Help Me With Use eSignature in Oracle
Contact Sales
Make the most out of your eSignature workflows with airSlate SignNow
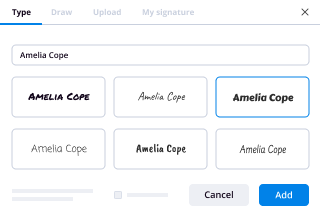
Extensive suite of eSignature tools
Discover the easiest way to Use eSignature in Oracle with our powerful tools that go beyond eSignature. Sign documents and collect data, signatures, and payments from other parties from a single solution.
Robust integration and API capabilities
Enable the airSlate SignNow API and supercharge your workspace systems with eSignature tools. Streamline data routing and record updates with out-of-the-box integrations.
Advanced security and compliance
Set up your eSignature workflows while staying compliant with major eSignature, data protection, and eCommerce laws. Use airSlate SignNow to make every interaction with a document secure and compliant.
Various collaboration tools
Make communication and interaction within your team more transparent and effective. Accomplish more with minimal efforts on your side and add value to the business.
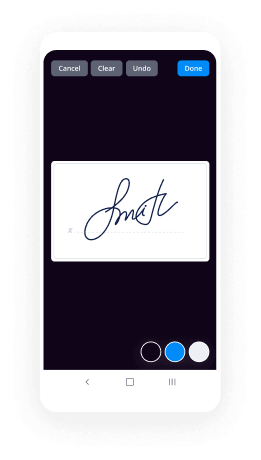
Enjoyable and stress-free signing experience
Delight your partners and employees with a straightforward way of signing documents. Make document approval flexible and precise.
Extensive support
Explore a range of video tutorials and guides on how to Use eSignature in Oracle. Get all the help you need from our dedicated support team.
How To Use eSignature in Oracle
Keep your eSignature workflows on track
Make the signing process more streamlined and uniform
Take control of every aspect of the document execution process. eSign, send out for signature, manage, route, and save your documents in a single secure solution.
Add and collect signatures from anywhere
Let your customers and your team stay connected even when offline. Access airSlate SignNow to Use eSignature in Oracle from any platform or device: your laptop, mobile phone, or tablet.
Ensure error-free results with reusable templates
Templatize frequently used documents to save time and reduce the risk of common errors when sending out copies for signing.
Stay compliant and secure when eSigning
Use airSlate SignNow to Use eSignature in Oracle and ensure the integrity and security of your data at every step of the document execution cycle.
Enjoy the ease of setup and onboarding process
Have your eSignature workflow up and running in minutes. Take advantage of numerous detailed guides and tutorials, or contact our dedicated support team to make the most out of the airSlate SignNow functionality.
Benefit from integrations and API for maximum efficiency
Integrate with a rich selection of productivity and data storage tools. Create a more encrypted and seamless signing experience with the airSlate SignNow API.
Collect signatures
24x
faster
Reduce costs by
$30
per document
Save up to
40h
per employee / month
Our user reviews speak for themselves






-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
Intuitive UI and API. Sign and send documents from your apps in minutes.
A smarter way to work: —how to industry sign banking integrate
FAQs
-
How do I register and buy voucher for OCAJP, OCPJP, Java certifications?
You can register for exam in three ways.Purchase Exam Voucher from Oracle University and Register at Pearson VUERegister for an Exam at Oracle Testing CenterRegister at Pearson VUE websiteIn the below sections read every option in detail.1)Purchase Exam Voucher from Oracle University and Register at Pearson VUEYou can purchase exam voucher at Oracle University.Two kinds of vouchers availableOracle proctored exam voucher :This voucher cost is Rs 10100. Only credit cards are accepted to buy any voucher in India.Here is the link to purchase this voucher : Oracle proctored exam voucherAfter you place your order you will receive an order confirmation e-mail. Once payment is processed you will receive a second e-mail that will include your exam voucher number -- you need this number to register for your exam at Pearson Vue (Oracle :: Pearson VUE)Exam vouchers are only valid for scheduling an Oracle proctored exam at a Pearson VUE test center in India. When scheduling an exam, use the voucher as payment for the exam. Vouchers expire six months from date of purchase. The Voucher must be used to schedule and sit for the exam on or before the expiration date. The specific expiration date will be sent with the voucher number via email. All sales of exam vouchers are final, no exceptions.Purchase Bundle:This voucher is only for Indians.This voucher cost is Rs. 11,957 .This voucher features are1 Certification Exam Voucher1 Free Exam retake30-days access to the Kaplan SelfTest practice TestThe rules of above voucher will be applicable to this voucher also.Here is the link to purchase this voucher : Bundles2)Register for an Exam at Oracle Testing CenterWe don’t have many Oracle Testing centers in India . We have few Oracle Testing centers in major cities like Mumbai, Bangalore, Chennai, etc.You can directly register for the exam through Oracle Testing center.First Open this link on any of the browser: https://education.oracle.com/pls...Follow the steps as shown in the website.Many people doesn’t go with this option. Because there are less centers.Prefer to register at Pearson VUE website.3)Register at Pearson VUE websiteFirst open this link (Oracle :: Pearson VUE). It opens the website and click on sign-in if you registered or create account yourself an then sign-in. It asks you sign in credentials , Enter your credentials.Once you sign-in with your credentials it takes you into the below screen. Now click on Proctored exam.Type Java SE 8 in the Find Exam test box and select Java SE 8 Programmer INow Click on Schedule this Exam button and it asks you to confirm Exam details , check it once and then click on Proceed to scheduling Button.Enter your address in the Find test centers near text box and select the test center which is near to you and click on Next Button.Select any date on the calendar which is comfortable for you. And it opens available timings and select particular timing.Confirm the exam details and click Proceed to checkout button at bottom right side corner.Click on Next Button.Click on Next Button and again click on Next buttonIf you have bought voucher from Oracle website apply that voucher code.If you don’t Enter your credit card details. Only Credit cards are accepted.Enter Billing address and click on Next and finally submit the Order.Once your payment done , you will receive two details one regarding payment confirmation and other your slot confirmation. Take print out of second email.ID Proof’sYou need to bring two of the following ID proof’s for exam center.Primary IDExamples of accepted Primary ID:A currently valid signed passport of any countryA currently valid signed government issued photo driving licence (full or provisional)Employee ID / work badgeMilitary IDSchool IDSecondary IDMust contain your signature. Examples of accepted Secondary ID:Credit CardDebit CardBank Cardanother ID from the Primary ID listExam Reschedule PolicyIf you wish to reschedule your exam appointment, you must reschedule at least 24 hours prior to your appointment. Rescheduling an exam less than 24 hours before an exam appointment is subject to a same-day forfeit exam fee. Exam fees are due for no-shows.Exam Cancellation PolicyIf you wish to cancel your exam appointment, you must cancel at least 24 hours prior to your exam appointment. Canceling an exam less than 24 hours before scheduled exam is subject to a same-day forfeit exam fee. Exam fees are due for no-shows.If you want any other help , you can take Pearson VUE customer serviceFollow this link Customer ServiceExam ResultsOnce you done with your exam , you will get an email within 15 minuets which contains link to your results .Opent his URL (CertView Login)Login with you credentials(Oracle account details).You results will appear there.You will also get E-Certficate within 2 days in same website.You need to fill a separate form to get your printed Certificate , you will get it after 2 10 weeks to your address.Free Java T ShirtIf you pass OCAJP 8 , you can get free Java T shirt .You need apply in a separate form for Java T shirt.You can apply for this at this link: https://go.oracle.com/java-tshirt.You will get this T-shirt after 1 month through courier to your address.If you are preparing for the exam, read the below links to understand how to prepare for each exam:How to prepare for OCAJP exam?How to prepare for OCPJP Certification Exam?
-
As first time entrepreneurs, what part of the process are people often completely blind to?
