Signer électroniquement Et Fournir Une Approvisionnement Juste-à-temps. Utilisez Des Outils De Signature électronique Qui Fonctionnent Où Vous êtes.
Améliorez votre flux de travail documentaire avec airSlate SignNow
Flux de signature électronique polyvalents
Visibilité instantanée sur l'état du document
Configuration d'intégration facile et rapide
Signer électroniquement et fournir une approvisionnement juste-à-temps sur n'importe quel appareil
Traçabilité avancée des audits
Normes de sécurité strictes
Découvrez les signatures électroniques airSlate SignNow en action
Solutions airSlate SignNow pour une meilleure efficacité
Les avis de nos utilisateurs parlent d'eux-mêmes






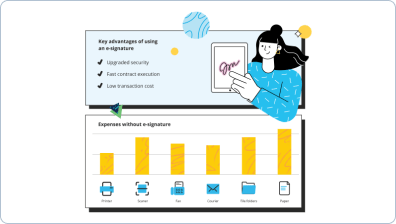
Pourquoi choisir airSlate SignNow
-
Essai gratuit de 7 jours. Choisissez le forfait dont vous avez besoin et essayez-le sans risque.
-
Tarification honnête pour des forfaits complets. airSlate SignNow propose des abonnements sans frais supplémentaires ni frais cachés lors du renouvellement.
-
Sécurité de niveau entreprise. airSlate SignNow vous aide à respecter les normes de sécurité mondiales.

Votre guide étape par étape — e sign and provide just in time provisioning
Signer électroniquement et fournir une approvisionnement juste-à-temps. Obtenez le maximum d'avantages de la solution de signature électronique la plus fiable et la plus sûre. Simplifiez vos transactions électroniques en utilisant airSlate SignNow. Optimisez les flux de travail pour tout, des documents de personnel simples aux accords complexes et modèles de vente.
Comprenez comment signer électroniquement et fournir une approvisionnement juste-à-temps :
- Ajoutez quelques pages depuis votre lecteur ou stockage cloud.
- Faites glisser et déposez des champs remplissables avancés (signature, texte, date/heure).
- Modifiez la taille des champs en appuyant dessus et en sélectionnant Ajuster la taille.
- Placez des cases à cocher, des menus déroulants et des groupes de boutons radio.
- Ajoutez des signataires et créez la demande de documents supplémentaires.
- signer électroniquement et fournir une approvisionnement juste-à-temps.
- Ajoutez la formule où vous souhaitez que le champ apparaisse.
- Appliquez des remarques et des annotations pour les signataires n'importe où sur la page.
- Enregistrez tous les ajustements en cliquant sur TERMINÉ.
Connectez des personnes de l'extérieur et de l'intérieur de votre entreprise pour accéder électroniquement à des documents importants et signer électroniquement et fournir une approvisionnement juste-à-temps à tout moment et sur n'importe quel appareil avec airSlate SignNow. Vous pouvez surveiller chaque activité effectuée sur vos documents, recevoir des alertes et un rapport d'audit. Restez concentré sur votre entreprise et vos relations clients tout en sachant que vos données sont précises et protégées.
Comment ça marche
Fonctionnalités airSlate SignNow appréciées par les utilisateurs
Découvrez des résultats exceptionnels Signer électroniquement et fournir une approvisionnement juste-à-temps. Utilisez des outils de signature électronique qui fonctionnent où vous êtes.
Obtenez des signatures juridiquement contraignantes dès maintenant !
FAQ
-
Qu'est-ce que l'approvisionnement juste-à-temps ?
L'approvisionnement juste-à-temps offre une autre façon d'approvisionner les utilisateurs dans le service VMware Identity Manager. Au lieu de synchroniser les utilisateurs à partir d'une instance Active Directory, avec l'approvisionnement juste-à-temps, les utilisateurs sont créés et mis à jour dynamiquement lorsqu'ils se connectent, en fonction des assertions SAML envoyées par le fournisseur d'identité. -
Qu'est-ce que l'auto-provisionnement SSO ?
