Create eSignature Form Later
Make the most out of your eSignature workflows with airSlate SignNow
Extensive suite of eSignature tools
Robust integration and API capabilities
Advanced security and compliance
Various collaboration tools
Enjoyable and stress-free signing experience
Extensive support
ESign PDF for Administrative Fast
Keep your eSignature workflows on track
Our user reviews speak for themselves






Create eSignature Form Later. Discover the most user-pleasant knowledge of airSlate SignNow. Control your complete file processing and sharing method digitally. Change from hand held, paper-structured and erroneous workflows to automatic, electronic digital and faultless. It is simple to generate, provide and sign any paperwork on any system anywhere. Make sure that your important business circumstances don't move over the top.
See how to Create eSignature Form Later. Stick to the straightforward manual to get going:
- Design your airSlate SignNow bank account in click throughs or sign in along with your Facebook or Google accounts.
- Enjoy the 30-time free trial offer or go with a costs plan that's ideal for you.
- Locate any legal template, create on the internet fillable kinds and share them firmly.
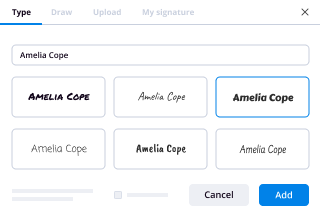
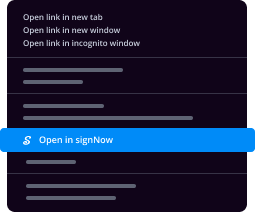
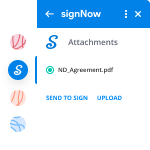
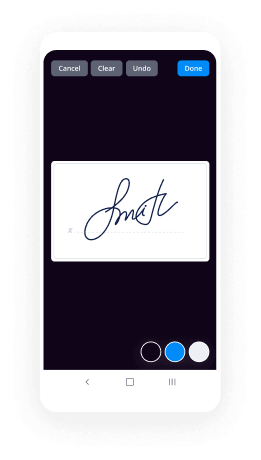
- Use innovative functions to Create eSignature Form Later.
- Sign, modify putting your signature on purchase and gather in-individual signatures 10 times faster.
- Established automatic reminders and obtain notices at each and every stage.
Relocating your activities into airSlate SignNow is straightforward. What practices is a simple approach to Create eSignature Form Later, along with recommendations to keep your co-workers and companions for far better partnership. Empower your workers together with the greatest resources to keep along with organization processes. Boost output and range your small business more quickly.
How it works
Rate your experience
-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
Intuitive UI and API. Sign and send documents from your apps in minutes.
A smarter way to work: —how to industry sign banking integrate
FAQs
-
What are the best productivity tools for entrepreneurs?
I now accept Suggested Edits, as they come in. Include the price of the product/service.Pre Launch:Javelin. Start and grow your product faster. javelin.com/?ref=p5eybNFKResearch:Clipular http://www.clipular.com (free)Evernote http://www.evernote.com. Free, and $45 per year.Launching Soon Page:LaunchRock http://www.launchrock.comLaunchSoon http://launchsoon.comLanding PagesSelf Hosted:ThemeForest http://www.themeforest.net $8+Hosted:UnBounce (landing pages) http://www.unbounce.com $50/moKickOffLabs: http://www.kickofflabs.com/ $15/monthOptimizely: https://www.optimizely.com/ $17/monthTurnkey...
-
How do I create a web design contract?
First of all, good for you for having the mental clarity to want to use contracts for web design. You believe it or not, are far ahead of most “developers” just by virtue of being able to conceive of using contracts. You’ll be ahead of most “wantrepreneurs” and “startup founders” just by thinking of using contracts, so hats off to you young man.You can find sample contracts very easily, just by Googling the free-to-use “contract killer” template. Just Google “contract killer web design contract.” Another way to find even more sample contracts is to take a few “how to be a web developer” courses on Udemy and I think you’d probably find more by Googling “sample web design contract,” going to the Freelancer’s Union website, going to signNow and looking at theirs as well.I’m not a lawyer, but I don’t have to be one (nor do you) in order to use or edit contracts. I started out as a web developer not using contracts simply because nobody else I spoke with knew anything and it was a very intimidating topic; and like so many other things of value in life, if you want it done correctly sometimes you just have to get off your butt and do some hard work. I had more than my fair share of being taken advantage of by non-profits (I used to be in favor of volunteering, now I will never do it again) who once they had pro bono (free basically) work, had “revisions” without end - taking professional design and wanting to turn it into a coloring book for a bi-polar paranoid schizophrenic. I had “agencies” asking me to build sites for them “on spec,” (for free), playing mind games with “more work later.” “Agencies” with $200 budgets, and so on and on it went. Until I saw what real agencies charged for crap work with no SEO or thought. Now I always contracts, and I use electronic signatures, and store contracts for years on Dropbox in case they “forget” something a year or two out.I keep a folder of different contracts, RFP responses, generic “sorry your budget is so low” letters, and “hey, we’d love to work with you” letters and suggest you do the same. You can use Gravity Forms to set up or send form contracts with IP tracking and e-signature or use fill-in PDF forms, or even old-fashioned paper contracts, but contracts are a necessity especially in a profession as under-valued and as misunderstood as ours.Good luck and if you need any future help, I’d be happy to pitch in.
