Signature électronique Par SMS
Faites avancer votre entreprise avec la solution de signature électronique airSlate SignNow
Ajoutez votre signature juridiquement contraignante
Créez votre signature en quelques secondes sur n'importe quel ordinateur de bureau ou appareil mobile, même hors ligne. Tapez, dessinez ou téléchargez une image de votre signature.
Intégrez via l'API
Offrez une expérience de signature électronique fluide depuis n'importe quel site web, CRM ou application personnalisée — partout et à tout moment.
Envoyez des documents conditionnels
Organisez plusieurs documents en groupes et envoyez-les automatiquement aux destinataires selon un ordre basé sur les rôles.
Partagez des documents via un lien d'invitation
Collectez des signatures plus rapidement en partageant vos documents avec plusieurs destinataires via un lien — pas besoin d'ajouter les adresses e-mail des destinataires.
Gagnez du temps avec des modèles réutilisables
Créez un nombre illimité de modèles pour vos documents les plus utilisés. Facilitez leur remplissage en ajoutant des champs personnalisables.
Améliorez la collaboration d'équipe
Créez des équipes dans airSlate SignNow pour collaborer en toute sécurité sur des documents et des modèles. Envoyez la version approuvée à chaque signataire.
Découvrez les signatures électroniques airSlate SignNow en action
Solutions airSlate SignNow pour une meilleure efficacité
Gardez les contrats protégés
Améliorez la sécurité de vos documents et protégez vos contrats contre tout accès non autorisé grâce à l'authentification à deux facteurs. Demandez à vos destinataires de prouver leur identité avant d'ouvrir un contrat pour e sign and use ip authentication.
Restez mobile lors de la signature électronique
Installez l'application airSlate SignNow sur votre appareil iOS ou Android et concluez des accords de n'importe où, 24h/24 et 7j/7. Travaillez avec des formulaires et des contrats même hors ligne et e sign and use ip authentication plus tard lorsque votre connexion Internet est rétablie.
Intégrez les signatures électroniques dans vos applications métier
Intégrez airSlate SignNow dans vos applications métier pour e sign and use ip authentication rapidement sans changer de fenêtres ou d'onglets. Profitez des intégrations airSlate SignNow pour gagner du temps et de l'effort lors de la signature électronique de formulaires en quelques clics.
Générez des formulaires remplissables avec des champs intelligents
Mettez à jour n'importe quel document avec des champs remplissables, rendez-les obligatoires ou facultatifs, ou ajoutez des conditions pour leur apparition. Assurez-vous que les signataires remplissent correctement votre formulaire en attribuant des rôles aux champs.
Concluez des accords et soyez payé rapidement
Collectez des documents auprès de clients et partenaires en quelques minutes au lieu de semaines. Demandez à vos signataires de e sign and use ip authentication et ajoutez un champ de demande de paiement à votre exemple pour collecter automatiquement les paiements lors de la signature du contrat.
Collecter les signatures
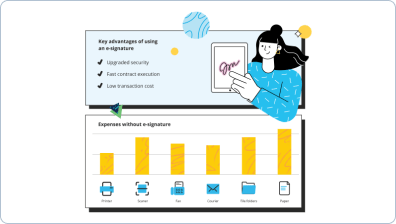
24x
plus rapide
Réduire les coûts de
$30
par document
Économisez jusqu'à
40h
par employé / mois
Les avis de nos utilisateurs parlent d'eux-mêmes






soyez prêt à en obtenir plus
Pourquoi choisir airSlate SignNow
-
Essai gratuit de 7 jours. Choisissez le forfait dont vous avez besoin et essayez-le sans risque.
-
Tarification honnête pour des forfaits complets. airSlate SignNow propose des abonnements sans frais supplémentaires ni frais cachés lors du renouvellement.
-
Sécurité de niveau entreprise. airSlate SignNow vous aide à respecter les normes de sécurité mondiales.

Votre guide étape par étape — e sign and use ip authentication
eSign and use IP authentication. Get maximum benefit from the most respected and safe eSignature platform. Simplify your electronic deals using airSlate SignNow. Optimize workflows for everything from basic employee documents to complex agreements and sales forms.
