Install Electronic signature Form Computer
Make the most out of your eSignature workflows with airSlate SignNow
Extensive suite of eSignature tools
Robust integration and API capabilities
Advanced security and compliance
Various collaboration tools
Enjoyable and stress-free signing experience
Extensive support
How To Save eSignature in Oracle
Keep your eSignature workflows on track
Our user reviews speak for themselves






Install Electronic signature Form Computer. Check out one of the most consumer-friendly exposure to airSlate SignNow. Control all of your document handling and expressing system electronically. Range from hand held, document-centered and erroneous workflows to computerized, electronic digital and faultless. You can actually produce, produce and signal any files on any gadget anyplace. Ensure that your airSlate SignNow company cases don't slide over the top.
Find out how to Install Electronic signature Form Computer. Keep to the basic guide to start:
- Create your airSlate SignNow bank account in click throughs or log in with the Facebook or Google bank account.
- Benefit from the 30-day time free trial or go with a prices prepare that's great for you.
- Get any legitimate design, create on-line fillable types and talk about them safely.
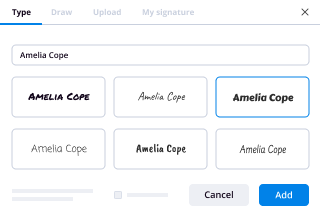
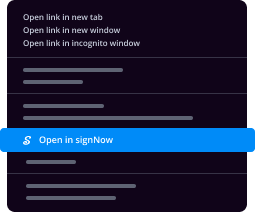
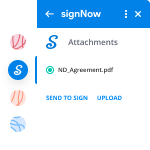
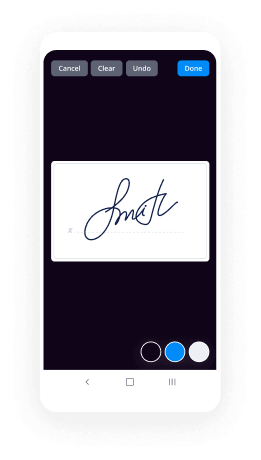
- Use superior features to Install Electronic signature Form Computer.
- Indicator, individualize signing order and accumulate in-individual signatures ten times faster.
- Set up automated reminders and get notifications at every stage.
Shifting your duties into airSlate SignNow is straightforward. What follows is a simple procedure to Install Electronic signature Form Computer, in addition to recommendations to maintain your fellow workers and partners for far better collaboration. Empower your staff with the finest tools to remain along with business procedures. Boost output and scale your business faster.
How it works
Rate your experience
-
Best ROI. Our customers achieve an average 7x ROI within the first six months.
-
Scales with your use cases. From SMBs to mid-market, airSlate SignNow delivers results for businesses of all sizes.
-
Intuitive UI and API. Sign and send documents from your apps in minutes.
A smarter way to work: —how to industry sign banking integrate
FAQs
-
What does an information technology lawyer do?
