Use Double Factor Authentication to Customize Messages in Your Email and eSignature
Do more online with a globally-trusted eSignature platform
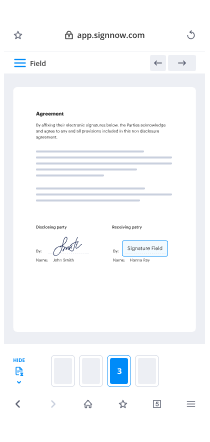
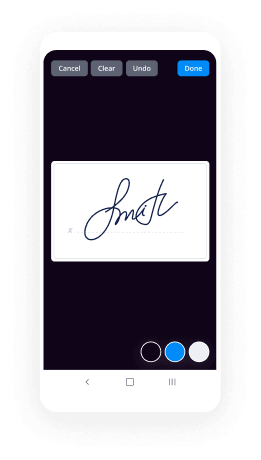
Remarkable signing experience
Reliable reports and analytics
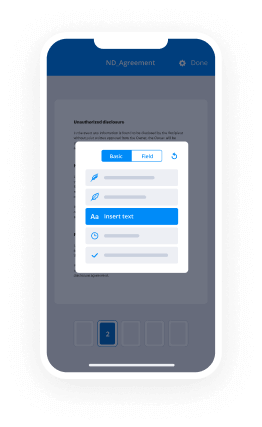
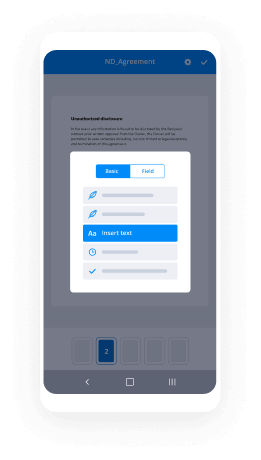
Mobile eSigning in person and remotely
Industry regulations and compliance
Use double factor authentication customize message in your email and eSignature, faster than ever
Useful eSignature add-ons
Découvrez les signatures électroniques airSlate SignNow en action
Solutions airSlate SignNow pour une meilleure efficacité
Les avis de nos utilisateurs parlent d'eux-mêmes






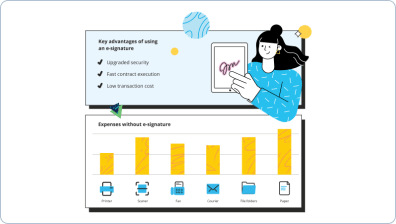
Pourquoi choisir airSlate SignNow
-
Essai gratuit de 7 jours. Choisissez le forfait dont vous avez besoin et essayez-le sans risque.
-
Tarification honnête pour des forfaits complets. airSlate SignNow propose des abonnements sans frais supplémentaires ni frais cachés lors du renouvellement.
-
Sécurité de niveau entreprise. airSlate SignNow vous aide à respecter les normes de sécurité mondiales.

