Template Library
Create reusable templates with predefined signature fields and certificate requirements to accelerate consistent PKI-enabled document distribution across teams and departments.
Using the signNow PKI technology adds cryptographic signer identity, tamper-evident seals, and certificate-based validation to electronic transactions, improving legal defensibility and auditability without replacing standard eSignature workflows.

IT Administrators configure PKI integrations, manage certificate authorities, and maintain revocation and OCSP/CRL checks. They also set system-wide policies, automate certificate provisioning where possible, and troubleshoot interoperability issues between signNow and enterprise identity services.
Compliance Officers define acceptable identity proofing levels, map PKI usage to regulatory requirements like ESIGN and UETA, and retain audit records. They review certificate trust policies and retention settings to ensure legal defensibility of signed documents and evidence.
Typical adopters include regulated teams and organizations that need cryptographic identity and strong audit evidence for agreements.
These users prioritize verifiable identity, tamper detection, and a clear audit trail over minimal friction, and they often combine PKI with existing signNow features.
Create reusable templates with predefined signature fields and certificate requirements to accelerate consistent PKI-enabled document distribution across teams and departments.
Assign roles and permissions to control who can send documents, manage certificate mappings, or view sensitive audit logs within the signNow account.
Distribute identical, certificate-required documents to multiple recipients while preserving individual certificate bindings and tracking per-recipient audit entries.
Use signNow APIs to automate certificate checks, initiate signing sessions that require PKI credentials, and integrate events with enterprise systems.
Apply conditional fields or routing based on certificate attributes or verification outcomes to enforce downstream approvals or escalations.
Leverage encrypted cloud storage with controlled retention for PKI-signed documents and associated audit artifacts to support audits.
Supports integration with enterprise and third-party certificate authorities to accept X.509 certificates for signer authentication and to bind certificates to signature events within documents.
Performs OCSP or CRL checks during signature validation so that revoked or suspended certificates are detected and reflected in the signing outcome and audit record.
Applies cryptographic hashing and sealed signatures that show whether document content has been altered after signing, preserving integrity for legal and compliance review.
Generates timestamped logs capturing certificate details, validation results, IP addresses, and signing actions to support investigations and regulatory reporting.

| Workflow Setting Name and Description Header | Default configuration or expected values |
|---|---|
| Integration with external Certificate Authorities | OCSP endpoint configured |
| Signer certificate provisioning method | Manual or automated issuance |
| Revocation checking frequency and method | OCSP preferred, periodic CRL fallback |
| Audit logging verbosity level | Full verification details recorded |
| Document retention and archival policy | Immutable storage with retention period |
Confirm supported platforms and client prerequisites before deploying certificate-based signing to avoid compatibility issues.
Ensure end-user devices can securely store and present private keys (hardware tokens or OS key stores where possible), verify that mobile clients support the required certificate formats, and confirm that the enterprise CA provides accessible OCSP or CRL endpoints for revocation checks.
A regional clinic uses certificate-backed signatures for clinician credential attestations to ensure identity and consent integrity.
Resulting in auditable medical approvals that align with HIPAA documentation and internal compliance reviews.
A regional bank requires PKI-based signatures for vendor agreements to enforce non-repudiation and stronger identity verification.
Leading to clearer contractual evidence and streamlined vendor audits during regulatory examinations.
| Feature or Criteria Name for Comparison | signNow (Recommended) | Adobe Sign | DocuSign |
|---|---|---|---|
| PKI (X.509) support | |||
| OCSP/CRL revocation checks | |||
| Qualified electronic signature (eIDAS) | Limited | Available via provider | Available via provider |
| Audit trail detail level | High | High | High |
| Plan / Vendor Column Names | signNow (Featured) | DocuSign Business | Adobe Sign Business | HelloSign Pro | PandaDoc Business |
|---|---|---|---|---|---|
| Starting price per user (monthly) | From $8/user/month | From $10/user/month | From $9.99/user/month | From $15/user/month | From $19/user/month |
| Advanced authentication included | Included in select plans | Add-on or higher tier | Included in business tiers | Included in pro | Add-on available |
| API access availability | API access per plan | API available | API available | API available | API available |
| Document retention and archival | Configurable retention | Configurable retention | Configurable retention | Limited retention | Configurable retention |
| HIPAA-compliant options | Available with BAA | Available with BAA | Available with BAA | Available via agreement | Available via agreement |
Digital signatures are often used in highly regulated industries and regions to ensure that an authorized sender has signed a document and it was not modified in transit. A digital signature is generated using a trusted digital ID, aka a digital certificate or public key certificate. An accredited Certificate Authority (CA) issues a digital certificate after validating the requestor's identity.