That is not a term I have see used in real life.I offer the following from HG.org on Information Technology Law:What is Information Technology Law?Information technology law provides the legal framework for collecting, storing, and disseminating electronic information in the global marketplace. Attorneys practicing in this area of the law represent individuals and businesses from all different industries. They help structure information technology transactions in a way that maximizes the client’s economic benefit while ensuring regulatory compliance. A great deal of emphasis is also placed on anticipating potential sources of dispute between the parties to a transaction, and crafting agreements that address these concerns, thereby reducing the risk of litigation.When disputes arise in the field of information technology that cannot be resolved outside of the court system, a lawyer specializing in these types of cases can prove a powerful advocate compared to a general legal practitioner. Information technology law firms tend to hire lawyers with practical experience working in the industry prior to entering the legal profession. With such a background, a lawyer is more effective at explaining technical concepts to a judge or jury, and he or she will likely have contacts within the industry that make finding consultants and expert witnesses less difficult. Clearly, information technology law is a niche practice. Those looking to hire an attorney should bear this in mind.Software Licensing IssuesBusinesses often change or update their operating software in an effort to keep pace with technology. Switching software programs can lead to greater profitability, but it can also present any number of legal pitfalls for unsuspecting business managers. For example, a typical software licensing contract will contain provisions relating to performance warranties, installation and troubleshooting, user training, limited liability and indemnification of the vendor, infringement disclaimers, payment and finance terms, and more. Despite the complexity of these agreements, some software company representatives purposefully wait to provide a copy until shortly before the sale closes.Owners and managers who find themselves presented with a licensing agreement that they do not completely understand should resist pressure from the sales representative to sign the document with little or no time for meaningful review. Any “deadline” imposed by the vendor is likely nothing more than a high pressure sales tactic. There is simply too much at stake in the event the software fails to meet the needs of the business. The wisest course of action is to demand additional time, and hire an information technology attorney to analyze the contract and to point out terms that should be negotiated.Data Privacy and SecurityMuch of the litigation that occurs in the field of information technology results from enterprises failing to keep customer and employee information secure. Now that it is primarily stored in digital format, sensitive information is susceptible to theft on a scale unimaginable in previous generations. Hackers and other cyber criminals routinely target financial institutions, e-commerce websites, and ordinary businesses, sometimes gaining access to thousands of customers’ data all at once. This can lead to various legal claims, from government enforcement actions to class action consumer lawsuits.Companies that have any presence on the internet should act proactively to avoid these problems. Information technology lawyers are available to audit security systems and policies, and to recommend any necessary changes. If a bsignNow has already occurred, an experienced legal team can represent companies in investigations by the FTC or state attorneys general, and defend against civil litigation brought by private parties. Data privacy and security issues can arise at any time. To succeed in today’s business environment, it is critical to stay ahead of the curve and make safeguarding digital information a priority.Electronic Signature LawsAnother growing area of concern for many businesses involves electronic signatures. Like digital storage, electronic signature software has the potential to dramatically streamline operations for businesses willing to embrace new technology. At the same time, care must be taken to avoid compromising sensitive customer data and/or violating government regulations on the subject. With respect to electronic signature laws, business owners should be aware of at least the following two pieces of legislation: the Uniform Electronic Transactions Act (UETA), and the Electronic Signatures in Global and National Commerce Act (ESIGN).Nearly every state has adopted UETA in some form, while ESIGN was passed at the federal level. Together, these laws allow companies to replace traditional paper signature documents with electronic forms. Customers can agree to contractual terms with the click of a computer mouse, speeding up the turnaround time for a transaction considerably. However, UETA and ESIGN require businesses that use electronic signatures to comply with rules relating to customer consent disclosures, record retention, and document reproduction capabilities. Again, engaging an attorney to conduct a compliance review in this area is highly recommended.
-
Has anybody applied for learning or driving license online, how is the process for the same?