Know how to eSign and use IP authentication:
- Upload a few pages from your computer or cloud storing.
- Drag & drop custom fillable fields (signature, text, date/time).
- Alter the fields sizing, by tapping it and choosing Adjust Size.
- Place checkboxes and dropdowns, and radio button groups.
- Edit signers and create the request for attachments.
- eSign and use IP authentication.
- Add the formula where you require the field to generate.
- Apply remarks and annotations for the signers anywhere on the page.
- Approve all adjustments by clicking on DONE.
Link up people from outside and inside your organization to electronically access important signNowwork and eSign and use IP authentication anytime and on any system utilizing airSlate SignNow. You may monitor every activity performed to your samples, get alerts an audit report. Stay focused on your business and consumer relationships while with the knowledge that your data is accurate and protected.
Comment ça marche
Créez des eSignatures juridiquement contraignantes
Éditez et signez-le depuis n'importe où
Éditez et eSign à distance
Fonctionnalités airSlate SignNow appréciées par les utilisateurs
Découvrez des résultats exceptionnels Signature électronique par SMS
soyez prêt à en obtenir plus
Obtenez des signatures juridiquement contraignantes dès maintenant !
FAQ
-
What is electronic signature authentication?
11.3 (US federal regulations) (5) Digital signature means an electronic signature based upon cryptographic methods of originator authentication, computed by using a set of rules and a set of parameters such that the identity of the signer and the integrity of the data can be verified. -
What is considered an electronic signature?
A qualified electronic signature is not defined in the United States. ... Under UETA, the term means "an electronic sound, symbol, or process, attached to or logically associated with a record and executed or adopted by a person with the intent to sign the record." -
Can I type an electronic signature?
An electronic signature can be anything that constitutes an online mark, like a symbol or an image of your signature. Electronic signatures don't have the security of a digital signature, as they don't create a hash of a document, or tie the signature to the document itself. -
What counts as electronic signature?
A qualified electronic signature is not defined in the United States. ... Under UETA, the term means "an electronic sound, symbol, or process, attached to or logically associated with a record and executed or adopted by a person with the intent to sign the record." -
Do electronic signatures hold up in court?
Otherwise, it is widely recognized that electronic signatures do hold up in court. -
What is electronic signature and digital signature?
Digital Signatures. A digital signature is a type of electronic signature that offers more security than a traditional electronic signature. When you sign a document with a digital signature, the signature links a \u201cfingerprint\u201d of the document to your identity. -
What is the difference between electronic signature and digital signature?
Difference Between Digital Signature and Electronic Signature. ... The main difference between the two is that digital signature is mainly used to secure documents and is authorized by certification authorities while electronic signature is often associated with a contract where the signer has got the intention to do so. -
What qualifies as an electronic signature?
A qualified electronic signature is not defined in the United States. ... Under UETA, the term means "an electronic sound, symbol, or process, attached to or logically associated with a record and executed or adopted by a person with the intent to sign the record." -
Is airSlate SignNow a digital signature?
Digital signatures, like handwritten signatures, are unique to each signer. Digital signature solution providers, such as airSlate SignNow, follow a specific protocol, called PKI. ... The resulting encrypted data is the digital signature. The signature is also marked with the time that the document was signed. -
How do you validate an electronic signature?
Set your signature verification preferences. ... Open the PDF containing the signature, then click the signature. ... For more information about the Signature and Timestamp, click Signature Properties. Review the Validity Summary in the Signature Properties dialog box.
Ce que disent les utilisateurs actifs — e sign and use ip authentication
Questions fréquemment posées
Comment ajouter une signature électronique à un document Word ?
Vous pouvez ajouter des signatures électroniques à un document Word en utilisant l'outil Dessin. Selon la loi américaine, chaque signature électronique que vous ajoutez dans Word est reconnue comme une signature électronique officielle. Cependant, cette méthode ne sera pas adaptée à de nombreux secteurs qui incluent des données sensibles ou des flux de signature complexes. Pour sécuriser vos documents et éviter d'éventuels problèmes, envisagez de télécharger un document Word pour la signature sur airSlate SignNow et utilisez ses outils pour une expérience de signature beaucoup plus sûre et fiable.