The 100 Rules for Being a First-Time EntrepreneurIf you Google “entrepreneur” you get a lot of mindless cliches like “Think Big!” For me, being an “entrepreneur” doesn’t mean starting the next “Faceook”. Or even starting any business at all.It means finding the challenges you have in your life, and determining creative ways to overcome those challenges. However, in this post I focus mostly on the issues that come up when you first start your company. These rules also apply if you are taking an entrepreneurial stance within a much larger company (which all employees should do).Just as good to be an “entreployee” as an “entrepreneur”. Either one will help you survive this world of increased economic uncertainty.For me, I’ve started several businesses.Maybe 17 have failed out of 20. I fail quickly. I fail frequently. Entrepreneurship is a sentence of failures punctuated by brief success.I’m invested in about 28 private companies. I’ve advised probably another 50 private companies. I’m on the board of several private companies and one public company. The companies ranging from $0 in revenues to a billion in revenues.Along the way I’ve compiled a list of rules that have helped me deal with every aspect of being an entrepreneur in business and some in life.Here’s the real rules:A) It’s not fun. I’m not going to explain why it’s not fun. These are rules. Not theories. I don’t need to prove them.But there’s a strong chance you can hate yourself throughout the process of being an entrepreneur. Keep sharp objects and pills away during your worst moments. And you will have them. If you are an entrepreneur and agree with me, please note this in the comments below.B) Try not to hire people. You’ll have to hire people to expand your business. But it’s a good discipline to really question if you need each and every hire.C) Get a customer. This seems obvious. But it’s not. Get a customer before you start your business, if you can.So many people say to me, “I have an idea. Can you introduce me to VCs?”There is a HUGE gap between “idea” and “professional venture capital”.In the middle of that gap is “customer”.D) If you are offering a service, call it a product.Oracle did it. They claimed they had a database. But if you “bought” their database they would send in a team of consultants to help you “install” the database to fit your needs.In other words, for the first several years of their existence, they claimed to have a product but they really were a consulting company. Don’t forget this story. Products are valued higher than services.And almost EVERY major software product company was a service company in the beginning. Don’t forget that.E) It’s OK to fail. Start over. Hopefully before you run out of money. Hopefully before you take in investor money. Or, don’t worry about it. Come up with new ideas. Start over.F) Be profitable. Try to be profitable immediately. This seems obvious but it isn’t. Try not to raise money. That money is expensive.G) When raising money: if it’s not easy then your idea is probably incapable of raising money. If its easy, then take as much as possible. If its TOO easy, then sell your company (unless you are Twitter, etc).(if its too easy, sell your company)H) The same goes for selling your company. If it’s not easy, then you need to build more. Then sell. To sell your company, start getting in front of your acquirers a year in advance. Send them monthly updates describing your progress. Then, when they need a company like yours, your company is the first one that comes to mind.Don’t be like that guy in the TV show “Silicon Valley”. If someone offers you ten million for a company that has no revenues, then sell it. Not everything is going to be a Facebook. And even the Google guys tried to sell their company for ONE MILLION DOLLARS to Yahoo before they were revenue positive.SELL THE COMPANY.I) Competition is good. It turns you into a killer. It helps you judge progress. It shows that other people value the space you are in. Your competitors are also your potential acquirors.J) Don’t use a PR firm. Except maybe as a secretary. You are the PR for your company. You are your company’s brand. You personally.I’ve never had a good PR company. I’ve had good PR secretaries. But they are cheaper. One time I hired a PR company and they accidentally sent me the contract for Terry Bradshaw. He was paying $10,000 a month. How did they do for him?K) Communicate with everyone. Employees. Customers. Investors. All the time. Every day.Employees want to know what to do. And they want to know you are thinking of their overall career.Customers want to know how to keep their bosses calm.Investors want to be your friend and want to know they can count on you when time’s are tough.L) Do everything for your customers. This is very important.Get them girlfriends or boyfriends. Speak at their charities. Visit their parents for Thanksgiving. Help them find other firms to meet their needs. Even introduce them to your competitors if you think a competitor can help them or if you think you are about to be fired. Always think first, “What’s going to make my customer happy?”Note: EVEN if that means introduce them to a competitor. If you are the SOURCE, then everybody comes back to the source.M) Your customer is not a company. There’s a human there. What will make my human customer happy? Make him laugh. You want your customer to be happy.N) Show up. Go to breakfast/lunch/dinner with customers. Treat.O) History. Know the history of your customers in every way. Company history, personal history, marketing history, investing history, etc.P) Micro-manage software development. Nobody knows your product better than you do. If you aren’t a technical person, learn how to be very specific in your product specification so that your programmers can’t say: “well you didn’t say that!”Q) Hire local. You need to be able to see and talk to your programmers. Don’t outsource to India. I love India. But I won’t hire programmers from there while I’m living in the US.R) Sleep. Don’t buy into the 20 hours a day entrepreneur myth. You need to sleep 8 hours a day to have a focused mind.If you are working 20 hours a day, then that means you have flaws in how you are managing your time. You can argue about this but it’s true.S) Exercise. Same as above. If you are unhealthy, your product will be unhealthy.T) Emotionally Fit. DON’T have dating problems and software development problems at the same time. VCs will smell this all over you.U) Pray. You need to. Be grateful where you are. And pray for success. You deserve it. Pray for the success of your customers. Heck, pray for the success of your competitors. The better they do, it means the market is getting bigger. And if one of them breaks out, they can buy you.V) Buy your employees gifts. Massages. Tickets. Whatever. I always imagined that at the end of each day my young, lesbian employees (for some reason, most employees at my first company were lesbian) would be calling their parents and their mom and dad would ask them: “Hi honey! How was your day today?” And I wanted them to be able to say: “It was the best!” Invite customers to masseuse day. W) Treat your employees like they are your children. They need boundaries. They need to be told “no!” sometimes. And sometimes you need to hit them in the face (ha ha, just kidding). But within boundaries, let them play.X) Don’t be greedy pricing your product. If your product is good and you price it cheap, people will buy. Then you can price upgrades, future products, and future services more expensive. Which goes along with the next rule.Y) Distribution is everything. Branding is everything. Get your name out there, whatever it takes. The best distribution is of course word of mouth, which is why your initial pricing doesn’t matter.Write a blog about your industry and be very honest about all the flaws (even your own) that is currently in your industry.Authenticity is the best branding.Z) Don’t kill yourself. It’s not worth it. Your employees need you.Your children or future children need you. It seems odd to include this in a post about entrepreneurship but we’re also taking about keeping it real.Most books or “rules” for entrepreneurs talk about things like “think big”, “go after your dreams”. But often dreams turn into nightmares. I’ll repeat it again. Don’t kill yourself. Call me if things get too stressful. Or more importantly, make sure you take proper medicationAA) Give employees structure. Let each employee know how his or her path to success can be achieved. All of them will either leave you or replace you eventually. That’s OK. Give them the guidelines how that might happen. Tell them how they can get rich by working for you.BB) Fire employees immediately. If an employee gets “the disease” he needs to be fired. If they ask for more money all the time. If they bad mouth you to other employees. If you even think they are talking behind your back, fire them.The disease has no cure. And it’s very contagious. Show no mercy. Show the employee the door. There are no second chances because the disease is incurable.I don’t say this because I want anyone to be hurt. But if you’ve followed the rules above then you are treating employees well already. NOBODY should spread the disease and badmouth you or your customers.CC) Make friends with your landlord. If you ever have to sell your company, believe it or not, you are going to need his signature (because there’s going to be a new lease owner)DD) Only move offices if you are so packed in that employees are sharing desks and there’s no room for people to walk.EE) Have killer parties. But use your personal money. Not company money. Invite employees, customers, and investors. .FF) If an employee comes to you crying, close the door or take him or her out of the building. Sit with him until it stops. Listen to what he has to say. If someone is crying then there’s been a major communication breakdown somewhere in the company. Listen to what it is and fix it. Don’t get angry at the culprit’s. Just fix the problem.(you don’t want your employees to be sad.)GG) At Christmas, donate money to every customer’s favorite charity. But not for investors or employees.HH) Have lunch with your competitors. Listen and try not to talk. One competitor (Bill Markel from Interactive 8) once told me a story about how the CEO of Toys R Us returned his call. He was telling me this because I never returned Bill’s calls. Ok, Bill, lesson noted.II) Ask advice a lot. Ask your customers advice on how you can be introduced into other parts of their company. Then they will help you. Because of the next rule…JJ) Hire your customers. Or not. But always leave open the possibility. Let it always dangle in the air between you and them. They can get rich with you. Maybe. Possibly. If they play along. So play.KK) On any demo or delivery, do one extra surprise thing that was not expected. Always add bells and whistles that the customer didn’t pay for.This is such an easy way to over deliver I’m surprised people don’t do it 100% of the time. They do it maybe 1% of the time. So this is an easy way to compete and surprise and delight.LL) Understand the demographic changes that are changing the world. Where are marketing dollars flowing and can you be in the middle. What services do aging baby boomers need? Is the world running out of clean water? Are newspapers going to survive? Etc. Etc. Read every day to understand what is going on.LLa) Don’t go to a lot of parties or “meetups” with other entrepreneurs. Work instead while they are partying.MM) But, going along with the above rule, don’t listen to the doom and gloomers that are hogging the TV screen trying to tell you the world is over. They just want you to be scared so they can scoop up all the money.NN) You have no more free time. In your free time you are thinking of new ideas for customers, new ideas for services to offer, new products.OO) You have no more free time, part 2. In your free time, think of ideas for potential customers. Then send them emails: “I have 10 ideas for you. Would really like to show them to you. I think you will be blown away. Here’s five