Verificar Identidad Para Firmar Electrónicamente. Use Herramientas De Firma Electrónica Que Funcionan Donde Usted Trabaja.
Haz más en línea con una plataforma de firma electrónica de confianza mundial
Experiencia de firma notable
Informes y análisis robustos
Firma electrónica móvil en persona y a distancia
Regulaciones y cumplimiento industrial
Verificación de identidad para firmar electrónicamente, más rápido que nunca
Extensiones útiles de firma electrónica
Vea las firmas electrónicas de airSlate SignNow en acción
Soluciones de airSlate SignNow para una mayor eficiencia
Las reseñas de nuestros usuarios hablan por sí mismas






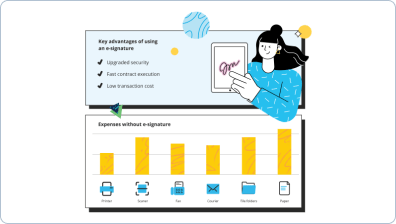
Por qué elegir airSlate SignNow
-
Prueba gratuita de 7 días. Elige el plan que necesitas y pruébalo sin riesgos.
-
Precios honestos para planes completos. airSlate SignNow ofrece planes de suscripción sin cargos adicionales ni tarifas ocultas al renovar.
-
Seguridad de nivel empresarial. airSlate SignNow te ayuda a cumplir con los estándares de seguridad globales.

Tu guía paso a paso — verify identity to eSign
Verificar identidad para firmar electrónicamente. Obtén el máximo rendimiento del sistema de firma electrónica más respetado y seguro. Mejora tus acuerdos electrónicos usando airSlate SignNow. Optimiza los flujos de trabajo para todo, desde documentos simples del personal hasta acuerdos complejos y formularios de marketing.
Aprende cómo verificar identidad para firmar electrónicamente:
- Importa múltiples archivos desde tu dispositivo o almacenamiento en la nube.
- Arrastra y suelta campos rellenables personalizados (firma, texto, fecha/hora).
- Modifica el tamaño de los campos, tocándolos y eligiendo Ajustar tamaño.
- Coloca casillas de verificación, listas desplegables y grupos de botones de opción.
- Agrega firmantes y solicita materiales adicionales.
- Verificar identidad para firmar electrónicamente.
- Incluye la fórmula en el lugar donde necesitas que se genere el campo.
- Agrega comentarios y anotaciones para los destinatarios en cualquier parte de la página.
- Guarda todos los ajustes haciendo clic en HECHO.
Conecta personas dentro y fuera de tu empresa para acceder electrónicamente a los trabajos esenciales de firma y verificar identidad para firmar electrónicamente en cualquier momento y en cualquier dispositivo usando airSlate SignNow. Puedes monitorear cada acción realizada en tus documentos, recibir alertas y un informe de auditoría. Mantén el enfoque en tu negocio y relaciones con clientes mientras tienes la seguridad de que tus datos son precisos y seguros.
Cómo funciona
Funciones de airSlate SignNow que los usuarios adoran
Vea resultados excepcionales Verificar identidad para firmar electrónicamente. Use herramientas de firma electrónica que funcionan donde usted trabaja.
¡Obtenga firmas legalmente vinculantes ahora!
Preguntas frecuentes
-
¿Cómo verificas una firma electrónica?
Abre un documento PDF que contenga una firma digital. Haz clic derecho en una firma en la página y selecciona Verificar firma en el menú contextual. La caja de información Estado de validación muestra los resultados. Haz clic en Propiedades para obtener más información sobre la firma. -
¿Cómo verifico una firma electrónica en PDF?
Abre el cuadro de diálogo Preferencias. En Categorías, selecciona Firmas. Para Verificación, haz clic en Más. Para validar automáticamente todas las firmas en un PDF al abrir el documento, selecciona Verificar firmas al abrir el documento. -
¿Cómo se verifica una firma digital?
Verificación de firmas digitales La tecnología de firma digital permite al destinatario de un mensaje firmado verificar su origen real y su integridad. El proceso de verificación de firma digital está diseñado para determinar si un mensaje dado ha sido firmado con la clave privada que corresponde a una clave pública dada. -
¿Cómo desactivo la verificación de firma en signNow?
Ve a Editar - Preferencias - Firmas y haz clic en Más junto a Verificación, y luego desmarca la casilla "Verificar firmas al abrir el documento". -
¿Cómo verificas una firma digital?
Abre un documento PDF que contenga una firma digital. Haz clic derecho en una firma en la página y selecciona Verificar firma en el menú contextual. La caja de información Estado de validación muestra los resultados. Haz clic en Propiedades para obtener más información sobre la firma. -
¿Cómo desactivo la verificación de airSlate SignNow?
Inicia sesión en tu cuenta de airSlate SignNow con tu ID y contraseña. Haz clic en Contraseña y seguridad en el panel izquierdo de Perfil. En la sección Verificación en dos pasos, haz clic en Gestionar. En la pantalla de Verificación en dos pasos, desactiva la opción Verificación en dos pasos. -
¿Qué es una firma verificada?
La verificación de firma es una técnica utilizada por bancos, agencias de inteligencia e instituciones de alto perfil para validar la identidad de una persona. ... Una imagen de una firma o una firma directa se introduce en el software de verificación de firma y se compara con la imagen de firma almacenada.
Lo que dicen los usuarios activos — verify identity to eSign
Preguntas frecuentes
¿Cómo agrego una firma electrónica a un documento de Word?
¿Cómo agrego una firma electrónica a un PDF?
¿Cómo creo un PDF y lo envío a mi cliente para que lo firme?
Obtén más para verify identity to eSign
Todo sobre la firma electrónica

Descubre otros verify identity to eSign
- Legalidad de la eFirma para Carta de Cese y ...
- Desbloquea el Poder de la Legitimidad de la eSignature ...
- Legitimidad de la eSignature para el Acuerdo de ...
- Legitimidad de la eFirma para el Acuerdo de No ...
- Mejora la Legitimidad de la eFirma para el ...
- Desbloquea el poder de la licitud de eSignature para ...
- Desbloqueando el Poder de la Legalidad de la Firma ...
- Asegurando el Cumplimiento de las Leyes de Firma ...
- Legitimidad de la Firma Digital para la Política de ...
- Mejora la Legitimidad de la Firma Digital para el ...
- Legitimidad de la Firma Digital para Abordar el Acoso ...
- Asegurando la licitud de la firma digital para el ...
- Entendiendo la Legalidad de la Firma Electrónica para ...
- Asegurando la Legalidad de la Firma Electrónica para ...
- Entendiendo la Legalidad de las Firmas Electrónicas ...
- Desbloqueando el Poder de la Legitimidad de la Firma ...
- Mejora la Legitimidad de los Contratos de Freelance con ...
- Legitimidad de la Firma Electrónica para Contratos en ...
- Asegurando la Legitimidad de la Firma Electrónica para ...
- Mejora la Legitimidad de la Firma Electrónica para ...













