Based on my own experience of getting the Driving license for Geared two wheeler on myself with no bribe/brokers, I can say the process of getting driving license in Bangalore, Karnataka can be divided into two stages.Stage 1 : Apply for Learner’s License (LLR)Visit the Sarathi website and select the New Learners license under Apply online drop down menu. Fill in all the required details, upload signature and photograph, upload required proofs, book slot, make payment (FYI the payment can also be done at the respective RTO) and visit the applied RTO on the slot date with the printed application form, xerox copies of the proofs(FYI I have submitted my rental agreement + Electricity bill for residence proof, Aadhaar card for Id proof, Birth Certificate for DOB proof) along with the originals for verification.The computer operator will verify the documents and start your test. The test contains the questions on basic traffic signs. Once passed, After 3 days, the RTO authorities would upload the Learner’s license to the sarathi website for you application number. You may take the print out of you Learner’s License. The approximate cost would be around 250 INR.Stage 2: Apply for Driving License (DL)Step 1:Once you complete 30 days after Learner license approval, you can again visit the Sarathi website and select the New Driving license under Apply online drop down menu. Fill in all the required details, book slot, make payment (FYI the payment can also be done at the respective RTO).Step 2:Visit the applied RTO on the slot date with the application print outs along with the documents of the vehicle you take for the driving test. You need to staple the Chalaan payment bill with Application form, Learner’s license printout, Slot booking appointment printout, vehicle documents, Stamped Postal cover with the delivery address written on it (This is used to send your DL through post. Usually you can get it in the shops near RTO offices). Once verified you will be directed to take the bio-metrics followed by the DL test(I was asked to go straight, take a U turn and come back which I did giving the vehicle and hand signals. In case of the RTOs having separate track installed, the test might vary). Once passed, you will be asked to sign in the DL register and be informed the DL will be dispatched through post within 20 days. If in case you have not received the driving license in 20 days, you may enquire the RTO with the application number. The estimated cost would be around 750 INR for geared two wheeler license.Note: This is as per my experience at the Electronic City RTO, Bangalore, Karnataka.Hope this helps. Thank you :)
-
Is mandatory DSC for proprietor ship in GST?
Hi,GST Application for registration is filed online or digitally. So the Proprietor or Partner or Director need to sign the application digitally as well.Government has provided 2 ways to sign application digitally.EVC: AADHAR BasedDSC based.AADHAR Based Signing:Not Available to Companies and LLPsMobile No of Proprietor or Partner must be linked to AADHAR.If Mobile No is mentioned on AADHAR Card then it is linked to a person's mobile no.At the time of registration OTP is sent to a person's mobile no which is linked to AADHAR on successful validation.If mobile no. is not mentioned on AADHAR then Proprietor or Partner will be required to complete the registration with the use of DSC.2. DSC Based Signing:DSC is compulsory In case of Companies or LLPs.If AADHAR is not linked to mobile no of Proprietor or Partner then he is also required to get a DSCCONCLUSION:If Proprietor's AADHAR is linked to mobile no then he does not need DSC.If Proprietor's AADHAR is not linked to his mobile no then he needs DSC.Hope the answer was helpful!Thanks.CS Priyal Pathakwww.cspriyal.com
-
What is malware and what is an example of it?
Malware is an abbreviated term meaning “malicious software.” This is software that is specifically designed to gain access or damage a computer without the knowledge of the owner. There are various types of malware including spyware, keyloggers, true viruses, worms, or any type of malicious code that infiltrates a computer. Generally, software is considered malware based on the intent of the creator rather than its actual features. Malware creation is on the rise due to the sheer volume of new types created daily and the lure of money that can be made through organized internet crime. Malware was originally created as experiments and pranks, but eventually led to vandalism and destruction of targeted machines. Today, much of malware is created for profit through forced advertising (adware), stealing sensitive information (spyware), spreading emailspam or child pornography (zombie computers), or to extort money (ransomware). Various factors can make computers more vulnerable to malware attacks, including defects in the operating system design, having all of the computers on a network run the same OS, giving users to much permissions or just using the Windows OS (due to its popularity, it gets the most malware written for it). The best protection from malware continues to be the usual advice: be careful about what email attachments you open, be cautious when surfing and stay away from suspicious websites, and install and maintain an updated, quality antivirus program.AdwareAdware (short for advertising-supported software) is a type of malware that automatically delivers advertisements.Common examples of adware include pop-up ads on websites and advertisements that are displayed by software. Often times software and applications offer “free” versions that come bundled with adware. Most adware is sponsored or authored by advertisers and serves as a revenue generating tool. While some adware is solely designed to