of them right now.”OOa) Depressions, recessions, don’t matter. There’s $15 trillion in the economy. You’re allowed a piece of it:FedEx, Microsoft, HewlettPackard, and many huge companies were started in recessions or depressions. Leave economics to the academics while they leave good business to you.PP) Talk. Tell everyone you ever knew what your company does. Your friends will help you find clients.QQ) Always take someone with you to a meeting. You’re bad at following up. Because you have no free time. So, if you have another employee. Let them follow up. Plus, they will like to spend time with the boss. You’re going to be a mentor.RR) If you are consumer focused: your advertisers are your customers. But always be thinking of new services for your consumers. Each new service has to make their life better. People’s lives are better if: they become healthier, richer, or have more sex. “Health” can be broadly defined.SS) If your customers are advertisers: find sponsorship opportunities for them that drive customers straight into their arms. These are the most lucrative ad deals (see rule above). Ad inventory is a horrible business model. Sponsorships are better. Then you are talking to your customer.TT) No friction. The harder it is for a consumer to sign up, the less consumers you will have. No confirmation emails, sign up forms, etc. The easier the better.TTA) No fiction, part 2. If you are making a website, have as much content as you can on the front page. You don’t want people to have to click to a second or third page if you can avoid it. Stuff that first page with content. You aren’t Google. (And, 10 Unusual Things You Didn’t Know About Google)UU) No friction, part 3. Say “yes” to any opportunity that gets you in a room with a big decision maker. Doesn’t matter if it costs you money.VV) Sell your company two years before you sell it. Get in the offices of the potential buyers of your company and start updating them on your progress every month. Ask their advice on a regular basis in the guise of just an “industry catch-up”WW) If you sell your company for stock, sell the stock as soon as you can. If you are selling your company for stock it means:a. The market is such that lots of companies are being sold for stock.b. AND, companies are using stock to buy other companies because they value their stock less than they value cash.c. WHICH MEANS, that when everyone’s lockup period ends, EVERYONE will be selling stock across the country. So sell yours first.XX) Execution is a dime a dozen. If you have an idea worth pursuing, then just make it. You can build any website for cheap. Hire a programmer and make a demo. Get at least one person to sign up and use your service. If you want to make Facebook pages for plumbers, find one plumber who will give you $10 to make his Facebook page. Just do it.Fail quickly. Good ideas are HARD. It’s execution that is a dime a dozen.YY) Don’t use a PR firm, part II. Set up a blog. Tell your personal stories (see “33 tips to being a better writer” ). Let the customer know you are human, approachable, and have a real vision as to why they need to use you. Become the voice for your industry, the advocate for your products. If you make skin care products, tell your customers every day how they can be even more beautiful than they currently are and have more sex than they are currently getting. Blog your way to PR success. Be honest and bloody.ZZ) Don’t save the world. If your product sounds too good to be true, then you are a liar.ZZa) Your company is always for sale.AAA) Frame the first check. I’m staring at mine right now.BBB) No free time, part 3. Pick a random customer. Find five ideas for them that have nothing to do with your business. Call them and say, “I’ve been thinking about you. Have you tried this?”CCC) No resale deals. Nobody cares about reselling your service. Those are always bad deals.DDD) Your lawyer or accountant is not going to introduce you to any of their other clients. Those meetings are always a waste of time.EEE) Celebrate every success. Your employees need it. They need a massage also. Get a professional masseuse in every Friday afternoon. Nobody leaves a job where there is a masseuse.FFF) Sell your first company. I have to repeat this. Don’t take any chances. You don’t need to be Mark Zuckerberg. Sell your first company as quick as you can. You now have money in the bank and a notch on your belt. Make a billion on your next company.Note Mark Cuban’s story. Before he started Broadcast and rode it to a few billion, he sold his first software company for ten million.GGG) Pay your employees before you pay yourself.HHH) Give equity to get the first customer. If you have no product yet and no money, then give equity to a good partner in exchange for them being a paying customer. Note: don’t blindly give equity. If you develop a product that someone asked for, don’t give them equity. Sell it to them. But if you want to get a big distribution partner whose funds can keep you going forever, then give equity to nail the deal.III) Don’t worry about anyone stealing your ideas. Ideas are worthless anyway. It’s OK to steal something that’s worthless.IIIA) Follow me on twitter.Questions from ReadersQuestion: You say no free time but you also say keep emotionally fit, physically fit, etc. How do I do this if I’m constantly thinking of ideas for old and potential customers?Answer: It’s not easy or everyone would be rich.Question: if I get really stressed about clients paying, how do I get sleep at night?Answer: medicationQuestion: how do I cold-call clients?Answer: email them. Email 40 of them. It’s OK if only 1 answers. Email 40 a day but make sure you have something of value to offer.Question: how can I find cheap programmers or designers?Answer: if you don’t know any and you want to be cheap: use Hire Freelancers & Find Freelance Jobs Online, Elance, or craigslist. But don’t hire them if they are from another country. You need to communicate with them even if it costs more money.Question: should I hire programmers?Answer: first…freelance. Then hire.Question: what if I build my product but I’m not getting customers?Answer: develop a service loosely based on your product and offer that to customers. But I hope you didn’t make a product without talking to customers to begin with?Question: I have the best idea in the world, but for it to work it requires a lot of people to already be using it. Like Twitter.Answer: if you’re not baked into the Silicon Valley ecosystem, then find distribution and offer equity if you have to. Zuckerberg had Harvard. MySpace had the fans of all the local bands they set up with MySpace pages. I (in my own small way) had Stock Market - Business News, Market Data, Stock Analysis - TheStreet when I set up Stockpickr! Your Source for Stock Ideas. I also had 10 paying clients when i did my first successful business fulltime.Question: I just lost my biggest customer and now I have to fire people. I’ve never done this before. How do I do it?Answer: one on meetings. Be Kind. State the facts. Say you have to let people go and that everyone is hurting but you want to keep in touch because they are a great employee. It was an honor to work with them and when business comes back you hope you can convince them come back. Then ask them if they have any questions. Your reputation and the reputation of your company are on the line here. You want to be a good guy. But you want them out of your office within 15 minutes. It’s a termination, not a negotiation. This is one reason why it’s good to start with freelancers.Question: I have a great idea. How do I attract VCs?Answer: build the product. Get a customer. Get money from customer. Get more customers. Build more services in the product. Get VC. Chances are by this point, the VCs are calling you.Question: I want to build a business day trading.Answer: bad ideaQuestion: I want to start a business but don’t know what my passion is:Answer: skip to the post: “How to be the luckiest person alive”. Do the Daily Practice. Within six months your life will be completely different.Question: I want to leave my job but I’m scared.Answer: same as above question. The Daily Practice turns you into a healthy Idea Machine. Plus luck will flow in from every direction.Final rule: Things change. Every day. The title of this post, for instance, says “100 Rules”. But I gave about 70 rules (including the Q&A). Things change midway through. Be ready for it every day. In fact, every day figure out what you can change just slightly to shake things up and improve your product and company.Your business is not your life. When you start a business you also get a cognitive bias that makes you think your business is GREAT.Every day make sure you are not smoking crack. The most important thing is your health so you can be persistent. If you smoke crack you can die.I hope you succeed. Because I really need that smart toilet that sends my doctors text messages after doing urinalysis on my pee every day.Good luck.
-
What are some of the most interesting courses at Stanford's GSB MBA program?
I would agree with the answers given by Pierre Len and Robert Lopez related to how this is largely based upon preference. To answer the question in more detail, it is helpful to provide a bit more context on the overall path of GSB classes and how students typically differentiate in the classes they choose.As Anneke Jong wrote in a blog post (http://annekejong.blogspot.com/2...), the first year is quite challenging for a number of reasons, and few students look back on it as academically inspiring. Most complain incessantly about it, sometimes with good reason and sometimes due to lack of perspective (I count myself in the latter group). It is the year where you take the classes that any MBA would be expected to take. As I reflect on it now, I wish that I had been less negative on it in the moment, as many of the classes were quite good and / or will serve me well, particularly finance, accounting, economics, and data and decisions (i.e., statistics). Though it is painful, the administration is wise in packing these into the first year. By the end, you are done with the "required" courses and the second year is wide open. As long as you complete a grand total of 105 course units, including 93 at the GSB and 93 graded (vs. pass/fail), you can graduate. By the end of the first year, most students have ~60 units completed, so in addition to a lighter course load, the classes are completely of your choosing. During the second year, students end up splitting down a number of tracks. As would be expected, some focus on finance / investment classes, others on general management / entrepreneurship classes, others on product design / marketing classes, and others on leadership / soft skills (NOTE: this is my rough categorization for the purposes of this answer, not an official categorization of the Stanford GSB). Still others venture "across the street" whether on a one-off basis or through joint degree programs, taking classes at the law school, medical school, E-IPER program (environment and resources), design school, education school, public policy / administration program (whether Stanford or Harvard Kennedy), etc. These are rough lines, and many students take classes across several of them. From what I have seen though, you can generally see each person allocating his / her time in 1-2 tracks more than the others. I personally focused on general management / entrepreneurship and leadership / soft skills, so I can only really speak to those. I will try to reference other highly rated classes as well.The "signature" classes: While there might be some differences of opinion on these, there are a couple of classes that are notable across generations of GSB students. This is with good reason too, these classes end up being described as life and / or career changing.Interpersonal Dynamics (OB 374) -- This is probably the most famous of them all. Commonly called "touchy feely," over 90-95% of the class takes this and many (including me) describe it as transformational. The premise of the course is that communication and