Formulario Seguro. Utilice Herramientas De Firma Electrónica Que Funcionan Donde Usted Trabaja.
Haz más en línea con una plataforma de firma electrónica de confianza mundial
Experiencia de firma excepcional
Informes y análisis robustos
Firma electrónica móvil en persona y a distancia
Normas y cumplimiento de la industria
Formulario seguro, más rápido que nunca
Complementos de firma electrónica útiles
Vea las firmas electrónicas de airSlate SignNow en acción
Soluciones de airSlate SignNow para una mayor eficiencia
Las reseñas de nuestros usuarios hablan por sí mismas






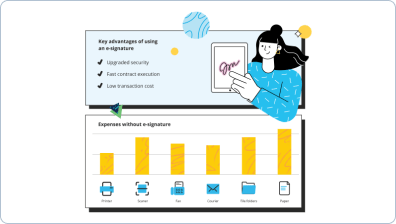
Por qué elegir airSlate SignNow
-
Prueba gratuita de 7 días. Elige el plan que necesitas y pruébalo sin riesgos.
-
Precios honestos para planes completos. airSlate SignNow ofrece planes de suscripción sin cargos adicionales ni tarifas ocultas al renovar.
-
Seguridad de nivel empresarial. airSlate SignNow te ayuda a cumplir con los estándares de seguridad globales.