deliver advertisements, it is not uncommon for adware to come bundled with spyware (see below) that is capable of tracking user activity and stealing information. Due to the added capabilities of spyware, adware/spyware bundles are signNowly more dangerous than adware on its own.BotBots are software programs created to automatically perform specific operations. While some bots are created for relatively harmless purposes (video gaming, internet auctions, online contests, etc), it is becoming increasingly common to see bots being used maliciously. Bots can be used in botnets (collections of computers to be controlled by third parties) for DDoS attacks, as spambots that render advertisements on websites, as web spiders that scrape server data, and for distributing malware disguised as popular search items on download sites. Websites can guard against bots with CAPTCHA tests that verify users as human.BugIn the context of software, a bug is a flaw produces an undesired outcome. These flaws are usually the result of human error and typically exist in the source code or compilers of a program. Minor bugs only slightly affect a program’s behavior and as a result can go for long periods of time before being discovered. More signNow bugs can cause crashing or freezing. Security bugs are the most severe type of bugs and can allow attackers to bypass user authentication, override access privileges, or steal data. Bugs can be prevented with developer education, quality control, and code analysis tools.RansomwareRansomware is a form of malware that essentially holds a computer system captive while demanding a ransom. The malware restricts user access to the computer either by encrypting files on the hard drive or locking down the system and displaying messages that are intended to force the user to pay the malware creator to remove the restrictions and regain access to their computer. Ransomware typically spreads like a normal computer worm (see below) ending up on a computer via a downloaded file or through some other vulnerability in a network service.RootkitA rootkit is a type of malicious software designed to remotely access or control a computer without being detected by users or security programs. Once a rootkit has been installed it is possible for the malicious party behind the rootkit to remotely execute files, access/steal information,modify system configurations, alter software (especially any security software that could detect the rootkit), install concealed malware, or control the computer as part of a botnet. Rootkit prevention, detection, and removal can be difficult due to their stealthy operation. Because a rootkit continually hides its presence, typical security products are not effective in detecting and removing rootkits. As a result, rootkit detection relies on manual methods such as monitoring computer behavior for irregular activity, signature scanning, and storage dump analysis. Organizations and users can protect themselves from rootkits by regularly patching vulnerabilities in software, applications, and operating systems, updating virus definitions, avoiding suspicious downloads, and performing static analysis scans.SpywareSpyware is a type of malware that functions by spying on user activity without their knowledge. These spying capabilities can include activity monitoring, collecting keystrokes, data harvesting (account information, logins, financial data), and more. Spyware often has additional capabilities as well, ranging from modifying security settings of software or browsers to interfering with network connections. Spyware spreads by exploiting software vulnerabilities, bundling itself with legitimate software, or in Trojans.Trojan HorseA Trojan horse, commonly known as a “Trojan,” is a type of malware that disguises itself as a normal file or program to trick users into downloading and installing malware. A Trojan can give a malicious party remote access to an infected computer. Once an attacker has access to an infected computer, it is possible for the attacker to steal data (logins, financial data, even electronic money), install more malware, modify files, monitor user activity (screen watching, keylogging, etc), use the computer in botnets, and anonymize internet activity by the attacker.VirusA virus is a form of malware that is capable of copying itself and spreading to other computers. Viruses often spread to other computers by attaching themselves to various programs and executing code when a user launches one of those infected programs. Viruses can also spread through script files, documents, and cross-site scripting vulnerabilities in web apps. Viruses can be used to steal information, harm host computers and networks, create botnets, steal money, render advertisements, and more.WormComputer worms are among the most common types of malware. They spread over computer networks by exploiting operating system vulnerabilities.Worms typically cause harm to their host networks by consuming bandwidth and overloading web servers. Computer worms can also contain “payloads” that damage host computers. Payloads are pieces of code written to perform actions on affected computers beyond simply spreading the worm. Payloads are commonly designed to steal data, delete files, or create botnets. Computer worms can be classified as a type of computer virus, but there are several characteristics that distinguish computer worms from regular viruses. A major difference is that computer worms have the ability to self-replicate and spread independently while viruses rely on human activity to spread (running a program, opening a file, etc). Worms often spread by sending mass emails with infected attachments to users’ contacts. Copies from pctools and veracode.