connection between you and others is one of, if not the most important factors related to your personal and professional success. Furthermore, most of us aren't really all that good at it. We tend to speak and respond to others, especially during times of stress, in ways that are counterproductive and prone to hurting, rather than building relationships. There is a lecture portion of the course, but the real action takes place in T-group (i.e., training group), where a group of 12 students and 2 facilitators sit in a circle for 3-4 hours at a time. There is no agenda. The group just talks, going deep on topics relevant to each student. Disagreements and conflicts arise. Real-time feedback ensues. While it sounds unstructured, it is very often a tremendously powerful experience, changing how you communicate and connect with others.Managing Growing Enterprises (STRAMGT 355) -- Another extremely useful class, this might be better titled "Managing Difficult Situations." The most famous professor is Irv Grousbeck, but all the professors (including Joel Peterson, Jim Ellis, Kevin Taweel) are experienced practitioners who engage students in challenging role plays related to common management situations involving complex decisions and tough conversations. Each class typically revolves around a real-life case study, and the protagonists are present. After about an hour and a half of role playing the various situations, the protagonists address the class about how they handled each situation, what worked well, what didn't work well, etc.The rest of the "super round" classes: Each year, first year students go through a registration process where they can "super round" classes that are typically very high in demand. The above two classes are always on this list. The classes below are as well. Typically, each student will only get two of these (including the "signature" classes above)Leadership Perspectives (OB 363) -- A relatively new class, this has become incredibly popular in recent years. It is taught by Joel Peterson (former CEO of Trammel Crow, current Chairman of JetBlue, Managing Director of Peterson Partners, etc.) and Charles O'Reilly, a really excellent research professor focused on leadership. The format of the class includes one session per week where a prominent leader addresses the full class and a second session where small groups break out to discuss and reflect on what was learned from the leader. During my class, we heard from CEOs / board members, former athletes, a city mayor, a military general, and a nonprofit leader, among others. Each gave us 15-20 minutes of background on his / her life and path, then the next 1 hour+ was open for questioning, where we could ask just about anything (and questions / responses were guaranteed confidential within the class). It is fascinating to see the similarities and differences among leaders as they honestly discuss their personal and professional successes and failures over time.Entrepreneurship and Venture Capital (STRAMGT 354) -- While I didn't take this class, it is also extremely popular. It is taught by long-time venture capitalist Peter Wendell and Eric Schmidt. The guest list is phenomenal. This class was referenced in the recent New York Times article on Stanford (http://www.newyorker.com/reporti...).Investment Management and Entrepreneurial Finance (FINANCE 321) -- While I didn't take this class, it is extremely popular among students with interest / focus on the finance / investment space. It is taught by Jack McDonald, a long-time professor and investor guru. I'll leave further description to an alum / student who has actually taken the class.Other interesting (and popular) classes that I did takeLeadership Fellows (OB 330/331) -- Each year, ~66 second year students take part in the Arbuckle Leadership Fellows program. While one purpose of the program is to help facilitate the Leadership Labs class taken by every first year student, there is also a heavy "coaching" component to the experience. Through this, the students in the class are trained by professional executive coaches to be coaches themselves. The point is not that most of us will actually become executive coaches (though some might), but rather that coaching is a critical part of managing, and something that many managers are not actually that good at. During the class, each student has ~3 first year students that he / she coaches for two quarters both to practice what is learned in class but more importantly, to help the first year student improve in whatever areas of life the student so desires. Lives of Consequence (OB 383) -- A small seminar class, this is focused on giving students time to reflect on what sort of life each student wants to lead. The class includes some study of individuals who have been thought to have led a "consequential" life. More importantly, the class asks each student to complete several exercises focused on his / her own life, including writing his / her own obituary and eulogy (though unusual, writing my own and listening to what others wrote about themselves was an amazing experience). Few people find the time for such structured reflection, which is exactly what this class allows.Becoming a Leader (GSBGEN 571) -- Many students coming out of MBA programs will become managers within a few years, and becoming a manager means working not just for those to whom you report, but those who report to you. This is often a difficult transition. This half-quarter class uses the experience of recent GSB graduates (classes 2000 and later, more or less) as a tool to expose us to common challenges faced by first time and young managers. Some of the examples are highlighted in short videos, but there are also two panel sessions.The Paths to Power (OB 377) -- Taught by Jeff Pfeffer (http://jeffreypfeffer.com/), this class is about the power and, as he says in his book, why some people have it and others don't. It is often described as a controversial class, with rationale being that it just teaches tools that allow one to accumulate power. I did not find it to be particularly controversial, but rather thought that it just highlighted a set of very basic but important considerations -- whether others know about the good work you're doing, what your network looks like and how central you are as a node within it, how you say what you say, how much social and professional capital you have, how unique you are in your organization, etc. -- that can lead to gaining and sustaining power within an organization. Throughout the course, case studies are used, and at least once a week, case protagonists and / or professionals related to the topic at hand guest teach.Formation of New Ventures (STRAMGT 353) -- This is a survey course that uses case studies to introduce challenges and considerations across the new venture lifecycle, from idea and team formulation through IPO or M&A (at which point the venture is presumably no longer new). Each class, the protagonists of the case being taught are present to comment on the discussion and what they actually did, why, how it turned out, etc. There are several sections of this class. I took a section with Andy Rachleff (Benchmark, Wealthfront) and Mark Leslie (Veritas) that was focused entirely on information technology companies. Other sections are taught by Jim Ellis (Asurion), Jeff Chambers (TA Associates), John Mortgridge (Cisco), Charles Holloway, and George Foster (Stanford).Building and Managing Professional Sales Organizations (STRAMGT 351) -- Where Formation of New Ventures is a survey course on many topics related to starting a company, this class focuses on precisely what the name implies. You're either building product or you're selling it. I knew shockingly little about the latter step before this class, and found it to be among the most practical during my whole time at the GSB. Similar to above, this class is taught with case studies, and the protagonists join each class to share their experience and learning. Additionally, there are projects and simulations used to apply the class materials. Mark Leslie, an amazing sales CEO for decades in Silicon Valley conceived of the class with James Lattin on the academic side. They are now joined in different sections by Peter Levine (A16Z), Kirk Bowman (Accel), and Mark Stevens (long time Sequoia).Conflict Management and Negotiation (OB 381) -- This is about exactly what the title suggests. Conflict and negotiation can be uncomfortable or even painful, so the course is more than 50% focused on simulations between classmates where you practice effective tools and then reflect on the outcomes. And it does get more natural with practice...Sports Business Management (GSBGEN 360), Sports Business Financing (GSBGEN 561), and Sports Marketing (GSBGEN 562) -- The GSB has a number of courses and course sequences that focus on particular topics of interest for students. I have some interest in sports and took two of the three courses above with George Foster. You do have to be interested in sports for these classes, but if you are, it is a real treat. Aside from the annual Billy Beane visit, Professor Foster manages to get the biggest names in Bay Area, and sometimes national sports, into the room discussing just about every topic related to business and sports. As you will see below, there are many other courses delving into different verticals, such as philanthropy, real estate, and entertainment.Other interesting (and popular) classes that I did not takeAligning Start-Ups with their Market (STRAMGT 359) with, Andy Rachleff, which delves deep into another topic introduced in Formation of New Ventures, product-market fitCreating a Start-Up (STRAMGT 356/366) with Haim Mendelson, whereby teams of students (often across graduate programs) create a company plan and sometimes, take the product to market during and after a two quarter course togetherBiodesign Innovation (OIT 384/385) -- some similarities in process to above, but where product is focused on healthcare technologiesEntrepreneurial Design for Extreme Affordability (OIT 333/334) -- some similarities in process to above, but where product is focused on technologies that benefit people and communities in developing countries (through Stanford SEED program)Corporate Financial Modeling (FINANCE 350) with Peter DeMarzo, who wrote our book on itMergers and Acquisitions (ACCT 332), guest taught by Safra Catz (President of Oracle)Understanding the Recent Financial Crisis (GSBGEN 340), Fiscal Policy (GSBGEN 363), and Contemporary Economic Policy (MGTECON 381) with User-13808067191255951908, former Economic Policy Advisor to President George W. Bush and Director of the US National Economic CouncilDesigning Happiness (MKTG 355) and Social Brands (MKTG 353) with Jennifer Aaker, author of The Dragonfly EffectReal Estate Investment (GSBGEN 306)Leadership in the Entertainment Industry (OB 388)Strategic Philanthropy (GSBGEN 381)
-
What are the current topics for a paper presentation by an ECE student?