Tu guía paso a paso — secure form
Formulario seguro. Obtén el máximo beneficio del sistema de firma electrónica más confiable y seguro. Optimiza tus transacciones digitales empleando airSlate SignNow. Mejora los flujos de trabajo para todo, desde documentos básicos del personal hasta acuerdos avanzados y formularios de marketing.
Entiende cómo asegurar un formulario:
- Agrega múltiples documentos desde tu computadora o almacenamiento en la nube.
- Arrastra y suelta campos rellenables inteligentes (firma, texto, fecha/hora).
- Modifica el tamaño de los campos, tocándolos y seleccionando Ajustar tamaño.
- Inserta listas desplegables y casillas de verificación, y grupos de botones de opción.
- Agrega firmantes y crea la solicitud de adjuntos.
- Formulario seguro.
- Incluye la fórmula en el lugar donde requieres que se genere el campo.
- Aplica comentarios y anotaciones para los destinatarios en cualquier parte de la página.
- Aprueba todos los ajustes simplemente haciendo clic en HECHO.
Conecta a las personas dentro y fuera de tu organización para acceder electrónicamente al trabajo esencial de firma y formulario seguro en cualquier momento y en cualquier sistema usando airSlate SignNow. Puedes monitorear cada actividad realizada en tus muestras, recibir notificaciones y un informe de auditoría. Mantente enfocado en tus interacciones comerciales y con los consumidores sabiendo que tus datos son precisos y están protegidos.
Cómo funciona
Funciones de airSlate SignNow que los usuarios adoran
Vea resultados excepcionales Formulario seguro. Utilice herramientas de firma electrónica que funcionan donde usted trabaja.
¡Obtenga firmas legalmente vinculantes ahora!
Preguntas frecuentes
-
¿Cómo encriptar un formulario?
Para habilitar el cifrado del formulario, vaya a "Seguridad" en la pestaña Configuración de su formulario y haga clic en "Cifrar datos guardados" en el cuadro de Configuración de contraseña y cifrado. Se le pedirá que cree una contraseña. -
¿Cómo encriptar un formulario web?
Para configurar formularios encriptados para formularios individuales, simplemente seleccione preferencias del formulario, luego la opción para encriptar el formulario. Al hacer clic en la página de cuentas, puede designar que todos los futuros formularios estén encriptados. Con nuestro Asistente de clave de cifrado, puede crear una clave privada segura. -
¿Cómo crear un formulario web seguro?
Personalice las entradas de campo. La validación de entrada es el acto de asegurarse de que lo que su visitante del sitio debe ingresar en cada campo del formulario sea todo lo que están ingresando. ... Habilite CAPTCHA. ... Habilite doble opción de suscripción. ... Formularios de carga de archivos seguros. -
¿Cómo encriptar un formulario de Google?
Para configurar formularios encriptados para formularios individuales, simplemente seleccione preferencias del formulario, luego la opción para encriptar el formulario. Al hacer clic en la página de cuentas, puede designar que todos los futuros formularios estén encriptados. Con nuestro Asistente de clave de cifrado, puede crear una clave privada segura. -
¿Son seguros los formularios de correo electrónico?
Los datos del formulario se almacenan de forma segura en los servidores de Formstack. Todos los usuarios tienen la opción de habilitar el cifrado para sus envíos almacenados. Los usuarios también pueden habilitar el cifrado de correo electrónico PGP para proteger la información compartida a través de correos electrónicos de notificación y confirmación. -
¿Se pueden encriptar los formularios de Google?
Sí, las respuestas de Google Forms se almacenan en una hoja de cálculo que solo puede accederse mediante inicio de sesión en una cuenta de Google. La transmisión de datos utiliza SSL para cifrar los datos durante el transporte (¡pero no en almacenamiento!). Los datos son tan seguros como en la mayoría de los otros sistemas que recopilan datos de encuestas y los almacenan. -
¿Se puede proteger con contraseña un formulario de Google?
Crea un formulario protegido con contraseña Abre este formulario de Google y notarás que tiene un campo de contraseña. Tendrás que ingresar la contraseña correcta* para ver el formulario real, de lo contrario no te permitirá avanzar más allá de la primera pantalla. ... Llámalo "Contraseña" y haz que sea una pregunta obligatoria como se muestra en la ilustración a continuación. -
¿Se puede hacer que los formularios de Google sean privados?
Crea, envía, comparte y edita un formulario. Un formulario de Google está conectado automáticamente a una hoja de cálculo con el mismo título. La hoja de cálculo tiene configuraciones de uso compartido privadas por defecto. Necesitarás acceder a la hoja de cálculo para actualizar los derechos de uso compartido de la hoja que contiene las respuestas de los formularios completados. -
¿Está encriptado Google One?
Seguridad adicional para Google Drive. Boxcryptor protege tu Google Drive con cifrado de extremo a extremo y con un estándar de conocimiento cero, lo que significa que nadie más que tú puede acceder a tus datos, ni nosotros, ni Google, ni terceros. -
¿Cómo uso la encriptación?
Cifrar un teléfono inteligente Android es igual de fácil y puede hacerse durante la configuración o navegando a Configuración, seleccionando Seguridad y seleccionando Cifrar dispositivo. (La redacción puede variar según la marca del teléfono. Si tienes problemas, intenta buscar "cifrado" en Configuración.)
Lo que dicen los usuarios activos — secure form
Preguntas frecuentes
¿Cómo agrego una firma electrónica a un documento de Word?
¿Cómo firmo un PDF electrónicamente?
¿Cómo pongo una firma electrónica en un archivo PDF?
Obtén más para secure form
- Firma en línea para CRM para Investigación y Desarrollo
- Firma en línea para CRM para gestión
- Firma en línea para CRM para Administración
- Firma en línea para CRM para Atención al Cliente
- Firma en línea para CRM para soporte al cliente
- Firma en línea para CRM para Soporte Técnico
- Firma en línea para CRM para Marketing
- Firma en línea para CRM para logística
Todo sobre la firma electrónica

Descubre otros secure form
- Aplicación de firma digital para iPad sin esfuerzo ...
- Crea tu creador de firmas único para PDF sin esfuerzo
- Accede a tu inicio de sesión de cuenta de firma ...
- Firma documentos PDF en línea en Chrome sin esfuerzo
- Digitaliza mi firma fácilmente con airSlate SignNow
- Descubre nuestro visor de PDF gratuito con firma ...
- Descubre la mejor herramienta de análisis de firmas en ...
- Descubre software de firma electrónica compatible con ...
- Optimiza tu flujo de trabajo con nuestra descarga ...
- Descubre la mejor herramienta gratuita de firma de ...
- Descargue un firmador de PDF por lotes gratis para una ...
- Optimiza tu flujo de trabajo con nuestra herramienta de ...
- Experimenta un registro sin problemas en el portal ...
- Accede sin esfuerzo a la descarga del archivo de ...
- Descubre las mejores herramientas de firma digital ...
- Descubre el mejor lector de PDF para múltiples firmas
- Descubre la mejor herramienta de firma PDF gratuita en ...
- Descubre soluciones de firma electrónica para abogados ...
- Firma y completa en línea tu documento PDF gratis sin ...
- Descubre el mejor software de firma electrónica para ...













