-
What is the best PDF reader, annotator, and organizer for academic scholars using a Mac? Is there such an application and/or sof
Even I had the similar problem, my windows 10 upgrade laptop crashed badly and I decided to go for Macbook Air which is all new OS for me. Earlier I had organised my work in Zotero in Mozilla Firefox, and I was using symlink to dropbox to sync my library between my office PC and Laptop (as free 300 MB cloud storage got exhausted early and I had no credit card to buy additional Cloud Storage from Zotero), it was all working good until I went for Window 10 upgrade and finally my hardware crashed. Now in mac I don’t know much where the appdata file stored and not sure even the symlink can be created from Zotero library stored in dropbox or not.I have installed Zotero in Firefox on mac yet I’m looking to find more easy way to do the same. I read a comparison which I hope you’ll find useful http://thesismonkey.com/compare-...Now, I’m going to try Readcube coz it has auto search and highlighted pdf options along with other features like Zotero. Lets hope it works well!
-
How does anyone make money making porn films when they're all free on the web?
This is going to be fun. Although I could elaborate my answer and broaden it up, I will stick to the question's details.Brazzers is owned by a company called MindGeek. Mindgeek happens to own also Digital Playground. Brazzers and Digital Playground shoot porn scenes and wrap them into DVDs or add them to their premium websites (sometimes both). Some money come from users who subscribe to those websites or buy the DVDs, usually because they want to get entertained by first-hand material. A lot of that material, however, end up being available "for free" on PornHub and RedTube. I have put for free in quotes because nothing is for free, especially in the adult entertainment business. AdvertisingWhen you watch a free movie or a scene on a porn tube you are forced to interact with some form of advertising at some point. Being it when you click on the play button or even before that as soon as you have loaded the page containing the video, the porn tube will deliver you a piece of advertising. It doesn't matter if you pay attention to it or not, if you follow it up or not: you have spent a part of your time in interacting with that particular ad and someone is going to cash your time in. It may seem free to you at that time, but in truth you have paid with your visit and if you keep reading you will realize that you might be ending up pay with real money too at some point.Cookies and privacyThe tube installs a cookie (well, more than one...a lot) on your computer which tracks and collects a lot of information about you and your browsing habits. Some of these cookies are temporary and expire soon after you leave the site; some others, however, are persistent and they get stored on your computer forever (or until you delete them of course). The sad (or scary, it depends how you look at it) thing is that when you visit a tube, your computer does not just get injected with the site cookies but also with third parties cookies, "delivered" to you not only any time you interact with an ad, but more often than not also as soon as you load the first page of that site. This is a typical excerpt from the privacy page on porn tubes:We have to emphasize that our Website includes Third-Party’s Content or some other type of external services. These providers, partners and contents use Cookies as well though We have no control or insights over their Cookies and it’s usage. For these reasons, We advise You to read carefully any Cookie Policy issued by our Partners in order to avoid any misuse of Your personal information collected and processed by these Administrators.How you pay for free pornSo now, not only you have watched an ad that you would have otherwise happily skipped, but you have also passed a certain amount of private information to a third party company, which will use it to push you targeted ads for as long as their cookie resides on your computer. And chances are that before or after you will buy something with real money. So, to recap, this is how you pay for free porn:The video you watch is often attached to a referral code. An adult film studio add their videos to PornHub which have signed up to that company referral program. When you watch the video that referral code and its related information are stored on your computer (yes, another cookie). If you will visit the studio's website, one day, and you will buy something in there, a slice of the sale will be turned to the initial referrer (the tube, in this case).Even if you will never visit that company's