Digital signatures use the public-key cryptography method to generate a pair of private and public keys, included in a digital certificate. When a signer adds their digital signature using a private key, the digital certificate is also cryptographically bound to a document. During the verification process, the linked public key decrypts a signature, ensuring its authenticity and validity.
Public Key Infrastructure is a security technology that enables digital signature processes. PKI consists of the roles, policies, procedures, and systems needed to create digital signatures, administer digital certificates, and manage public keys. PKI facilitates the trusted electronic identities for individuals or institutions with digital certificates and a Certificate Authority.
Upload a document to your airSlate SignNow account and open it in the editor. Drag and drop fillable fields and assign roles.
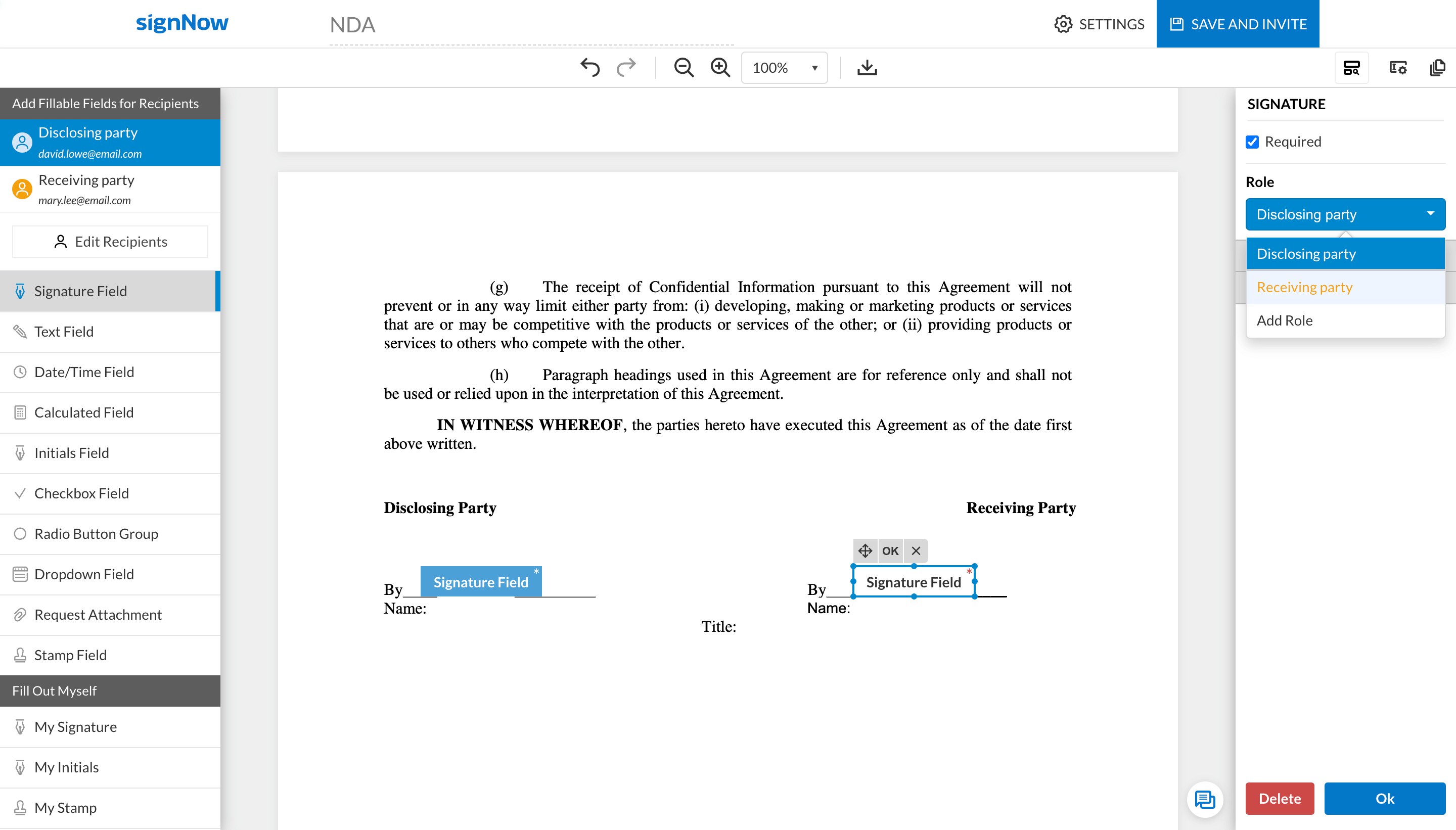
Click SAVE AND INVITE once your document is ready for sending.
