Verrouiller Le PDF Du Téléphone. Utilisez Des Outils De Signature électronique Qui Fonctionnent Où Que Vous Soyez.
Améliorez votre flux de travail documentaire avec airSlate SignNow
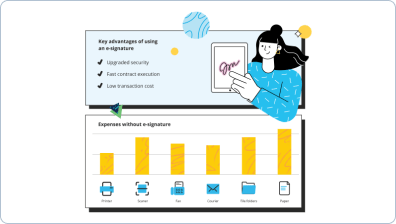
Flux de travail eSignature agiles
Visibilité rapide sur l'état du document
Configuration d'intégration simple et rapide
Verrouiller le PDF du téléphone sur n'importe quel appareil
Traçabilité d'audit complète
Exigences de sécurité rigoureuses
Découvrez les signatures électroniques airSlate SignNow en action
Solutions airSlate SignNow pour une meilleure efficacité
Les avis de nos utilisateurs parlent d'eux-mêmes






Pourquoi choisir airSlate SignNow
-
Essai gratuit de 7 jours. Choisissez le forfait dont vous avez besoin et essayez-le sans risque.
-
Tarification honnête pour des forfaits complets. airSlate SignNow propose des abonnements sans frais supplémentaires ni frais cachés lors du renouvellement.
-
Sécurité de niveau entreprise. airSlate SignNow vous aide à respecter les normes de sécurité mondiales.

Votre guide étape par étape — lock phone pdf
Verrouiller le PDF du téléphone. Obtenez les meilleures performances avec la solution de signature électronique la plus respectée et la plus sûre. Améliorez vos transactions numériques en utilisant airSlate SignNow. Optimisez les flux de travail pour tout, des dossiers employés simples aux contrats complexes et formulaires de paiement.
Apprenez comment verrouiller le PDF du téléphone :
- Ajoutez plusieurs pages depuis votre lecteur ou espace de stockage cloud.
- Faites glisser et déposez des cases à cocher personnalisées (signature, texte, date/heure).
- Modifiez la taille des champs en appuyant dessus et en choisissant Ajuster la taille.
- Insérez des cases à cocher, des menus déroulants et des groupes de boutons radio.
- Ajoutez des signataires et demandez des matériaux supplémentaires.
- Verrouillez le PDF du téléphone.
- Incluez la formule où vous souhaitez que le champ apparaisse.
- Utilisez des commentaires et des annotations pour les destinataires n'importe où sur la page.
- Enregistrez toutes les modifications en cliquant sur TERMINÉ.
Connectez des utilisateurs de l'intérieur et de l'extérieur de votre entreprise pour travailler électroniquement sur les tâches importantes de signNow et verrouiller le PDF du téléphone à tout moment et sur n'importe quel système en utilisant airSlate SignNow. Vous pouvez suivre chaque activité effectuée sur vos échantillons, recevoir des notifications et un rapport d'audit. Restez concentré sur votre entreprise et vos partenariats clients tout en étant assuré que vos données sont précises et sécurisées.
Comment ça marche
Fonctionnalités airSlate SignNow appréciées par les utilisateurs
Découvrez des résultats exceptionnels Verrouiller le PDF du téléphone. Utilisez des outils de signature électronique qui fonctionnent où que vous soyez.
Obtenez des signatures juridiquement contraignantes dès maintenant !
FAQ
-
Combien y a-t-il de combinaisons de verrouillage de téléphone ?
Dans les conditions créées par ces règles, vous pouvez créer un total de 389 112 motifs différents ! Sources et références : - Quora : ''Android (système d'exploitation) : Combien de combinaisons le déverrouillage par points d'Android 9 possède-t-il ?'' https://www.quora.com/Android-operati... -
Combien y a-t-il de combinaisons possibles de verrouillage de téléphone ?
Sur Android, ce n'est pas le cas. Si l'on suppose les règles d'Android, en exigeant 4 points dont le point de départ, il y a un total de 389 112 motifs possibles, décomposés par longueur dans un tableau ici, incluant également le code source pour calculer ces nombres. -
Combien y a-t-il de combinaisons d'écran de verrouillage Android ?
Par exemple, si le motif de verrouillage ne comporte qu'un seul point, il y a 9 combinaisons à l'écran. Par la méthode d'essais et d'erreurs, les étudiants peuvent déverrouiller le verrouillage de motif au maximum 9 fois. -
Combien y a-t-il de combinaisons pour un verrou à 3 chiffres ?
Si chaque chiffre dans un verrou à 3 chiffres
Ce que disent les utilisateurs actifs — lock phone pdf
Questions fréquemment posées
Comment ajouter une signature électronique à un PDF ?
Comment signer un document PDF ?
Comment signer électroniquement un PDF sur mon ordinateur ?
Obtenez plus pour lock phone pdf
- Avantages de airSlate SignNow CRM vs. Pipedrive
- Avantages de airSlate SignNow CRM vs. iSales
- Avantages de airSlate SignNow CRM vs. Zoho CRM
- Avantages de airSlate SignNow CRM vs. Salesforce
- Avantages de airSlate SignNow CRM vs. Creatio
- Avantages de airSlate SignNow CRM vs. Apptivo
- Avantages de airSlate SignNow CRM vs. Zendesk Sell
- Avantages de airSlate SignNow CRM vs. Copper
Tout savoir sur la signature électronique

Découvrez d'autres lock phone pdf
- Ajouter une signature à un PDF sans Acrobat avec ...
- Méthodes gratuites pour signer un document PDF en ...
- Comment ajouter une signature électronique à un PDF ...
- Comment signer des fichiers PDF électroniquement sur ...
- Comment signer un fichier PDF sur téléphone ...
- Application iPhone pour signer des documents en toute ...
- Signer un PDF sans Acrobat avec airSlate SignNow
- Envoyer un document avec une signature par e-mail ...
- How to sign a document online and email it with ...
- Comment utiliser un certificat de signature numérique ...
- Comment utiliser la signature électronique dans ...
- Comment utiliser une signature numérique sur MacBook ...
- Méthodes pour signer un PDF en ligne facilement
- Simplifiez votre commande de signature PDF Linux avec ...
- Signer des documents PDF sur Windows facilement
- Signez un fichier PDF et renvoyez-le par email ...
- Signer un document PDF sur téléphone facilement avec ...
- Signer un document PDF avec un certificat facilement et ...
- Signer un document PDF sur mon iPhone avec airSlate ...
- Signer un PDF en ligne avec une signature électronique ...













