website, the tube has forced one or more ads to you and the company featured in the ad has paid the tube a certain amount of money.The company featured on the ad or their intermediary ads agency has paid for injecting a cookie on your computer in order to collect sensitive private data about your browsing history and taste. This same data have been grabbed and will be used also by the tube and not necessarily on the tube site itself. But I will talk about this later.Even if you used something like AdBlock, non-intrusive ads are still served to you and cookies still get installed in your machine. Furthermore, the use of adblock is often countered by artificially crafted workarounds such as disabling some features on the tube website and making it a nightmare to browse it.Hence, it is clear that you don't watch movies for free: you pay by watching ads and by "selling" your privacy (and personal data, in the digital era, are gold). Adult tubes capitalize on their traffic by referring sales to other websites and by selling ads and users' private information, as well as premium subscriptions.Brazzers and Digital PlaygroundGoing back to the core of your question, how do Brazzers and Digital Playground make money when their porn is "freely" available on PornHub and Redtube? Well, partly from those referral sales I was mentioning before. Broadening up the question, that works for most of the companies out there. But when it comes to Brazzers and Digital Playground there is something else worth noting. Those two film studios are functional to the PornHub and RedTube's business model and as long as those tubes earn money the companies are just fine. The reason for this is easily explained.Do you remember Mindgeek owning Brazzers and Digital Playground? Well, Mindgeek owns also PornHub and RedTube. And YouPorn and Tube8 and Xtube and Sextube and many many more. They own all the major porn tubes online except for Xvideos and Xhamster. The main line of business of Mindgeek is porn tubes, not adult film studios. The adult film studios are functional to the tubes and Mindgeek have acquired or got involved with most of the major film studios around, so that they can profit to the expense of smaller studios. The Mindgeek business modelThe tube features free porn. Some of this free porn is legit, some other is stolen copyrighted material. The tube's owners acquire legitimate, important, major film studios. They flood the tube with legitimate content from their just acquired studios and they capitalize on traffic through affiliations, advertising and the sale of sensitive data. This works like a charm and I wouldn't have much to object, as long as the law allows it, if it wasn't for the fact that the tube remains filled with stolen copyrighted content. This is why I didn't want to generalize the answer much and instead i focused on the questions' details. Brazzers and Digital Playground make money, because their mother company Mindgeek makes money or, if you prefer, because PornHub and RedTube make money. They are tools to add legitimate, quality free content to the tube and keep the traffic numbers high; of course a big chunk of that traffic is returned to the studios websites, benefiting their sales volume as well. The real victims and the infamous DMCAIt's all the rest of the industry that suffers from the, often illegitimate, availability of free porn, though. There is so much copyright infringement on porn tubes that you cannot even imagine. Back in 2010 Ventura, owners of the big production studio Pink Visual, filed a lawsuit against Mindgeek for numerous copyright infringements. In the suit the company, among others, stated [1]:These Tube Sites maintain the fiction that they offer a forum for consumers to upload and share their own original ‘user-generated’ adult video content; however in reality, they function as repositories for an extensive collection of infringing adult videos.The suit was settled later that year and the terms of the settlement haven't been disclosed [2]. Whatever convinced Ventura to drop the case, it is obvious that smaller producers don't have either the tools or the money to force tubes to comply with take-down notices. I know this too well. If an hypothetical Mr. Smith uploads a scene of mine stolen from my website to a porn tube, this is going to be the best possible scenario before me:First, I have to discover that a video of mine has been uploaded illegally to a tube. This is very hard because there are thousands of tubes out there and each, especially the major ones, feature hundreds of thousands of videos. I am supposed to monitor all the tubes out there 24/7 checking every new upload. Impossible. All I can