Setup Dual Factor Authentication for Secure Signatures
Improve your document workflow with airSlate SignNow
Flexible eSignature workflows
Fast visibility into document status
Simple and fast integration set up
Setup dual factor authentication make content changes and sign on any device
Detailed Audit Trail
Rigorous safety standards
Découvrez les signatures électroniques airSlate SignNow en action
Solutions airSlate SignNow pour une meilleure efficacité
Les avis de nos utilisateurs parlent d'eux-mêmes






Pourquoi choisir airSlate SignNow
-
Essai gratuit de 7 jours. Choisissez le forfait dont vous avez besoin et essayez-le sans risque.
-
Tarification honnête pour des forfaits complets. airSlate SignNow propose des abonnements sans frais supplémentaires ni frais cachés lors du renouvellement.
-
Sécurité de niveau entreprise. airSlate SignNow vous aide à respecter les normes de sécurité mondiales.

Votre guide étape par étape — setup dual factor authentication make content changes and sign
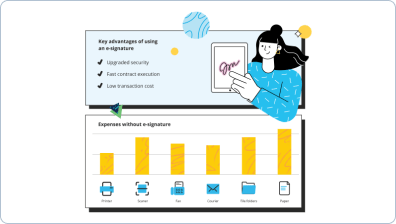
Setup dual factor authentication, Make content changes and Sign. Get greatest value from the most trustworthy and secure eSignature solution. Simplify your digital transactions using airSlate SignNow. Optimize workflows for everything from simple staff records to complex contracts and payment forms.
Learn how to Setup dual factor authentication, Make content changes and Sign:
- Upload a few files from your drive or cloud storage space.
- Drag & drop custom fillable boxes (signature, text, date/time).
- Modify the fields size, by tapping it and choosing Adjust Size.
- Insert dropdowns and checkboxes, and radio button groups.
- Add signers and request attachments.
- Setup dual factor authentication, Make content changes and Sign.
- Include the formula the place you require the field to appear.
- Apply comments and annotations for the users anywhere on the page.
- Approve all modifications by simply clicking DONE.
Connect users from outside and inside your enterprise to electronically access important signNowwork and Setup dual factor authentication, Make content changes and Sign anytime and on any system utilizing airSlate SignNow. You can track every activity carried out to your templates, receive notifications an audit report. Remain focused on your business and consumer relationships while understanding that your data is precise and protected.
Comment ça marche
Fonctionnalités airSlate SignNow appréciées par les utilisateurs
Découvrez des résultats exceptionnels Setup Dual Factor Authentication for Secure Signatures
Obtenez des signatures juridiquement contraignantes dès maintenant !
FAQ
-
How do I change my two factor authentication?
Go to Settings > [your name]. If you're using iOS 10.2 or earlier, go to Settings > iCloud and tap your Apple ID. Tap Password & Security. If asked, enter your Apple ID password. Tap Turn On Two-Factor Authentication. -
How do I turn off two factor authentication on my iPhone 2019?
Turn off two-step verification Sign in to your Apple ID account page. In the Security section, click Edit. Click Turn Off Two-Step Verification. Click again to confirm. -
How do I turn off 2 factor authentication on iPhone 2019?
Turn off two-step verification Sign in to your Apple ID account page. In the Security section, click Edit. Click Turn Off Two-Step Verification. Click again to confirm. -
How do I turn off two factor authentication?
On your Android phone or tablet, open your device's Settings app Google Google Account. At the top, tap Security. Under "Signing in to Google," tap 2-Step Verification. You might need to sign in. Tap Turn off. Confirm by tapping Turn off. -
How do I get rid of iPhone verification required?
Open the "Settings" app on the iPhone or iPad. Pick "iTunes & App Store" configurations, then tap the "Apple ID: your@email.com" button near the top of the settings. Tap on "View Apple ID" and sign in to the Apple ID as normal. Under 'Payment Method', choose "None" -- or, rather, update the payment procedure * -
Can not turn off two factor authentication Apple?
Visit appleid.apple.com. Enter your Apple ID and password and log in. Find the Security section. Click Edit. Then click \u201cTurn off two-factor authentication\u201d (if you do not see this, then you cannot turn this off). -
How do I bypass two factor authentication on Apple?
Go to your Apple ID account page and enter your Apple ID and password. On the Verify Your Identity screen, select "Can't access your trusted devices?" In the pop-up window, enter your Recovery Key. Go to the Security section and click Edit. -
How do I skip two factor authentication on Apple?
Sign in to your Apple ID account page. In the Security section, click Edit. Click Turn Off Two-Step Verification. Click again to confirm. Create new security questions and verify your date of birth. ... Remember to make sure that you're still signed in to iCloud. -
How can I get my Apple verification code without my phone?
Click Didn't get a verification code on the sign in screen. Choose to have the code sent to your trusted phone number. You'll get a text message or phone call from Apple with your verification code. Enter the code on your other device to complete sign in. -
How do I turn off 2 step verification?
On your Android phone or tablet, open your device's Settings app Google Google Account. At the top, tap Security. Under "Signing in to Google," tap 2-Step Verification. You might need to sign in. Tap Turn off. Confirm by tapping Turn off.
Ce que disent les utilisateurs actifs — setup dual factor authentication make content changes and sign
Questions fréquemment posées
Comment ajouter une signature électronique à un document Word ?
Comment signer électroniquement dans MS Word ?
Comment définir et enregistrer une signature électronique ?
Obtenez plus pour setup dual factor authentication make content changes and sign
- ESignature pour la gestion de la relation client pour l'éducation
- Signature électronique pour la gestion des leads pour la comptabilité et la fiscalité
- ESignature pour la gestion des leads pour les Communications & Médias
- Signature électronique pour la gestion des leads dans l'industrie de la construction
- Signature électronique pour la gestion des leads dans les services financiers
- Signature électronique pour la gestion des leads pour le gouvernement
- Signature électronique pour la gestion des leads dans le secteur de la santé
- Signature électronique pour la gestion des leads dans l'enseignement supérieur
Tout savoir sur la signature électronique

Découvrez d'autres setup dual factor authentication make content changes and sign
- Numérisez ma signature facilement avec airSlate ...
- Découvrez notre visionneuse PDF gratuite avec ...
- Découvrez le meilleur outil d'analyse de signature en ...
- Découvrez le logiciel de signature électronique ...
- Rationalisez votre flux de travail avec notre ...
- Découvrez le meilleur outil de signature de document ...
- Téléchargez un signataire PDF en masse gratuit pour ...
- Rationalisez votre flux de travail avec notre outil de ...
- Découvrez une inscription au portail resman sans ...
- Accédez facilement au téléchargement du fichier ...
- Découvrez les meilleurs outils de signature numérique ...
- Découvrez le meilleur lecteur PDF pour plusieurs ...
- Découvrez le meilleur outil de signature PDF gratuit ...
- Découvrez des solutions de signature électronique ...
- Signez et remplissez en ligne votre document PDF ...
- Découvrez le meilleur logiciel de signature ...
- Découvrez le meilleur éditeur PDF web gratuit pour ...
- Découvrez les meilleurs outils de signature de ...
- Signez des documents sans effort avec notre solution de ...
- Ajoutez facilement une signature électronique à ...













