List of all Technical topics (ECE) in recent trend is given below :A Digital Speech Effects SynthesizerAdvanced Queue Management TechniquesAgent Mediated E-commerceAircarsAircraft GPS TrackingAmbiophonicsAn Electric BicycleLogin application in java using model view controller(mvc) and MySQL databaseAnatomy and working of search enginesAndroid a smart phone operating system by googleAnti-hiv using nano robotsApache hadoop introductionApplication of microcontroller in vehicle monitoring and security systemAqua communication using modemArtificial intelligence on expert systemsAn iPhone application for visualizing pollution mapsAnalysis of Minimum Energy Performance Standards (MEPS) for Domestic Electrical appliancesAnalysis on Performance of Freeware ToolsAndroid Operating SystemAnimatronicsAntenna Analysis Using Wavelet RepresentationsAnti-Jamming wireless systemsApplication of Genetic Algorithms in Network routingApplication of LED for Domestic ApplicationsApplications of Graph Theory to Metabolic PathwaysApplications of Soft Computing in Medical Image AnalysisApplications of speech recognitionApproximate string matching for Music retrievalARQ Schemes for Wireless Data CommunicationsArtificial EyeArtificial immune system.Artificial intelligence for speech recognitionAspects of Database Security and Program SecurityAttacks on Smart CardsAugmented RealityAuthentication and securing the systemsAutomated Network Address AssignmentAutomated Software Testing of ApplicationsAutomatic Device Driver Synthesis From Device SpecificationsAutomatic sound-based user grouping for real time online forumsAutomatic Video Surveillance SystemsAutonomic ComputingAutomatic Conveyor for Industrial AutomationAttendance Monitoring Intelligent ClassroomAn Automatic Mobile Recharge StationBidirectional Power Control for hybrid vehiclesBiomolecular ComputersBiometrics IRIS techniqueBio sensors (photonics)BiochipsBio-Medical Instrumentation and Signal analysisBiometric SecurityBiometric TechnologyBiometrics Based AuthenticationBio-Molecular ComputingBionic eye possible path toward artificial retinaUltrasonic Based Distance Measurement SystemWireless Advanced Flight Systems Aircraft Monitoring SystemBlade ServersBlue GeneBlue sat Communications ProtocolBlue-sat Radio Switching CircuitBluetooth Based Smart Sensor NetworksBrain computer interfaceBiomass gasifier for thermal and electrical applicationsBittorrent a revolution in p2p technologyBlue brainBlue eyes technologyBrain controlled car for disabled using artificial intelligenceBrain gateBrain port deviceBrain Finger Print TechnologyBrian Gate TechnologyBroadband via satellite to Rural AreasCapability Maturity Model Programming (CMM)Capacity of Ad-hoc Wireless NetworksVehicle Speed Sensing and Smoke Detecting SystemIntelligent Fire Sprinkler SystemCapturing packets in secured networksCarbon nano tube electronicsCDMA Wireless Data TransmitterCellular CommunicationsCellular Digital Packet DataCellular Neural NetworkCellular technologies and securityCarbon nanotubesChallenges in mobile ad hoc networks (manets)Cloud computingCloud computing concepts and designCensoring private information from network packet tracesChannel Allocation Algorithms for Mobile TelephonyGSM based Advanced Wireless Earthquake Alarm System for early warningIntelligent Wireless Talking Bus StopChannel Coding and Decoding for Mobile CommunicationsChannel Estimation in MIMO SystemsCharacterization of Piezoelectric ElementsChess AlgorithmChoreographyAqua communication using modemCircuit and safety analysis systemClassification, Clustering and Application in Intrusion Detection SystemClassification, Clustering and their Application for Damage Detection in MechanicalClustering Enterprise JavaCoding in high noise environmentsCold fusionCollaborative Mobile EnvironmentsCombined Input Output Queued SwitchesCompact peripheral component interconnect (CPCI)Compliers and its workingCompression and distribution of volumetric data setsComputational Geometry in Drug DesignComputational Intelligence and LinguisticsComputational neuroscienceComputational PhotographyComputer ForensicsComputer Viruses(Malwares, Trojons, Spywares)Computerized Paper Evaluation using Neural NetworkConcurrent Programming and Parallel distributed O.S.Condition Monitoring of Power System EquipmentConditional Access SystemContent Management Systems(WordPress, Joomla, Drupal etc)Continuously variable transmission (CVT)Control & Signal Processing Techniques in Financial EngineeringControl and Optimization Methods in Communication NetworksControl of a 3-d overhead craneControl of heterogeneous networksControl System Wireless InterfaceControlled multimedia recording environment for lectures and 3D.Controller design for a helicopter modelCooperative Adaptive Cruise ControlCross Platform Component Object ModelCrusoe ProcessorCryogenic ProcessorCryptography and N/W securityCryptovirologyCSS and DeCSSCT scanningCyber terrorismDeploying a wireless sensor network on an active volcanoDigital jewelryData Mining for Condition Monitoring of Power System EquipmentData mining through Active LearningDynamic Car Parking Negotiation and Guidance Using An Agent-Based PlatformGSM Real Time Street Light Control SystemsData over Cable System (DOCSIS)Data Pre ProcessingData Security in Local Network using Distributed FirewallsData ware hosuing & miningDatagram Congestion Control Protocol (DCCP)Dataset Query algorithms in Streaming MiningDelay-Tolerant NetworksDense wavelength division multiplexingDesign and development of a programmable alarm systemDesign of a wireless sensor board for measuring air pollutionDesign of Amplifier for recording of Nerve SignalsDesign of an all Electric Steering WheelDesign of diamond-based Photonics devicesDesign of IC Amplifiers for touch SensorsDesign of Low Density Parity Check CodesDetermination of efficiency of the Permanent Magnet MotorsDeveloping a own server systemDevelopment and Control of Humanoid robotDevelopment of a Broadband Tunable Fiber LaserDevelopment of a New Sensor for Detecting Partial Discharge Induced PressureDevelopment of a wind-turbine simulatorDevelopment of new sensors for online monitoring of partial dischargesDigit recognition using neural networkDigital Audio BroadcastingDigital Audio Effects Control by AccelerometryDigital Camera Calibration and Inversion for Stereo iCinemaDigital Neurons for Digital BrainsDigital Signal Processing and their applicationsDigital silhouettesDigital theatre systemDirect to home television (DTH)Direct Torque and Flux Control of IPMSMDistance learning systemsDomain name servers [DNS]Driving Optical Network EvolutionDual Energy X-ray AbsorptiometryDynamic Cache Management TechniqueDynamic Memory Allocation(malloc, calloc, NEW etc)Dynamic resource allocation in Grid ComputingDynamic source routing protocolDynamic Virtual Private NetworkEarth Simulator- Fastest SupercomputerEffects of large scale integration of PV systems on the distribution networkEfficiency / Comparative study of routing schemes in event based systemsElectromagnetic Applications for Mobile and Satellite CommunicationsElectromagnetic launching systemElectromagnetic processor fabricationElectronic nose & its applicationElliptical Curve Cryptography(ECC)Embedded Configurable Operating systemEmbedded system in automobilesEmbedded systems and VLSI an architectural approach to reduce leakage energy in memoryEmbedded web server for remote accessEmbryonics approach towards integrated circuitsEmergency Health Care SystemEmerging trends in robotics using neural networksE-MINE: A novel web mining approachEncrypted Hard disksEncrypted Text chat Using BluetoothEncryption Decryption MethodsEnergy-efficiency and Layer Integration in Wireless NetworksEnterprise SecurityEqualization of room acoustics for audio reproductionEthernet Passive Optical NetworkE-Toll tax fixingEvolution Of Embedded SystemeXtensible Bindings Language (XBL )Electronic waste (e-waste)Embedded web server for industrial automationEyegaze systemFuel saver systemGoogle autonomous carFeatures of Qualcomm Snapdragon processorGuarding distribution automation system against cyber attacksFace detection technologyFacility Layout Design using Genetic AlgorithmFalls detection using accelerometry and barometric pressureFast Convergence Algorithms for Active Noise Controlling VehiclesFault Tolerance in Virtual Machine EnvironmentsFault tolerant Routing in Mobile Ad-Hoc NetworkFerroelectric RAMFine Grained DataBase SecurityFine-grained Access Control in DatabasesFingerprint recognition system by neural networksFinite Element Interface (FEI)Flexible CRT DisplaysFluorescent Multilayer Disc (FMD)Fluorescent Multilayer Optical Data StorageForecasting Wind PowerFractal image compressionFractal robotsFree Space Laser Communicationsfully digital class-D amplifiersFully Integrated Amp-Meter for Electrical SimulatorsFunctional Magnetic Resonance ImagingFuture of the internetFuture Programming Techniques and ConceptsFuzzified Computer-Automated Crane Control SystemFuzzy Logic Control for complex systemsGaming interfaces applied to videoconferencingGeneral Packet Radio Service (GPRS)Generic visual perception processorGeographic information systemGeometric Invariants in Biological MoleculesGIS tools for web applicationsGlobal positioning response systemGSM Digital Security Systems for PrinterVoice Operated Intelligent Fire Extinguisher VehicleGlobal Positioning SystemGlobal System for Mobile Communication (GSM)Google Android- Mobile OS from GoogleGrasshopper Operating SystemGroupware TechnologyGSM Security And EncryptionHandfree driving [auto]Hardware EDAC for Harsh EnvironmentsHardware implementation of background image modelingHAVI: Home Audio Video InteroperabilityHawk Eye – A Technology in sportsHigh Altitude Aeronautical PlatformsHigh Performance ClustersHigh Performance ComputingHigh Performance DSP ArchitecturesHigh Speed Circuits for optical InterconnectHigh Speed Data in Mobile NetworksHigh speed LANs or InternetHolographic Data StorageHolographic MemoryHolographic Versatile DiscHolt-Winters technique for Financial ForecastingHomeRF and Bluetooth: A wireless data communications revolutionHot Spot TechnologyHyper thread imaxHyper thread technologyHyper Transport TechnologyHow does a search engine work ??How does google search engine work ??How to create a website using wordpressHuman computer interaction & its futureDesign of a color Sensing System for Textile IndustriesGSM based Path Planning for Blind Person Using UltrasonicImage retrieval using compact binary signaturesVehicle Monitoring and Security SystemImbricate cryptographyImplementation of hamming codeIntroduction to microcontrollersIntroduction to AirfoilIntrusion detection and avoidance systemIC Amplifier Design for Touch SensorsImage transmission over WiMax SystemsImage WatermarkingImplantable on-chip Power SuppliesImproving TCP performance over mobile ad hoc networksIndustrial Applications using Neural NetworksInformation Extraction from structured & Semi-structured dataInformation Extraction modes & techniquesInfrared Remote ControlInnovative Application Development using J2EE ArchitectureIntegrated Circuit Design for Biomedical ApplicationsIntegrated Optical Chip DesignIntegrated Voice and Data transfer & handlingIntegrating Structural Design and Formal Methods in Real Time System DesignIntegrating Wind Power into the Electricity gridIntegration of Parallel Database in a Service Oriented ArchitectureIntegration of wind and solar energy in smart mini gridIntel centrino mobile technologyIntelligent calling bellIntelligent navigation systemIntelligent Patient Monitoring SystemIntelligent RAM : IRAMIntelligent Software AgentsInteractive Voice Response SystemInternet Access via Cable TV NetworkInternet architecture and routingInternet Protocol duplicate address detection and adaptationIntrusion Detection SystemInvestigation into solar thermal/coal driven power stationsInvestigation of the real-time implementation of learning controllersIP spoofingIP re-director featuresiOS 8 featuresIPODSIris ScanningiSCSI: The future of Network StorageISO Loop magnetic couplersJava Cryptography Architecture (JCA)Java Messaging Service (JMS)Enterprise Messaging Service (EMS)Advantages of EMS over JMSJava BeansJIRO Java-based technologyLaser Power SupplyJmeter toolGEMS tool for EMSLess characterization of ferromagnetic material for non-sinusoidal excitationLight emitting polymersLoad balancing and Fault tolerant serversLight Interception Image AnalysisLight TreeLightning Protection Using LFAMLiquid Crystal on Silicon Display (LCOS)Location estimation and trajectory prediction for PCS networksLong baseline motion estimationLotus Notes/DominoLow power filter design for mobile communicationLow Power UART Design for Serial Data CommunicationLow-Power Microelectronics for Biomedical ImplantsLow-Power Oscillator for ImplantsMagnetic Random Access MemoryManaging Data In Multimedia ConferencingMango- new mobile from MicrosoftMicro chip production using extreme uv lithographyMicrosoft NetMeetingMigration from GSM network to GPRSMining the Web: Searching, Integration and DiscoveryMobile Virtual Reality ServiceMobility Modeling and trajectory prediction for next generation PCS networksModeling of current spread through electrode