Add recipient emails, set the signing order, and check the box Send using GlobalSign PKI signature.
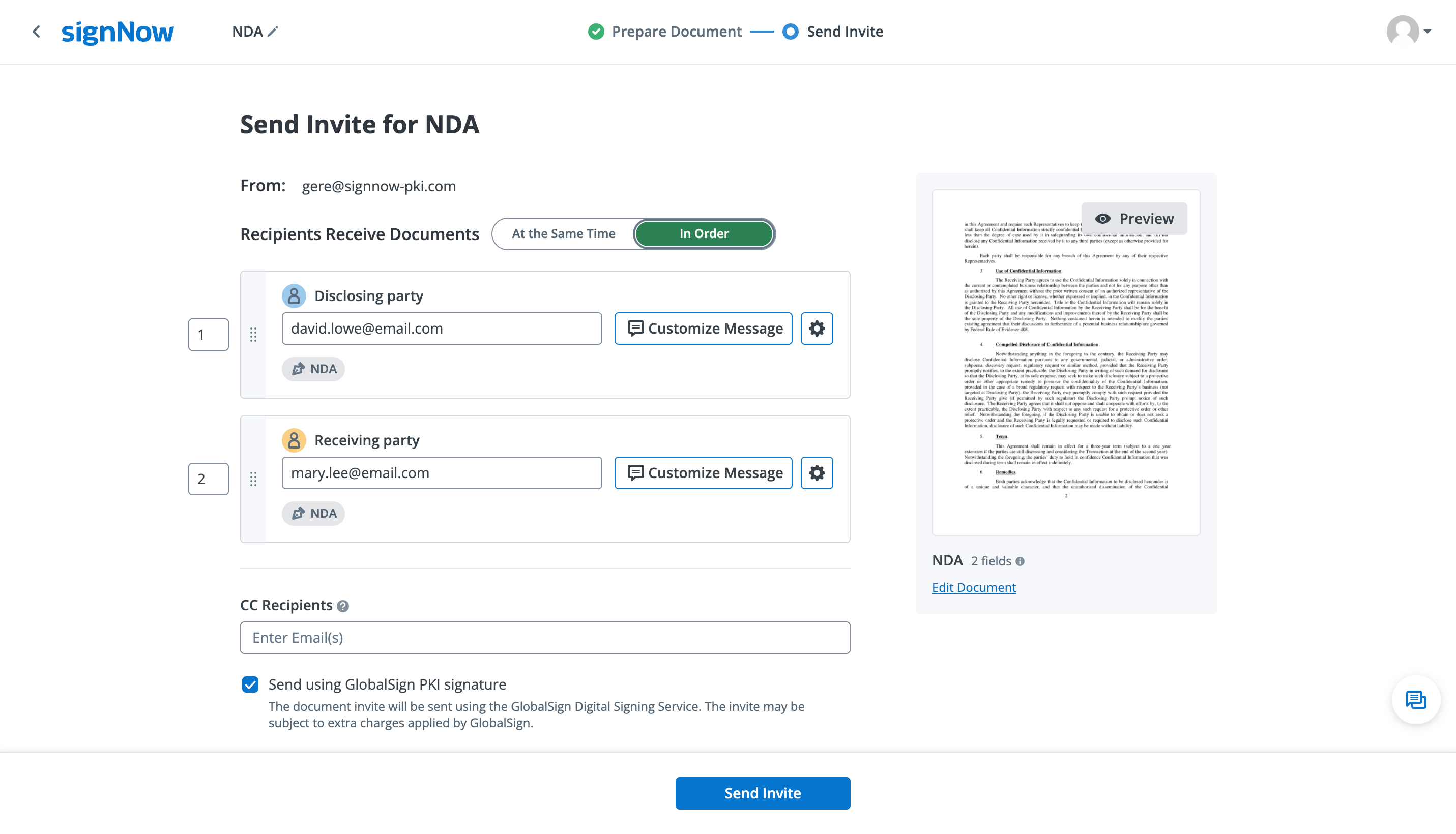
Note: only eligible organizations can send documents using the PKI technology. Contact us for details.
