eSign Y Configurar Permisos Y Privilegios
Haz más en línea con una plataforma de firma electrónica de confianza mundial
Experiencia de firma sobresaliente
Informes y análisis robustos
Firma electrónica móvil en persona y a distancia
Políticas y cumplimiento de la industria
E firma y configure permisos y privilegios, más rápido que nunca
Extensiones útiles de firma electrónica
Vea las firmas electrónicas de airSlate SignNow en acción
Soluciones de airSlate SignNow para una mayor eficiencia
Las reseñas de nuestros usuarios hablan por sí mismas






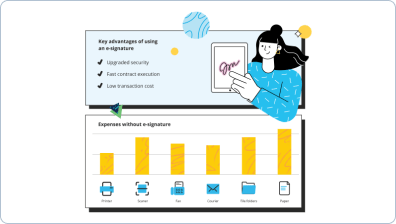
Por qué elegir airSlate SignNow
-
Prueba gratuita de 7 días. Elige el plan que necesitas y pruébalo sin riesgos.
-
Precios honestos para planes completos. airSlate SignNow ofrece planes de suscripción sin cargos adicionales ni tarifas ocultas al renovar.
-
Seguridad de nivel empresarial. airSlate SignNow te ayuda a cumplir con los estándares de seguridad globales.

Tu guía paso a paso — e sign and configure permissions and privileges
eSign y configure permisos y privilegios. Obtenga el mayor beneficio de la solución de firma electrónica más confiable y segura. Simplifique sus transacciones electrónicas usando airSlate SignNow. Automatice flujos de trabajo para todo, desde documentos de personal simples hasta acuerdos avanzados y plantillas de marketing.
Aprenda cómo eSign y configure permisos y privilegios:
- Agregue algunas páginas desde su dispositivo o almacenamiento en la nube.
- Arrastre y suelte cajas inteligentes rellenables (firma, texto, fecha/hora).
- Modifique el tamaño de los campos, tocándolos y seleccionando Ajustar tamaño.
- Coloque desplegables y casillas de verificación, y grupos de botones de opción.
- Agregue firmantes y cree la solicitud de adjuntos.
- eSign y configure permisos y privilegios.
- Incluya la fórmula donde necesita que se genere el campo.
- Utilice comentarios y anotaciones para los destinatarios en cualquier parte de la página.
- Guarde todas las modificaciones haciendo clic en HECHO.
Enlace a personas dentro y fuera de su negocio para trabajar electrónicamente en signNowwork importante y eSign y configure permisos y privilegios en cualquier momento y en cualquier dispositivo utilizando airSlate SignNow. Puede rastrear cada acción completada en sus plantillas, recibir alertas y un estado de auditoría. Manténgase enfocado en su negocio y asociaciones con los clientes mientras comprende que sus datos son precisos y seguros.
Cómo funciona
Funciones de airSlate SignNow que los usuarios adoran
Vea resultados excepcionales eSign y configurar permisos y privilegios
¡Obtenga firmas legalmente vinculantes ahora!
Preguntas frecuentes
-
¿Cuáles son los mejores sitios de minería legítimos para bitcoin?
Como todos han dicho, la minería en la nube es una estafa. Si quieres minar, debes estar preparado para hacer una inversión decente y aprender cómo hacerlo. Hay piscinas de minería a las que puedes unirte, si eso es lo que quisiste decir — cobran una pequeña tarifa para agrupar tu tasa de hash con otros, lo cual es bueno para las personas que no pueden construir granjas de minería. Los ASIC se usan para minar Bitcoin, mientras que las GPU se usan para minar casi todo lo demás. Prepárate para comprar el hardware y cubrir tus costos de energía. El retorno de inversión suele ser de unos 9 meses en promedio. También ten en cuenta que la minería requiere potencia y refrigeración, y el hardware suele ser bastante ruidoso. Probablemente no podrás generar un ingreso promedio minando en tu casa — no tendrás suficiente potencia, y tu sistema de refrigeración no podrá eliminar todo el calor... y podrás escucharlo funcionando. Si buscas ganar más de probablemente $25,000 al año, necesitarás un edificio dedicado con su propia energía y refrigeración. -
¿Cómo creas un volumen en un sistema de archivos?
Cuando se formatea una unidad, estás creando un volumen de disco, del tamaño de todo el disco. Con el uso de software de particionado, puedes dividir tu unidad en varias partes o volúmenes. Los volúmenes tampoco tienen que ser todos del mismo tamaño. Lógicamente, estas piezas son discos separados a pesar de que todo sea solo un disco físico. Los discos físicos también pueden estar vinculados para formar un disco aún más grande lógicamente.
Lo que dicen los usuarios activos — e sign and configure permissions and privileges
Preguntas frecuentes
¿Cómo agrego una firma electrónica a un documento de Word?
¿Qué es una firma electrónica y digital?
¿Cómo puedo obtener fácilmente una firma electrónica creada en Word?
Obtén más para e sign and configure permissions and privileges
- Firma electrónica para Gestión de relaciones con clientes para Farmacéutica
- Firma electrónica para Gestión de relaciones con clientes para Recursos Humanos
- Firma electrónica para Gestión de relaciones con clientes para RR.HH.
- Firma electrónica para Gestión de relaciones con clientes para Entretenimiento
- Firma electrónica para Gestión de relaciones con clientes para Educación
- Firma electrónica para gestión de clientes potenciales para Contabilidad y Impuestos
- Firma electrónica para gestión de Leads para Comunicaciones y Medios
- Firma electrónica para gestión de Leads en la Industria de la Construcción
Todo sobre la firma electrónica

Descubre otros e sign and configure permissions and privileges
- Comience su viaje de firma electrónica: dibujo de ...
- Desbloquea el poder de la eSignature: generador de ...
- Comienza tu viaje de eSignature: imagen de firma en ...
- Desbloquea el poder de la eSignature: software de ...
- Desbloquea el Poder de la eSignature: software de ...
- Comienza tu viaje de eSignature: firma en línea para ...
- Encuentra Todo lo que Necesitas Saber: firma en línea ...
- Prueba eSignatures sin problemas: firma en línea para ...
- Encuentra todo lo que necesitas saber: firmar un ...
- Explora tu firma digital – Preguntas respondidas: ...
- Comienza tu viaje de eSignature: firma de tipo en ...
- Explora tu firma digital – Preguntas respondidas: ...
- Comience su viaje de eSignature: subir firma en línea
- Explore las características populares de eSignature: ...
- Explora tu firma digital – Preguntas respondidas: ...
- Explora tu firma digital – Preguntas respondidas: ...
- Explora tu firma digital – Preguntas respondidas: ...
- Disfruta de flujos de trabajo de eSignature flexibles: ...
- Explora tu firma digital – Preguntas respondidas: ...
- Explora tu firma digital – Preguntas respondidas: ...













