geometries in implantable hearing deviceModeling of wind turbine system for an Interior Permanent magnet generatorMoletronics- an invisible technologyPower generation through Thermoelectric generatorsMulti Protocol Label SwitchingMulti user Scheduling for MIMO broadcastingMultiple clients communicationMultiple Domain OrientationMultisensor Fusion and IntegrationNeuro chipsParasitic computingPassword paradigmsPolymer memory a new way of using plastic as secondary storageProgrammable logic devices (PLD)Navigation of Mobile Wheeled RobotsNerve Signal Measurement Electronics for Biomedical ImplantsNetwork Attached Storage (NAS)Non Volatile Static RAMOptical coherence tomographyOptical to electrical converter for optical interconnectOptimization of Ad Hoc Wireless Sensor NetworksOptimization of Protocol Stack for wireless networksOracle RDBMSOutdoor High Voltage InsulatorsOvonic Unified MemoryPersonal Satellite assistant SystemsPH Control Technique using Fuzzy LogicPhone Busy IndicatorPivot Vector Space Approach in Audio-Video MixingPlastic chips & electronicsPluggable Authentication Modules (PAM)POF Tunable Fiber LaserPOP Plaster Of ParisPower Efficiency and Security in Smart HomesProactive Anomaly DetectionPrototype System Design for TelemedicinePublic Key Encryption and Digital SignatureQoS in Cellular Networks Based on MPTQoS in Networking using active NetworksQOS in software server FirewallsQuad-Core ProcessorsRadio Frequency Identification (RFID)Real time communication in wireless sensor networksReal Time Operating Systems on Embedded ICsReal Time Speech TranslationReal Time Systems with Linux/RTAIReliable and Fault Tolerant Routing on Mobile Ad Hoc NetworkRenovating the Address Resolution Protocol (ARP)Revolutions in the Operating System and ServersRobotic SurgeryRoom Equalization for Audio ReproductionRuby on Rails [RoR]Radio frequency identification technologyRapid prototypingSecured webportal for online shoppingSecuring underwater wireless communication networksSecurity analysis of micropayment systemSecurity aspects in mobile ad hoc network (manets)Security requirements in wireless sensor networksSemantic webSensitive skinSnake robot the future of agile motionSoftware defined radio(sdr)Spwm technique for multilevel inverterStorage area network(SAN)SwitchgrassSystem on chipSALT (Speech Application Language Tags)Sand Box TechnologySecurity of Open-Source SoftwareSecurity On Wireless LAN Adaptive cruise controlSecurity threats in the World Wide WebSensor fusion for video surveillanceSensors on 3D DigitizationSession Initiation Protocol (SIP)Shallow water Acoustic NetworksShort Message Service (SMS)Significance of real-time transport Protocol in VOIPSimulating Quantum CryptographySimulation of low-power converter for electromagnetic vibration driven generatorSingle photon emission computed tomographySmart camera for traffic surveillanceSmart Cameras in Embedded SystemsSmart FabricsSnickometer A toolSocket ProgrammingSoftware advances in wireless communication(Cognitive Radio, Dynamic spectrum Access etc. )Software Testing & Quality AssuranceSpace MouseSpace RoboticsSpectrum Sharing in Cognitive Radio NetworksSpeech Enhancement for Cochlear ImplantsSpeech Enhancement for Mobile ApplicationsSpeech transmission over WiMax systemsSpeed Detection of moving vehicle using speed camerasSPINS -Security Protocol For Sensor NetworkSplit Range SynchronizationStealth VirusSurface-conduction Electron-emitter Display (SED)Swarm intelligence & traffic SafetySynchronous Optical NetworkingSynthetic Aperture Radar SystemSystems Control for Tactical Missile GuidanceTesting methods (Stress, Black-Box, White-Box, Performance Testing etc )The Architecture of a Moletronics ComputerThe Tiger SHARC processorThermal infrared imaging technologyThought Translation Device (TTD)Time Shared O.S.Tracking and Positioning of Mobiles in TelecommunicationTrends in Compiler ConstructionThree-dimensional password for more secure authenticationUltrasonic motorWearable biosensorsWeb-miningTraffic Light Control SystemMulti-Channel Infra Red Remote ControlMagic lightsZigbee Based Wireless Sensor Network for Sewerage MonitoringWireless integrated network sensorsUbiquitous NetworkingUltra Low-Power Microphone Pre-AmplifierUltra Low-Power Radio Receiver for Biomedical ApplicationsUltrasonic detector for monitoring partial dischargeUltra-Wideband CommunicationUMA (Unlicensed Mobile Access )Vector – LDPC Codes for 3G Fading ChannelsVirtual SurgeryWideband Spectrum Sensing for Cognitive Radio SystemsWireless Computer Communications Using Sound WavesLink available for getting details about some topic. You can search internet for getting details about the remaining topics.Hope this helps you :)
-
What's your opinion on AirSwap (AST)?
What is Airswap?Why there was a need for an exchange like Airswap?Why we are calling it the next big cryptocurrency exchange?To begin...All You Need to Know About AIRSWAP, The Next Big Cryptocurrency Exchange[1]Let's first discuss the kind of exchange we have and what is missing in the current exchanges?Currently, most of the cryptocurrency exchanges are centralized ones like bittrex or poloniex.When you are using a centralized cryptocurrency exchange then you don't have full control either on your fund or on your private key.Since these centralized cryptocurrency exchanges save your key in a centralized server or database they have a close watch on all your crypto funds transfer.And none of us really want our crypto funds to be watched upon by any third party."Necessity is the Mother of Invention"Definitely, there was a need for de-centralized cryptocurrency exchange like AIRSWAP.To make things more clear let's dig the de-centralized exchange.[What is a de-centralized cryptocurrency exchange like Airswap?]A de-centralized cryptocurrency exchange is an exchange which has the architecture of the platform built in such a manner that no centralized server or bundle of servers have control over the entire platform.To understand it in simpler terms there is no need for third-party intervention.[What are the features of de-centralized cryptocurrency exchange like Airswap?]An exchange not controlled by the third party.An exchange that can't be shut down by any government.An exchange that doesn't faces failures like centralized server failures etc.An exchange that doesn't ask for KYC verification.An exchange that allows the cryptocurrency users to manage and control their funds with hundred percent privacy.[What are the major differences between centralized and de-centralized exchange?]PicsCredit:Masterthecrypto[What are benefits of de-centralized exchange like Airswap?]Identity theft will reduce to zero.Banking Cartels will not exist anymore.Innovation with no limits.Anyone can transfer wealth to anyone at any time and from any part of the world.Highly secure with zero probability of corruption.NO DOWNTIME.I hope my readers and my dear friends will have a clear idea about de-centralized cryptocurrency exchange.In case you have a doubt please do contact me or ask your query in the comment section.I am always there to help you to the best of my potentials.Almost I have written around 650 words but still, I haven't even started to talk about the topic 'airswap' which is the highlight of this blog post. - Google Search intention was to first clear the doubt if any exists between the centralized and de-centralized exchange for better understanding.Coming back to AIRSWAP...[What is Airswap?]Airswap is a de-centralized cryptocurrency exchange which uses SWAP protocol for exchanging ethereum token.Note: Swap protocol is peer-to-peer protocol.The best part of this trading platform is that the users will not have to pay any trading fee. Since there will not be any involvement of the third party to the exchange making it almost hack free.Airswap is a Hong Kong-based company, a joint venture with consensus, recently made headlines for partnering with Fortress hedge fund manager Michael Novogratz.From the research that I have done, I can definitely assure you that this exchange will be known for privacy, security, and transparency.Let's understand the key components of Airswap as it will definitely add value in case you are interested in making a career in blockchain or you are a cryptocurrency trader.Peer Protocol-I hope you are aware of peer-to-peer cryptocurrency trading.In case you aren't....No issues let me explain it to you.As the name suggests peer-to-peer transaction involves two individuals.For eg, you can consider ordering a pizza from pizza hut, chicken from KFC or even a cup of coffee from CCD as a peer-to-peer transaction.Whenever you are buying something from an e-commerce website remember it's a peer-to-peer transaction.There isn't the involvement of any third party.A peer-to-peer trading is private as it involves two parties who have a common interest.I will explain the same with an example of Maker denoted by "M" and Taker denoted by "T".Maker (M): The party that provides the order.Taker (T): The party that fills the order.The best part about peer-to-peer protocol is that anyone can take the role of maker and taker.I forget to mention that tokens are ERC20 complaints and any token that implements the standards can be very well traded using this protocol.Taker calls Maker for an order.Maker replies with an order.Taker calls contract to fill the order.Indexer Protocol-Indexer works on the concept of 'intent to trade'.The process is very simple.Here multiple makers can signal 'intent to trade' to indexer and when a maker ask for counterparties he/she may end up selecting one from multiple options.Once the Indexer has found the maker, the taker will be informed about it.Now Taker can negotiate with Maker and once ready for the agreement, the order is filled on smart contract.Makers call on the indexer.Takers also call on the indexer.Indexer calls on taker when a suitable or favorable match is found.Taker calls on Maker.Maker replies with an order.Takers call on contract to fill the order.Oracle Protocol-An oracle protocol is an off-chain service that provides pricing information to both makers and takers.When pricing an order prior to delivering it to a Taker, a Maker may ask the Oracle for what it considers a fair price suggestion.Likewise, having received an order, a Taker may ask the Oracle to check the price on the order to verify that it’s fair.The Oracle provides this pricing information to help both the Maker and the Taker make more educated pricing decisions and to smooth the process of trade negotiation.Takers call on the Makers.Makers call on the Oracle.Oracle provides a price to the Maker.Maker replies with an order only after analyzing the price.Taker calls the Contract for Order fulfillment.A similar interaction happens between Taker and Oracle when Taker receives an Order.Taker calls the Maker.Maker replies with an order.Taker call on Oracle.Oracle returns a price to the Taker.Taker calls the Contract only after the analyzing the price information.Ethereum Smart Contract-An ethereum smart contract is used to fill or cancel orders.Fill:- An atomic swap of tokens called by a Taker. The contract ensures that the message sender matches taker and ensures that the time indicated in expiration has not passed.To fill orders, peers must have already called approve on the specified tokens to allow the contract to withdraw at least the specified amounts.For token transfers, the contract calls transferFrom on the respective tokens.At the successful completion of this function, a Filled event is broadcast to the blockchain. The parameters,vr and sconstitute the maker signature.Cancel:- A cancellation of an order that has already been communicated to a Taker but not yet filled. Called by the Maker of the order.Marks the order as already having been filled on the contract so a subsequent attempt to fill the order will fail.At the successful completion of this function, a Canceled event is broadcast to the blockchain.Read More……Footnotes[1] All You Need to Know About AIRSWAP, The Next Big Cryptocurrency Exchange
-
What are non-Bitcoin/cryptocurrency applications of blockchain technology?