do is to check from time to time and to hope to get lucky enough to spot my video if the offender has used some title or description terms that sound familiar to me. Often, if ever, I can spot an illegal upload after weeks, if not months; let's assume that for once i get particularly lucky and that i spot a copyright infringement one week after the video has been uploaded and running. Now I have to let the tube know and file a take-down notice according to the Online Copyright Infringement Liability Limitation Act (aka DMCA). If the video was on PornHub, this is what I have to send:Identification of the copyrighted work you believe to have been infringed or, if the claim involves multiple works, a representative list of such works.Identification of the material you believe to be infringing in a sufficiently precise manner to allow us to locate that material. If your complaint does not contain the specific URL of the video you believe infringes your rights, we may be unable to locate and remove it. General information about the video, such as a channel URL or username, typically is not adequate. Please include the URL(s) of the exact video(s).Adequate information by which we, and the uploader(s) of any video(s) you remove, can contact you (including your name, postal address, telephone number and, if available, e-mail address).A statement that you have a good faith belief that use of the copyrighted material is not authorized by the copyright owner, its agent or the law.A statement that the information in the written notice is accurate, and under penalty of perjury, that you are the owner, or an agent authorized to act on behalf of the owner, of an exclusive right that is allegedly infringed.Complete complaints require the physical or electronic signature of the copyright owner or a representative authorized to act on their behalf. To satisfy this requirement, you may type your full legal name to act as your signature at the bottom of your complaint.Assuming that once I have filed the complaint the company goes through it and acts withing 72 hours, they will contact the offender who may or may not appeal sending a counter-notification within 10 days[3]. If my luck holds and they don't appeal, ten more days have passed and the offending content is finally taken down. For twenty days my stolen content has been made available on a high traffic website and downloaded by thousands of people. By this time it has already been uploaded back to other tubes, if not to the same one as Xbiz journalists Stephen Yagielowicz & Rhett Pardon explain well:For example, one shady scenario involves a company that knowingly and willingly submits infringing content to its tube site — or pays others to do it for them — under the guise of “user” uploads. Then in an effort to seemingly comply with the DMCA, removes clips on request — only to have the compliance department send the removed material to the upload department, where this cynically cyclical process is endlessly repeated. [4] [5] You've got the picture: the big majority of content producers get their content stolen and they lose money while feeding the tubes' traffic despite themselves; part of this traffic is redirected to Brazzers and Digital Playground to finance their big productions; their scenes are leaked back into the tubes, which are owned by the same company, to feed even more traffic;the tubes cash in;rinse and repeat.ConclusionIt is worth noting that ironically this business model has started playing against its own creators. In late 2015, Mindgeek has filed an infringement lawsuit against Xvideos' (one of the only two major adult tubes players not owned by Mindgeek) parent company for allegedly streaming its content "in excess of 100 million times without authorization" and seeking $150,000 for each infringed film which Mindgeek estimate to be in the range of tens to hundreds of thousands[6]. Although the copyright infringements over my content in various tubes relate to only a few tens of videos, this scenario makes me a potential multi millionaire. Today's virtual drinks are on me, fellow Quorans. And if you want real drinks, make sure you pay the producers and not the tubes, when you look for porn. This of course stands for any copyrighted material, including, among others, Hollywood movies, books, software and music.Footnotes[1] "Tube Sites" Threaten Porn Studios[2] Pornhub[3] Online Copyright Infringement Liability Limitation Act[4] The Porn Industry Is Being Ripped Apart By Piracy-Fueled 'Tube' Websites[5] DMCA: The Porn Industry’s Worst Nightmare[6] MindGeek Is Both Plaintiff And Defendant In Two New DMCA Lawsuits
-
How do I get a 2 wheeler driving license in Bangalore?
