Journal De Liens. Utilisez Des Outils eSignature Qui Fonctionnent Où Que Vous Soyez.
Faites plus en ligne avec une plateforme eSignature de confiance mondiale
Expérience de signature remarquable
Rapports et analyses fiables
Signature électronique mobile en personne et à distance
Règles et conformité industrielles
Journal de liens, plus rapide que jamais
Extensions eSignature pratiques
Découvrez les signatures électroniques airSlate SignNow en action
Solutions airSlate SignNow pour une meilleure efficacité
Les avis de nos utilisateurs parlent d'eux-mêmes






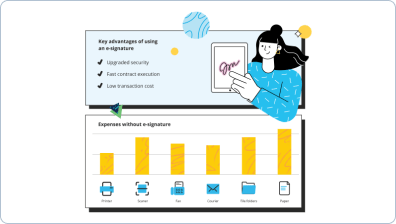
Pourquoi choisir airSlate SignNow
-
Essai gratuit de 7 jours. Choisissez le forfait dont vous avez besoin et essayez-le sans risque.
-
Tarification honnête pour des forfaits complets. airSlate SignNow propose des abonnements sans frais supplémentaires ni frais cachés lors du renouvellement.
-
Sécurité de niveau entreprise. airSlate SignNow vous aide à respecter les normes de sécurité mondiales.

