Protection De La Libération Du Lien. Utilisez Des Outils De Signature électronique Qui Fonctionnent Où Vous êtes.
Obtenez les fonctionnalités robustes de signature électronique dont vous avez besoin avec la solution en laquelle vous avez confiance
Choisissez le service professionnel adapté aux pros
Configurez rapidement l'API de signature électronique
Travaillez mieux ensemble
Protégez la libération du lien en quelques minutes
Réduisez le délai de clôture
Gardez les informations importantes en sécurité
Découvrez les signatures électroniques airSlate SignNow en action
Solutions airSlate SignNow pour une meilleure efficacité
Les avis de nos utilisateurs parlent d'eux-mêmes






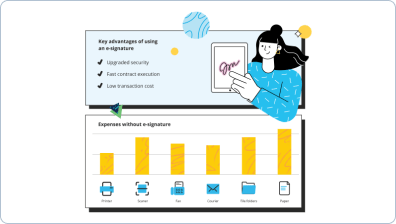
Pourquoi choisir airSlate SignNow
-
Essai gratuit de 7 jours. Choisissez le forfait dont vous avez besoin et essayez-le sans risque.
-
Tarification honnête pour des forfaits complets. airSlate SignNow propose des abonnements sans frais supplémentaires ni frais cachés lors du renouvellement.
-
Sécurité de niveau entreprise. airSlate SignNow vous aide à respecter les normes de sécurité mondiales.

Votre guide étape par étape — protect link release
Protection de la libération du lien. Obtenez la valeur maximale du système de signature électronique le plus fiable et sécurisé. Améliorez vos transactions numériques avec airSlate SignNow. Automatisez les flux de travail pour tout, des simples dossiers employés aux accords complexes et formulaires de vente.
Apprenez comment protéger la libération du lien :
- Ajoutez une série de fichiers depuis votre lecteur ou stockage cloud.
- Faites glisser et déposez des cases à remplir intelligentes (signature, texte, date/heure).
- Modifiez la taille des champs en appuyant dessus et en sélectionnant Ajuster la taille.
- Placez des cases à cocher, des menus déroulants et des groupes de boutons radio.
- Ajoutez des signataires et demandez des pièces jointes.
- Protégez la libération du lien.
- Ajoutez la formule où vous souhaitez que le champ se génère.
- Utilisez des remarques et des annotations pour les utilisateurs n'importe où sur la page.
- Approuvez toutes les modifications en cliquant simplement sur TERMINER.
Connectez des personnes de l'intérieur et de l'extérieur de votre entreprise pour travailler électroniquement sur des documents importants et protéger la libération du lien à tout moment et sur n'importe quel système avec airSlate SignNow. Vous pouvez suivre chaque action effectuée sur vos modèles, recevoir des notifications et un rapport d'audit. Restez concentré sur votre entreprise et vos relations clients tout en sachant que vos données sont précises et protégées.
Comment ça marche
Fonctionnalités airSlate SignNow appréciées par les utilisateurs
Découvrez des résultats exceptionnels Protection de la libération du lien. Utilisez des outils de signature électronique qui fonctionnent où vous êtes.
Obtenez des signatures juridiquement contraignantes dès maintenant !
FAQ
-
Que se passe-t-il lorsqu'un utilisateur envoie une URL réécrite Mimecast à un destinataire externe ?
Si une URL réécrite est envoyée en sortie via Mimecast, l'URL revient à sa forme originale. ... Ceci est utilisé pour toutes les URLs sur lesquelles on clique avant que des vérifications soient effectuées. -
Comment fonctionne la protection des URLs Mimecast ?
Protection contre les menaces ciblées - URL Protect est un service avancé de Mimecast, qui s'appuie sur nos services de passerelle de sécurité pour protéger votre organisation contre la menace croissante posée par les attaques de phishing avancées et de spear phishing dans le courrier entrant. Il fonctionne en réécrivant toutes les URLs dans les messages entrants. -
Qu'est-ce que la protection contre les menaces ciblées Mimecast ?
Mimecast Targeted Threat Protection – Impersonation Protect Impersonation Protect est une technologie avancée de sécurité des emails qui protège les employés contre les attaques de social engineering ciblées dans les emails, souvent appelées whaling ou fraude du PDG. -
Comment fonctionne la sécurité des emails Mimecast ?
Mi
Ce que disent les utilisateurs actifs — protect link release
Questions fréquemment posées
Comment puis-je générer un PDF et le rendre signable?
Que dois-je faire pour signer électroniquement un PDF ?
Où dois-je signer dans un PDF ?
Obtenez plus pour protect link release
- Avantages de airSlate SignNow CRM vs. Insightly pour les opérations
- Avantages de airSlate SignNow CRM vs. Insightly pour la planification
- Avantages de airSlate SignNow CRM vs Insightly pour l'achat
- Avantages du CRM airSlate SignNow vs. Insightly pour l'assurance qualité
- Avantages de airSlate SignNow CRM vs. Insightly pour l'ingénierie
- Avantages du CRM airSlate SignNow vs. Insightly pour l'export
- Avantages de airSlate SignNow CRM vs. Insightly pour l'expédition
- Avantages de airSlate SignNow CRM vs. Insightly pour les relations publiques
Tout savoir sur la signature électronique

Découvrez d'autres protect link release
- Renforcez vos flux de travail avec l'IA pour la ...
- Autonomiser vos flux de travail avec l'IA pour la ...
- Renforcez vos flux de travail avec l'IA pour la ...
- Autonomiser vos flux de travail avec l'IA pour la ...
- Autonomiser vos flux de travail avec l'IA pour la ...
- Autonomiser vos flux de travail avec l'IA pour la ...
- Autonomiser vos flux de travail avec l'IA pour la ...
- Autonomiser vos flux de travail avec l'IA pour la ...
- Renforcez vos flux de travail avec l'IA pour la ...
- Renforcez vos flux de travail avec l'IA pour la ...
- Renforcez vos flux de travail avec des outils d'IA pour ...
- Commencez votre parcours de signature électronique : ...
- Commencez votre parcours de signature électronique : ...
- Commencez votre parcours de signature électronique : ...
- Commencez votre parcours de signature électronique : ...
- Commencez votre parcours de signature électronique : ...
- Commencez votre parcours de signature électronique : ...
- Commencez votre parcours de signature électronique : ...
- Commencez votre parcours de signature électronique : ...
- Commencez votre parcours de signature électronique : ...













