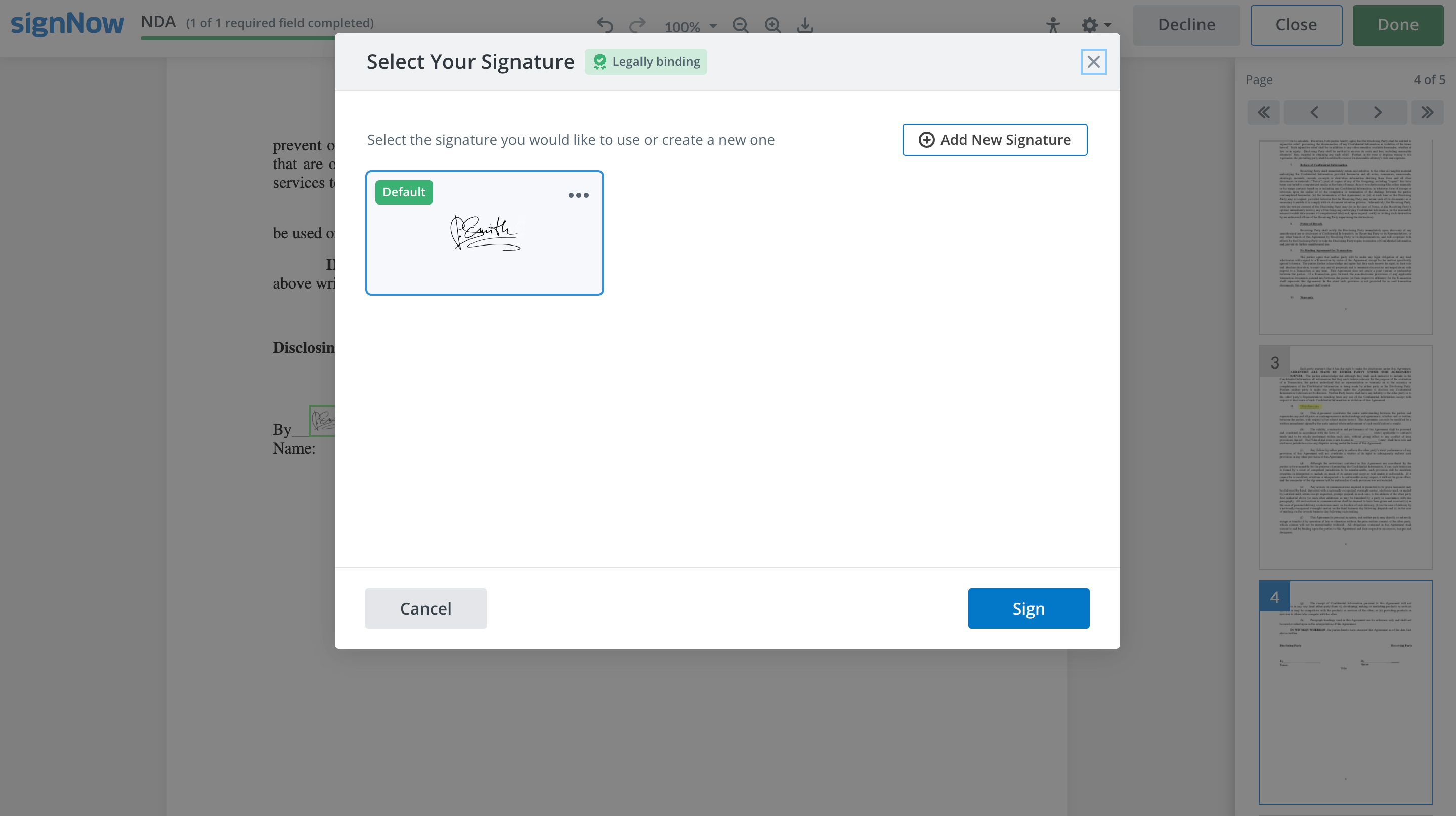
Once you receive a signature request, click to open a document and add your digital signature in seconds. You can draw, type, or upload an image of your signature.
Once every signer has signed your document, you can download it and view the digital certificate. To open a digital certificate, open your signed document in Adobe Acrobat Reader®. Click on the digital signature and select Signature Properties > Show Signer’s Certificate.