Votre guide étape par étape — link link log
Journal de liens. Obtenez des performances maximales avec la plateforme eSignature la plus fiable et sécurisée. Simplifiez vos transactions électroniques en utilisant airSlate SignNow. Optimisez les flux de travail pour tout, des documents de personnel de base aux contrats complexes et modèles d'achat.
Comprenez comment utiliser le journal de liens :
- Importer une série de documents depuis votre lecteur ou stockage cloud.
- Faire glisser et déposer des cases à remplir personnalisées (signature, texte, date/heure).
- Modifier la taille des champs en appuyant dessus et en sélectionnant Ajuster la taille.
- Insérer des menus déroulants, des cases à cocher et des groupes de boutons radio.
- Modifier les signataires et créer la demande de pièces jointes.
- Journal de liens.
- Ajouter la formule où vous souhaitez que le champ apparaisse.
- Utiliser des remarques et des annotations pour les destinataires n'importe où sur la page.
- Enregistrer toutes les modifications en cliquant simplement sur TERMINER.
Connectez des personnes de l'intérieur et de l'extérieur de votre entreprise pour travailler électroniquement sur des documents importants et utiliser le journal de liens à tout moment et sur n'importe quel système avec airSlate SignNow. Vous pouvez suivre chaque activité effectuée sur vos documents, recevoir des alertes et un rapport d'audit. Restez concentré sur votre entreprise et vos relations clients tout en ayant la certitude que vos données sont précises et protégées.
Comment ça marche
Fonctionnalités airSlate SignNow appréciées par les utilisateurs
Découvrez des résultats exceptionnels Journal de liens. Utilisez des outils eSignature qui fonctionnent où que vous soyez.
Obtenez des signatures juridiquement contraignantes dès maintenant !
FAQ
-
Comment puis-je vérifier mon solde de lien ?
Regardez votre dernier reçu, si vous l'avez. Allez sur le site Web de la carte Illinois Link. Appelez la ligne d'assistance Illinois Link au 1-800-678-LINK (5465) ou au 1-877-765-3459 (TTY) Obtenez votre solde dans un magasin qui accepte la carte Link. ... Effectuez une vérification du solde à un ATM (pour le solde du compte en espèces uniquement). -
Comment puis-je vérifier mon solde de coupons alimentaires en ligne ?
Vérifiez votre solde SNAP sur votre dernier reçu d'épicerie. Connectez-vous et vérifiez votre solde en ligne si votre État fournit des informations sur votre compte SNAP en ligne. Appelez le numéro du service client de transfert électronique de prestations (EBT) de votre État, un représentant du service client EBT devrait pouvoir vous aider. -
Comment puis-je vérifier mes prestations SNAP dans l'Illinois ?
Si vous ne trouvez pas votre carte EBT, appelez la ligne directe EBT de l'Illinois dès que possible : 1-800-678-5465. -
Comment puis-je vérifier mon solde de coupons alimentaires dans l'Illinois ?
Si vous n'avez pas de compte Illinois Link, vous pouvez en créer un ici. La dernière option pour vérifier le solde de votre carte est par téléphone. Appelez le numéro du service client EBT (1-800-678-5465) au dos de votre carte. La ligne d'assistance est disponible 24h/24 et 7j/7. -
Comment puis-je vérifier mes prestations SNAP ?
Vérifiez votre solde SNAP sur votre dernier reçu d'épicerie. Connectez-vous et vérifiez votre solde en ligne si votre État fournit des informations sur votre compte SNAP en ligne. Appelez le numéro du service client de transfert électronique de prestations (EBT) de votre État, un représentant du service client EBT devrait pouvoir vous aider. -
Comment puis-je vérifier mon solde de lien ?
Connectez-vous au portail des titulaires de carte EBT. Appelez le numéro du service client EBT (1-888-356-3281) au dos de votre carte. ... Vérifiez vos soldes de l'aide alimentaire ou du compte en espèces à un distributeur automatique ou à un terminal de point de vente. -
Comment puis-je vérifier ma carte Link ?
Si vous ne trouvez pas votre carte EBT, appelez la ligne directe EBT de l'Illinois dès que possible : 1-800-678-5465. -
Quel est le numéro de lien ?
Ligne d'assistance Illinois Link 1-800-678-LINK (5465) Écoutez les options linguistiques en anglais, arabe, chinois, polonais, espagnol ou ourdou. Pour parler en réponse, attendez les invites jusqu'à ce qu'on vous demande de parler de votre numéro de carte à 16 ou 19 chiffres. -
Quel est le numéro de téléphone de la carte Link ?
ou Numéro de carte : Si vous avez des questions, veuillez appeler la ligne d'assistance Illinois Link : 1-800-678-LINK (5465) -
Comment activer ma carte Link ?
Composez le 1-866-545-6502 et écoutez le système automatisé. Appuyez sur 1 pour l'anglais ou 2 pour l'espagnol. Entrez votre numéro de carte à 16 chiffres au recto de votre carte. Appuyez sur 4 pour configurer votre code PIN. Entrez votre date de naissance. ... Entrez votre numéro de sécurité sociale lorsque cela est demandé. Sélectionnez 4 chiffres comme votre code PIN.
Ce que disent les utilisateurs actifs — link link log
Questions fréquemment posées
Qu'est-ce qu'une signature électronique et numérique ?
Comment envoyer un PDF de manière à ce que quelqu'un puisse le signer électroniquement et le renvoyer
Quelle est la différence entre une signature numérique et une signature électronique ?
Obtenez plus pour link link log
- AirSlate SignNow CRM vs. Freshsales CRM pour l'assurance qualité
- AirSlate SignNow CRM vs. Freshsales CRM pour l'ingénierie
- AirSlate SignNow CRM vs. Freshsales CRM pour l'export
- AirSlate SignNow CRM vs. Freshsales CRM pour l'expédition
- AirSlate SignNow CRM vs. Freshsales CRM pour les relations publiques
- AirSlate SignNow CRM vs. Freshsales CRM pour la production
- AirSlate SignNow CRM vs. Freshsales CRM pour la supervision
- AirSlate SignNow CRM vs. Freshsales CRM pour la qualité du produit
Tout savoir sur la signature électronique

Découvrez d'autres link link log
- Comprendre la légalité de la signature électronique ...
- Assurer la légalité de la signature électronique ...
- Comprendre la légalité des signatures électroniques ...
- Déverrouiller le pouvoir de la légitimité de la ...
- Améliorez la légitimité des contrats de freelance ...
- Légitimité de la signature électronique pour les ...
- Assurer la légitimité de la signature électronique ...
- Améliorez la légitimité de la signature ...
- Maximisez la légitimité de la signature électronique ...
- Légitimité de la signature électronique pour les ...
- La légitimité des signatures électroniques pour la ...
- Légalité de la signature électronique pour le ...
- Légalité de la signature en ligne pour les ...
- Déverrouillez le pouvoir de la légalité de la ...
- Légalité de la signature en ligne pour les contrats ...
- Déverrouiller le pouvoir de la légalité de la ...
- Déverrouillez le pouvoir des signatures en ligne ...
- Déverrouillez la légalité de la signature en ligne ...
- Déverrouillez le pouvoir de la signature électronique ...
- Améliorez vos documents avec une signature manuscrite













































