Asegurar La Autenticación Doble Para Proteger Documentos
¿Qué es la solución de nube privada de airSlate SignNow y cómo mejora la seguridad?
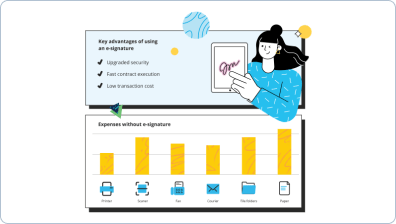
Las soluciones de airSlate SignNow On-Premises y Private Cloud permiten a las empresas aprovechar el poder y la usabilidad de la plataforma de firma electrónica airSlate SignNow mientras satisfacen requisitos de seguridad robustos.
Con esto en mente, airSlate SignNow ofrece dos opciones de implementación diferentes: Appliance y Virtual Appliance. El Appliance es para usuarios que necesitan ejecutar su nube privada de airSlate SignNow en las instalaciones. El Virtual Appliance es para clientes que prefieren desplegar airSlate SignNow en una máquina virtual VMware o Hyper-V.
Mantener datos en el sitio
El Appliance y Virtual Appliance de airSlate SignNow funcionan dentro de su red y no requieren conexión a Internet. También puede exponer selectivamente la aplicación al entorno externo de varias maneras: abriendo puertos o separando la capa de aplicación y almacenándola en la DMZ. Para otras opciones, por favor contacte a nuestro equipo de soporte.
Mantener datos en el país
Con el Appliance y Virtual Appliance de airSlate SignNow, puede ejecutar una versión privada o públicamente disponible de la aplicación mientras mantiene todos sus datos en un centro de datos dentro de un país específico. Por ejemplo, puede ejecutar su propia instancia única de airSlate SignNow desde un centro de datos en Alemania. Y aunque puede accederse desde cualquier lugar, usted sabe exactamente dónde se almacenan sus datos.
Controlar su tráfico SMTP
Al usar el Appliance o Virtual Appliance de airSlate SignNow, tiene control detallado sobre el tráfico SMTP. Puede aplicar políticas y controlar los datos usando sus propios estándares. Por ejemplo, puede establecer políticas de retención SMTP o añadir descargos de responsabilidad automáticamente al tráfico de correo electrónico sin ninguna acción requerida por parte de sus usuarios. También están disponibles soluciones de hardware.
Mantener el cumplimiento con estándares de la industria
El Appliance de airSlate SignNow funciona con sistemas que soportan HIPAA, FINRA y otras regulaciones de cumplimiento.
Descargar historial completo de auditoría
El Appliance de airSlate SignNow permite a los administradores descargar un historial completo de auditoría como parte de su solución de respaldo.
Entornos virtuales o hardware
airSlate SignNow utiliza VMware ESX y ESXi, VMware Server/Workstation/Player/Fusion, Microsoft Hyper-V, CITRIX XenServer, así como varias soluciones de hardware.
Soporte para Active Directory y LDAP
Aproveche los directorios de usuarios existentes mediante Active Directory o LDAP con la capacidad de gestionar el acceso por grupo y dominio.
Funciona con sistemas de correo electrónico existentes
El Appliance de airSlate SignNow se integra con sus sistemas de correo electrónico existentes para facilitar el cumplimiento y control.
Exportar documentos con historial de auditoría
Obtenga fácilmente documentos con sus registros históricos detallados desde el Appliance de airSlate SignNow.
API REST completa
Al igual que la solución de nube pública de airSlate SignNow, el Appliance de airSlate SignNow se integra sin problemas con otras aplicaciones mediante la API RESTful.
Múltiples configuraciones de red
El Appliance de airSlate SignNow puede funcionar en un entorno completamente privado, en una nube privada alojada, en una red corporativa o en muchas otras configuraciones.
Cifrado de datos fuerte
En la máquina virtual de airSlate SignNow, los datos están cifrados en reposo, lo que garantiza la seguridad de la información almacenada.
¿Cuáles son las opciones de implementación?
¿Qué hay de la seguridad?
¿Qué aplicaciones cliente son compatibles?
La aplicación web es accesible usando los siguientes navegadores: Safari, Chrome, Firefox e Internet Explorer. Las aplicaciones móviles están disponibles para iPhone, iPad y dispositivos Android (versión 4.3 y superior).
Vea las firmas electrónicas de airSlate SignNow en acción
Elimine la papeleo rutinario con airSlate SignNow
Solución de firma en línea
Creador de plantillas rellenables
Plantillas de documentos
API de firma electrónica
Integraciones nativas en aplicaciones
Capacidad para solución de nube privada para una mejor seguridad
Las reseñas de nuestros usuarios hablan por sí mismas






Por qué elegir airSlate SignNow
-
Prueba gratuita de 7 días. Elige el plan que necesitas y pruébalo sin riesgos.
-
Precios honestos para planes completos. airSlate SignNow ofrece planes de suscripción sin cargos adicionales ni tarifas ocultas al renovar.
-
Seguridad de nivel empresarial. airSlate SignNow te ayuda a cumplir con los estándares de seguridad globales.