-
What are the applications of a digital signature?
AuthenticationAlthough messages may often include information about the entity sending a message, that information may not be accurate. Digital signatures can be used to authenticate the source of messages. When ownership of a digital signature secret key is bound to a specific user, a valid signature shows that the message was sent by that user. The importance of high confidence in sender authenticity is especially obvious in a financial context. For example, suppose a bank's branch office sends instructions to the central office requesting a change in the balance of an account. If the central office is not convinced that such a message is truly sent from an authorized source, acting on such a request could be a grave mistake.IntegrityIn many scenarios, the sender and receiver of a message may have a need for confidence that the message has not been altered during transmission. Although encryption hides the contents of a message, it may be possible to change an encrypted message without understanding it. (Some encryption algorithms, known as nonmalleable ones, prevent this, but others do not.) However, if a message is digitally signed, any change in the message after signature invalidates the signature. Furthermore, there is no efficient way to modify a message and its signature to produce a new message with a valid signature, because this is still considered to be computationally infeasible by most cryptographic hash functions (see collision resistance).Non-repudiationNon-repudiation, or more specifically non-repudiation of origin, is an important aspect of digital signatures. By this property, an entity that has signed some information cannot at a later time deny having signed it. Similarly, access to the public key only does not enable a fraudulent party to fake a valid signature.
-
What is a brief history of blockchain?
Hey there, that is a great question and one that I’d love to give you a thorough answer to!The dream of bringing money into the digital realm has been dreamed by innovative, bright minds for a long time before Satoshi Nakamoto released his whitepaper on the first blockchain-based cryptocurrency. It is important to note that there are big technical differences that make Bitcoin the first of its kind though!For now, let me give you a brief run-down of the most important digital currencies before Bitcoin, that all contributed to the eventual advent of blockchain technology in the form of Bitcoin.1982 - David Chaum publishes a groundbreaking paper called “Blind Signatures”, which is the fundament for his revolutionary digital currency called eCash, which he releases in 1993. You can read more about this fascinating chapter of history here: ’82 | The Birth Of Digital Cash – blockwhat? – Medium1996 - The oncologist Douglas Jackson creates e-gold, the first gold backed digital currency that sees mass adoption among users and merchants (over 3.5 mio accounts!). Fascinating story that involves lots of gold, Eastern European Hackers, the Secret Services and Islamic financial Jihad: ’96 | Oncologist + Gold = Revolution? – blockwhat? – Medium1997 - Adam Back comes up with his so called hashcash, aka one of the first implementations of a Proof-of-Work! He is also one of the few people cited by Satoshi Nakamoti in his whitepaper for Bitcoin. ’97 | Anybody interested in some hash(cash)? – blockwhat? – Medium1998 - The computer scientist Wei Dai shares his proposal for a digital currency called b-money with the legendary (and now defunct) mailing list “Cypherpunk”. He also gets cited by Satoshi Nakamoto in Bitcoin’s whitepaper! ’98 | Wei Dai — Who dat? – blockwhat? – Medium1998 - In the same year, Nick Szabo first has his idea to create something that he would later call BitGold. There exist many theories that this guy might be behind Nakamoto’s pseudonym.2003 - Emir Sin Gün publishes his paper on a decentralized currency system powered by Proof-of-Work (sounds familiar, doesn’t it?).2004 - The legendary Hal Finney shares his idea about so called Reusable-Proof-of-Works.There were many other digital currencies that ended up somewhere in the great trash can of history - nevertheless I always find out mesmerizing to see for how long the dream of digital currencies has been around before Bitcoin!I hope that I could offer my two cents to answer your question. If you want to, I’d feel humbled if you check out my blog called “blockwhat?”, in which I thoroughly explore the history behind blockchain(:blockwhat? – MediumAll the bestTill
-
How did Bitcoin get started?