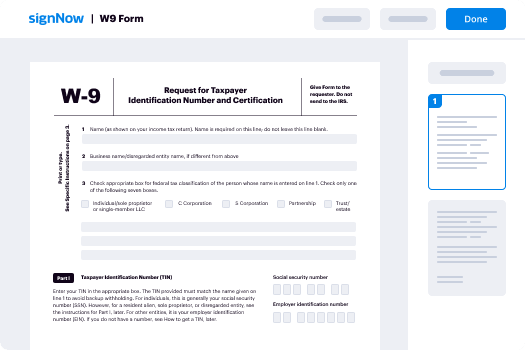
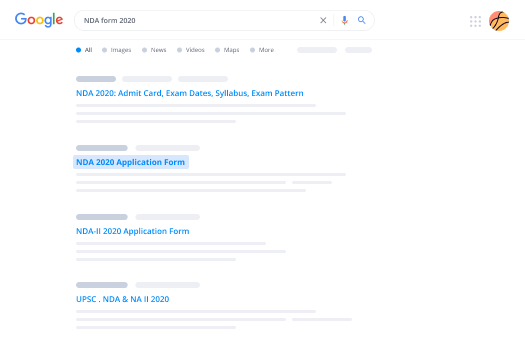
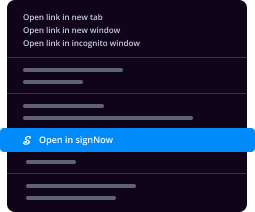
Votre guide étape par étape — use double factor authentication customize message in your email and eSignature
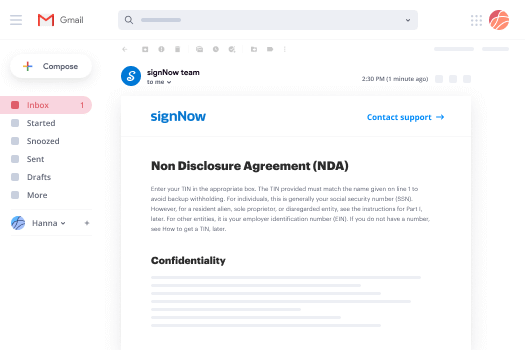
Use double factor authentication, Customize message in your email and eSignature. Get maximum performance from the most trustworthy and safe eSignature solution. Streamline your digital transactions employing airSlate SignNow. Automate workflows for everything from basic personnel documents to complex contracts and payment templates.
Understand how to Use double factor authentication, Customize message in your email and eSignature:
- Import a series of documents from your device or cloud storage.
- Drag & drop smart fillable fields (signature, text, date/time).
- Modify the fields size, by tapping it and selecting Adjust Size.
- Place checkboxes and dropdowns, and radio button groups.
- Add signers and request additional materials.
- Use double factor authentication, Customize message in your email and eSignature.
- Include the formula where you need the field to generate.
- Apply remarks and annotations for the recipients anywhere on the page.
- Approve all adjustments by clicking DONE.
Link up people from inside and outside your enterprise to electronically work on essential signNowwork and Use double factor authentication, Customize message in your email and eSignature anytime and on any device using airSlate SignNow. You can track every activity carried out to your templates, receive notifications an audit statement. Remain focused on your business and customer partnerships while with the knowledge that your data is accurate and secure.
Comment ça marche
Fonctionnalités airSlate SignNow appréciées par les utilisateurs
Découvrez des résultats exceptionnels Use Double Factor Authentication to Customize Messages in Your Email and E-Signature
Obtenez des signatures juridiquement contraignantes dès maintenant !
FAQ
-
What is double factor authentication and how does it enhance security?
Double factor authentication adds an extra layer of security to your digital transactions. When you use double factor authentication, you need to provide two forms of identification before accessing your account. This process is crucial for those using airSlate SignNow to customize messages in your email and e signature, ensuring that your documents remain secure. -
How can I use double factor authentication to customize messages in my email?
To use double factor authentication as you customize messages in your email and e signature, simply enable this feature in your account settings. This will require additional verification when accessing sensitive areas of your account, greatly increasing security while ensuring that your customized messages are sent without compromise. -
What are the pricing options for airSlate SignNow with double factor authentication?
airSlate SignNow offers various pricing tiers that include the double factor authentication feature. Each plan is designed to cater to different business needs, allowing you to use double factor authentication to customize messages in your email and e signature based on your selected subscription. Contact our sales team for a detailed breakdown of pricing options. -
Can I integrate airSlate SignNow with other tools while using double factor authentication?
Yes, airSlate SignNow is designed to seamlessly integrate with various third-party applications. You can confidently use double factor authentication during these integrations to ensure that your customized messages in your email and e signature remain secure across all platforms, enhancing overall workflow security. -
What benefits will I experience when I use double factor authentication?
Using double factor authentication signNowly enhances your account security by requiring two forms of verification. This added layer is particularly beneficial for users looking to customize messages in their email and e signature on airSlate SignNow, as it minimizes the risk of unauthorized access to sensitive documents. -
Is it easy to set up double factor authentication on airSlate SignNow?
Absolutely! Setting up double factor authentication on airSlate SignNow is a straightforward process. Head to your account settings and follow the prompts to enable this feature, allowing you to securely use double factor authentication to customize messages in your email and e signature effortlessly. -
Will using double factor authentication affect the speed of my eSigning process?
While using double factor authentication may add a few extra seconds for verification, the security benefits far outweigh any minor time delays. This is especially important when you are customizing messages in your email and e signature on airSlate SignNow, as it ensures the protection of your valuable document transactions.
Ce que disent les utilisateurs actifs — use double factor authentication customize message in your email and eSignature
Questions fréquemment posées
Comment générer un document et y appliquer une signature électronique ?
Comment puis-je mettre une signature électronique sur un document ?
Comment puis-je taper mon nom dans le champ de signature dans un PDF ?
Obtenez plus pour use double factor authentication customize message in your email and eSignature
Tout savoir sur la signature électronique

Découvrez d'autres use double factor authentication customize message in your email and eSignature
- Application de signature numérique iPad sans effort ...
- Créez votre créateur de signature unique pour PDF ...
- Accédez à votre connexion de compte de signature ...
- Signez des documents PDF en ligne dans Chrome sans ...
- Numérisez ma signature facilement avec airSlate ...
- Découvrez notre visionneuse PDF gratuite avec ...
- Découvrez le meilleur outil d'analyse de signature en ...
- Découvrez le logiciel de signature électronique ...
- Rationalisez votre flux de travail avec notre ...
- Découvrez le meilleur outil de signature de document ...
- Téléchargez un signataire PDF en masse gratuit pour ...
- Rationalisez votre flux de travail avec notre outil de ...
- Découvrez une inscription au portail resman sans ...
- Accédez facilement au téléchargement du fichier ...
- Découvrez les meilleurs outils de signature numérique ...
- Découvrez le meilleur lecteur PDF pour plusieurs ...
- Découvrez le meilleur outil de signature PDF gratuit ...
- Découvrez des solutions de signature électronique ...
- Signez et remplissez en ligne votre document PDF ...
- Découvrez le meilleur logiciel de signature ...