Quelle est la différence entre un tampon de signature et une signature électronique ?
La loi ESIGN ne donne pas une réponse claire à ce qu'est la différence entre un tampon électronique et une signature électronique, cependant, la caractéristique la plus notable est que les tampons sont plus populaires parmi les entités légales et les sociétés. Il existe une opinion répandue selon laquelle les tampons sont plus fiables. Cependant, selon la loi ESIGN, les exigences pour une signature électronique et un tampon électronique sont presque les mêmes. Contrairement aux signatures numériques, qui sont basées sur des clés privées et vérifiées. Le principal problème avec les signatures numériques est qu'elles nécessitent plus d'énergie pour être créées et peuvent être considérées comme plus compliquées à utiliser.
Comment signer des fichiers PDF en ligne ?
La plupart des services web qui permettent de créer des signatures électroniques ont des limites quotidiennes ou mensuelles, ce qui diminue considérablement votre efficacité. airSlate SignNow vous donne la possibilité de signer autant de fichiers en ligne que vous le souhaitez sans limitations. Il suffit d'importer vos PDF, de placer votre(s) signature(s) électronique(s), et de télécharger ou d'envoyer des échantillons. L'interface conviviale d'airSlate SignNow rend la signature électronique rapide et facile. Pas besoin de suivre de longues tutoriels pour comprendre comment cela fonctionne.
Obtenez plus pour e sign and use ip authentication
- Signature électronique pour la gestion des leads dans les services financiers
- Signature électronique pour la gestion des leads pour le gouvernement
- Signature électronique pour la gestion des leads dans le secteur de la santé
- Signature électronique pour la gestion des leads dans l'enseignement supérieur
- Signature électronique pour la gestion des leads dans l'industrie de l'assurance
- Signature électronique pour la gestion des leads pour les services juridiques
- Signature électronique pour la gestion des leads dans les sciences de la vie
- Signature électronique pour la gestion des leads pour les prêts hypothécaires
Tout savoir sur la signature électronique
Un contrat doit-il être signé par les deux parties ?
Apprenez la législation sur la signature de contrats. Découvrez ce qui rend le document juridiquement contraignant.
Quelle est la différence entre un utilisateur et un expéditeur dans airSlate SignNow?
Apprenez différentes façons d'envoyer des documents dans airSlate SignNow, d'inviter plusieurs signataires et de suivre le statut des documents.

Affaires à distance : Quelle est la façon la plus simple pour vos clients de signer des documents en ligne ?
Apprenez comment faciliter la signature électronique de documents en ligne pour vos clients. Profitez de la solution de signature électronique la plus facile à utiliser dans l'industrie.
Découvrez d'autres e sign and use ip authentication
- Découvrez la puissance d'une signature virtuelle en ...
- Application de signature numérique iPad sans effort ...
- Créez votre créateur de signature unique pour PDF ...
- Accédez à votre connexion de compte de signature ...
- Signez des documents PDF en ligne dans Chrome sans ...
- Numérisez ma signature facilement avec airSlate ...
- Découvrez notre visionneuse PDF gratuite avec ...
- Découvrez le meilleur outil d'analyse de signature en ...
- Découvrez le logiciel de signature électronique ...
- Rationalisez votre flux de travail avec notre ...
- Découvrez le meilleur outil de signature de document ...
- Téléchargez un signataire PDF en masse gratuit pour ...
- Rationalisez votre flux de travail avec notre outil de ...
- Découvrez une inscription au portail resman sans ...
- Accédez facilement au téléchargement du fichier ...
- Découvrez les meilleurs outils de signature numérique ...
- Découvrez le meilleur lecteur PDF pour plusieurs ...
- Découvrez le meilleur outil de signature PDF gratuit ...
- Découvrez des solutions de signature électronique ...
- Signez et remplissez en ligne votre document PDF ...
être prêt à en obtenir plus













