Bitcoin was introduced to the public on November 1st, 2008 with an email from Satoshi Nakamoto to the cryptography@metzdowd.com mailing list:I've been working on a new electronic cash system that's fully peer-to-peer, with no trusted third party.The paper is available at:http://www.bitcoin.org/bitcoin.pdfThe main properties: Double-spending is prevented with a peer-to-peer network. No mint or other trusted parties. Participants can be anonymous. New coins are made from Hashcash style proof-of-work. The proof-of-work for new coin generation also powers the network to prevent double-spending. Bitcoin: A Peer-to-Peer Electronic Cash System Abstract. A purely peer-to-peer version of electronic cash would allow online payments to be sent directly from one party to another without the burdens of going through a financial institution. Digital signatures provide part of the solution, but the main benefits are lost if a trusted party is still required to prevent double-spending. We propose a solution to the double-spending problem using a peer-to-peer network. The network timestamps transactions by hashing them into an ongoing chain of hash-based proof-of-work, forming a record that cannot be changed without redoing the proof-of-work. The longest chain not only serves as proof of the sequence of events witnessed, but proof that it came from the largest pool of CPU power. As long as honest nodes control the most CPU power on the network, they can generate the longest chain and outpace any attackers. The network itself requires minimal structure. Messages are broadcasted on a best effort basis, and nodes can leave and rejoin the network at will, accepting the longest proof-of-work chain as proof of what happened while they were gone. Full paper at: http://www.bitcoin.org/bitcoin.pdfSatoshi NakamotoThe resulting thread saw some insightful analysis by Hal Finney, James A. Donald, and others on the email list. Satoshi also revealed something of 'his' motivations by saying that while Bitcoin wouldn't solve the world's political problems, "we can win a major battle in the arms race and gain a new territory of freedom for several years".Prior to that first email, nothing is known of the genesis of the Bitcoin idea. Satoshi Nakamoto is a pseudonym, used by an individual or a group to protect their identity. The protocol has precedents in prior e-cash attempts, like Wei Dai's "B-money".Two months later, the official Block 0 was mined, and Satoshi posted to the crypto list again to announce the open-source release of the first Bitcoin client.References:Bitcoin P2P e-cash paperRe: Bitcoin P2P e-cash paperRe: Bitcoin P2P e-cash paperBitcoin v0.1 released
-
How are cracked versions of software created and why are developers not able to prevent it?
Cracked versions of software are created with the use of debuggers. (A debugger is a special type of software that lets programmers deconstruct their software into its constituent parts for the purpose of finding bugs, and thus de-bugging. Additionally debuggers can be used for reverse-engineering, or to see what is inside the software, to learn its logic. The latter method is used mostly by malware researchers to study what malware (or computer viruses) do on-the-inside. But it can be also used by an attacker to "crack" (or bypass) legal software registration, or at times, to alter normal behavior of software, for instance by injecting a malicious code into it.)For the sake of this example, I will assume that the software that is being "cracked" was compiled into a native code, and is not a .NET or a JavaScript based application. (Otherwise it will be somewhat trivial to view its source code.) The compiled native code is a bit more tricky "beast" to study. (Native means that the code executes directly by the CPU, GPU, or other hardware.)So let's assume that the goal of an attacker is to bypass the registration logic in the software so that he or she doesn't have to pay for it. (Later for lolz, he or she may also post such "crack" on some shady online forum or on a torrent site so that others can "use" it too and give him or her their appreciation.)For simplicity let's assume that the original logic that was checking for the software registration was written in C++ and was something similar to the following code snippet:In this code sample "RegistrationName" and "RegistrationCode" are special strings of text that a legitimate software user will receive after paying for the license. (The name is usually that person's actual name or their email address, and the code is some string of unique/special characters that is tied to the name.)In the logic above, the function named "isRegistrationCodeGood()" will check if "RegistrationName" and "RegistrationCode" are accepted using some proprietary method. If they are, it will return true. Otherwise false. That outcode will dictate which branch (or scope) the execution will follow.So the logic above will either show that registration failed and quit:Or, if the registration code and name matched, it will save the registration details in persistent storage (such as the File System or System Registry) using the function named "rememberRegistrationParameters()" and then display the message thanking the user for registering:A "cracker" will obviously want to achieve the second result for any registration code that he or she enters. But they have a problem. They do not have the C++ source code, part of which I showed above. (I hope not!)So the only recourse for an attacker is to disassemble the binary code (that always ships with software in the form of .exe and .dll files on Windows, and mostly as Unix executables inside the .app packages on a Mac.) An attacker will then use a debugger to study the binary code and try to locate the registration logic that I singled out above.Next you can see the flowchart for a snippet of code that I showed in C++, presented via a low-level debugger. Or, as the code will be read in the binary form after compilation:(For readability I added comments on the right with the names of functions and variables. They will not be present in the code that an attacker could see.)