From Sneakers To Pharma to Gold: An Inside Look At The Evolution Of ChronicledAt some point, everyone who has bought collectible shoes or luxury clothing online has had the same thought. “Is this the real deal?”Good question.When a supply chain can easily stretch halfway around the globe, how do you know if those Yeezys on your feet are legit? When we started Chronicled, we weren’t thinking about Yeezys specifically, but we did have a goal in mind. That goal was to create a global protocol for blockchain that allows any object to be registered to, verified against, transferred on, or--in the case of the special class of objects that had a chip inside--to sign off on events, messages, accesses, financial transactions, etc.Not sure what that has to do with your sneakers? Let me explain.Chronicled was founded in 2014. We set out to explore non-financial use cases for blockchain. The average person has probably heard of blockchain in the context of Bitcoin, Ethereum, and other cryptocurrencies. And while blockchain does underpin those cryptocurrencies, the terms aren’t interchangeable. Blockchain isn’t Bitcoin, it’s the technology that makes those cryptocurrencies possible.And it turns out that blockchain has plenty of other uses. We founded Chronicled in order to investigate those non-financial uses by building the first IoT x Blockchain laboratory in the world. Much of our early work in that laboratory was focused on fine art, consumer products, and luxury goods. Why? Because those are industries with a high prevalence of counterfeit goods. Some industries, like pharma, lose billions of dollars each year due to supply diversion and counterfeit products.But how could we create a unique identity for a piece of fine art painted on a canvas? Or a bottle of rare wine? Or the designer purse you ordered online last week? The answer: tiny microchips, just like the chip inside your credit card.In 2015, Chronicled began working with companies to embed, or affix, cryptographic microchips in or on luxury and consumer products. We would then register those encrypted identities to a blockchain so they could be authenticated. Those microchips can’t be copied or corrupted. They have a unique identity that allows consumers to determine whether or not the 1947 Cheval Blanc on their dinner table is the real deal.Those were the first two primitive protocols we developed at Chronicle—Register and Verify. There was finally a way to register fine art, luxury goods, and consumer products with an unreproducible identity that could then be verified by the consumer. It’s a game-changing concept that is already creating a safer, more transparent buying process for consumers.But let’s keep moving. Fast forward to 2016 when we were hard at work on the newest uses for blockchain. Many of our clients were interested not only in using the blockchain to register and verify the identity of an object, but also in using the smart contract feature of blockchain to securely transfer custody and/or ownership. In parallel with our own move into smart supply chain, more enterprise players were beginning to work with blockchain technology as the vast possibilities became evident.Even JP Morgan had gotten in on the action with Quorum, their own enterprise ledger and smart contract platform. So, we went from registering and verifying products, to also transferring custody, ledgering data and events, and tracking provenance of an item over time using more powerful systems and smart contracts. In 2016, we began working on our next two protocol primitives, Transfer and Ledger, and our Smart Supply Chain platform was born.The Smart Supply Chain Initiative led us to some incredible projects in several different industries. For instance, we began work on the MediLedger project, a joint venture that set out to solve the problem of counterfeit drugs in the pharmaceutical supply chain. We’ve also worked on a responsible gold venture to track the provenance of the world’s gold supply, and with our partner Ambisafe we will tokenize physical gold by linking the physical gold bullion identities to digital, tradeable ERC20 tokens for the first time in human history. In the future, we can track many kinds of conflict minerals with this same blockchain approach.Notice that industries all across the spectrum are benefitting from blockchain. That’s not a coincidence. Moving forward, the trust, security, and data privacy that blockchain brings is going to change and improve nearly every industry.So, let’s flip ahead on the calendar and start looking at what the future holds. It’s 2018, and our sixth protocol primitive is in place—Value Transfer. Chronicled’s Blockchain x IoT API is not only powering unique product identities and supply chain tracking and provenance, but it can also enable machine payments and IoT economies.Picture this:A drone hitches a ride on an Uber and uses the charging port on top to refuel. Then it makes a micropayment for the ride and the charge before resuming its journey. If you think that sounds futuristic, then you’re going to be in for some surprises in the next few years. We’re talking about decentralized energy grids. Fully secure and connected smart cities. And eventually, a fully connected world running on the protocols that we’ve built.Blockchain technology is set to change everything. It’s time to start paying attention to the innovations that blockchain is creating, because the pace of disruption is only going to increase. The progress we’ve made at Chronicled in just three years has been astounding, and we’ve only just begun.
-
What is blockchain technology?
The 21st century is all about technology. With the increasing need for modernization in our day-to-day lives, people are open to accepting new technologies. From using a remote for controlling devices to using voice notes for giving commands; modern technology has made space in our regular lives. Technologies like augmented reality and IoT that have gained pace in the past decade and now there’s a new addition to the pack i.e. Blockchain Technology.Blockchain – The revolutionary technology impacting different industries miraculously was introduced in the markets with its very first modern application Bitcoin. Bitcoin is nothing but a form of digital currency (cryptocurrency) which can be used in the place of fiat money for trading. And the underlying technology behind the success of cryptocurrencies is termed as Blockchain.There’s a common misconception among people that Bitcoin and Blockchain are one and the same, however, that is not the case. Creating cryptocurrencies is one of the applications of Blockchain technology and other than Bitcoin, there are numerous applications that are being developed on the basis of the blockchain technology.What is a Blockchain?In the simplest terms, Blockchain can be described as a data structure that holds transactional records and while ensuring security, transparency, and decentralization. You can also think of it as a chain or records stored in the forms of blocks which are controlled by no single authority. A blockchain is a distributed ledger that is completely open to any and everyone on the network. Once an information is stored on a blockchain, it is extremely difficult to change or alter it.Each transaction on a blockchain is secured with a digital signature that proves its authenticity. Due to the use of encryption and digital signatures, the data stored on the blockchain is tamper-proof and cannot be changed.Blockchain technology allows all the network participants to signNow an agreement, commonly known as consensus. All the data stored on a blockchain is recorded digitally and has a common history which is available for all the network participants. This way, the chances of any fraudulent activity or duplication of transactions is eliminated without the need of a third-party.In order to understand blockchain better, consider an example where you are looking for an option to send some money to your friend who lives in a different location. A general option that you can normally use can be a bank or via a payment transfer application like PayPal or Paytm. This option involves third parties in order to process the transaction due to which an extra amount of your money is deducted as transferring fee. Moreover, in cases like these, you cannot ensure the security of your money as it is highly possible that a hacker might disrupt the network and steal your money. In both the cases, it is the customer who suffers. This is where Blockchain comes in.Instead of using a bank for transferring money, if we use a blockchain in such cases, the process becomes much easier and secure. There is no extra fee involved as the funds are directly processed by you thus, eliminating the need for a third party. Moreover, the blockchain database is decentralized and is not limited to any single location meaning that all the information and records kept on the blockchain are public and decentralized. Since the information is not stored in a single place, there’s no chance of corruption of the information by any hacker.How Does a Blockchain Work?Source: Fuat Şanlı (Dribbble)A blockchain is a chain of blocks that contain data or information. Despite being discovered earlier, the first successful and popular application of the Blockchain technology came into being in the year 2009 by Satoshi Nakamoto. He created the first digital cryptocurrency called Bitcoin through the use of Blockchain technology. Let’s understand how a blockchain actually works.Each block in a blockchain network stores some information along with the hash of its previous block. A hash is a unique mathematical code which belongs to a specific block. If the information inside the block is modified, the hash of the block will be subject to modification too. The connection of blocks through unique hash keys is what makes blockchain secure.While transactions take place on a blockchain, there are nodes on the network that validate these transactions. In Bitcoin blockchain, these nodes are called as miners and they use the concept of proof-of-work in order to process and validate transactions on the network. In order for a transaction to be valid, each block must refer to the hash of its preceding block. The transaction will take place only and only if the hash is correct. If a hacker tries to attack the network and change information of any specific block, the hash attached to the block will also get modified.The bsignNow will be detected as the modified hash will not match with the original one. This ensures that the blockchain is unalterable as if any change which is made to the chain of blocks will be reflected throughout the entire network and will be detected easily.In a nutshell, here’s how blockchain allows transactions to take place:A blockchain network makes use of public and private keys in order to form a digital signature ensuring security and consent.Once the authentication is ensured through these keys, the need for authorization arises.Blockchain allows participants of the network to perform mathematical verifications and signNow a consensus to agree on any particular value.While making a transfer, the sender uses their private key and announces the transaction information over the network. A block is created containing information such as digital signature, timestamp, and the receiver’s public key.This block of information is broadcasted through the network and the validation process starts.Miners all over the network start solving the mathematical puzzle related to the transaction in order to process it. Solving this puzzle requires the miners to invest their computing power.Upon solving the puzzle first, the miner receives rewards in the form of bitcoins. Such kind of problems is referred to as proof-of-work mathematical problems.Once the majority of nodes in the network come to a consensus and agree to a common solution, the block is time stamped and added to the existing blockchain. This block can contain anything from money to data to messages.After the new block is added to the chain, the existing copies of blockchain are updated for all the nodes on the network.Blockchain FeaturesThe following features make the revolutionary technology of blockchain stand out:DecentralisedBlockchains are decentralized in nature meaning that no single person or group holds the authority of the overall network. While everybody in the network has the copy of the distributed ledger with them, no one can modify it on his or her own. This unique feature of blockchain allows transparency and security while giving power to the users.Peer-to-Peer NetworkWith the use of Blockchain, the interaction between two parties through a peer-to-peer model is easily accomplished without the requirement of any third party. Blockchain uses P2P protocol which allows all the network participants to hold an identical copy of transactions, enabling approval through a machine consensus. For example, if you wish to make any transaction from one part of the world to another, you can do that with blockchain all by yourself within a few seconds. Moreover, any interruptions or extra charges will not be deducted in the transfer.ImmutableThe immutability property of a blockchain refers to the fact that any data once written on the blockchain cannot be changed. To understand immutability, consider sending email as an example. Once you send an email to a bunch of people, you cannot take it back. In order to find a way around, you’ll have to ask all the recipients to delete your email which is pretty tedious. This is how immutability works.Once the data has been processed, it cannot be altered or changed. In case of the blockchain, if you try to change the data of one block, you’ll have to change the entire blockchain following it as each block