA-protected documents, and who can access signed documents, supporting separation of duties.

| Setting Name | Configuration |
|---|---|
| Reminder Frequency | 48 hours |
| Authentication Method | TOTP or SMS |
| Enforcement Scope | High-risk documents |
| Session Timeout | 15 minutes |
| Recovery Procedure | Admin reset |
Verify that your signing platform and recipient devices support the chosen second-factor options before enabling enforcement organization-wide.
Confirm device and browser compatibility, SSO connectivity, and reliable OTP delivery methods to ensure smooth signer experience and consistent enforcement of double factor authentication policies.
A regional hospital digitized patient consent forms and required a password plus TOTP authenticator for remote signing
Resulting in clearer audit trails and stronger HIPAA alignment for electronic consents.
A university moved transcript release to an eSignature platform and required student password plus SMS OTP for external requests
Leading to improved FERPA compliance and reduced manual identity checks.
| Authentication Provider | signNow (Recommended) | DocuSign | Adobe Sign |
|---|---|---|---|
| 2FA Support | |||
| TOTP Authenticator | |||
| SMS OTP | |||
| SSO Integration | SAML / OIDC | SAML / OIDC | SAML / OIDC |
Match document retention to statutory and contractual obligations.
Retain logs for the same period as signed documents for legal defensibility.
Periodically review who can access archived protected documents.
Define handling for documents signed by revoked or suspended accounts.
Establish secure deletion timelines and procedures.
| Plan/Metric | signNow (Featured) | DocuSign | Adobe Sign | PandaDoc | HelloSign |
|---|---|---|---|---|---|
| Starting Price (monthly) | Per-user monthly $8 | Per-user monthly $10 | Per-user monthly $29 | Per-user monthly $19 | Per-user monthly $15 |
| Included 2FA Features | TOTP, SMS, SSO | TOTP, SMS, SSO | TOTP, SMS, SSO | TOTP, SMS | TOTP, SMS, SSO |
| Advanced Auth Options | Adaptive rules available | Advanced adaptive features | Enterprise MFA add-on | Limited adaptive options | Enterprise SSO support |
| Compliance Support | HIPAA/FERPA controls | Extensive enterprise controls | Enterprise compliance features | Business-level compliance | Business compliance support |
| API Availability | Full API access | Full API access | Full API access | Full API access | Full API access |
To ensure that your document is signed by the right person, protect it with a password. Make sure to share the password with the recipient using any secure communication channel (e.g., SMS, phone call, personal message, etc.) at your disposal.
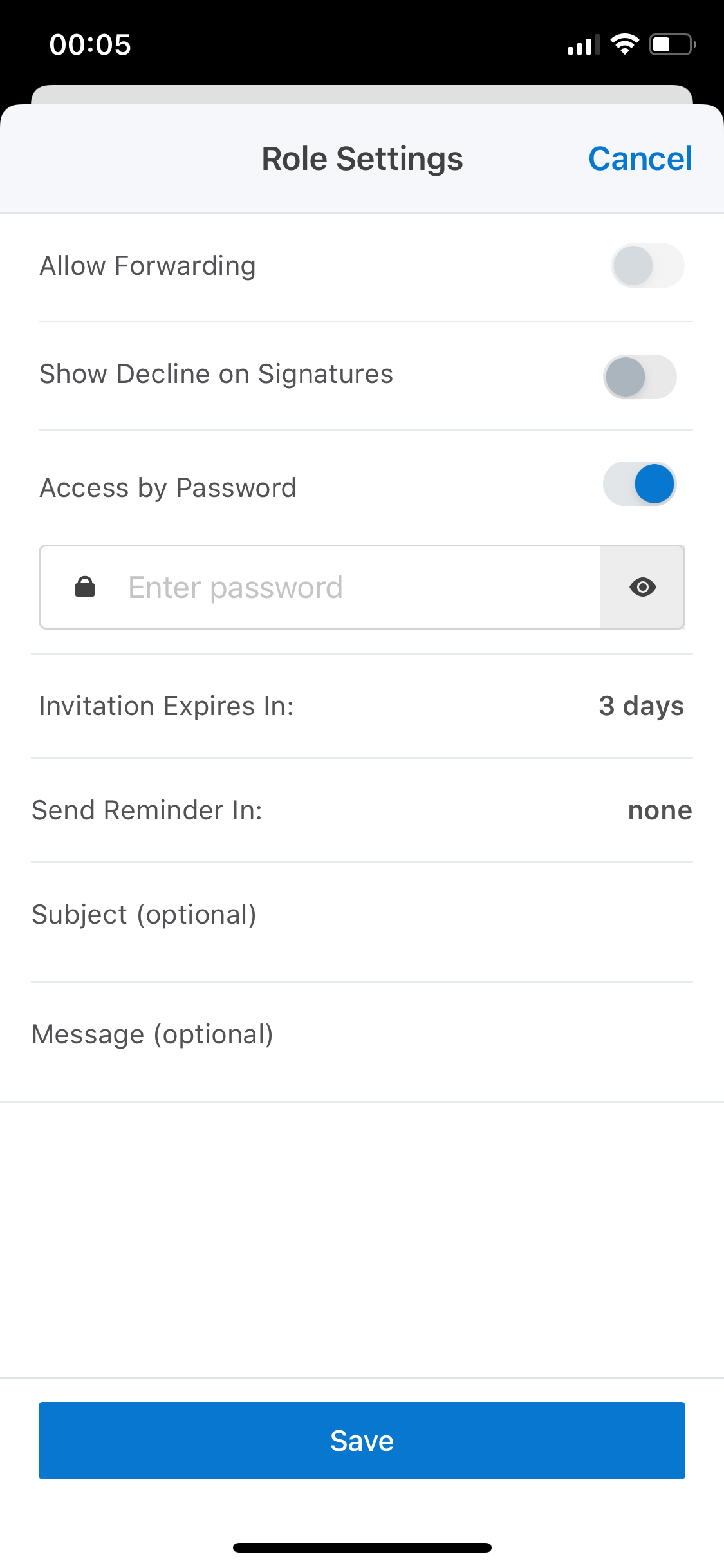
Once you have tapped Invite to Sign and entered your recipient’s email address, tap on the gear icon next to the signer’s email address. The advanced invite settings will open.