Tu guía paso a paso — private cloud solution for better security
La ventaja conceptual clave del software de firma electrónica airSlate SignNow para la automatización empresarial es en realidad un entorno de información único que amplía la organización pero muestra un flujo de trabajo empresarial exclusivo. Puede crear y agregar su logotipo personalizado para la Solicitud de Firma, dar un enlace de invitación a sus socios, proveedores o compañeros de equipo. Nuestro innovador servicio simplifica los procesos de control y evaluación. Permite gestionar el flujo de trabajo de manera más flexible sin involucrar personal adicional. Puede fortalecer indirectamente la relación entre socios y permitirles mejorar la experiencia del cliente.
Cómo crear y agregar su logotipo personalizado para la Solicitud de Firma con airSlate SignNow:
- Cree su nombre de usuario y contraseña de forma gratuita o inicie sesión si ya tiene uno.
- Puede ingresar con la funcionalidad de inicio de sesión único si tiene el perfil de airSlate SignNow.|Si tiene la cuenta de airSlate SignNow, puede iniciar sesión con la funcionalidad de inicio de sesión único.
- Implemente el documento desde su dispositivo portátil o de escritorio.
- Además, puede cargar el documento necesario desde su almacenamiento en la nube. Nuestro software basado en navegador funciona con los repositorios más recomendados: Google Drive, OneDrive, DropBox.
- Realice cambios fácilmente en su plantilla con nuestro avanzado pero fácil de usar Editor PDF.
- Ingrese el contenido textual, coloque imágenes, deje sus anotaciones o comentarios, etc.
- Puede configurar elementos rellenables de diferentes tipos: texto o fecha, calculado o desplegable, y más.
- Organice y configure el requisito de adjunto.
- Coloque el campo de firma para enviar a firmar y recopilar firmas en persona o múltiples firmas electrónicas. Puede firmar la plantilla usted mismo si es relevante.
- Finalice la edición con el botón Listo y pase a crear y agregar su logotipo personalizado para la Solicitud de Firma.
airSlate SignNow es la primera opción para la automatización de procesos comerciales y la solución para crear y agregar su logotipo personalizado para la Solicitud de Firma y concluir rápidamente los asuntos para agencias de todos los niveles en términos de empleados y estructura. Los usuarios pueden interactuar tanto externamente como internamente con clientes y proveedores. ¡Pruebe todas las ventajas ahora!
Cómo funciona
Vea resultados excepcionales Asegurar la Autenticación Doble para Proteger Documentos
Preguntas frecuentes
-
¿Es seguro enviar documentos para firmar a través de airSlate SignNow?
Sí. Además de los protocolos de cifrado avanzado para almacenamiento y transmisión de datos mantenidos por airSlate SignNow, también puede agregar una capa adicional de protección a cualquier documento que envíe. Por ejemplo, los usuarios pueden habilitar la autenticación del firmante mediante contraseña, número de teléfono o llamada telefónica.
Lo que dicen los usuarios activos — private cloud solution for better security
Preguntas frecuentes
¿Cómo generas un documento y aplicas una firma electrónica en él?
¿Cómo agrego una firma electrónica a un documento de Word?
¿Cómo puedo subir y firmar un PDF?
Obtén más para private cloud solution for better security
- Registro de código postal de ubicación
- Texto del enlace de ubicación
- Registro de enlace de ubicación
- Location Numbers Record for Secure eSignature
- Lock Checkbox PDF Easily with signNow
- Lock Date Resolution: Secure eSignature Solutions
- Lock Date Text for Secure Signatures
- Lock Phone PDF with signNow's Secure eSignature Solution
Todo sobre la firma electrónica

Descubre otros private cloud solution for better security
- Empoderando tus flujos de trabajo con IA para la firma ...
- Empoderando tus flujos de trabajo con IA para la firma ...
- Empoderando tus flujos de trabajo con IA para la firma ...
- Empoderando tus flujos de trabajo con IA para la firma ...
- Empoderando tus flujos de trabajo con IA para la firma ...
- Empoderando tus flujos de trabajo con IA para la firma ...
- Empoderando tus flujos de trabajo con IA para la firma ...
- Empoderando tus flujos de trabajo con IA para la firma ...
- Empoderando tus flujos de trabajo con IA para la firma ...
- Empoderando tus flujos de trabajo con IA para la firma ...
- Empoderando tus flujos de trabajo con herramientas de ...
- Comience su viaje de firma electrónica: firmar ...
- Comience su viaje de eSignature: firmador de pdf en ...
- Comienza tu viaje de firma electrónica: firma de ...
- Comienza tu viaje de eSignature: firmar documentos en ...
- Comienza tu viaje de eSignature: firma el pdf en línea
- Comienza tu viaje de eSignature: firma en pdf en línea
- Comienza tu viaje de eSignature: firma cualquier ...
- Comience su viaje de firma electrónica: documentos ...
- Comienza tu viaje de eSignature: firma documento pdf ...










