(To understand what is shown above an attacker will have to have good knowledge of the Assembly language instructions for the native code.)I also need to point out that having a disassembly snippet like the one above is the final result for an attacker. The main difficulty for him or her is to locate it among millions and millions of other similar lines of code. And that is their main challenge. Not many people can do it and that is why software "cracking" is a special skill.So having found the code snippet above in the software binary file a "cracker" has two choices:1) Modify (or patch) the binary.2) Reverse-engineer the "isRegistrationCodeGood()" function and copy its logic to create what is known as a "KeyGen" or "Key Generator."Let's review both:The first choice is quite straightforward. Since an attacker got this far, he or she knows the Intel x64 Instruction Set quite well. So they simply change the conditional jump from "jnz short loc_7FF645671430" at the address 00007FF645671418 (circled in red in the screenshots) to unconditional jump, or "jmp short loc_7FF645671430". This will effectively remove any failed registration code entries and anything that the user types in will be accepted as a valid registration.Also note that this modification can be achieved by changing just one byte in the binary code from 0x75 to 0xEB:But this approach comes with a "price" of modifying the original binary file. For that an attacker needs to write his own "patcher" (or a small executable that will apply the modification that I described above.) The downside of this approach for an attacker is that patching an original executable file will break its digital signature, which may alert the end-user or the vendor. Additionally the "patcher" executable made by an attacker can be easily flagged and blocked by the end-user's antivirus software, or lead criminal investigators to the identity of the attacker.The second choice is a little bit more tricky. An attacker will have to study "isRegistrationCodeGood()" function and copy it into his own small program that will effectively duplicate the logic implemented in the original software and let him generate the registration code from any name, thus giving any unscrupulous user of that software an ability to register it without making a payment.Vendors of many major software products understand the potential impact of the second method and try to prevent it by requiring what is known as "authentication." This is basically a second step after registration, where the software submits registration name to the company's web server that returns a response back to the software of whether the code was legitimate or not. This is done by Microsoft when you purchase Windows (they call it "Activate Windows") and also by signNow, and many other companies. This second step may be done behind-the-scenes on the background while the software is running, and will usually lead to cancellation of prior registration if it was obtained illegally.So now you know how software is "cracked".Let me answer why it is not possible to prevent it. It all boils down to the fact that any software code needs to be read either by CPU (in case of a binary native code) or by an interpreter or a JIT compiler (in case of JavaScript or .NET code.) This means that if there's a way to read/interpret something, no matter how complex or convoluted it is, an attacker with enough knowledge and persistence will be able to read it as well, and thus break it.There is an argument though that cloud-based software is more secure, which is true, since its (binary) code remains on the server and end-users do not have direct access to it. And even though cloud-based software is definitely the future, it has some major drawbacks that will never allow it to fully replace your conventional software. To name just a few:Not everyone has an internet connection, or is willing to upload their data online. Additionally someone’s internet connection can be very expensive or too slow to make the software run very laggy.Then there’s a question of distributed computing. For instance, Blizzard Entertainment would never make “World of Warcraft” to fully run on their servers due to immense computational resources needed to render every single scene for every player they have. Thus it is in their best interest to let each individual user’s computer to do the rendering instead.As a software developer myself, I obviously don't like when people steal software licenses. But I have to accept it and live with it. The good news is that there are not that many people who are willing to go extra mile and search for a cracked version of software. The main problem for those who do, is that by downloading a patched executable, or an attacker's KeyGen or a Patcher, they are effectively "trusting" him or her not to put anything "nasty" into it that was not "advertised on the package" (stuff like trojans, malware, or keyloggers.) So the question for those people becomes -- is it worth the cost of the software license to potentially infect your system with a nasty virus?On the other side of the equation, some developers react very negatively to any attempts to steal their software licenses. (I was there too.) They try to implement all kinds of countermeasures -- anything from tricking reverse-engineers, to adding booby traps in the code that may do something nasty if the code detects that it is being debugged, to obfuscating or scrambling the code, to enforcing all kinds of convoluted DRM schemes, to blocking users from certain countries. I personally try to stay away from all of those measures. And here's why:A) Any kind of anti-reverse-engineering tactics could be bypassed by an attacker with enough persistence. So why bother and waste my time when I can invest that time into adding