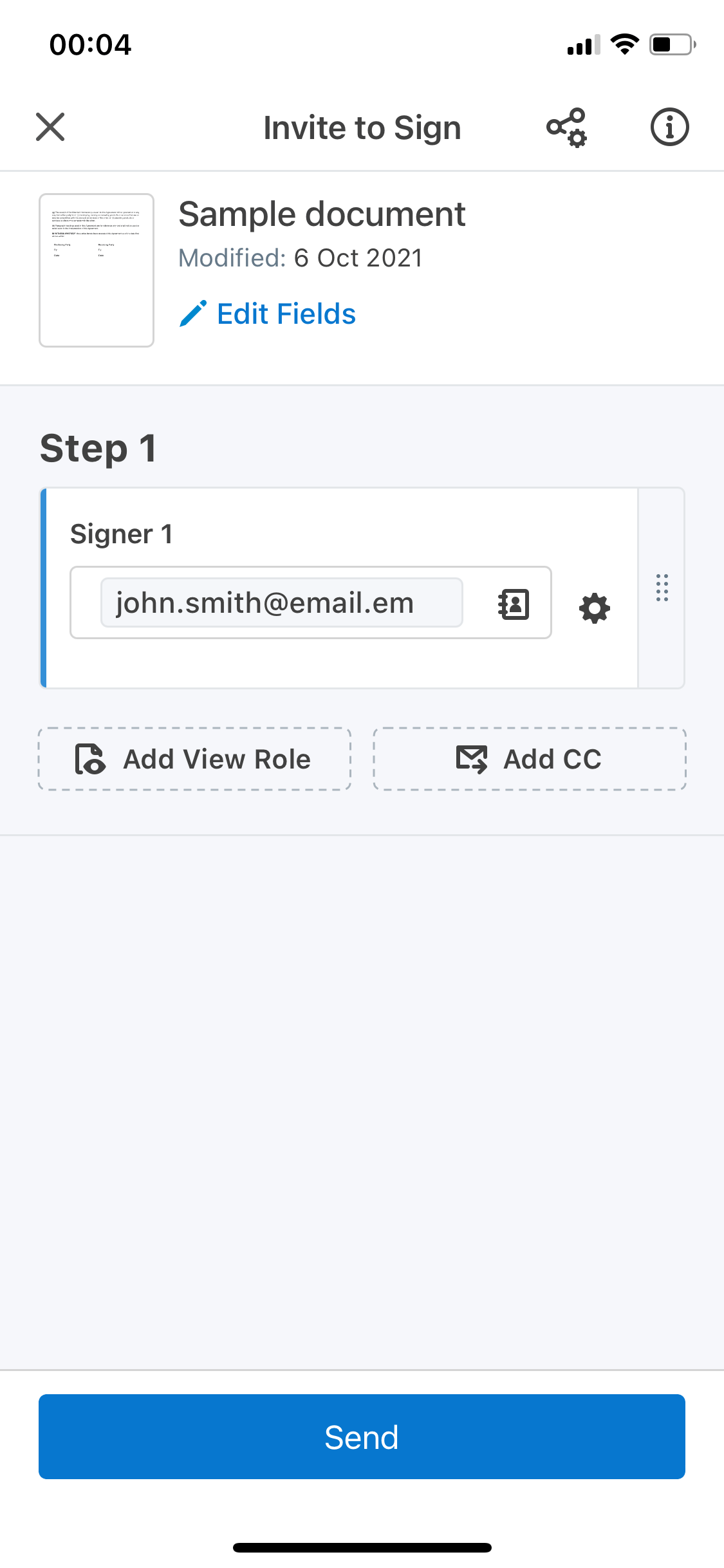
Switch on the option Access by Password. Set your password in the box that appears below. Then, tap Save and send your invite.