L'auto-provisionnement. Google supporte également l'auto-provisionnement pour environ un quart des applications avec SSO préconfiguré. L'approvisionnement signifie que lorsqu'un administrateur G Suite crée, modifie ou supprime un compte G Suite, un compte pour cet utilisateur sera créé, modifié ou supprimé dans le service connecté. -
Que signifie approvisionnement ?
L'approvisionnement des comptes utilisateurs concerne la création, la gestion et la maintenance des objets et attributs d'un utilisateur final en relation avec l'accès aux ressources disponibles dans un ou plusieurs systèmes. Essentiellement, l'approvisionnement des comptes utilisateurs fait référence à la gestion des droits et privilèges des utilisateurs. -
Qu'est-ce que l'authentification SAML ?
L'authentification SAML est le processus de vérification de l'identité et des identifiants de l'utilisateur (mot de passe, authentification à deux facteurs, etc.). L'autorisation SAML indique au fournisseur de services quel accès accorder à l'utilisateur authentifié. -
Comment activer SSO ?
Pour configurer la connexion unique par vous-même : Ouvrez l'onglet Paramètres utilisateur. Faites défiler jusqu'à la section Configurer la connexion unique (SSO) et cliquez sur Configurer pour commencer. Sélectionnez votre fournisseur d'identité (IdP). Si votre fournisseur n'apparaît pas dans la liste, utilisez le questionnaire SSO de Box pour que Box vous aide à configurer le SSO. -
Qu'est-ce que l'approvisionnement utilisateur dans Salesforce ?
L'approvisionnement utilisateur s'applique uniquement aux utilisateurs ayant un profil ou un ensemble d'autorisations leur accordant l'accès à l'application connectée. Salesforce fournit un assistant pour vous guider dans les paramètres d'approvisionnement utilisateur pour chaque application connectée. -
Qu'est-ce que l'approvisionnement utilisateur ?
L'approvisionnement des comptes utilisateurs concerne la création, la gestion et la maintenance des objets et attributs d'un utilisateur final en relation avec l'accès aux ressources disponibles dans un ou plusieurs systèmes. Essentiellement, l'approvisionnement des comptes utilisateurs fait référence à la gestion des droits et privilèges des utilisateurs. -
Qu'est-ce que Salesforce Identity Connect ?
Salesforce Identity Connect. Salesforce Identity Connect intègre Microsoft Active Directory (AD) avec Salesforce. Les informations utilisateur saisies dans AD sont partagées avec Salesforce de manière transparente et instantanée. Les entreprises utilisant AD pour la gestion des utilisateurs peuvent utiliser Salesforce Identity Connect pour gérer les comptes Salesforce. -
Comment changer le type de flux dans Salesforce ?
Pour modifier un flux, ouvrez-le dans le Cloud Flow Designer. Vous ne pouvez pas enregistrer les modifications d'une version de flux active. Cependant, vous pouvez ouvrir une version active d'un flux, le modifier, puis l'enregistrer en tant que nouvelle version ou nouveau flux. Depuis la configuration, saisissez Flows dans la boîte de recherche rapide, puis sélectionnez Flows.
Ce que disent les utilisateurs actifs — e sign and provide just in time provisioning
Questions fréquemment posées
Comment ajouter une signature électronique à un document Word ?
Qu'est-ce qu'une signature électronique et numérique ?
Comment signer un PDF en ligne ?
Obtenez plus pour e sign and provide just in time provisioning
- Signature électronique pour la gestion des leads dans l'industrie du voyage
- Signature électronique pour la gestion des leads pour HighTech
- Signature électronique pour la gestion des leads dans la fabrication
- Signature électronique pour la gestion des leads pour les services de construction
- Signature électronique pour la gestion des leads pour les organisations sportives
- Signature électronique pour la gestion des leads dans l'industrie pharmaceutique
- Signature électronique pour la gestion des leads pour les ressources humaines
- Signature électronique pour la gestion des leads pour les RH
Tout savoir sur la signature électronique