Registro De Enlace De Ubicación. Utilice Las Herramientas De Firma Electrónica Que Funcionan Donde Usted Trabaja.
Haz más en línea con una plataforma de firma electrónica confiable a nivel mundial
Experiencia de firma destacada
Informes y análisis confiables
Firma electrónica móvil en persona y a distancia
Normas de la industria y cumplimiento
Registro de enlace de ubicación, más rápido que nunca
Extensiones útiles de firma electrónica
Vea las firmas electrónicas de airSlate SignNow en acción
Soluciones de airSlate SignNow para una mayor eficiencia
Las reseñas de nuestros usuarios hablan por sí mismas






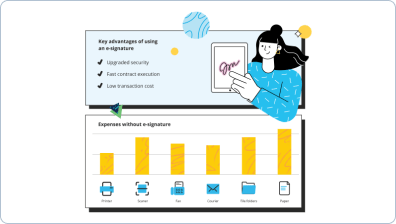
Por qué elegir airSlate SignNow
-
Prueba gratuita de 7 días. Elige el plan que necesitas y pruébalo sin riesgos.
-
Precios honestos para planes completos. airSlate SignNow ofrece planes de suscripción sin cargos adicionales ni tarifas ocultas al renovar.
-
Seguridad de nivel empresarial. airSlate SignNow te ayuda a cumplir con los estándares de seguridad globales.