something useful to my software that will make it more productive for legitimate users?B) Some code packers could create false positives with antivirus software, which is obviously not good for marketing of that software. It also creates unnecessary complexity for the developer to debug the software.C) Adding booby traps in the code can also “misfire” on your legitimate users, which will really infuriate them and can even lead to lawsuits.D) Any DRM scheme will probably catch some 100 illegal users and greatly inconvenience 10,000 legitimate ones. So why do it to your good customers?E) Our statistics show that about 75% of all illegal licenses come from China, Russia, Brazil, to name the worst offenders. (I also understand that the reason may be much lower incomes that people have in those countries.) The main issue for us though was the fact that if we enforce our DRM or add some strong registration authentication, many people that wanted to bypass our registration would simply use a stolen credit card number. And we had no control over it. Our system will use it to send them a legitimate license only to have the payment bounce in weeks time. As a result we would lose the money that were paid for the license, plus the credit card company will impose an additional chargeback fee to our account, which may range from $0.25 to $20 per bad purchase on top of the license cost.F) As was pointed out in the comments, some companies may actually benefit from allowing pirated copies of their software. Microsoft for instance gets a lot of free publicity from people using their Windows OS, the same goes for signNow with their Photoshop. That is a good point that I agree with.So my philosophy is now this -- if someone wants to go extra mile and steal our software, go for it! They went this far to do it anyway, so they probably have a good reason. On the positive side there are so many other customers that appreciate the work that goes into creating software that greatly outnumber those that don’t.PS. Thank you for all your feedback! It makes me feel good that the knowledge I shared is useful to others.
-
How do I register a startup in India? How much money and time does it take? If am currently only 17, what issues will I face dur
Algorithm for starting a Private Limited Company: Engineer's View Personally I believe, If someone is starting a company with long term perspective or to bring some change through their unique Product/Services, one must go for Private limited firm. Prime reason for this is easy to raise funds from Angels/VC in case you go for investment. Step 1. Registration of Company 1. Name Selection: Check whether your desired company name is available or not at MCA website [ http://www.mca.gov.in/ ]. Name must be unique & must resemble with business you intend to do (highlighted one). EX: Arihant Labs Retail Services Pvt. Ltd 2. Registration of Name at ROC: Name approval usually takes maximum of 14 days. This is done online through MCA website. Moreover, you need to apply with at least 4 names for approval with a writeup about significance of names with main business of the company. 3. 1. Documents Required: 2. 1. Options for names for the proposed Company (on the basis of preference) 2. Amount of Share Capital; proposed shareholding ratio 3. A paragraph on the proposed major line of business of the company (main objects) 4. City of Registered Office. 5. Copy of ownership deed/sale deed(if property is owned) 6. Copy of rent agreement with NOC (if property is rented) 7. Copy of latest electricity bill/telephone bill/mobile bill for both directors 8. Copy of latest electric bill/telephone bill for the registered office proof. 4. Obtaining DIN & DSC: 5. 1. Documents Required 2. 1. PAN Card copies for directors and shareholders. 2. Voter ID/Passport/Driving License for directors and shareholders. 3. Occupation of the Directors for directors and shareholders. 4. E-Mail IDs of all directors and shareholders. 5. Phone Numbers for all directors and shareholders. 6. Photos for directors and shareholders 6. Company Incorporation: After above mentioned formalities have been completed, we need to file following forms/docs in Rs 100 stamp paper: 7. 1. Affidavits for non- acceptance 2. INC 9, INC 10 3. DIR 2 4. NOC : This is required to be filed by the owner of the property on which your company will be situated. 5. Subscriber Sheets of MOA & AOA 6. Documents required for filling MOA & AOA 7. 1. Must be filled on OWN handwriting 2. Passport size photos 3. Sheets needs to be witnessed by CA/CS/Advocate Step 2. Obtaining PAN/TAN: After company gets incorporated, you may apply for PAN/TAN. Step 3. Trade Licence in case you are selling PRODUCTS: This is required in some places for carrying out sales. You can obtain this from local Municipality. Step 4. VAT/CST registration for selling Products: For selling intra-state, you need VAT registration & for selling inter-state, you need to register for CST. 1. Documents Required: 2. 1. Trade Licence 2. Company Incorporation Certificate 3. PAN card of company as well as of all the directors 4. Proof of residence of Directors 5. Proof of occupancy of place of business (Rent agreement/ ownership deed, Rent Bills etc) 6. MOA & AOA of company 7. Current Account in the name of company in any national bank Step 5. Service tax registration for Service Industry: In India, you need to pay service tax of 14.5% on every services you have charged customer for. 1. Documents Required: 2. 1. Company Incorporation Certificate 2. PAN card of company as well as of all the directors 3. Proof of residence of Directors 4. Proof of occupancy of place of business (Rent agreement/ ownership deed, Rent Bills etc) 5. MOA & AOA of company 6. Current Account in the name of company in any national bank That's All folks! Your STARTUP is up to Conquer the World. UPVOTE & SHARE your views/issues We at labkafe [ http://labkafe.com/ ], prefer taxmantra [ http://taxmantra.com/ ] for our legal requirements.