Recently I have finished my LL and DL test and got my Driving Licence from Electronic City RTO ,KA51 , I will sharing some of the problems which I faced do’s and don’ts not the process and documents needed which is answered by various people .LL TEST INFORMATION:1 ) Don’t use the online payment option its better you go there 30 mints earlier and make pay it offline. In my case it worked for the LL slot but not for DL , money got deducted but not reflected in the website and the customer care for Sarathi is useless ,they never respond you so better not to use the payment option online .2 ) While going for LL test , please carry the originals document along with the photo copy , digital copies are not accepted.3 ) For address proof I need to embed my Aadhar Card and Electricity bill copy at the end of the Rental Agreement Page where your Current Address is written.4) Medical Certificate is not required if you are below 40 or 50 (not sure the exact figure) don’t waste time on it.5 ) Always attach the appointment slot printout along with the documents.6) Always signNow 30 minutes earlier than the slot time , if you have any doubt ask the RTO people they will help to address your queries don’t ask the brokers over there .7 ) Prepare well for the test there are lots of youtube and blogs available for it , don’t take it lightly .DL TEST INFORMATION:Once you pass the LL exam, you need to wait 30days for DL test .For Electronic city RTO(KA51) DL test is carried out in HUKUR RTO office .1> Make sure you have an postal cover like below ,where your name and address it written . You need postal stamp(5 or 10 rupees ) . make sure you have it before going to the RTO ,I had spent 1 hr to find the postoffice and stamp .2> First you need to pay the fees in Room-1 (Cash Counter) make sure you carry some change with you ,there is not Card Payment only cash is accepted. They will charge around 650 rupees for 2 wheeler .3 > Once you paid the go the Biometrics room where your photo and signature will be recorded . You need to pay 60 rupees here .4> Once matrices is done they will send you to the cash counter again where they will tele-verify your Id number, chill you don’t have to pay anything here .5> Next step is to go for the Vehicle Registration section where you need to submit your Application and Vehicle Documents , they will ask your Original RC book for cross verification .Once the verify they will ask you to give a test , this test will be on a KIOSK and it consists of four questions , once you complete it, they will give an RFID card for Driving Test on the circuit .6> Final test will be your driving in an the circuit as below , make sure you wear helmet and don’t panic . They will mount Sensors to bike’s foot rest , it finds out how many times you have grounded your sept make sure you should not ground it more that 3 to 4 times , I have touched the ground twice .7> Once you complete the test, the result will be out soon you need to submit the RFID card then they will show you your report sheet , if you pass on both the tests i.e, the the one with the KIOSK and track test then you are through !! . You can take a snap of the result sheet and submit it back to them . Thats all you need to wait 15day to get the DL to your address .I hope it will help. Cheers !!!!
Trusted esignature solution— what our customers are saying
Get legally-binding signatures now!
Related searches to Install Electronic signature Form Computer
Frequently asked questions
How do i add an electronic signature to a word document?
How to sign a pdf in paint?
How long does it take to get documents for sign?
Get more for Install Electronic signature Form Computer
- Can I Electronic signature Illinois Sports Presentation
- How To Electronic signature Illinois Sports Presentation
- How Do I Electronic signature Illinois Sports Presentation
- Help Me With Electronic signature Illinois Sports Presentation
- Can I Electronic signature Illinois Sports Presentation
- How Can I Electronic signature Illinois Sports Presentation
- How To Electronic signature Missouri Police PDF
- How Do I Electronic signature Missouri Police PDF
Find out other Install Electronic signature Form Computer
- In person drop off you may drop off form
- Would include any new information that fws
- Does not impose an information fws
- Proposed renewal fws form
- Investigation will reclassify its seattle fws form
- Disrupted fws form
- While you can ask us in your comment fws form
- Authorities fws form
- Rulemaking guide 318 dm 5 centralized library u fws form
- Doi facilities maintenance and capital improvements fws form
- Bancroft elementary school garden success u s fish and wildlife fws form
- Shiloh iv me form
- Parker little colorado river spinedace recovery plan form
- Strix occidentalis lucida us fish and wildlife service form
- Fiscal year annual budget and work plan approved august 14 san juan river recovery implementation program fy2009 funding 09 sow form
- This example fws form
- With granite outcrops would continue to fws form
- Everglade snail kite rostrhamus sociabilis plumbeus form
- Seepage swamps form
- Best science committee form