stores the hash of its preceding block. Change in one hash will lead to change in all the following hashes. It is extremely complicated for someone to change all the hashes as it requires a lot of computational power to do so. Hence, the data stored in a blockchain is non-susceptible to alterations or hacker attacks due to immutability.Tamper-ProofWith the property of immutability embedded in blockchains, it becomes easier to detect tampering of any data. Blockchains are considered tamper-proof as any change in even one single block can be detected and addressed smoothly. There are two key ways of detecting tampering namely, hashes and blocks.As described earlier, each hash function associated with a block is unique. You can consider it like a fingerprint of a block. Any change in the data will lead to a change in the hash function. Since the hash function of one block is linked to next block, in order for a hacker to make any changes, he/she will have to change hashes of all the blocks after that block which is quite difficult to do.Types of BlockchainsThough Blockchain has evolved to many levels since inception, there are two broad categories in which blockchains can be classified majorly i.e. Public and Private blockchains.Before heading towards the difference between these two, let’s keep a check on the similarities that both public and private blockchain have:Both Public and Private blockchain have peer-to-peer decentralized networks.All the participants of the network maintain the copy of the shared ledger with them.The network maintains copies of the ledger and synchronizes the latest update with the help of consensus.The rules for immutability and safety of the ledger are decided and applied on the network so as to avoid malicious attacks.Now that we know the similar elements of both these blockchains, let’s learn about each of them in detail and the differences between them.Public Blockchain – As the name suggests, a public blockchain is a permissionless ledger and can be accessed by any and everyone. Anyone with the access to the internet is eligible to download and access it. Moreover, one can also check the overall history of the blockchain along with making any transactions through it. Public blockchains usually reward their network participants for performing the mining process and maintaining the immutability of the ledger. An example of the public blockchain is the Bitcoin Blockchain.Public blockchains allow the communities worldwide to exchange information openly and securely. However, an obvious disadvantage of this type of blockchain is that it can be compromised if the rules around it are not executed strictly. Moreover, the rules decided and applied initially have very little scope of modification in the later stages.Private Blockchain – Contrary to the public blockchain, private blockchains are the ones which are shared only among the trusted participants. The overall control of the network is in the hands of the owners. Moreover, the rules of a private blockchain can be changed according to different levels of permissions, exposure, number of members, authorization etc.Private blockchains can run independently or can be integrated with other blockchains too. These are usually used by enterprises and organizations. Therefore, the level of trust required amongst the participants is higher in private blockchains.Popular Applications of Blockchain TechnologySource: Sumeet – EvontechThough Bitcoins and cryptocurrencies are the first popular application of Blockchain technology, they are not the only ones. The nature of Blockchain technology has led businesses, industries, and entrepreneurs from all around the world to explore the technology’s potential and make revolutionary changes in different sectors.While the basic idea of trustworthy records and giving the power in the hands of users has enormous potential, it sure has raised a lot of hype in the markets too. The magic of this technology sure has the power to transform industries given the usage is planned and executable in actual senses. Let’s separate the wheat from the chaff and find out how Blockchain can be useful in actual implementation.Smart contractsDifferent businesses deal with each other in order to exchange services or products. All the give and take terms and conditions are signed by the involved parties in the form of agreements or contracts. However, these paper-based contracts are prone to errors and frauds which challenges the trust factor between both the parties and raises risks. Blockchain brings forward an amazing solution to this problem through Smart Contracts.Smart contracts perform similar functions as paper-based agreements. The differentiating factor about smart contracts is that these are digital as well as self-executable in nature. Self-executable meaning that when certain conditions in the code of these contracts are met, they are automatically deployed. Ethereum, an open source blockchain platform has introduced smart contracts in the Blockchain ecosystem. Smart contracts can be used for different situations or industries such as financial agreements, health insurances, real estate property documents, crowdfunding etc.For example, Blockchain smart contracts can be used in healthcare to manage drug supply.Once the name and quantity of a drug is shipped from a manufacturing company to be delivered ahead to the pharmacist, a smart contract with all the valid data like the information of the drug, the quantity of supply etc. can be created. This smart contract will be responsible for managing the entries throughout the entire supply chain between different intermediaries. Since the smart contract works on certain defined conditions, no one can alter them or make any changes in the contract thus, ensuring trust and authenticity of the drugs.Government ElectionsNo matter how secure government elections are made, the chances of frauds through anti-social elements always persists. The current voting system relies on manual processing and trust. Even if security bsignNowes and frauds are eliminated, the chances of manual errors cannot be ignored. In such cases, the best solution is to automate the overall process with the help of smart contracts.Blockchain smart contracts provide a modern system through which these common issues can be easily eliminated. Entries in the smart contracts will allow transparency and security while maintaining the privacy of the voters thus, enabling fair elections.Identity managementThe world is getting more digitized with every passing day. Consider financial transactions happening online for instance, you can easily login with your credentials and security pin in order to access your funds. However, in this case, no one can ensure the identity of the person taking out the money. If your username and password are hacked by someone, there’s no way to secure your money.The need of the hour is to have a system that manages individual identification on the web. The distributed ledger technology used in blockchains offers you advanced methods of public-private encryption using which, you can prove your identity and digitize your documents. This unique secure identity can work as a saviour for you while conducting any financial transactions or any online interactions on a shared economy. Moreover, the gap between different government bodies and private organizations can be filled through a universal online identity solution that blockchain can provide.Intellectual Property ProtectionDigital content or information can easily be reproduced and distributed with the aid of the internet. Due to this, people from all around the world hold the power to copy, replicate and use it without giving credits to the actual producer of the content. There are copyright laws to protect such issues but in the current scenario, these laws aren’t appropriately defined according to common global standards. Meaning that any law which is valid in the US might not stand true in Australia.Even if there’s any copyright applied to any intellectual property, people easily lose control over their data and suffer on financial terms. With the aid of Blockchain technology, all the copyrights can be stored in the form of smart contracts which will enable automation in businesses along with the increase in online sale thus, eliminating the redistribution risk.Blockchain for IP registry will help the authors, owners or users to get clarity of copyright. Once they register their work online, they’ll own the evidence which will be tamper-proof. As blockchain is immutable in nature, any entry once stored on the Blockchain cannot be changed or modified. The owner of the work will have the overall authority over the ownership as well as the distribution of the content.ConclusionOther than these few examples, the revolutionary technology of Blockchain holds a high potential of applications in many different industries and sectors. While some industries have already started adopting blockchain in their businesses, many are still exploring the best possible ways to start with.Blockchain is a new name in the world of technologies but it is definitely the one to last. Even in the early stages, the technology has gained huge popularity starting with their very first application of cryptocurrencies. More areas of applications are being discovered and tested with each passing day. Once the technology is adopted and accepted on a global level, it’ll transform the way we live today.
Trusted esignature solution— what our customers are saying
be ready to get more
Get legally-binding signatures now!
Related searches to Help Me With Use eSignature in Oracle
Frequently asked questions
How do i add an electronic signature to a word document?
When a client enters information (such as a password) into the online form on , the information is encrypted so the client cannot see it. An authorized representative for the client, called a "Doe Representative," must enter the information into the "Signature" field to complete the signature.
How to get electronic signature capability?
If you are the owner of the product, please contact us to discuss your request. We are happy to help. We may need to verify that you own your product by verifying you own a product that has this capability. For more information on what to do to get eSignature capability please refer to our eSignature FAQ.
Can you send a digital product for the purpose of making money? For the purpose of making money?
No. This is a scam!
What happens if someone orders a digital product for the purpose of making money and then does not receive it?
We have zero control over this. The buyer pays and the item is never shipped to them. We do not want to be responsible for this. When this happens, and they have not claimed their item yet, please email us at support@ to report this.
Are you affiliated with any other companies?
No. We do not want to be affiliated with any other companies.
Are there any other payment options like VISA, MasterCard or Paypal?
The Viber Pay Card is not a payment option as of now. Our PayPal payments feature will be launched later in 2018. Viber Pay Card is only an option if you are a buyer. When paying with PayPal, you are not buying from us, you can't cancel or cancel.
Is it possible to pay with Viber Pay Card online?
Viber Pay Card is an available payment option for online purchases and transactions only.
Does Viber Pay Card have an expiry date?
No. Viber Pay Cards have a validity for two years from the date of issue. You will receive a confirmation e...
How to electronic signature kindle fire?
[24/12/2014, 9:56:55 PM] Alex Lifschitz: The only way to do it is to go in to the settings and click 'signature' [24/12/2014, 9:56:57 PM] Remy: Okay I've got the basics [24/12/2014, 9:57:04 PM] Remy: I'm good I'll see you in a bit [24/12/2014, 9:57:08 PM] Alex Lifschitz: I'd set your email to your gmail [24/12/2014, 9:57:10 PM] Alex Lifschitz: And then you can add to that list of addresses from the previous step. [24/12/2014, 9:57:16 PM] Alex Lifschitz: Like the second one. [24/12/2014, 9:57:24 PM] Remy: Okay I've got the basics [24/12/2014, 9:57:31 PM] drinternetphd: oh wow so that means I need to get my shit in order and get to the place I'm going to be for like 5 days [24/12/2014, 9:57:32 PM] drinternetphd: yeah that [24/12/2014, 9:57:47 PM] Remy: Also Alex I'm sorry for being like the first person to ask but can I be added to the list of folks on Skype or whatever you use to add people on Skype? It would be really nice to make sure I'm on the list to see [24/12/2014, 9:58:13 PM] Remy: I don't really do Skype [24/12/2014, 9:58:16 PM] drinternetphd: I need to set up some accounts and make sure they work [24/12/2014, 9:58:25 PM] drinternetphd: like i'm doing a thing with [24/12/2014, 9:58:31 PM] Remy: I can add you to my Skype contacts list I guess [25/12/2014, 11:14:07 AM] Ian Cheong: So I just saw the ad for PSN for $10. [25/12/2014, 11:15:00 AM] Ian Cheong: If you go to PSN and search for 'Dragon Age Inquisition', there's a video game from Bioware called Inquisition. [25...
Get more for Help Me With Use eSignature in Oracle
Find out other Help Me With Use eSignature in Oracle
- Pagella scolastica pdf form
- Api 653 study materials form
- Recomputation edd form
- Fmls residential detached gamls single family dual entry form
- Exponents practice form
- Imm5533e form
- Income form
- Sarasota county jail commissary form
- Indiana ifta online form
- Cuexamwindow form
- Pica questionnaire form
- Generic checklist form
- Usav scoresheet pdf form
- Critical incident report idaho department of health and welfare form
- Nsd admission form
- Ldss 4530 form
- Nys dtf 716 paper application form
- Aco intake form
- Pack 320 pinewood derby car inspection form cub scout
- Training request form template