-
What are some great online tools for startups? Why?
Startups need something that can give then maximum at minimum invest because the number of risks is always high! We understand all your needs and hence we have got this product for you- PayUnow!Be it any startup: food, automobiles, e-commerce, travel, IT, education or homemakers, this one is for you! It is available for FREE for Android and iOS users. Let customers discover you as you upload pictures of delicacies. To collect online payments easily, anytime and anywhere, all you have to do is share a unique business link or website which you will create with us for FREE! Here’s why you should download the app NOW:It is FREEAllows you to create a business website with zero maintenance costHas the lowest TDR in the market i.e 1.99+GST!Lets you showcase your productsAllow you to add contact details and locationMultiple payment options supportedYour customers do not need an app! All you need to accept payments directly in your bank is one link: you can choose this link for FREE!Quick and paperless bank verification and documentationPayUnow is a product of India’s largest Fintech Company- PayU! Join the communtiy of 4.5 lakhs+ businesses like you! We look forward to empowering the SMBs and give them a relief from the hassles of payments so that the only thing you need to focus is your business growth! We are continuously creating a guide to assist you with the best. Learn how to sign up, edit, share and verify by visiting here:
Trusted esignature solution— what our customers are saying
Get legally-binding signatures now!
Frequently asked questions
How do i add an electronic signature to a word document?
How do you esign financial documents in pdf?
What is webpage error missing parameter installkey mean when trying to esign?
Get more for Create eSignature Form Later
- How Can I Electronic signature Nevada Real Estate Presentation
- Can I Electronic signature Nevada Real Estate Presentation
- How To Electronic signature Nevada Real Estate Presentation
- How Do I Electronic signature Nevada Real Estate Presentation
- How Do I Electronic signature Nevada Real Estate Presentation
- Help Me With Electronic signature Nevada Real Estate Presentation
- How Can I Electronic signature Nevada Real Estate Presentation
- Help Me With Electronic signature Nevada Real Estate Presentation
Find out other Create eSignature Form Later
- Stipulation form 2dca 01 california courts
- De 120pa attachment to notice of hearing proof of personal service probate decedents estates and guardianships and form
- Fw 004 order on application for waiver of additional alpine courts ca form
- Interpreter request form superior court riverside riverside courts ca
- Gc 400e1gc 405e1 cash assets on hand at end of account period standard and simplified accounts judicial council forms courts ca
- Subject access request sar form subject access request gdpr
- Fl 2 case management conference report 01 01 doc form
- Super 8s cricket scoresheet cricket super 8s scoresheet form
- Treatment proivider kiln drying certificate form
- Repaidslpcsydney cba com au form
- Timesheet template daily medical temp time sheet form
- Ringwood secondary collegebuilding an even better future form
- Retail bond numberretail bond lodgement office use form
- Certificate of compliance trailer caravan certificate of compliance trailer caravan catalogue no 45071569 form no 1590 571308942
- Application for asset protection permit city of boroondara form
- Meter form wiring diagramswatthour meters
- Download gen form 04pdf 67020 kb state revenue office
- Transport and main roads corporate forms f4862
- Medicare compensation recovery notice of past benefits request m0026 form
- Application formtelstra bereavement support heres