Tu guía paso a paso — location link log
Registro de enlace de ubicación. Obtén el máximo rendimiento del sistema de firma electrónica más confiable y seguro. Simplifica tus transacciones electrónicas usando airSlate SignNow. Optimiza los flujos de trabajo para todo, desde documentos simples de empleados hasta contratos avanzados y formularios de marketing.
Entiende cómo funciona el registro de enlace de ubicación:
- Importa múltiples archivos desde tu unidad o almacenamiento en la nube.
- Arrastra y suelta cuadros rellenables avanzados (firma, texto, fecha/hora).
- Modifica el tamaño de los campos tocándolos y eligiendo Ajustar tamaño.
- Coloca casillas de verificación, listas desplegables y grupos de botones de opción.
- Edita los firmantes y crea la solicitud de materiales adicionales.
- Registro de enlace de ubicación.
- Incluye la fórmula en el lugar donde necesitas que se genere el campo.
- Agrega comentarios y anotaciones para los destinatarios en cualquier parte de la página.
- Guarda todos los ajustes haciendo clic en HECHO.
Vincula a los usuarios dentro y fuera de tu empresa para trabajar electrónicamente en los signNow y en el registro de enlace de ubicación en cualquier momento y en cualquier sistema utilizando airSlate SignNow. Puedes monitorear cada acción realizada en tus documentos, recibir notificaciones y un informe de auditoría. Mantén el enfoque en tu negocio y en las interacciones con los clientes con la seguridad de que tus datos son precisos y seguros.
Cómo funciona
Funciones de airSlate SignNow que los usuarios adoran
Vea resultados excepcionales Registro de enlace de ubicación. Utilice las herramientas de firma electrónica que funcionan donde usted trabaja.
¡Obtenga firmas legalmente vinculantes ahora!
Preguntas frecuentes
-
¿Qué es un enlace de Grabify?
Destacado en la serie de televisión Catfish de MTV, en la temporada 7, episodio 8, Grabify es un generador de enlaces de seguimiento que facilita atrapar a un gato en línea en una mentira. -
¿Qué hace el enlace de Grabify?
Acerca de. Grabify IP Logger URL & Shortener te proporciona algunos de los datos estadísticos y metadatos más avanzados y detallados para todos los clics en tus enlaces. Tu enlace de IP Logger puede acceder a información sobre la dirección IP del usuario, rastreador de ubicación (país, ciudad) y más. -
¿Qué es Grabify?
A: "Smart Logger" es una tecnología de registro de última generación que permite al usuario también registrar elementos como: nivel de batería, si el dispositivo está cargando, orientación de la pantalla, orientación del dispositivo y mucho más que está por venir. Puedes ver todos los datos que Grabify puede registrar AQUÍ. -
¿Es seguro el enlace de Grabify?
Grabify es un sitio que te permite rastrear a las personas que hacen clic en ciertos enlaces... Visitar el sitio sin nada después de la parte "hxxp://grabify.link" es seguro. -
¿Qué es Grabify?
Grabify es un proyecto basado en la web de jLynx que se puede acceder desde cualquier navegador. Aunque no necesitas registrarte para usar Grabify, es gratuito, y hay algunas opciones adicionales disponibles después de hacerlo. -
¿Es ilegal usar Grabify?
La dirección IP es información pública. En la mayoría de los casos, esa dirección IP no puede ser rastreada hasta el nombre de la persona u otra información personal. Sin embargo, si les dices que tienes información sobre ellos, independientemente de cómo hayas encontrado esa información, es claramente ilegal. Si van a la policía, depende mucho de lo que les hayas dicho. -
¿Qué es un registrador de IP?
Un registrador de IP es un servicio web simple utilizado para registrar y recopilar estadísticas para tu blog, sitio web o foros. Cuando usas un registrador de IP, puedes recopilar información sobre cualquier dirección IP de internet que visite tus enlaces. -
¿Cómo puedo rastrear una dirección IP?
Encuentra la dirección IP que deseas rastrear. Puedes encontrar la dirección IP de un sitio web en Windows, Mac, iPhone y Android. Haz clic en la barra de búsqueda. Esto es la caja blanca debajo del encabezado "Dirección IP o nombre de host". Escribe la dirección IP que encontraste. Haz clic en Buscar IP. Revisa los resultados. -
¿Para qué se usa Grabify?
Acerca de. Grabify IP Logger URL & Shortener te proporciona algunos de los datos estadísticos y metadatos más avanzados y detallados para todos los clics en tus enlaces. Tu enlace de IP Logger puede acceder a información sobre la dirección IP del usuario, rastreador de ubicación (país, ciudad) y más.
Lo que dicen los usuarios activos — location link log
Preguntas frecuentes
¿Qué es una firma electrónica y digital?
¿Cómo puedo hacer que otros firmen un archivo PDF?
¿Cómo pides a las personas que firmen documentos PDF?
Obtén más para location link log
- AirSlate SignNow CRM vs. Zendesk Sell para organizaciones sin fines de lucro
- AirSlate SignNow CRM vs. Zendesk Sell para PYMEs
- AirSlate SignNow CRM vs. Copper para empresas
- AirSlate SignNow CRM vs. Copper para pequeñas empresas
- AirSlate SignNow CRM vs. Copper para equipos
- AirSlate SignNow CRM vs. Copper para organizaciones
- AirSlate SignNow CRM vs. Copper para ONGs
- AirSlate SignNow CRM vs. Copper para organizaciones sin fines de lucro
Todo sobre la firma electrónica

Descubre otros location link log
- Descubre la mejor herramienta gratuita de firma de ...
- Descargue un firmador de PDF por lotes gratis para una ...
- Optimiza tu flujo de trabajo con nuestra herramienta de ...
- Experimenta un registro sin problemas en el portal ...
- Accede sin esfuerzo a la descarga del archivo de ...
- Descubre las mejores herramientas de firma digital ...
- Descubre el mejor lector de PDF para múltiples firmas
- Descubre la mejor herramienta de firma PDF gratuita en ...
- Descubre soluciones de firma electrónica para abogados ...
- Firma y completa en línea tu documento PDF gratis sin ...
- Descubre el mejor software de firma electrónica para ...
- Experimenta el mejor editor PDF web gratuito para ...
- Descubre las mejores herramientas de firma de ...
- Firma documentos sin esfuerzo con nuestra solución de ...
- Agrega fácilmente firma electrónica a Google Docs ...
- Cómo usar Google Docs para firmar documentos con ...
- Cómo agregar una firma digital a un formulario de ...
- Descubre soluciones de firma electrónica compatibles ...
- Descubre nuestra solución de firma compatible con ...
- Inicio de sesión de firma en línea sin esfuerzo para ...













































